
2023-12-13 06:9:34 Author: www.malwarebytes.com(查看原文) 阅读量:9 收藏
The cybersecurity market is awash with expensive, high-end solutions for detecting vulnerabilities in third-party applications. However, for smaller security teams, free vulnerability scanners offer a practical alternative.
But of course, free doesn’t always mean better—it’s crucial to thoroughly assess free vulnerability scanners before integrating one into your security protocols.
How to choose a free vulnerability scanner? Industry expert Robert Elworthy, NA Solutions Engineering Manager at ThreatDown, has the answers.
Robert has a wealth of experience from his tenure as IT manager at Langdale Industries, where he managed a network of over 500 endpoints. In this article, we’ll break down his advice on selecting a free vulnerability scanner
Let’s dive into the essentials.
Related: How to find vulnerabilities in your IT environment
1. Assessing your environment’s scale
Limits on the number of scannable endpoints are common with free vulnerability scanners. While a small business with a few devices might find them sufficient, larger enterprises with hundreds of endpoints could exceed these limits.
Elworthy, reflecting on his Langdale experience, highlights the importance of a tool capable of handling large-scale environments efficiently, a critical aspect for organizations with extensive networks:
“Free tools often struggle with large networks,” Elworthy said. “It’s important to choose a tool that can handle large-scale environments without compromising efficiency, especially for organizations with extensive networks, where the ability to scale effectively is crucial.”
2. Understanding scanning requirements
Different scanners have varied requirements. Some scanners need agents installed on each endpoint for in-depth insights, while others conduct less intrusive remote scans.
Elworthy emphasizes the need for scanners that minimize the complexity of agent installations, especially in large and diverse IT landscapes:
“Often, when you opt for a free tool, you might need to run the software on-premises or integrate it into your network. This becomes particularly challenging with remote work and constantly shifting targets,” Elworthy said. “How do you deploy an agent to gather the necessary information? It’s not always straightforward with free tools.”
3. Evaluating reporting capabilities
The effectiveness of a vulnerability scanner is largely measured by its reporting capabilities, but free vulnerability scanners might provide basic reports that overlook critical remediation details.
“You must consider how you can utilize the data once it’s acquired. Some tools may display the data, but offer limited reporting or feedback capabilities, which can be a significant limitation,” Elworthy said.
4. Checking ongoing support
Cyber threats evolve rapidly, and so must your scanner. Tools like OWASP ZAP are updated frequently but require users to stay on top of these updates manually, which could add to your team’s workload.
“Without ongoing support, free tools risk becoming outdated as new vulnerabilities are discovered,” Elworthy said. “To make sure your organization isn’t unaware of emerging threats, you should confirm a free vulnerability scanner has a process for frequently updating its vulnerability database.”
5. Integration capabilities
Integration with other security tools is crucial. Elworthy stressed the importance of tools that aid in both vulnerability identification and remediation:
“It’s important to have a scanner that not only detects vulnerabilities but also offers guidance on remediation.” Elworthy said. “Many free tools don’t automatically patch vulnerabilities found during scans since remediation is a separate process. Integrating with patch management is critical to easily fix any vulnerabilities found.”
The labor involved in configuring, updating, and mastering free vulnerability scanners represents a substantial investment. Elworthy points out the hidden labor costs in using “free” tools, which can affect team efficiency:
“The time and labor required to maintain scans and update tools can be significant,” Elworthy said, reflecting on his time at Langdale. “There are often-overlooked costs associated with ‘free’ vulnerability scanners. They may not require direct financial investment, but the manpower and time needed for their effective operation can be substantial.”
Alternative: ThreatDown Vulnerability Assessment solution
For teams seeking a streamlined approach, the ThreatDown Vulnerability Assessment solution, free for all ThreatDown customers, offers:
Single, Lightweight Agent
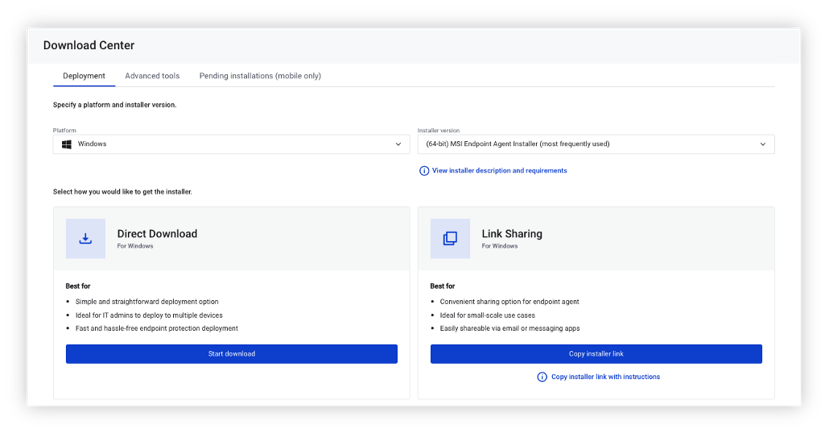
To simplify security and reduce costs, Vulnerability Assessment deploys easily in minutes without a reboot, using the same agent and cloud-based console that powers all ThreatDown endpoint security technologies.
