2018-4-15 23:56:0 Author: bartblaze.blogspot.com(查看原文) 阅读量:5 收藏
In this blog post, we'll analyse Spartacus, one of many new ransomware families popping up in 2018.
Analysis
This instance of Spartacus ransomware has the following properties:
- MD5; 25dee2e70c931f3fa832a5b189117ce8
- SHA1; a01294ffd541229718948e17f791694efb596123
- SHA256; ef25bdbcf05fa478df3ddc5f4f717c070e443da04cfc590d44409c815f237cb3
- Compilation timestamp: 2018-01-19 20:36:44
- VirusTotal report:
ef25bdbcf05fa478df3ddc5f4f717c070e443da04cfc590d44409c815f237cb3
| Figure 1 - Spartacus ransomware message |
The message reads:
All your files have been encrypted due to a security problem with your PC. If you want to restore them, write us the e-mail:
[email protected] and send personal ID KEY:
In case of no answer in 24 hours us to theese e-mail: [email protected]
The user may send up to 5 files for free decryption, as "guarantee". There's also a warning message at the end of the ransomware screen:
Do not rename encrypted files.
Do not try decrypt your data using party software, it may cause permanent data loss.
Decryption of your files with the help of thrid parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
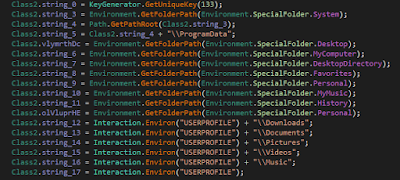
Spartacus will encrypt files, regardless of extension, in the following folders:
| Figure 2 - Target folders to encrypt |
Generating the key:
| Figure 3 - KeyGenerator |
As far as I'm aware, Spartacus is the first ransomware who explicitly asks you to send the public key (ID KEY), rather than just sending an email, including the Bitcoin address straight away, or sending the key automatically.
Encrypted files will get the extension appended as follows:
.[[email protected]].Spartacus
For example:
Penguins.jpg.[[email protected]].Spartacus
It will also drop the ransomware note, "READ ME.txt" in several locations, such as the user's Desktop:
All your data has been locked us. You want to return? Write email [email protected] or [email protected] Your personal ID KEY: DvQ9/mvfT3I7U847uKcI0QU3QLd+huv5NOYT2YhfiySde0vhmkzyTtRPlcu73BAJILIPdALjAIy5NLxBHckfyV2XS+GXdjlHMx2V/VEfj4BrZkLB3BQtEdAqS1d2yzb/2+AqTNjsRfZ99ZWVxUZO3AeEZk5h0+3hNM5GogUN2oV5zHkbMZuDaXZxQr56r8UKnW7gmSycdcJh2ueZMuEP1tAuuzdZYgmZ05x9ZT8FX9HIo03rwsi6UiJlgUTZCkiilZjxYyG+qVE+Gjk4H7dnXbQP1PC3k2WICA9R4TYb9SCdv8U/e5sxbuKAbJgEZ114liwHLasmLvQfKYSbxMlbEg==
Interestingly enough, Spartacus also embeds what appears to be a hardcoded and private RSA key:
xA4fTMirLDPi4rnQUX1GNvHC41PZUR/fDIbHnNBtpY0w2Qc4H2HPaBsKepU33RPXN5EnwGqQ5lhFaNnLGnwYjo7w6OCkU+q0dRev14ndx44k1QACTEz4JmP9VGSia6SwHPbD2TdGJsqSulPkK7YHPGlvLKk4IYF59fUfhSPiWleURYiD50Ll2YxkGxwqEYVSrkrr7DMnNRId502NbxrLWlAVk/XE2KLvi0g9B1q2Uu/PVrUgcxX+4wu9815Ia8dSgYBmftxky427OUoeCC4jFQWjEJlUNE8rvQZO5kllCvPDREvHd42nXIBlULvZ8aiv4b7NabWH1zcd2buYHHyGLQ== AQAB
Spartacus will delete Shadow Volume Copies by issuing the following command:
cmd.exe /c vssadmin.exe delete shadows /all /quiet
A unique mutex of "Test" will be created in order to not run the ransomware twice, and Spartacus will also continuously keep the ransomware screen or message from running in the foreground or on top, using the SetForegroundWindow function:
| Figure 4 - Ransom will stay on top and annoy the user |
Repeating, email addresses used are:
[email protected]
[email protected]
Decryption may be possible if the ransomware is left running, by extracting the key from memory.
Conclusion
Spartacus is again another ransomware family or variant popping up.
| Figure 5 - Meme |
Make sure to read the dedicated page on ransomware prevention to prevent Spartacus or any other ransomware.
IOCs
如有侵权请联系:admin#unsafe.sh