2024-2-21 03:3:56 Author: www.malwarebytes.com(查看原文) 阅读量:18 收藏
In an act of exquisite trolling, the UK’s National Crime Agency (NCA) has announced further details about its disruption of the LockBit ransomware group by using the group’s own dark web website.

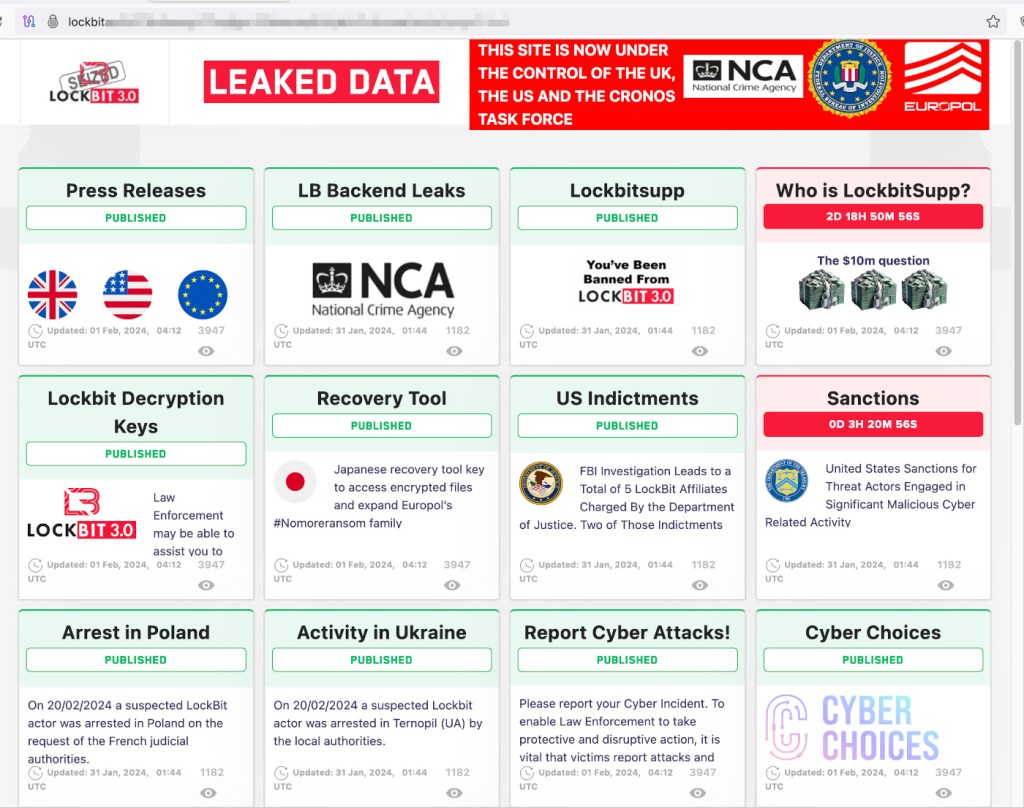
Since the demise of Conti in 2022, LockBit has been unchallenged as the most prolific ransomware group in the world. In the last 12 months it has racked up more than two and half times as many known attacks as its closest rival. That all stopped yesterday, though, when the LockBit site was replaced with a banner decorated with the flags and badges of the countries and agencies that cooperated to “disrupt” it. The banner read:
This site is now under the control of The National Crime Agency of the UK, working in close cooperation with the FBI and the international law enforcement task force, ‘Operation Cronos’.
It also promised more information would be revealed today at 11:30 GMT. It didn’t disappoint. There was a press release, of course, and a video:
— National Crime Agency (NCA) (@NCA_UK) February 20, 2024The NCA reveals details of an international disruption campaign targeting the world’s most harmful cyber crime group, Lockbit.
Watch our video and read on to learn more about Lockbit and why this is a huge step in our collective fight against cyber crime. pic.twitter.com/m00VFWkR9Z
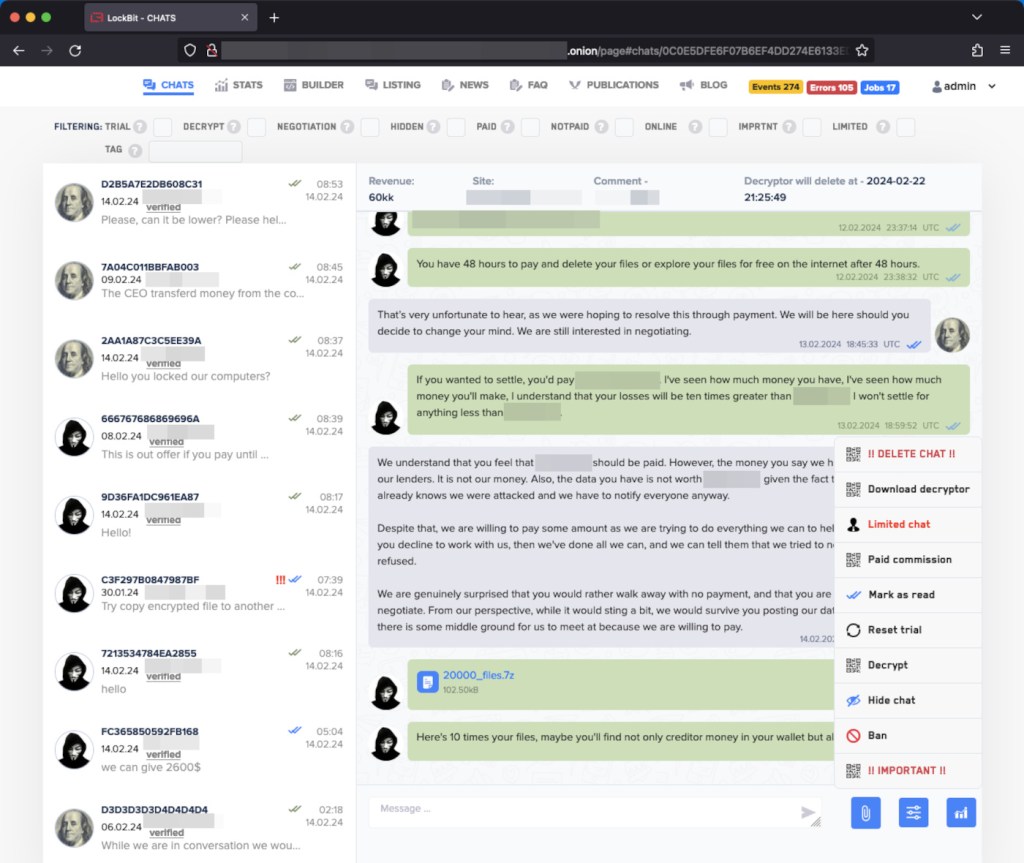
But the real treat was an updated version of the LockBit website that returned it to something resembling its former self. However, some crucial details had changed. Until yesterday, the secret dark web site was used to list details of the organizations being held to ransom by LockBit. Green squares represented companies whose data had been leaked. Timers on the red squares showed companies under threat of a leak just how long they had until their stolen data would be published.
Not any more, though.
In a graphic illustration of just how comprehensively the LockBit group has been compromised, the green squares now detail published information about the takedown, while red squares tease further reveals for the coming days.
Today, after infiltrating the group’s network, the NCA has taken control of LockBit’s services, compromising their entire criminal enterprise.
As well as taking over the leak site, law enforcement agencies have taken over LockBit’s administration environment, seized the infrastructure used by LockBit’s data exfiltration tool, Stealbit, captured over 1,000 decryption keys, and frozen 200 cryptocurrency accounts.
The group’s source code has also fallen into the hands of law enforcement, along with “a vast amount of intelligence” from its systems. Criminal affiliates who logged into the compromised environment were warned that the NCA knows all about their activities too, and the NCA reports that 28 servers belonging to LockBit affiliates have been taken down, too.
Two “LockBit actors” have been arrested in Poland and Ukraine, and the US Department of Justice has announced that two defendants responsible for using LockBit in ransomware attacks have been charged, are in custody, and will face trial in the US. It also unsealed indictments against two Russian nationals, for conspiring to commit LockBit attacks.
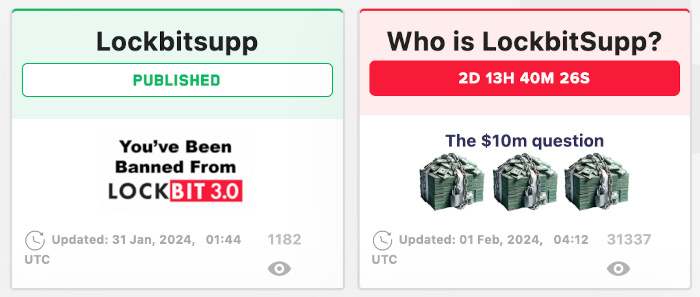
There are numerous reveals promised for the next few days, but the most tantalising is the imminent uncloaking of LockBit’s leader and spokesperson, LockBitSupp.
The NCA could have put the information about the takedown anywhere, but it didn’t; it did something memorable, humorous, and deliberately humiliating with it. In other words, it mimicked perfectly the way that ransomware gangs troll the world and each other. In doing so, the NCA signaled that it knows all about LockBit and the broader community of criminals it belongs to. It knows that LockBit’s affiliates and rivals will be watching, and looking over their shoulder.
Good times.
How to avoid ransomware
- Block common forms of entry. Create a plan for patching vulnerabilities in internet-facing systems quickly; and disable or harden remote access like RDP and VPNs.
- Prevent intrusions. Stop threats early before they can even infiltrate or infect your endpoints. Use endpoint security software that can prevent exploits and malware used to deliver ransomware.
- Detect intrusions. Make it harder for intruders to operate inside your organization by segmenting networks and assigning access rights prudently. Use EDR or MDR to detect unusual activity before an attack occurs.
- Stop malicious encryption. Deploy Endpoint Detection and Response software like ThreatDown EDR that uses multiple different detection techniques to identify ransomware, and ransomware rollback to restore damaged system files.
- Create offsite, offline backups. Keep backups offsite and offline, beyond the reach of attackers. Test them regularly to make sure you can restore essential business functions swiftly.
- Don’t get attacked twice. Once you’ve isolated the outbreak and stopped the first attack, you must remove every trace of the attackers, their malware, their tools, and their methods of entry, to avoid being attacked again.
You can learn more about the threat of big game ransomware like LockBit and ALPHV in our 2024 State of Malware report.
如有侵权请联系:admin#unsafe.sh