
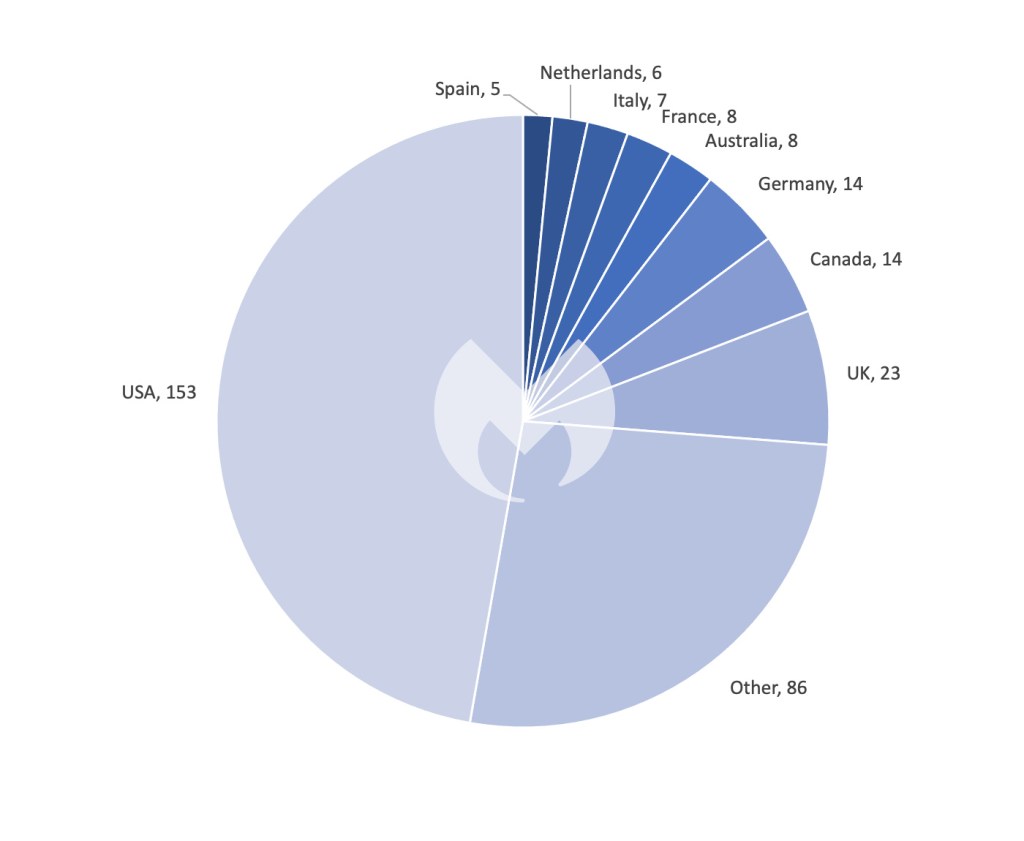
This article is based on research by Marcelo Rivero, Malwarebytes’ ransomware specialist, who monitors information published by ransomware gangs on their Dark Web sites. In this report, “known attacks” are those where the victim did not pay a ransom. This provides the best overall picture of ransomware activity, but the true number of attacks is far higher.
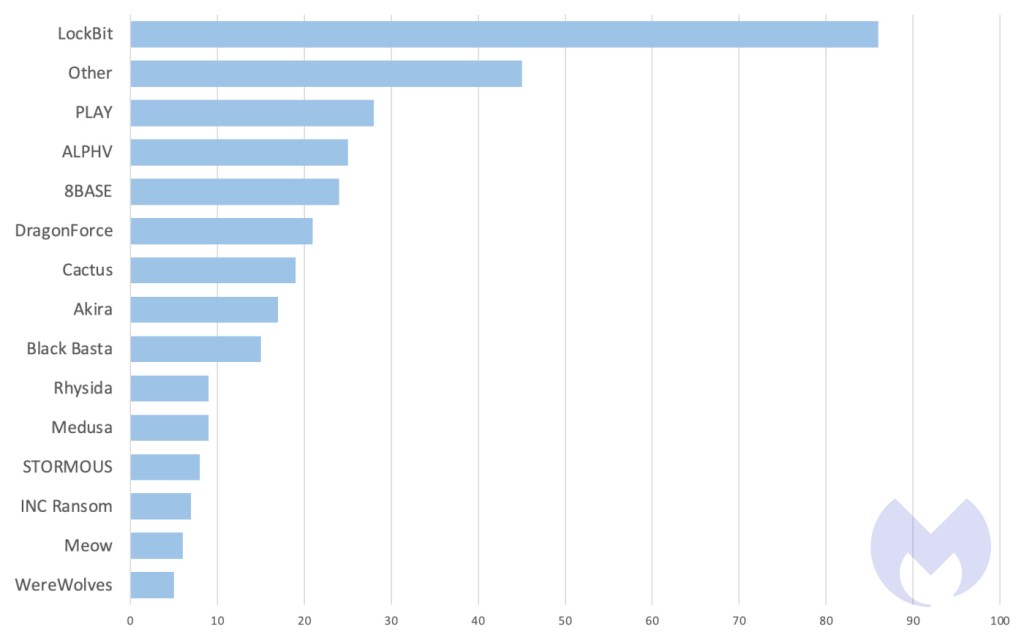
In December, the ransomware scene saw 334 attacks, with the ALPHV shutdown saga continuing to grab the spotlight. In last month’s review, when we wrote about ALPHV’s infrastructure going offline, there was widespread speculation about law enforcement involvement, but no concrete evidence to confirm this. Now, the picture is becoming clearer.
The previous theories about hardware failures within ALPHV are now overshadowed by the confirmed law enforcement action: recent updates revealed that the FBI played a pivotal role in disrupting ALPHV’s operations. This intervention led to the seizure of their URLs and enabled the recovery of decryption keys for many victims.
The FBI’s recent operation against ALPHV has been a game-changer, not only disrupting the group’s activities but also denting their reputation in the cybercriminal community. The ripple effects? ALPHV affiliates are showing signs of mistrust, with some resorting to direct victim contact via email, and others shifting alliances to rival groups like LockBit.
Adding to the intrigue, there’s talk of an emerging “cartel” between LockBit and ALPHV, according to messages on the dark web forums. This potential alliance could mark a new era in ransomware operations, where rivals look to pool resources and expertise in response to increasing law enforcement pressure.

