High-profile government and telecom entities in Asia have been targeted as part of an ongoing campaign since 2021 that's designed to deploy basic backdoors and loaders for delivering next-stage malware.
Cybersecurity company Check Point is tracking the activity under the name Stayin' Alive. Targets include organizations located in Vietnam, Uzbekistan, Pakistan, and Kazakhstan.
"The simplistic nature of the tools [...] and their wide variation suggests they are disposable, mostly utilized to download and run additional payloads," it said in a report published Wednesday. "These tools share no clear code overlaps with products created by any known actors and do not have much in common with each other."
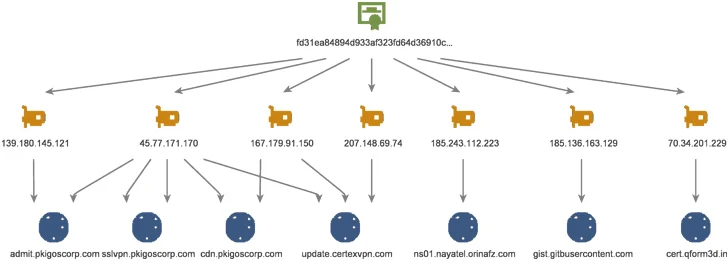
What's notable about the campaign is that the infrastructure shares overlaps with that used by ToddyCat, a China-linked threat actor known for orchestrating cyber assaults against government and military agencies in Europe and Asia since at least December 2020.
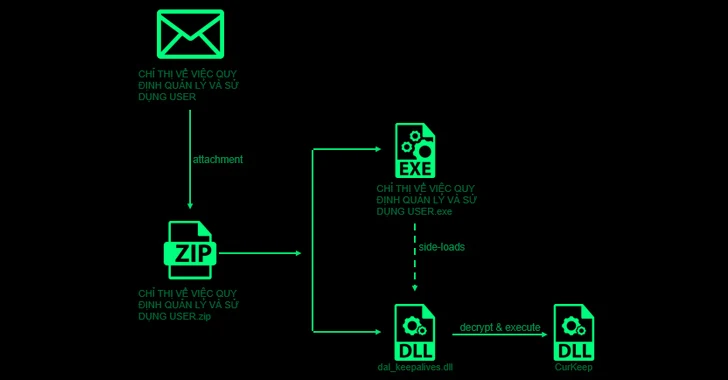
Attack chains commence with a spear-phishing email that contains a ZIP file attachment with a legitimate executable that leverages DLL side-loading to load a backdoor called CurKeep by means of a rogue DLL dal_keepalives.dll present within the archive.
CurlKeep is designed to send information about the compromised host to a remote server, execute commands sent by the server, and write server responses to a file on the system.
A closer examination of the command-and-control (C2) infrastructure has revealed a constantly evolving arsenal of loader variants dubbed CurLu, CurCore, and CurLog that are capable of receiving DLL files, executing remote commands, and launch a process associated with a newly generated file to which data from the server is written to.
Also discovered is a passive implant named StylerServ that listens on five different ports (60810, 60811, 60812, 60813, and 60814) to accept a remote connection and receive an encrypted configuration file.
While there is no conclusive evidence to connect Stayin' Alive to ToddyCat, the findings show that both intrusion sets utilize the same infrastructure to go after a similar set of targets.
"The use of disposable loaders and downloaders, as observed in this campaign, is becoming more common even among sophisticated actors," it said. "The use of disposable tools makes both detection and attribution efforts more difficult, as they are replaced often, and possibly written from scratch."
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.