In just a few years, the Flipper Zero has become so popular that it’s now surrounded by many myths. It’s no wonder that people in power are trying to make the Flipper Zero illegal. As you might have seen in the news, the Canadian government plans to ban the Flipper Zero as part of their efforts to combat auto theft.
TLDR: The Canadian government has proposed a ban on the Flipper Zero because it claims the device is being used to steal cars. This is not true.
Sign the petitionbefore the proposal is passed.
We believe that proposals like this are harmful to security and slow down technological progress. They are usually made by those who do not really understand how security works and will do nothing to solve the car theft problem. In this post, we’ll explain why banning the Flipper Zero instead of fixing security threats is not the solution.

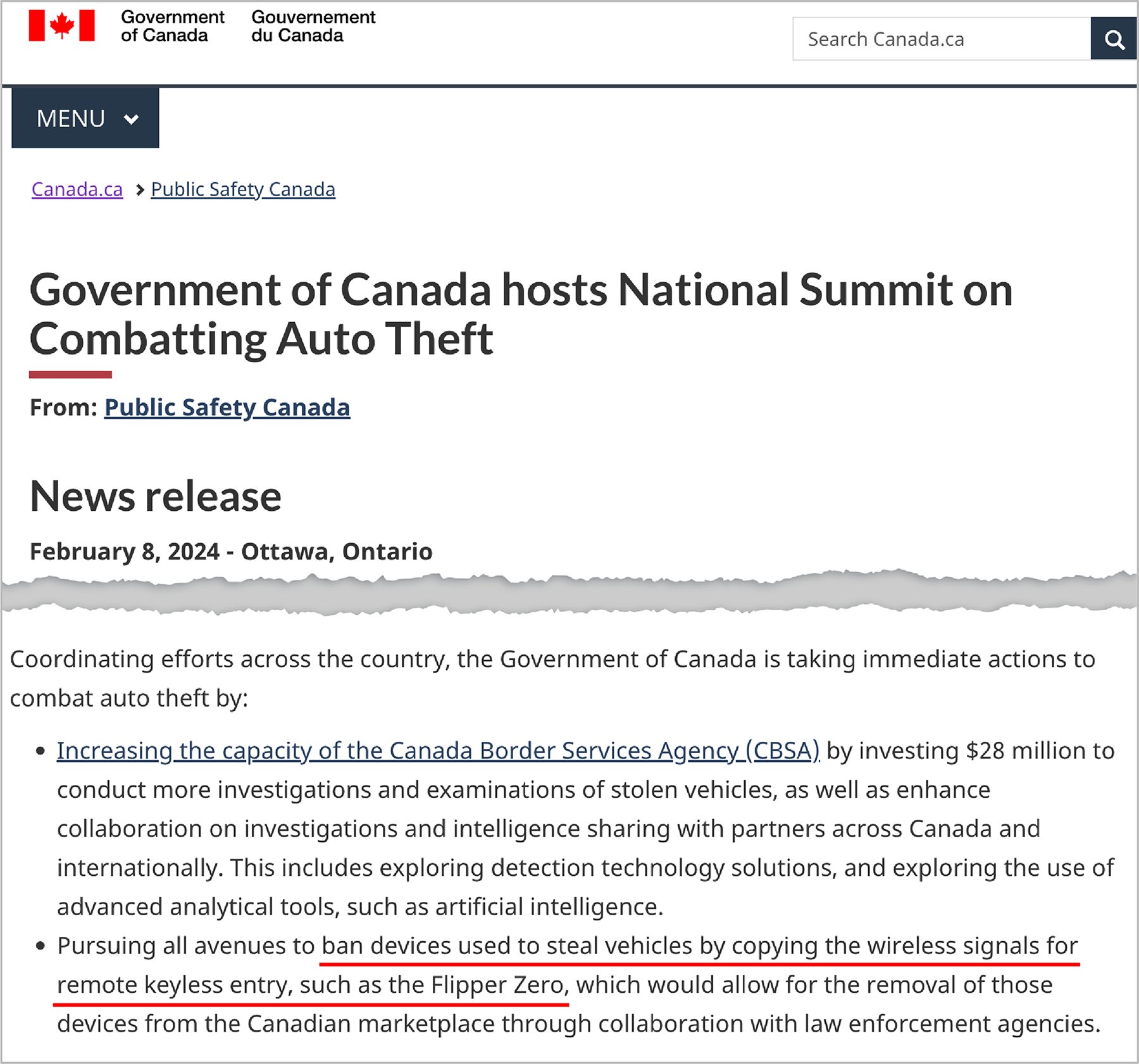
At the National Summit on Combatting Auto Theft held on February 8, François-Philippe Champagne, the Canadian Minister of Innovation, Science and Industry, announced measures to combat the rise in car theft in Canada. As one of the measures to address this issue, he proposed to ban the Flipper Zero because he claims the device is being used to steal cars with keyless entry systems🤯. (Spoiler: this is not true)
Francois-Philippe Champagne also tweeted about the announcement, which received close to 900K views and 800 replies, becoming one of the most criticized tweets in his career. Here are some replies:
By the way, at my CanSecWest conference some researchers recently showed how to use a Raspberry Pi to relay bluetooth to unlock poorly secured Bluetooth car locks. Does this mean you are going to try to outlaw computers too?
— dragosr (@dragosr) February 9, 2024
If you knew anything about technology you would know the flipper and others are just simple ARM processors with basic sensors attached. Nothing ground breaking this will not stop a thing but makes it look like your doing something. The trick of politicians everywhere and it is…
— Adam Taylor (@ATaylorFPGA) February 9, 2024
The announced plans to ban the Flipper Zero also caused a discussion on Hacker News (see here and here). Many users have said this ban won't fix the issue of insecure cars:
The Flipper Zero is a general-purpose tool and STEM educational device. By banning the device, a country would be setting back their workforce of engineers and scientists a bit.
How can you use a Flipper Zero to steal a car? Flipper Zero can't crack hard encryption.
Is the real problem that cars were made with security that they already knew was negligently weak at the time? If so, is a recall of those cars more appropriate?
So if I'm reading this right, they're banning something that is too underpowered to run the exploits people are using to steal cars (which are only possible in the first place because car companies' threat model is mostly about their customers rather than thieves) in order to pretend to do something about car theft
The Canadian Repair Coalition has issued a statement regarding our situation.
Simplistic solutions, such as banning a device without a thorough understanding of its functions and benefits, are counterproductive, and we encourage the government to do better.
The Canadian government news release mentions that the announced ban on the Flipper Zero is one of the measures to combat the theft of cars with keyless entry systems. To find out if the Flipper Zero can be used to steal such cars, it's important to understand how keyless entry systems work and what car thieves do to hack them.
What is a keyless entry system?
