A new phishing campaign is targeting U.S. organizations with the intent to deploy a remote access trojan called NetSupport RAT.
Israeli cybersecurity company Perception Point is tracking the activity under the moniker Operation PhantomBlu.
"The PhantomBlu operation introduces a nuanced exploitation method, diverging from NetSupport RAT's typical delivery mechanism by leveraging OLE (Object Linking and Embedding) template manipulation, exploiting Microsoft Office document templates to execute malicious code while evading detection," security researcher Ariel Davidpur said.
NetSupport RAT is a malicious offshoot of a legitimate remote desktop tool known as NetSupport Manager, allowing threat actors to conduct a spectrum of data gathering actions on a compromised endpoint.
The starting point is a Salary-themed phishing email that purports to be from the accounting department and urges recipients to open the attached Microsoft Word document to view the "monthly salary report."
A closer analysis of the email message headers – particularly the Return-Path and Message-ID fields – shows that the attackers use a legitimate email marketing platform called Brevo (formerly Sendinblue) to send the emails.
The Word document, upon opening, instructs the victim to enter a password provided in the email body and enable editing, followed by double-clicking a printer icon embedded in the doc to view the salary graph.
Doing so opens a ZIP archive file ("Chart20072007.zip") containing one Windows shortcut file, which functions as a PowerShell dropper to retrieve and execute a NetSupport RAT binary from a remote server.
"By using encrypted .docs to deliver the NetSupport RAT via OLE template and template injection, PhantomBlu marks a departure from the conventional TTPs commonly associated with NetSupport RAT deployments," Davidpur said, adding the updated technique "showcases PhantomBlu's innovation in blending sophisticated evasion tactics with social engineering."
Growing Abuse of Cloud Platforms and Popular CDNs
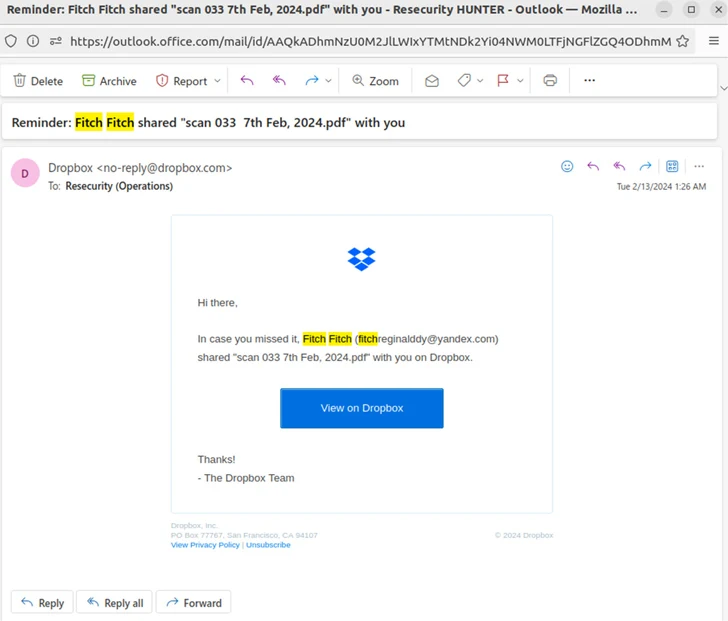
The development comes as Resecurity revealed that threat actors are increasingly abusing public cloud services like Dropbox, GitHub, IBM Cloud, and Oracle Cloud Storage, as well as Web 3.0 data-hosting platforms built on the InterPlanetary File System (IPFS) protocol such as Pinata to generate fully undetectable (FUD) phishing URLs using phishing kits.
Such FUD links are offered on Telegram by underground vendors like BulletProofLink, FUDLINKSHOP, FUDSENDER, ONNX, and XPLOITRVERIFIER for prices starting at $200 per month as part of a subscription model. These links are further secured behind antibot barriers to filter incoming traffic and evade detection.
Also complementing these services are tools like HeartSender that make it possible to distribute the generated FUD links at scale. The Telegram group associated with HeartSender has nearly 13,000 subscribers.
"FUD Links represent the next step in [phishing-as-a-service] and malware-deployment innovation," the company said, noting attackers are "repurposing high-reputation infrastructure for malicious use cases."
"One recent malicious campaign, which leveraged the Rhadamanthys Stealer to target the oil and gas sector, used an embedded URL that exploited an open redirect on legitimate domains, primarily Google Maps and Google Images. This domain-nesting technique makes malicious URLs less noticeable and more likely to entrap victims."
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.