本文为看雪论坛优秀文章
看雪论坛作者ID:HU_Moon
一
信息搜集
使用IDA寻找程序主函数。
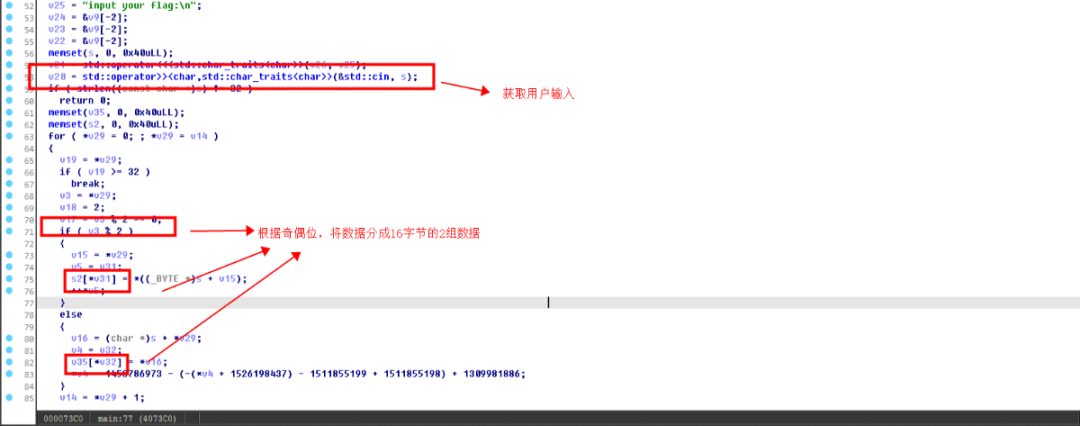
1.1获取用户输入
1.2初始化相关加密函数
1.3密文比较
二
函数功能猜测
函数中包含BASE编码表,同时存在base关键字,猜测使用了Base64编码。
sub_4059F0(参数 unk_609350、byte_6090A0:'swpu'、4)
函数内容比较复杂,同时控制流还经过混淆,可以使用deflat去处控制流混淆。
sub_406270(参数 unk_609350、s2:用户输入的部分数据、数据长度),根据代码中的rc4字符,猜测为rc4加密功能。
sub_400C10(参数 v35:用户输入的数据、v33:处理后的结果、长度)根据后面的strcmp函数,经过处理后的值为xlt0+V9PtVBKt0lEukZYug==,猜测该功能为Base64编码。
三
解密密文数据
xlt0+V9PtVBKt0lEukZYug==
"\x72\xA7\xE5\xB1\xBF\xD1\x3A\xC9\x7E\x5D\x83\xA8\x21\x4F\x70\x90"
3.1 密文1解密
根据我们的猜测,该函数为Base64加密函数,同时sub_405700函数中,保存了Base64的相关信息,猜测sub_405700为加密的初始函数,sub_405700函数的输入参数为byte_609450,我们动态运行程序,查看执行完成后byte_609450地址的值。
发现该地址生成了一个新的base表,使用该表对密文进行解密,得到明文'DST{Wo7Xj5Ad8Nx8'。
base64_table = 'ghijklmnopqrstuvwxyz0123456789+/ABCDEFGHIJKLMNOPQRSTUVWXYZabcdef'def btoa(): # base64编码函数s = input("input string to encode:\n")n = len(s) % 3x = ''asc = []for i in range(len(s)):asc.append(ord(s[i])) # 取各字符ascii值x += '{:08b}'.format(asc[i]) # 将各字符ascii值转为二进制if n:x += '0' * 2 * (3 - n) # 长度非3倍的结尾补零i = 0out = ''while i < len(x):out += base64_table[int(x[i:i + 6], 2)]i += 6if n:out += '=' * (3 - n) # 补上'='使编码后长度为4倍print(out)def atob(): # base64解码函数s = input("input string to decode:\n")b64 = []x = ''for i in range(len(s)):if s[i] == '=':b64.append(0)else:for j in range(64):if (s[i] == base64_table[j]):b64.append(j)breakx += '{:06b}'.format(b64[i])print(x)i = 0out = ''while i < len(x):if int(x[i:i + 8], 2):out += chr(int(x[i:i + 8], 2))i += 8print(out)def main():m = input('Input 1/2 to encode/decode:\n')if m == '1':btoa()elif m == '2':atob()else:print('Error! Please restart the process!')main()
3.2 密文2解密
使用该密钥对密文2进行解密,获得明文:
ACFg0Gw1Jo5Ix9C}
# RC4from Crypto.Util.number import bytes_to_long, long_to_byteskey = "szv~"msg = "\x72\xA7\xE5\xB1\xBF\xD1\x3A\xC9\x7E\x5D\x83\xA8\x21\x4F\x70\x90"key = list(key)# KSAS = [i for i in range(256)]j = 0for i in range(256):j = (j + S[i] + ord(key[i % len(key)])) % 256S[i], S[j] = S[j], S[i]# PRGAi = 0j = 0keystream = []for k in range(len(msg)):i = (i + 1) % 256j = (j + S[i]) % 256S[i], S[j] = S[j], S[i]keystream.append(S[(S[i] + S[j]) % 256])enc = "".join(map(chr, [(ord(msg[i]) ^ keystream[i]) for i in range(len(keystream))]))print(enc)
DASCTF{gW0oG7wX1jJ5oA5dI8xN9xC8}
看雪ID:HU_Moon
https://bbs.pediy.com/user-home-920107.htm
看雪CTF官网:https://ctf.pediy.com/
# 往期推荐
球分享
球点赞
球在看
点击“阅读原文”,了解更多!
文章来源: http://mp.weixin.qq.com/s?__biz=MjM5NTc2MDYxMw==&mid=2458483057&idx=1&sn=2d47aff54d3db6bf08aa7298925a3c2b&chksm=b18e49fb86f9c0edb01505729945c8afc6893e035ab17a4e1713fc9fdb35bbd6e4ed025a6a7c#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh