·
移动应用安全与风控
2.1 常用工具
2.1.1 越狱版商店Cydia
要安装Cydia首先需要对苹果设备进行越狱,只有越狱后的设备才能正常使用Cydia。如果对越狱不太了解,推荐使用爱思助手对设备进行越狱,可以通过图形界面引导越狱,如下图所示:
Cydia下方的工具栏共五个按键,分别是“Cydia”、“软件源”、“变更”、“已安装”、“搜索”,下面说明其具体功用。先从最重要的源添加,即“管理”讲起。
2.1.1 Root工具Magisk
本节主要介绍使用Magisk对Android设备进行Root。对设备进行Root首先需要对设备的Bootloader 进行解锁,只有解锁后才可以通过刷机等一系列操作完成Root。现在国内大部分手机厂商已经彻底关闭了Bootloader解锁方式。因此这里使用Google出产 pixel 系列手机进行Root演示。
将手机的 BootLoader 状态进行解锁,开发者模式下,开启 OEM unlocking,如下图所示:
adb reboot bootloader
fastboot flashing unlock 或 fastboot oem unlock
adb pull /sdcard/Download/magisk_patched-23000_T5HA4.img .
adb reboot bootloader
fastboot boot magisk_patched-23000_T5HA4.img
备注:Root时刷入的patch后的boot.img需要和目标设备的系统版本保持一致,否则将导致系统无法开启wifi等问题。
2.1.1 Hook框架EdXposed
上一节中对Android设备Root时已经安装了Magisk。EdXposed可通过Magisk进行安装,在其模块功能中搜索Riru和EdXposed模块并选择适配自己系统的进行安装。同时安装EdXposedManager客户端方便后续管理EdXposed插件。打开EdXposedManager软件首页中展示EdXposed框架已激活,说明EdXposed框架已经完美安装到当前的设备中。如果显示的未激活,可能是因为选择Riru和EdXposed模块与当前系统不匹配,在Magisk中删除之前安装的模块,重新下载对应版本的模块即可。EdXposed正确安装成功后,如下图所示:
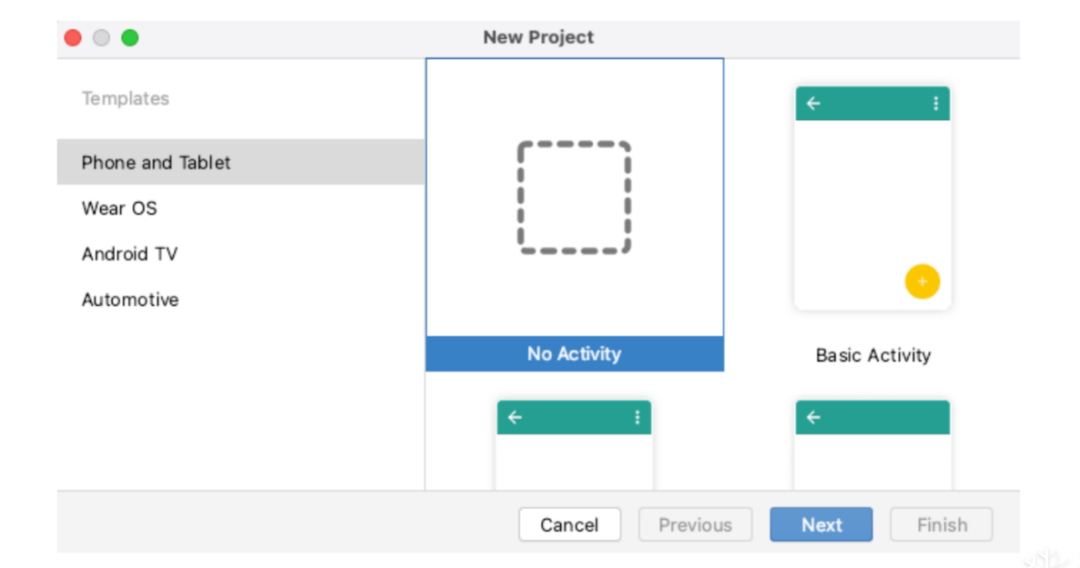
创建Xposed的模块时可根据交互情况选择创建的工程模版。此处为了让大家快速上手Xposed模块的开发,通过简单的无需交互的范例进行讲解。首先通过Android Studio 创建一个No Activity的工程,如下图所示:
<meta-data android:name="xposedmodule" android:value="true" />
<meta-data
android:name="xposeddescription"
android:value="Edxposed demo!" />
<meta-data android:name="xposedminversion" android:value="54" />
<?xml version="1.0" encoding="utf-8"?>
<manifest xmlns:android="http://schemas.android.com/apk/res/android"
package="com.hook.xposed">
<application
android:icon="@mipmap/ic_launcher"
android:label="@string/app_name">
<meta-data
android:name="xposedmodule"
android:value="true" />
<meta-data
android:name="xposeddescription"
android:value="Edxposed Xposed Test" />
<meta-data
android:name="xposedminversion"
android:value="54" />
</application>
</manifest>
dependencies {
compileOnly 'de.robv.android.xposed:api:82'
compileOnly 'de.robv.android.xposed:api:82:sources'
}
repositories {
jcenter()
}
dependencies {
compileOnly files('libs/XposedBridgeApi-82.jar')
}
com.hook.xposed.InitHook
findAndHookMethod("android.app.Application",
loadPackageParam.classLoader,
"attach",
Context.class,
new XC_MethodHook() {
@Override
protected void afterHookedMethod(MethodHookParam param) {
Context context = (Context) param.args[0];
ClassLoader classLoader = context.getClassLoader();
.....
}
}
);
......
public String getTextViewShowData(String input, int count) {
return "Hello, welcome to here!!!";
}
......
XposedHelpers.findAndHookMethod("com.demo.app.MainActivity", lpparam.classLoader, "getTextViewShowData", String.class, int.class, new XC_MethodHook() {
@Override