Quick Vulnerability Scans

Identifies vulnerabilities in modern and legacy applications in less than a minute.
Accurate severity ratings
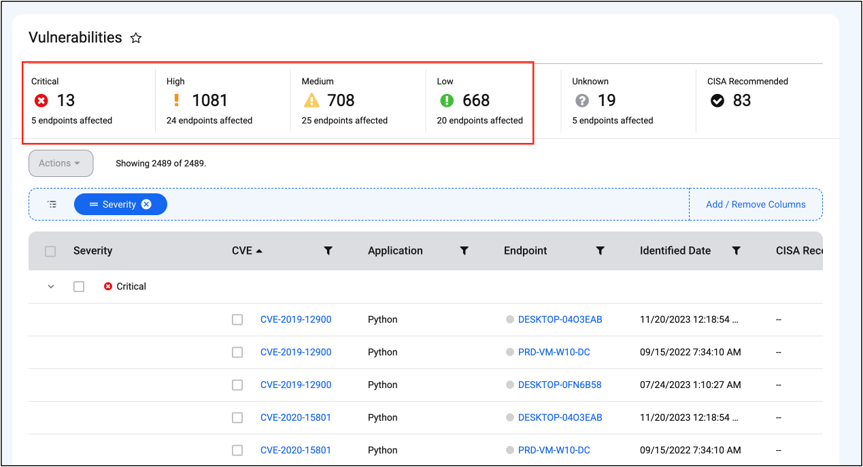
Utilizes the Common Vulnerability Scoring System (CVSS) and Cybersecurity and Infrastructure Security Agency (CISA) recommendations to evaluate and rank vulnerabilities for proper prioritization.
Security Advisor Integration
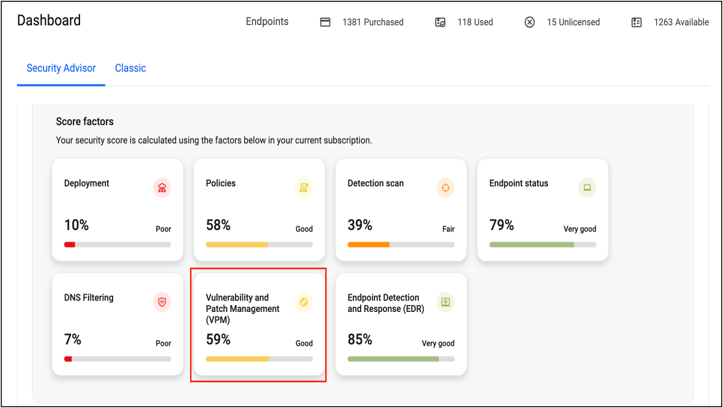
Our Security Advisor tool to analyzes an organization’s cybersecurity health—such as by assessment of current inventory and which assets are vulnerable—and generates a score based off what it finds. To improve the endpoint security health score, Security Advisor delivers recommendations to address discovered vulnerabilities: patching, updates, or policy changes.
Beyond the no-cost appeal
Opting for a free vulnerability scanner is about more than avoiding expenses. It’s about striking the right balance between cost, functionality, and available resources.
The ThreatDown Vulnerability Assessment solution simplifies the process with features like a lightweight agent, quick vulnerability scans, accurate severity ratings based on CVSS and CISA guidelines, and integration with Security Advisor for tailored recommendations and ThreatDown Patch Management for automated remediation.
Try ThreatDown Vulnerability Assessment today.
Interested in adding Patch Management capabilities as well? Check out ThreatDown Advanced, Ultimate, and Elite bundles.
Related: 3 benefits of ThreatDown bundles
如有侵权请联系:admin#unsafe.sh