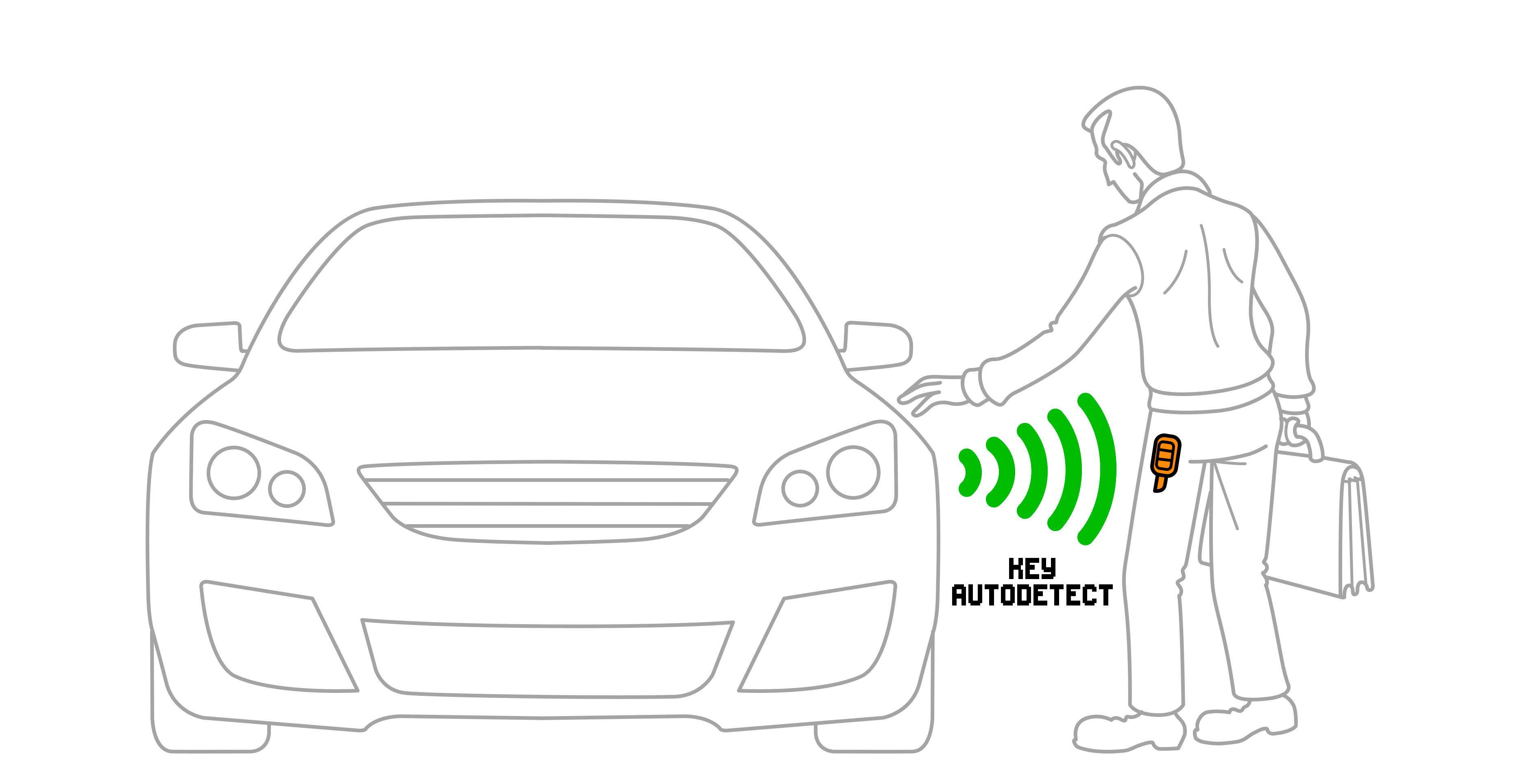
Cars with keyless entry systems are designed to unlock when the key fob is in close proximity without requiring the owner to press a button on the key fob. Simply touching the door handle is enough to trigger the car's sensors and unlock the doors. The engine then starts with a press of a button on the dashboard when the key is nearby. After that, the key fob won't be necessary until the next stop.
Once again, the engine will remain running and the doors unlocked — even if the original key fob is not in proximity of the car, which is exactly what car thieves exploit.
How thieves hack keyless entry systems
To steal a car with a keyless entry system, thieves work in pairs and use radio repeaters to trick the car into believing the key fob is nearby when it's actually inside the victim's house.
To do this, thieves establish a connection between the car and the key fob using two repeaters. They hold one repeater near the car and another as close as possible to the house to reach the key fob inside. The thief next to the house uses a repeater with a large antenna that can pick up signals even through a wall. Since key fobs are usually left near the front door, a thief with such a repeater can easily locate them. Once connected, the car and the key fob assume they are near each other, which allows the thieves to unlock the car door and start the engine.
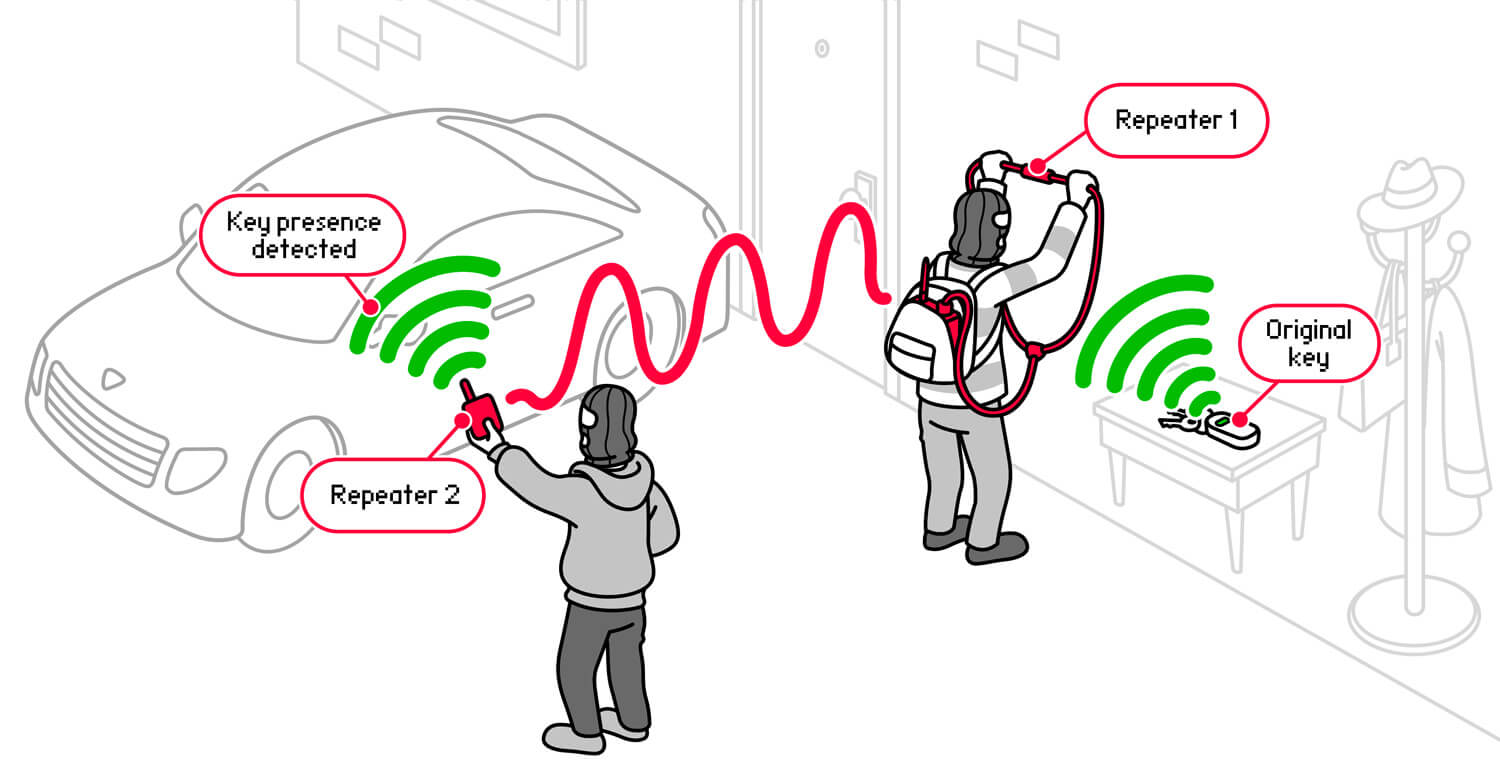
The communication protocol between a key fob and a car is bidirectional. Many keyless repeaters can relay signals in both directions with an attack range of up to 1 kilometer. Others relay signals only from the car to the key fob — their attack range is limited by the key fob signal range.