protected void beforeHookedMethod(MethodHookParam param) throws Throwable {
param.setResult("this function is be hooked!!!");
}
});
Class<?> customClass = XposedHelpers.findClass("自定义变量的的完整路径", classLoader);
findAndHookMethod(
"目标类名",
classLoader,
"目标方法名",
String.class,
customClass,
new XC_MethodHook() {
@Override
protected void afterHookedMethod(MethodHookParam param) {
}
}
);
2.1.4 Hook框架Frida
Frida分为客户端和服务端,需要两者配合才能正常使用。下面将以Mac和Android平台为例对该工具的安装和使用进行介绍。官网推荐使用pip进行安装,Python的版本最好为3.0以上的版本。
$ pip3 install frida-tools
adb push frida-server /data/local/tmp
adb shell // 进入到Android的命令行模式
$ su // 切换到root模式
# chemod a+x /data/local/tmp/frida-server
# ./data/local/tmp/frida-server
adb forward tcp:27042 tcp:27042
adb forward tcp:27043 tcp:27043
$ frida-ps -U
PID Name
----- -------------------------------------------------------
5805 com.google.android.gms
5366 com.google.android.gms.persistent
11067 com.google.android.gms.ui
7371 com.google.android.gms.unstable
5649 com.google.android.googlequicksearchbox
5592 com.google.android.googlequicksearchbox:interactor
5628 android.process.media
frida-ls-devices用于列出附加设备的命令行工具,在与多个设备交互时非常有用。
$ frida-ls-devices
Id Type Name
local local Local System
CVH7N15A20001095 usb Nexus 6P
socket remote Local Socket
$ frida-trace -i "recv*" -i "send*" <进程名>
$ frida-trace -m "ObjC" <进程名>
$ frida-trace -U -f <进程名> -I "call"
$ frida-trace -U -i "Java_*" <进程名>
frida-ps是一个用于列出进程的命令行工具,在与远程系统交互时非常有用。
$ frida-ps -U
$ frida-ps -Ua
$ frida-ps -Uai
$ frida -U Chrome -l test.js --debug
# 发现应用程序中的内部函数
$ frida-discover -n <进程名>
$ frida-discover -p <进程id>
$ frida-kill -D <DEVICE-ID> <PID>
$ frida-ls-devices
Id Type Name
---------------- ------ ------------
local local Local System
CVH7N15A20001095 usb Nexus 6P
socket remote Local Socket
$ frida-ps -D CVH7N15A20001095 -a
PID Name
----- -------------------------------------------------------
5805 com.google.android.gms
5366 com.google.android.gms.persistent
11067 com.google.android.gms.ui
7371 com.google.android.gms.unstable
5649 com.google.android.googlequicksearchbox
5592 com.google.android.googlequicksearchbox:interactor
5628 android.process.media
$ frida-kill -D CVH7N15A20001095 5805
process = frida.attach(target_process)
script = process.create_script(script_code)
script.load()
pid = device.spawn([packename])
process = device.attach(pid)
script = process.create_script(jscode)
script.on('message', on_message)
script.load()
device.resume(pid)
device = frida.get_device_manager().get_device("device id")
manager = frida.get_device_manager()
device = manager.add_remote_device("30.128.25.128:8080")
device = frida.get_usb_device()
import sys
import frida
device = frida.get_usb_device()
