
Some VPNs allow split tunneling, however, Cisco AnyConnect and many other solutions of 2019-7-2 18:56:21 Author: blog.silentsignal.eu(查看原文) 阅读量:19 收藏
Some VPNs allow split tunneling, however, Cisco AnyConnect and many other solutions offer a way for network administrators to forbid this. When that happens, connecting to the VPN seals off the client from the rest of the LAN. As it turns out, breaking this seal is not that hard, which can be useful for special cases like performing pentests over a VPN designed for average users.
In our case, we had to use a hardware token that only had drivers for Windows and Mac, while most of our tools run best (and are already installed) on Linux. We started investigating on both supported platforms mentioned above and found
what others have already discovered: the routing table is modified (and kept in this state), while packets are further filtered, probably using kernel hooks.
Both IPv4 and IPv6 are affected by this filtering, and traffic towards additional network interfaces also got redirected. So we embarked on a quest to find what could be done within the rules imposed by the VPN vendor. Our first stop was the gateway in our LAN towards the internet – and thus towards the VPN concentrator. The VPN client explicitly installed routes to keep that reachable, however, packets sent directly towards the LAN gateway never arrived there, leading us towards the idea of further kernel-based filters.
The next idea was the VPN server itself since it had to be able to receive packets from the clients as part of normal operation. However, the question is: how can you tell the packets apart on the gateway – as you still have to forward packets that are part of the normal VPN operator towards the VPN server. The trivial way was TCP port numbers, so we tried connecting to various TCP ports on the VPN server, but the gateway saw no SYN packets.
This left us with a single opportunity: keeping even the TCP port the same as the port used by the tunnel already. As netstat has shown, a TCP connection towards port 443 was kept open throughout the VPN session, and subsequent connections were allowed by the
filtering mentioned above – we could even see these SYN packets on the gateway. The only problem was to tell TCP streams apart at the gateway so that the VPN still worked while we could initiate connections outside of it at the same time.
And then it clicked: while trying to cope with the fact that many public (or semi-public) Wi-Fi networks filter everything besides TCP/443 (HTTPS), we had SSLH deployed to multiplex HTTPS and SSH on the same TCP port. This works reliably because they are really easy to tell apart upon the first packet:
- SSH clients send plain text one-liners that identify the protocol and client version, while
- SSL/TLS clients send binary Client Hello packets that identify the protocol version and supported ciphers.
SSH fits this case since its port forwarding features makes it possible to punch as many holes as necessary, regardless of the direction (VPN to LAN vs. LAN to VPN).
On Debian and its derivative systems, SSLH can be installed simply from the package with the same name (sslh) and configuration can be found in the file /etc/default/sslh as a command line, as this is where SSLH takes its options from. Below is the significant line:
DAEMON_OPTS="--user sslh --listen $GATEWAY_LAN_IP:443 --ssh $VM_HOST_IP:22 --ssl $VPN_SERVER:443 --pidfile /var/run/sslh/sslh.pid"
This just means that SSLH listens on the internal (LAN) IP address of the gateway and based on the first packet received from a client that reaches this port, it either forwards it to
- a local SSH server (here we had the VPN client running on a Windows VM, and the Linux host had the SSH daemon running, hence the variable name
$VM_HOST_IP) or - the original VPN server.
Changes to the options can be applied under Debian and its derivatives by running /etc/init.d/sslh restart and the results can be tested in isolation first by connecting to TCP port 443 of the gateway, which should behave like the VPN server when using a TLS client like openssl s_client and act as an SSH server when using OpenSSH or PuTTY.
When all this works, the last bit is to redirect traffic towards the VPN server to SSLH. One way is using NAT functionality from iptables:
iptables -t nat -A PREROUTING -i $LAN_IF -p tcp --dport 443 -d $VPN_SERVER -j REDIRECT --to 443
This command adds a rule to the chain called PREROUTING within the nat table, where packets arrive before the routing decision happens. The next part is the filter, which is important to avoid loops: we only apply the magic to packets where the network interface that the packet arrives through is the LAN interface. The rest narrows the filter further to the destination TCP port being 443 and the destination host being the VPN server. The last part is what happens when this rule matches: we invoke the REDIRECT target that rewrites
- the destination host to the IP address of the interface the packet arrived through (here: LAN interface) and
- the destination port to the one supplied (here: 443).
Since SSLH was configured to listen on TCP port 443 on the LAN interface, this results in the same effect as in the above SSLH testing scenario, where we connected directly to TCP port 443 on the gateway. And the best part is that the NAT solution provided by iptables is fully bidirectional, reply packets from SSLH are automatically translated back to make it seems as if they were sent by the VPN server.
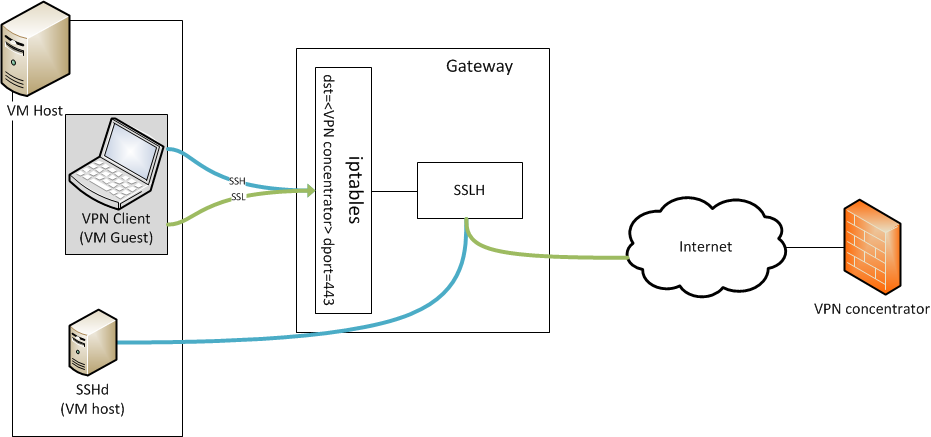
So with the iptables rule in place, everything is ready for a real-life test. The progress of SSLH can be followed in syslog and as it can be seen below, after the AnyConnect client has connected properly, SSH connections can also get through, and everything gets routed to its proper destination.
systemd[1]: Stopped SSL/SSH multiplexer.
systemd[1]: Started SSL/SSH multiplexer.
sslh[19158]: sslh-fork 1.18-1 started
sslh[19158]: ssl:connection from $VM_HOST_IP:39157 to router:https forwarded from router:57544 to vpn-server.example.com:https
sslh[19158]: ssl:connection from $VM_HOST_IP:32947 to router:https forwarded from router:57546 to vpn-server.example.com:https
sslh[19158]: ssl:connection from $VM_HOST_IP:44663 to router:https forwarded from router:57548 to vpn-server.example.com:https
sslh[19158]: ssl:connection from $VM_HOST_IP:34835 to router:https forwarded from router:57550 to vpn-server.example.com:https
sslh[19158]: ssl:connection from $VM_HOST_IP:52173 to router:https forwarded from router:57552 to vpn-server.example.com:https
sslh[19158]: ssh:connection from $VM_HOST_IP:50973 to router:https forwarded from router:55134 to $VM_HOST_IP:ssh
sslh[19158]: ssh:connection from $VM_HOST_IP:39031 to router:https forwarded from router:55136 to $VM_HOST_IP:ssh
如有侵权请联系:admin#unsafe.sh