0:00
/0:34
[video] CCTV footage showing how thieves steal cars with keyless entry systems

To transmit signals to key fobs through walls, thieves need huge antennas and powerful repeaters. All video-documented cases of car theft show that theft equipment takes up a lot of space in thieves' backpacks.
What hardware thieves actually use
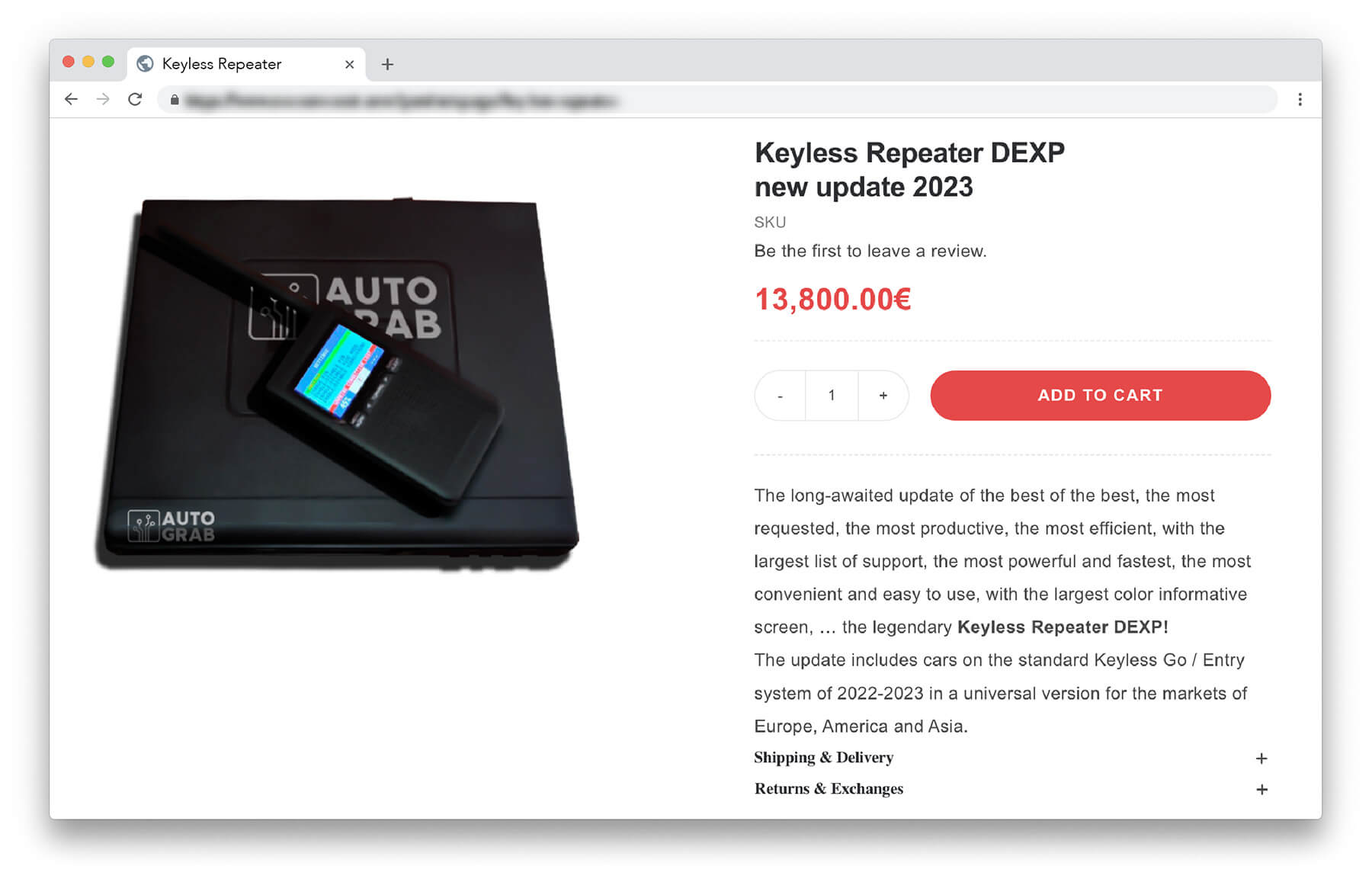
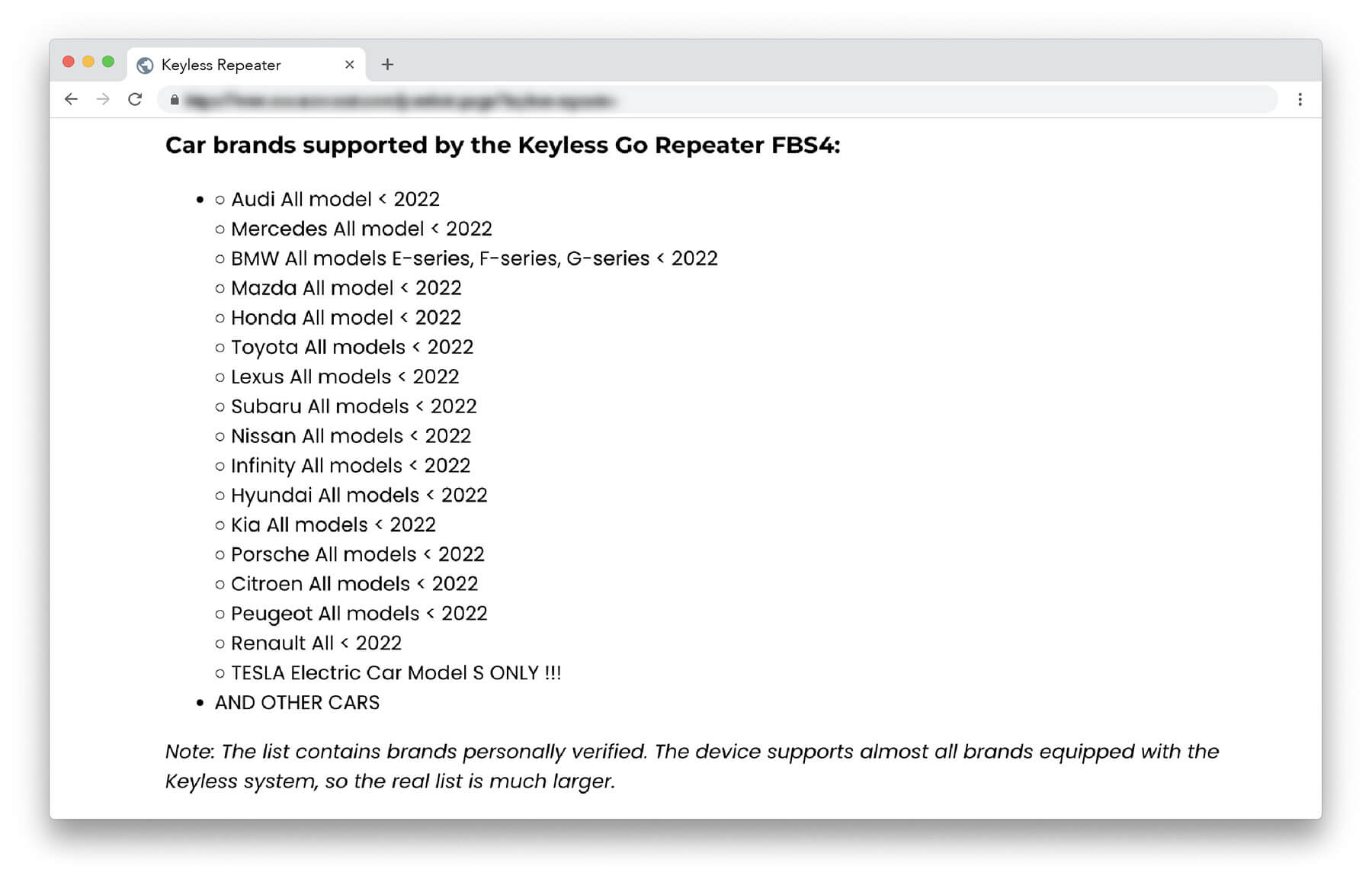
Car theft equipment for every car brand can be found on special websites for car thieves. Just google "keyless repeater" to get a long list of websites that offer car theft tools with worldwide shipping, with prices ranging from €5,000 to €14,000.
After learning about the sophisticated tools thieves use, let’s have a look at the Flipper Zero’s capabilities. Can it actually be used to steal cars?