pid = device.spawn(["com.frida.test"])
session = device.attach(pid)
device.resume(pid)
jscode = """
Java.perform(function(){
var main=Java.use("com.frida.test.MainActivity");
main.test.implementation = function()
{
console.log("You have been Hooked");
}
});
"""
def on_message(message,data):
print(message["payload"])
script = session.create_script(jscode)
script.on("message",on_message)
script.load()
sys.stdin.read()
import frida
import sys
device = frida.get_usb_device()
pid = device.spawn(["com.frida.test"])
session = device.attach(pid)
device.resume(pid)
jscode = """
var openPtr = Module.findExportByName("libc.so", "open");
Interceptor.attach(openPtr, {
onEnter : function(args){
var pathPtr = args[0];
send("open called ! path=" + pathPtr.readUtf8String());
},
onLeave : function(retval){
send("open leave.....");
}
});
"""
def on_message(message, data):
print(message["payload"])
script = session.create_script(jscode)
script.on("message", on_message)
script.load()
sys.stdin.read()
2.1.5 Hook工具Objection
pip3 install objection
objection -g [packageName/bundleID] explore
objection -g packageName explore --startup-command 'android hooking watch class_method xxxx'
android hooking list activities
android hooking list services
android hooking list receivers
android intent launch_activity [class_activity]
android intent launch_service [class_service]
android/ios hooking list classes
android/ios hooking list class_methods <class_name>
android/ios hooking search classes <class_name>
android/ios hooking search methods <method_name>
android/ios hooking watch class [class_name]
android/ios hooking watch class_method [class_name] --dump-args --dump-backtrace --dump-return
android/ios hooking set return_value [class_name] false
android/ios hooking generate simple [class_name]
# 搜索指定类的实例, 获取该类的实例id
search instances search instances [class_name]
# 通过实例id直接调用该类中的方法
android heap execute [instance_id] [method_name]
android/ios sslpinning disable
# 枚举当前进程模块
memory list modules
# 查看指定模块的导出函数
memory list exports [lib_name]
# 将导出函数的结果保存到指定的文件
memory list exports [lib_name] --json result.json
# 搜索内存
memory search --string --offsets-only
android root disable
android root simulate
android/ios ui screenshot [image.png]
ios jailbreak disable
ios keychain dump
ios ui biometrics_bypass
android shell_exec [command]
2.1.6 Hook工具Tweak
git clone --recursive https://github.com/theos/theos.git /opt/theos
export THEOS=/opt/theos
export PATH="$THEOS/bin:$PATH"
brew install ldid
Makefile:主要作用是自动化构建项目,文件中指定待编译的源代码、依赖信息和编译配置信息等。
TestTweak.plist:此文件用于存储的配置信息。配置信息中的Bundle ID决定了当前项目对哪些些应用生效。具体配置信息如下所示:
