A suspected Chinese-speaking threat actor has been attributed to a malicious campaign that targets the Uzbekistan Ministry of Foreign Affairs and South Korean users with a remote access trojan called SugarGh0st RAT.
The activity, which commenced no later than August 2023, leverages two different infection sequences to deliver the malware, which is a customized variant of Gh0st RAT (aka Farfli).
It comes with features to "facilitate the remote administration tasks as directed by the C2 and modified communication protocol based on the similarity of the command structure and the strings used in the code," Cisco Talos researchers Ashley Shen and Chetan Raghuprasad said.
The attacks commence with a phishing email bearing decoy documents, opening which activates a multi-stage process that leads to the deployment of SugarGh0st RAT.
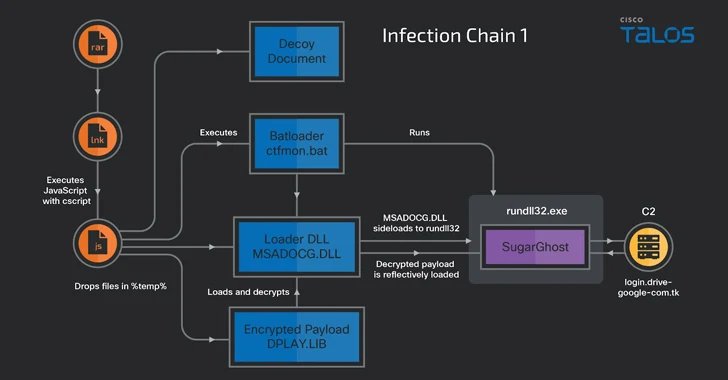
The decoy documents are incorporated within a heavily obfuscated JavaScript dropper that's contained within a Windows Shortcut file embedded in the RAR archive email attachment.
"The JavaScript decodes and drops the embedded files into the %TEMP% folder, including a batch script, a customized DLL loader, an encrypted SugarGh0st payload, and a decoy document," the researchers said.
The decoy document is then displayed to the victim, while, in the background, the batch script runs the DLL loader, which, in turn, side-loads it with a copied version of a legitimate Windows executable called rundll32.exe to decrypt and launch the SugarGh0st payload.
A second variant of the attack also begins with a RAR archive containing a malicious Windows Shortcut file that masquerades as a lure, with the difference being that the JavaScript leverages DynamicWrapperX to run shellcode that launches SugarGh0st.
SugarGh0st, a 32-bit dynamic-link library (DLL) written in C++, establishes contact with a hard-coded command-and-control (C2) domain, allowing it to transmit system metadata to the server, launch a reverse shell, and run arbitrary commands.
It can also enumerate and terminate processes, take screenshots, perform file operations, and even clear the machine's event logs in an attempt to cover its tracks and evade detection.
The campaign's links to China stem from Gh0st RAT's Chinese origins and the fact that the fully functional backdoor has been widely adopted by Chinese threat actors over the years, in part driven by the release of its source code in 2008. Another smoking gun evidence is the use of Chinese names in the "last modified by" field in the metadata of the decoy files.
"The Gh0st RAT malware is a mainstay in the Chinese threat actors' arsenal and has been active since at least 2008," the researchers said.
"Chinese actors also have a history of targeting Uzbekistan. The targeting of the Uzbekistan Ministry of Foreign Affairs also aligns with the scope of Chinese intelligence activity abroad."
The development comes as Chinese state-sponsored groups have also increasingly targeted Taiwan in the last six months, with the attackers repurposing residential routers to mask their intrusions, according to Google.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.