There are many videos on social media where kids promise to “hack the Pentagon” using a Flipper Zero to gain more views. Such content has created lots of myths and is used by journalists who don't bother with fact-checking. It's not surprising that some politicians have started to propose bans based on false information. To fix this, we'll try to bust some popular myths surrounding the Flipper Zero by answering the questions below:
— Can you steal a car with the Flipper Zero?
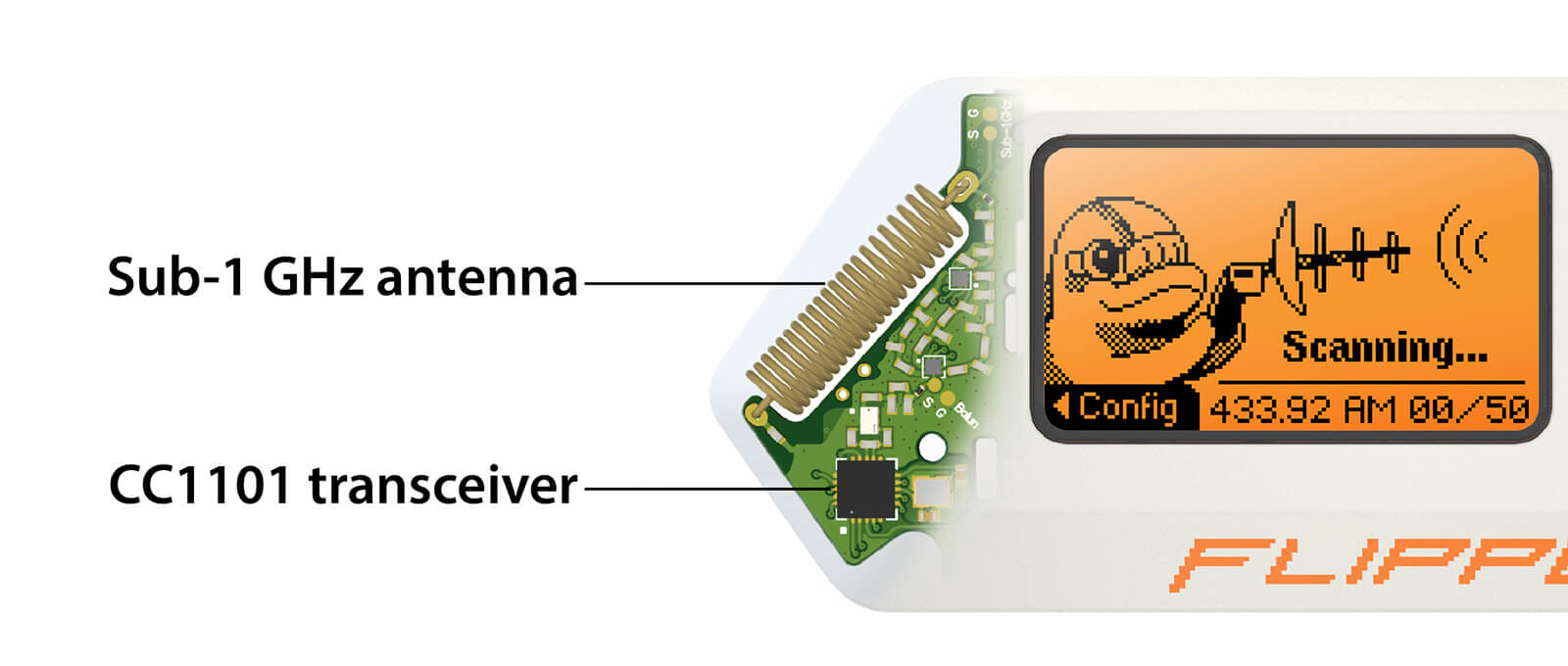
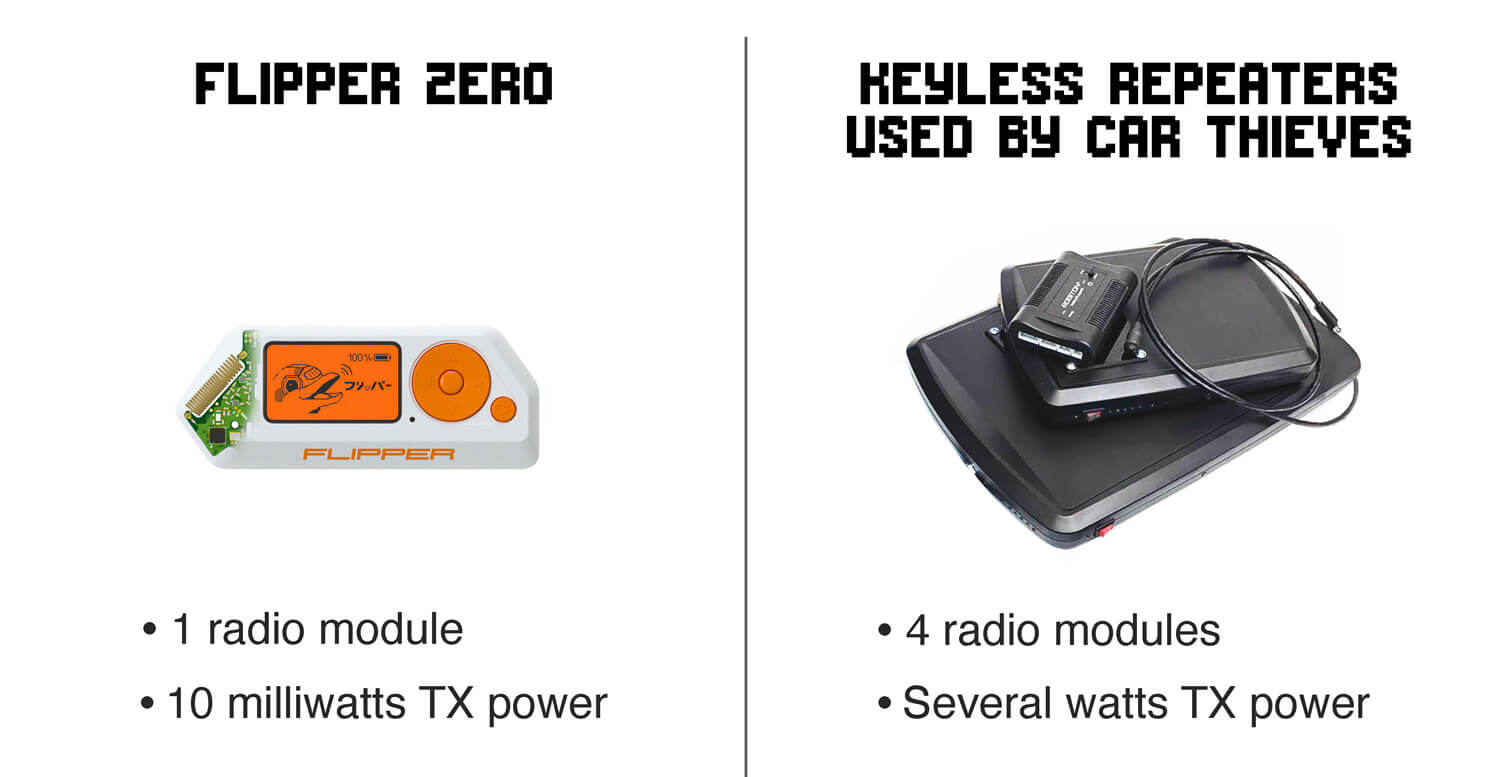
We are not aware of any officially confirmed cases of theft using a Flipper Zero. This is because the device has limited functionality and can't be used as a repeater to attack keyless entry systems. The Flipper Zero is equipped with only one sub-1 GHz radio module, while keyless repeaters have 4 radio modules: one for communication with the car, another one for communication with the key fob, and two for communication between the repeaters.
— But the Flipper Zero operates at the same frequencies as remote controls
Yes, the Flipper Zero can indeed receive and decode radio signals. However, intercepting the radio signal from the remote control won’t be enough to unlock a modern car because they use encryption to securely provide access. The most popular encryption system used in car keys is rolling code, where every press of the key fob button generates a different encrypted radio signal. This security feature helps prevent basic attacks that only require a $2 radio module.
— What is the difference between static and rolling code?
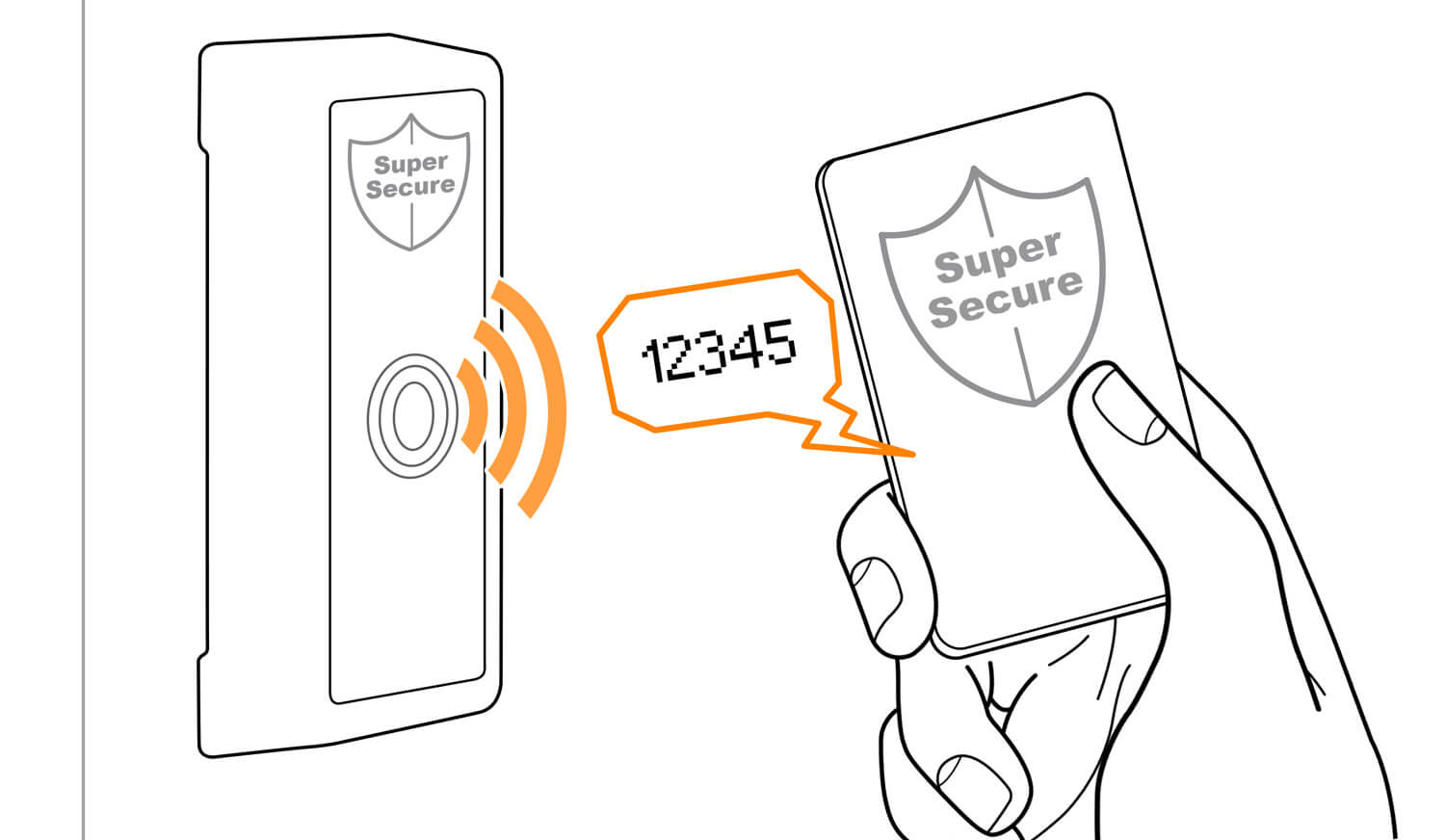
A static code is a fixed set of numbers access control systems use to grant access. Every time the user presses a button on a remote, the same set of numbers is sent. It is enough to capture such a signal once, which can then be endlessly replayed to grant access.