{ Filter = { Bundles = ( "com.test.demo","com.test.demo1" ); }; }
%hook ClassName
+ (id)sharedInstance {
return %orig;
}
- (void)messageName:(int)argument {
%orig;
}
- (id)noArguments {
%orig;
}
%end
%hook和%end组合,用于Hook目标类,在代码块中可以直接写需要Hook的方法,代码示例如下:
%hook ClassName
+ (id)sharedInstance {
return %orig;
}
%end
%group testGroup
%hook ClassName
// Hooking a class method
+ (id)sharedInstance {
return %orig;
}
%end
%end
%ctor {
%init(testGroup);
}
%hook ClassName
%new
- (void)addNewMethod {
}
%end
%hook ClassName
- (int)add:(int)a to:(int)b {
if (a != 0) {
// Return original result if `a` is not 0
return %orig;
}
// Otherwise, use 1 as `a`
return %orig(1, b);
}
%end
%hook ClassName
- (void)targetMethod:(id)arg1 {
%log
}
%end
#import <SpringBoard/SpringBoard.h>
%hook SpringBoard
-(void)applicationDidFinishLaunching:(id)application {
%orig;
UIAlertView *alert = [[UIAlertView alloc] initWithTitle:@"Test"
message:@"Tweak test!!!"
delegate:nil
cancelButtonTitle:@"确定"
otherButtonTitles:nil];
[alert show];
}
%end
export THEOS_DEVICE_IP=[目标手机IP]
make do
2.1.7 安全测试工具Drozer
Drozer运行需要依赖python2.x和java环境,在正式安装使用前需要先将其依赖的运行环境配置好。Drozer分为两部分,一部分是客户端,另一部分是手机端代理。手机端代理需要安装在目标设备,用于客户端和目标设备通信时数据代理转发。官网下载地址https://labs.f-secure.com/tools/drozer。
# Drozer依赖python 2.x,此处的pip 必须为python 2.x的版本
pip install drozer-2.4.4-py2-none-any.whl --ignore-installed pyOpenSSL
pip install protobuf==3.17.3 pyOpenSSL Twisted service_identity
# 安装 Mac Command Line
xcode-select --install
使用数据线将手机和电脑进行连接,安装agent到手机并开启服务。电脑的终端中执行端口转发命令和连接手机命令后,如下图所即可正式开始使用drozer工具。
adb forward tcp:31415 tcp:31415
drozer console connect
dz> run app.package.info -a package_name
dz> run app.package.attacksurface package_name
# 其它组件信息查询命令类似,只需更改命令中的组件类型即可
dz> run app.activity.info -a package_name
# 启动时使用空action
dz> run app.activity.start --component package_name activity_name
# 启动时指定action
dz> run app.activity.start --component package_name activity_name
--action android.intent.action.XXX
# 获取目标应用中对外暴露的URI
dz> run scanner.provider.finduris -a package_name
# 通过暴露的URI进行信息检索
dz> run app.provider.query content://uri/passwords/ --vertical
dz> run scanner.provider.injection -a package_name
# 全局可写文件检测
dz> run scanner.misc.writablefiles --privileged /data/data/pacakge_name
# 全局可读文件检测
dz> run scanner.misc.readablefiles --privileged /data/data/pacakge_name
看雪ID:FIGHTING安
https://bbs.kanxue.com/user-home-967913.htm
# 往期推荐
球分享
球点赞
球在看
点击阅读原文查看更多
文章来源: https://mp.weixin.qq.com/s?__biz=MjM5NTc2MDYxMw==&mid=2458546548&idx=1&sn=4dd2354d6a32b4b3f69e8d9378cb78d8&chksm=b18d41fe86fac8e81376782b1b163a0c9731dbb55fd407e3eeb04cdee898b846aafbfd77a654&scene=58&subscene=0#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh