2024-1-26 05:9:30 Author: www.malwarebytes.com(查看原文) 阅读量:32 收藏
An ongoing campaign of malicious ads has been targeting Chinese-speaking users with lures for popular messaging applications such as Telegram or LINE with the intent of dropping malware. Interestingly, software like Telegram is heavily restricted and was previously banned in China.
Many Google services, including Google search, are also either restricted or heavily censored in mainland China. Having said that, many users will try to circumvent those restrictions by using various tools such as VPNs.
The threat actor is abusing Google advertiser accounts to create malicious ads and pointing them to pages where unsuspecting users will download Remote Administration Trojan (RATs) instead. Such programs gives an attacker full control of a victim’s machine and the ability to drop additional malware.
It may not be a coincidence that the malvertising campaigns are primarily focused on restricted or banned applications. While we don’t know the threat actor’s true intentions, data collection and spying may be one of their motives. In this blog post, we share more information about the malicious ads and payloads we have been able to collect.
Malicious ads
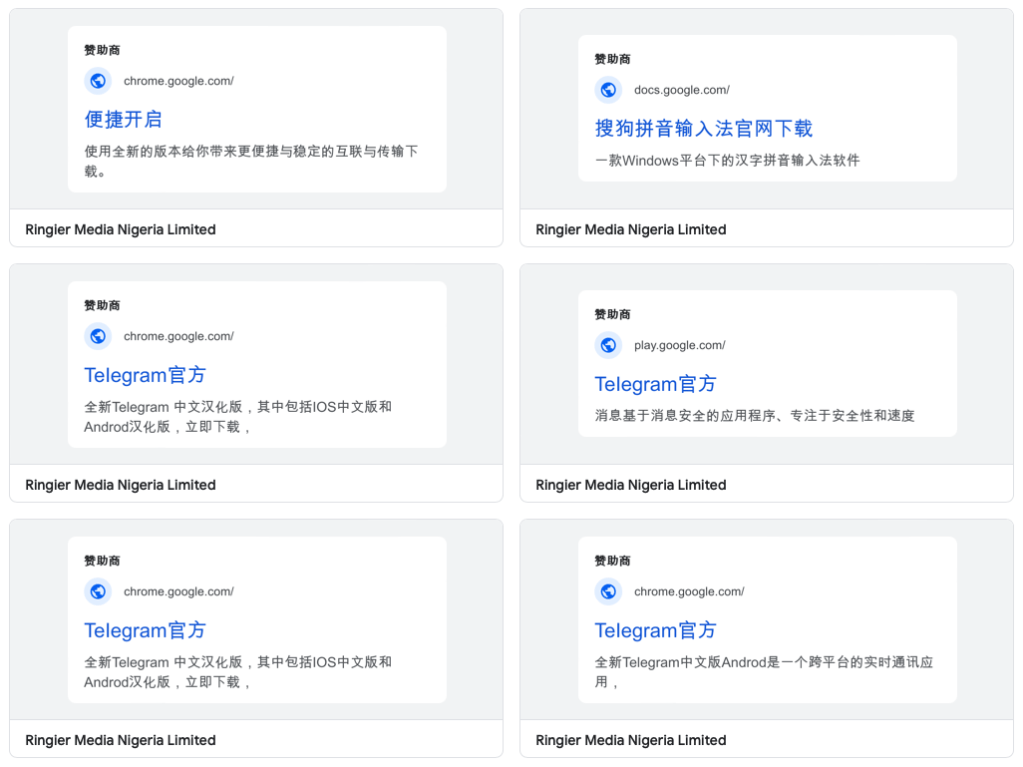
Visitors to google.cn are redirected to google.com.hk where searches are said to be uncensored. Doing a lookup for ‘telegram’ we see a sponsored search result.
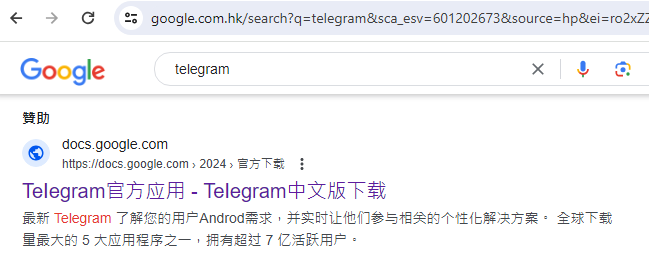
The following description is associated with this ad:
TeIegram official application – TeIegram Chinese version download docs.google.com https://docs.google.com › 2024 › Official download Latest Telegram Understand your users Androd needs and engage them with relevant personalized solutions in real time. One of the top 5 most downloaded apps in the world with over 700 million active users.
Here is an ad for ‘LINE’
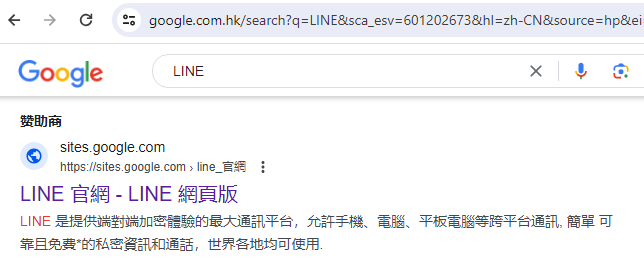
Description:
LINE is the largest communication platform that provides an end-to-end encrypted experience, allowing cross-platform communication across mobile phones, computers, tablets, etc. Simple, reliable, and free* private messages and calls can be used around the world.
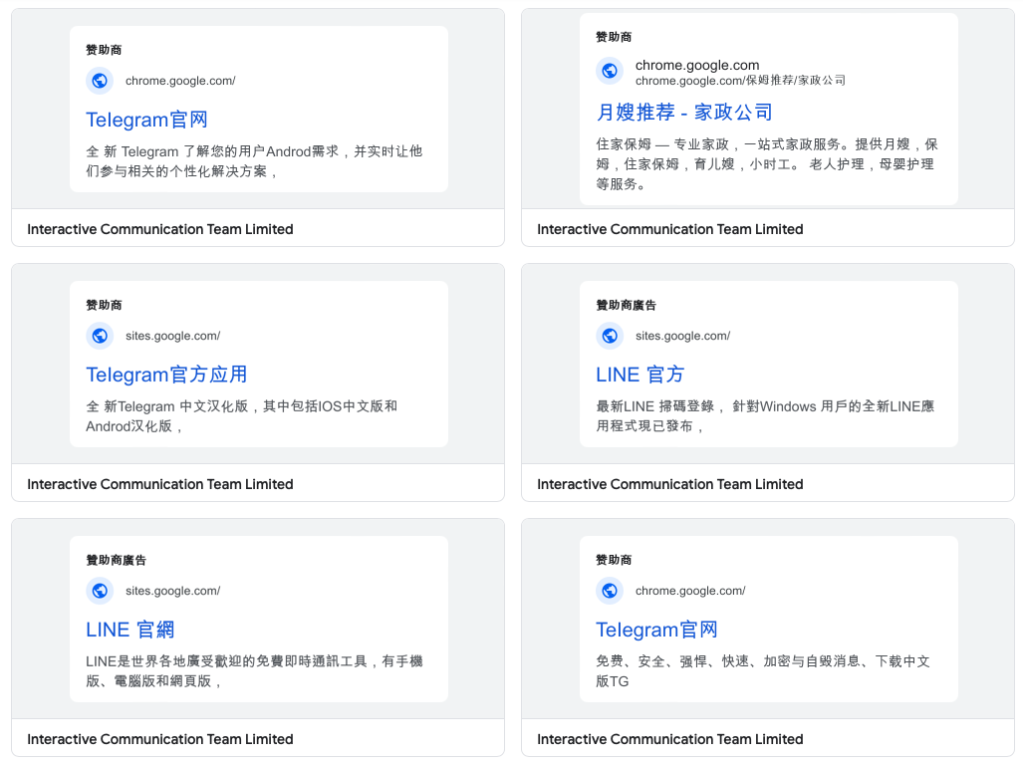
We identified two advertiser accounts behind those ads, both of them being associated with a user profile in Nigeria:
Due to the number of ads for each of these accounts (including many unrelated to these campaigns), we believe they may have been taken over by the threat actors.
Infrastructure
This threat actor seems to rely on Google infrastructure in the form of Google Docs or Google sites. This allows them to insert links for the download or even redirect to other sites they control.


Malware payloads
We collected a number of payloads from this campaign, all in MSI format. Several of those used a technique known as DLL side-loading, which consists of combining a legitimate application with a malicious DLL that gets loaded automatically.
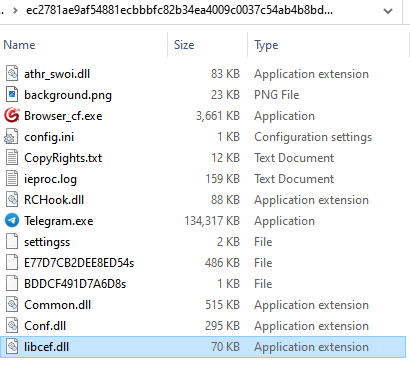
In the example above, the DLL is signed with a now revoked certificate from Sharp Brilliance Communication Technology Co., Ltd. which was also recently used to sign a PlugX RAT sample. (PlugX is a RAT from China that also performs DLL side-loading).
Not all dropped malware is new, in fact some were previously used in other campaigns and are variants of Gh0st RAT.
Active threat
A website and forum (bbs[.]kafan[.]cn) dedicated to security frequented by Chinese users keeps up with malware from these campaigns that they refer to as FakeAPP.
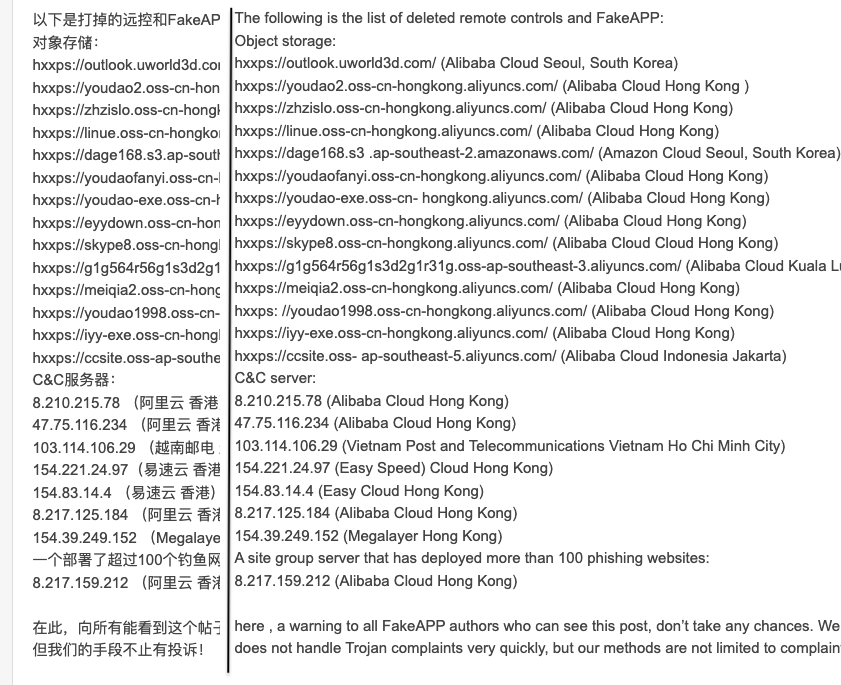
It also appears that the threat actor privileges quantity over quality by constantly pushing new payloads and infrastructure as command and control.
Online ads are an effective way to reach a certain audience, and of course they can be misused as well. People (such as activists) that live in countries where encrypted communication tools are banned or restricted will attempt to bypass these measures. It appears that a threat actor is luring potential victims with such ads.
The payloads are consistent with threats observed in the South Asia region, and we see similar techniques such as DLL side-loading that is quite popular with many RATs. This type of malware is ideal to gather information about someone and silently dropping additional components if and when necessary.
We have notified Google regarding the malicious ads and have reported the supporting infrastructure to the relevant parties.
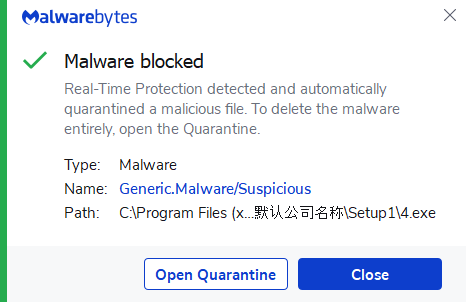
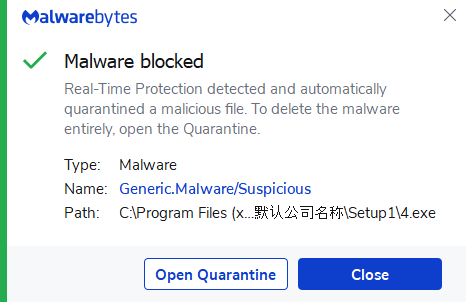
Malwarebytes detects the malicious payloads upon execution.
Indicators of Compromise
Fake domains
telagsmn[.]com
teleglren[.]com
teleglarm[.]com
Redirectors
5443654[.]site
5443654[.]world
Payloads
CS-HY-A8-bei.msi 63b89ca863d22a0f88ead1e18576a7504740b2771c1c32d15e2c04141795d79a w-p-p64.msi a83b93ec2a5602d102803cd02aecf5ac6e7de998632afe6ed255d6808465468e mGtgsotp_zhx64.msi acf6c75533ef9ed95f76bf10a48d56c75ce5bbb4d4d9262be9631c51f949c084 cgzn-tesup.msi ec2781ae9af54881ecbbbfc82b34ea4009c0037c54ab4b8bd91f3f32ab1cf52a tpseu-tcnz.msi c08be9a01b3465f10299a461bbf3a2054fdff76da67e7d8ab33ad917b516ebdc
C2s
47.75.116[.]234:19858 216.83.56[.]247:36061 45.195.148[.]73:15628
如有侵权请联系:admin#unsafe.sh