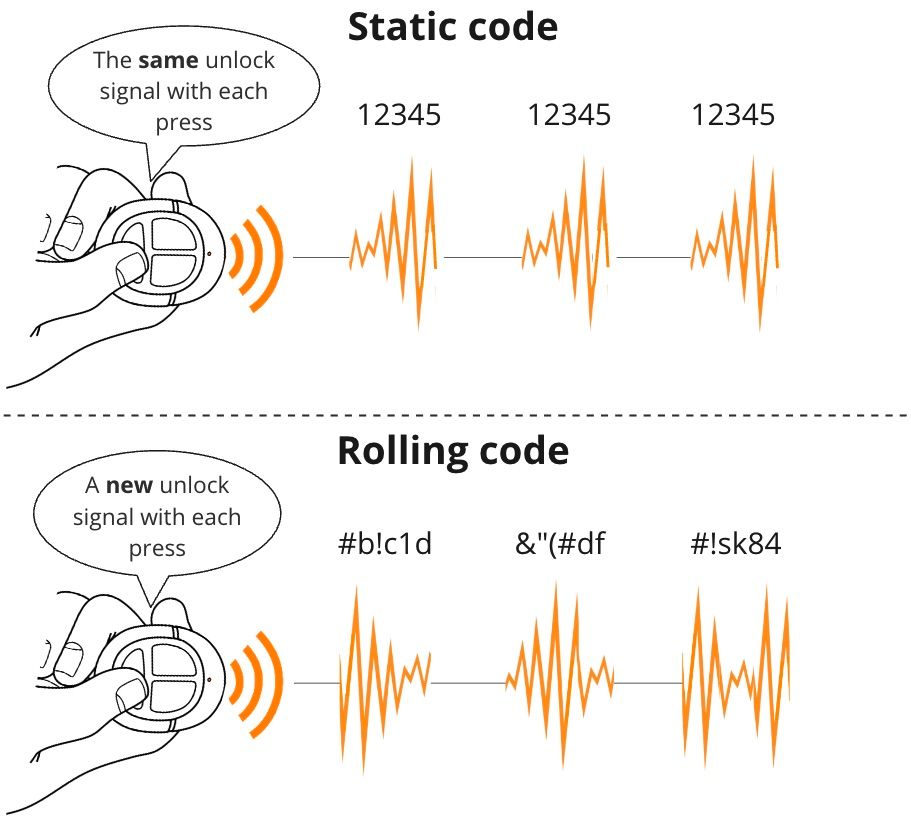
A rolling code is a changing set of numbers. This means that whenever the user presses a button on a remote, it generates a unique code based on a sequence known only by the access control system. Simply capturing a signal and replaying it wouldn't provide access since this set of numbers has already been used.
Although cars using static codes were discontinued around 20 years ago, they are still in use. The main vulnerability of such cars is that their radio signals can be easily captured and replayed without sophisticated tools. In fact, static codes are so insecure that they can be "hacked" with a piece of wire connected to a PC's microphone input:
0:00
/1:58
[video] Demonstration on how to receive a signal from a radio remote using a piece of wire
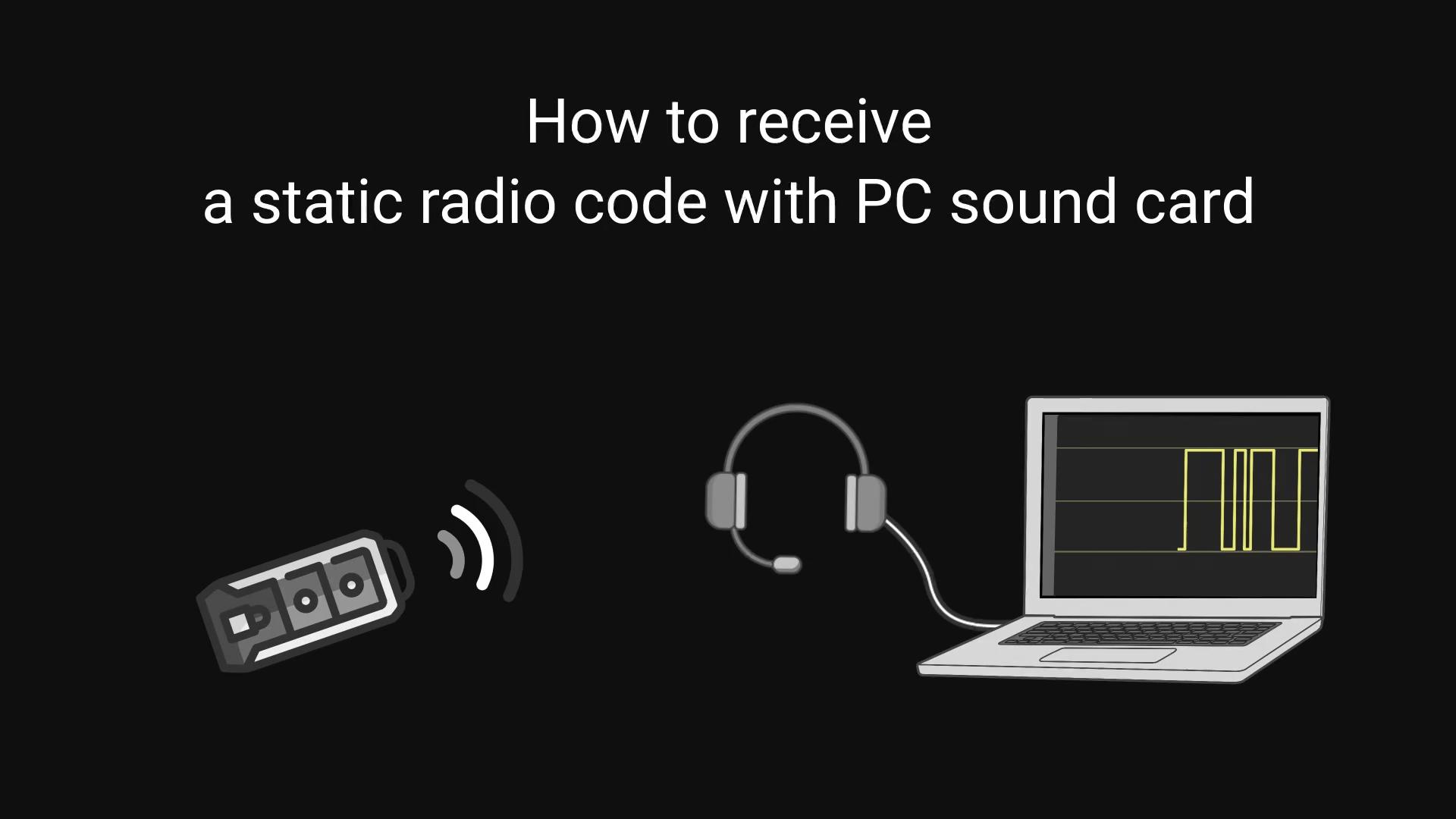
Technical details (click to expand)
- The key fob operates at a frequency of
433 MHz. This generates interference in the microphone circuit, which is captured as an audio signal when recording sound through the microphone. On-Off keying (OOK)modulation encodes data through pulse widths of reasonably low frequency (i.e., slowly), which allows capturing the intervals between pulses, even though the PC sound card itself cannot capture a signal of a frequency as high as433 MHz.The diodeis needed to allow only the positive half-wave of oscillations to pass into the microphone input. Since the amplitude of oscillations in the resonant circuit is symmetrical, if they are fed directly into the microphone input without a diode, the digitized signal will be nullified.The capacitoris required to block direct current (DC) from the microphone port from reaching the resonant circuit. Sound cards always supply a slight direct current to the microphone port, because it is needed for a microphone to work.