In other news, LockBit’s attack on Capital Health last month was starkly reminiscent of events from a year prior. In December 2022, LockBit audaciously targeted SickKids (a hospital for sick children), impacting the hospital’s internal and corporate systems, phone lines, and website. Back then, LockBit’s unexpected apology for the hospital attack—blamed on a rogue affiliate, and self-forgiven with a free decryptor—was a rare moment of contrition in the otherwise ruthless world of cybercrime.
Fast forward to December 2023, and the echoes of LockBit’s past actions were resonate.
Despite their previous promises and operational policies against targeting healthcare institutions, LockBit has claimed the recent attack on Capital Health. And even though the gang claims they did not encrypt the hospital’s files, that didn’t leave the hospital unharmed.
“[The] hospitals and physicians’ offices experienced IT outages that forced them to resort to emergency protocols designed for system outages. Several surgeries were moved to later dates and outpatient radiology appointments were canceled.”
Or what ransomware gangs probably call a classic case of “no encryption, no problem” for creating havoc.
This juxtaposition of LockBit’s 2022 apology with their ongoing aggressive actions in 2023 highlighted the duplicity inherent in the ransomware landscape. LockBit’s activities served as a sobering reminder that despite occasional gestures that seem to indicate restraint or remorse, the fundamental nature of ransomware operations remains unchanged—driven by disruption, data theft, and financial gain at the expense of vulnerable targets, including critical healthcare services.
More broadly speaking, December saw a continuation of an unnerving trend of healthcare sector attacks we touched upon in last month’s review, with disruptive attacks on Massachusetts-based Anna Jaques Hospital and Liberty Hospital in Missouri. In a sector where timing and information can be a matter of life and death, such disruptions are more than mere inconveniences; they are potentially life-threatening.
New ransomware gangs
DragonForce
DragonForce is a new ransomware gang that published 21 victims to their leak site last month, including a significant attack on the Ohio Lottery on Christmas Eve. In that attack, the group claims to have encrypted devices and stolen sensitive data amounting to over 600GB. including personal information of Ohio Lottery customers and employees.
While details about DragonForce are limited, their Ohio Lottery attack and their sophisticated negotiation methods suggest that DragonForce might be a rebranded version of a previous gang.
DragonForce leak site
WereWolves
WereWolves is a new ransomware group that posted 15 victims last month across various countries, including Russia, the USA, and parts of Europe. WereWolves is unusual for targeting Russian entities and employs a variant of LockBit3 ransomware in its attacks. They are known to target a range of sectors, with a particular focus on large-scale businesses.

WereWolves leak site
Preventing Ransomware
Fighting off ransomware gangs requires a layered security strategy. Technology that preemptively keeps gangs out of your systems is great—but it’s not enough.
Ransomware attackers target the easiest entry points: an example chain might be that they first try phishing emails, then open RDP ports, and if those are secured, they’ll exploit unpatched vulnerabilities. Multi-layered security is about making infiltration progressively harder and detecting those who do get through.
Technologies like Endpoint Protection (EP) and Vulnerability and Patch Management (VPM) are vital first defenses, reducing breach likelihood.
The key point, though, is to assume that motivated gangs will eventually breach defenses. Endpoint Detection and Response (EDR) is crucial for finding and removing threats before damage occurs. And if a breach does happen—choose an EDR solution with ransomware rollback to undo changes and restore files.
How ThreatDown Addresses Ransomware
ThreatDown Bundles take a comprehensive approach to ransomware. Our integrated solutions combine EP, VPM, and EDR technologies, tailored to your organization’s specific needs, including:
- Advanced Web Protection: Blocking phishing websites ransomware gangs use for initial access.
- RDP Shield: Securing remote access points with Brute Force Protection.
- Continuous Vulnerability Scanning and Patch Management: Identifying and patching weaknesses before ransomware gangs can exploit them.
- Sophisticated EDR: Detecting and neutralizing advanced threats such as LockBit within the network.
- Ransomware Rollback: Reversing the impact of any successful attacks.

ThreatDown EDR detecting LockBit ransomware
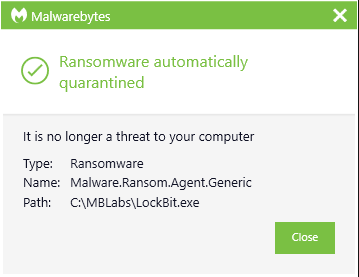
ThreatDown automatically quarantining LockBit ransomware
For resource-constrained organizations, select ThreatDown bundles offer Managed Detection and Response (MDR) services, providing expert monitoring and swift threat response to ransomware attacks—without the need for large in-house cybersecurity teams.
如有侵权请联系:admin#unsafe.sh