- In the video above, the audio is recorded using Audacity. The resulting .WAV file is processed in Universal Radio Hacker (URH) to decode the signal using the Princeton preset.
This example shows the absurdity of all attempts to ban devices like the Flipper Zero. To protect against the interception of radio signals, it would be necessary to ban all electronics, including headphones, which is unrealistic.
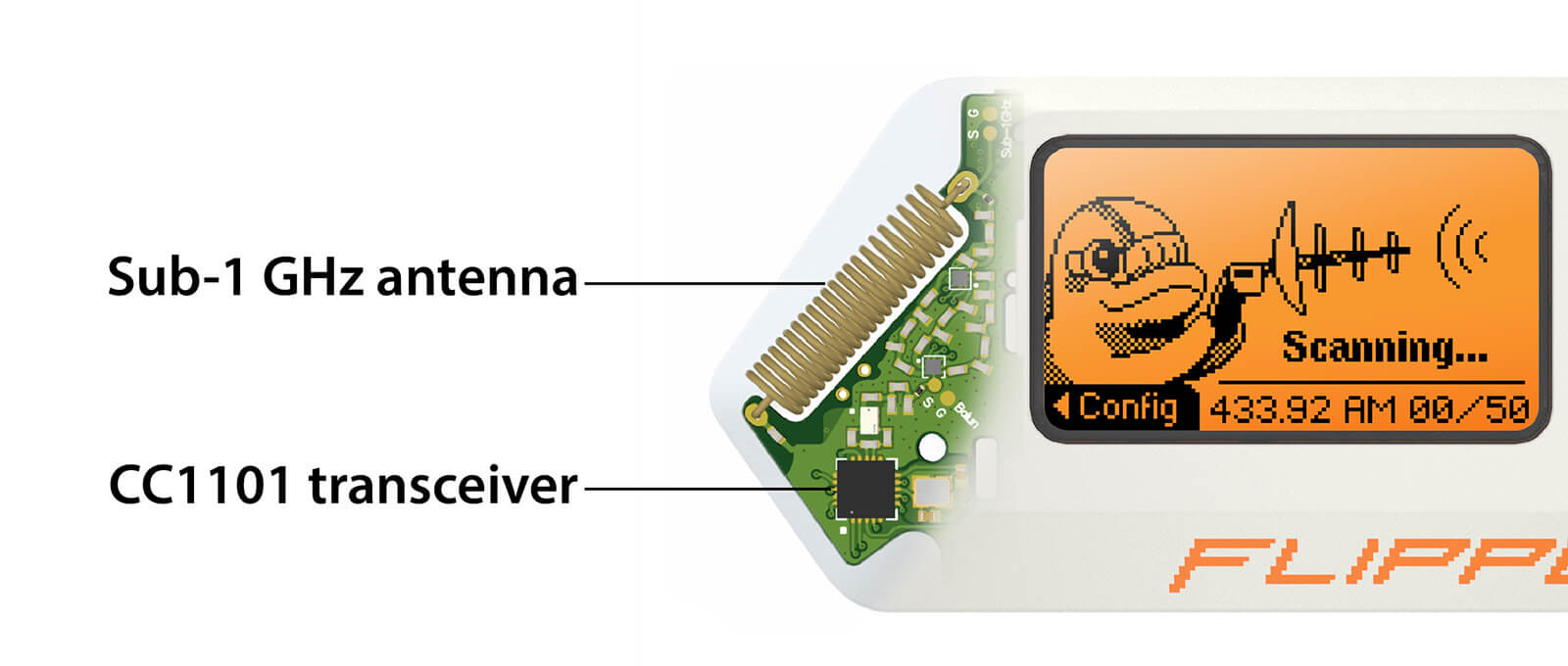
The Flipper Zero is built with hardware components used in thousands of devices ranging from radio toys to educational DIY kits. For example, the CC1101 radio transceiver inside the Flipper Zero has been widely used since its release in 2007. The problem is not in the available radio hardware, but rather in the insecurity of outdated access control systems.
Security through obscurity is a cybersecurity concept where a system's design is kept hidden from attackers to prevent them from exploiting its vulnerabilities.
However, once the inner workings of a system are exposed (which is only a matter of time), its vulnerabilities become evident, leaving it open to exploitation.
- In 2012, a vulnerability was discovered in hotel room locks manufactured by Onity. These locks were widely used in millions of hotel rooms across the globe. The discovery revealed that with a simple device that could be plugged into the DC port found on these locks, a person could bypass the card reader and open the lock within seconds.
- In the GSM mobile communication standard, the A5/1 encryption algorithm has been used for data encryption since 1987, with its security relying on the secrecy of the algorithm. The standard became widely adopted, but in 1994, the algorithms were disclosed, and millions of mobile phones became vulnerable to wiretapping. en.wikipedia.org/wiki/A5/1
Instead of banning cybersecurity tools capable of finding vulnerabilities in security systems, these vulnerabilities must be fixed. The cybersecurity industry has long recognized that bans do not fix insecure systems, but instead only cause more problems by creating a false impression that proper measures have been taken. Let’s have a look at real-life examples.
HTTP vs HTTPS
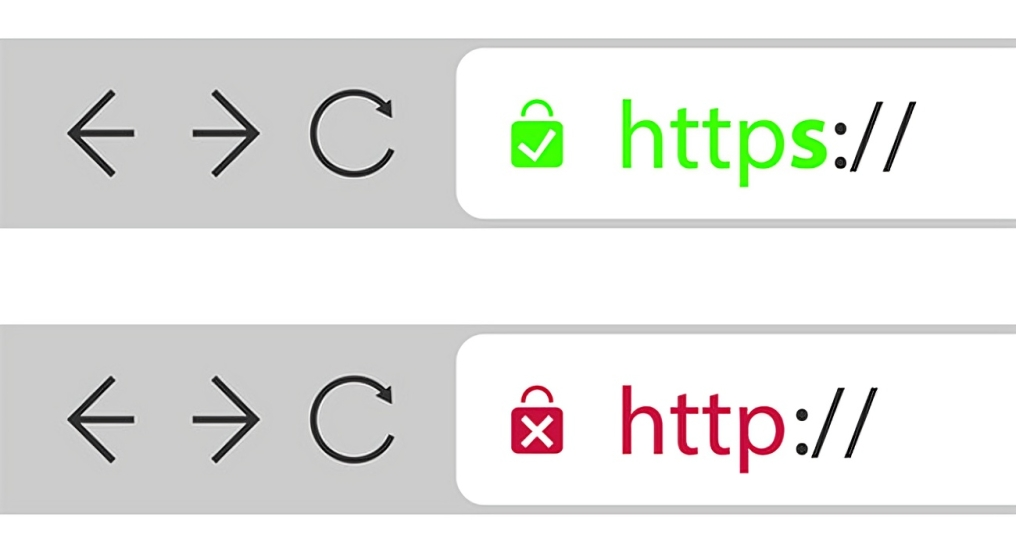
The current state of access control systems can be compared to the evolution of the World Wide Web (WWW) protocol . In the past, websites used the insecure HTTP protocol, which lacked encryption. This made it vulnerable to data interception by anyone along the way or via Wi-Fi. Since internet traffic was routed through the equipment of many companies, there was a high risk of data interception.
The HTTP protocol was replaced by HTTPS ("s" meaning secure), which fixed security vulnerabilities by providing data encryption. HTTPS has become the standard for secure communication on the web.
Credit Cards: magnetic stripe vs chip
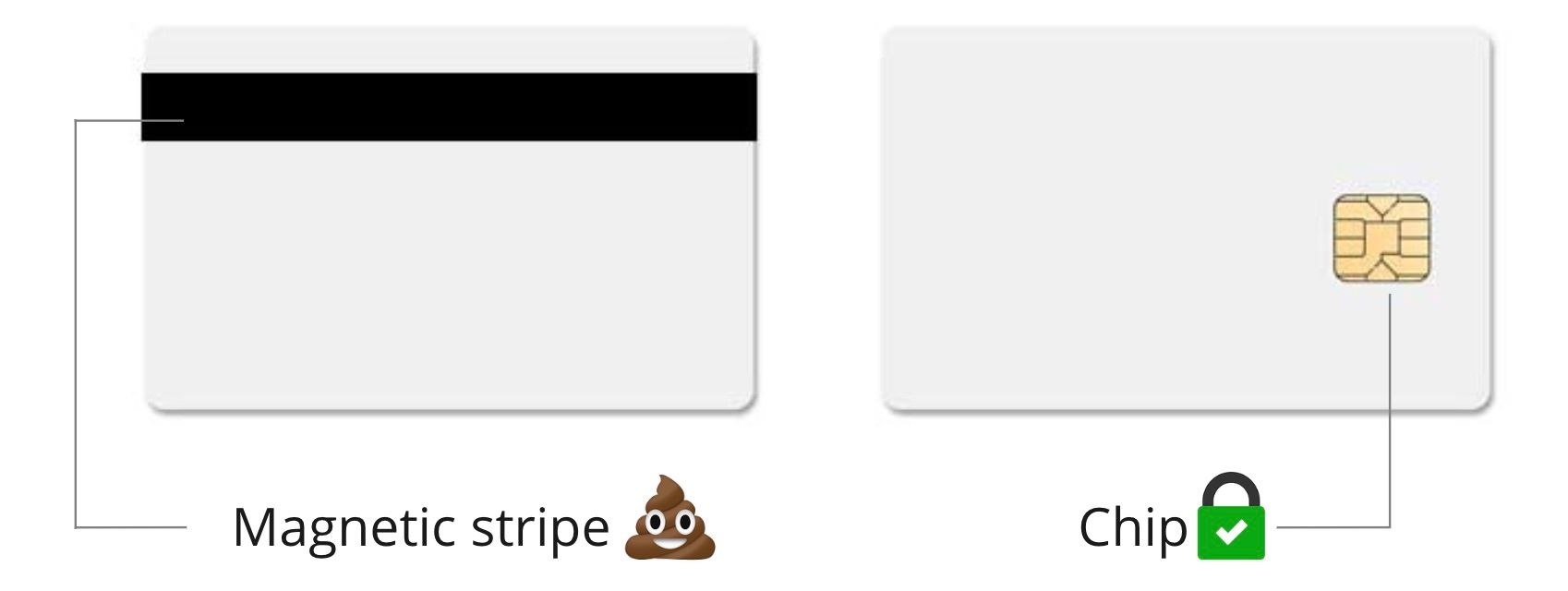
In the past, bank cards used magnetic stripe technology to store and transmit cardholder data. These magnetic stripes were easy to clone or skim. Criminals used skimming devices to steal card information, which allowed them to clone cards for unauthorized transactions.
To fight credit card fraud, chip cards were introduced. These cards use advanced technology with embedded microchips that generate unique transaction data for each transaction, making it extremely difficult for criminals to clone these cards.

We hope we've properly explained why banning the Flipper Zero makes no sense. Such measures do nothing but harm innovation and security. Now, it is our objective to convey this information to the government of Canada. Please, sign the petition.

What else can I do?
- If you are in Canada, contact your Member of Parliament and share this information with them. If you are a member of a political party in Canada, please pass this information on to its representatives.
- Get in touch with us if you believe you can help
[email protected] - We express our gratitude to the Canadian members of our community who have created a public initiative to save the Flipper Zero: saveflipper.ca