Indian government entities and energy companies have been targeted by unknown threat actors with an aim to deliver a modified version of an open-source information stealer malware called HackBrowserData and exfiltrate sensitive information in some cases by using Slack as command-and-control (C2).
"The information stealer was delivered via a phishing email, masquerading as an invitation letter from the Indian Air Force," EclecticIQ researcher Arda Büyükkaya said in a report published today.
"The attacker utilized Slack channels as exfiltration points to upload confidential internal documents, private email messages, and cached web browser data after the malware's execution."
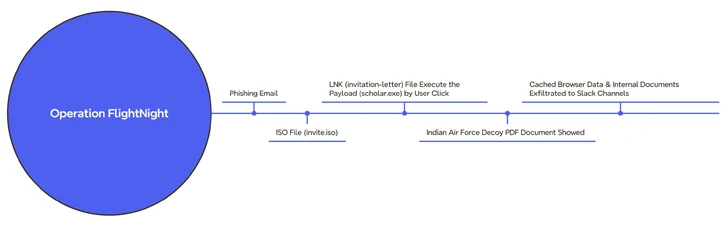
The campaign, observed by the Dutch cybersecurity firm beginning March 7, 2024, has been codenamed Operation FlightNight in reference to the Slack channels operated by the adversary.
Targets of the malicious activity span multiple government entities in India, counting those related to electronic communications, IT governance, and national defense.
The threat actor is said to have successfully compromised private energy companies, harvesting financial documents, personal details of employees, details about drilling activities in oil and gas. In all, about 8.81 GB of data has been exfiltrated over the course of the campaign.
The attack chain starts with a phishing message containing an ISO file ("invite.iso"), which, in turn, contains a Windows shortcut (LNK) that triggers the execution of a hidden binary ("scholar.exe") present within the mounted optical disk image.
Simultaneously, a lure PDF file that purports to be an invitation letter from the Indian Air Force is displayed to the victim while the malware clandestinely harvests documents and cached web browser data and transmits them to an actor-controlled Slack channel named FlightNight.
The malware is an altered version of HackBrowserData that goes beyond its browser data theft features to incorporate capabilities to siphon documents (Microsoft Office, PDFs, and SQL database files), communicate over Slack, and better evade detection using obfuscation techniques.
It's suspected that the threat actor stole the decoy PDF during a previous intrusion, with behavioral similarities traced back to a phishing campaign targeting the Indian Air Force with a Go-based stealer called GoStealer.
Details of the activity were disclosed by an Indian security researcher who goes by the alias xelemental (@ElementalX2) in mid-January 2024.
The GoStealer infection sequence is virtually identical to that FlightNight, employing procurement-themed lures ("SU-30 Aircraft Procurement.iso") to display a decoy file while the stealer payload is deployed to exfiltrate information of interest over Slack.
By adapting freely available offensive tools and repurposing legitimate infrastructure such as Slack that's prevalent in enterprise environments, it allows threat actors to reduce time and development costs, as well as easily fly under the radar.
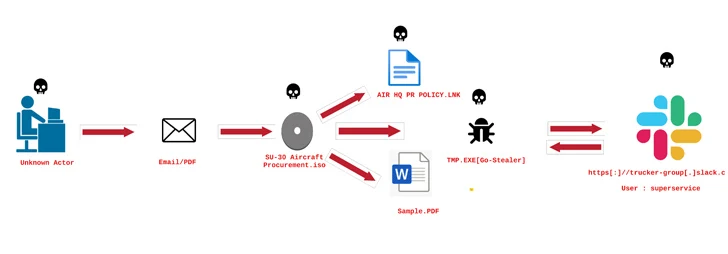 |
| Image source: ElementalX2 |
The efficiency benefits also mean that it's that much easier to launch a targeted attack, even allowing less-skilled and aspiring cybercriminals to spring into action and inflict significant damage to organizations.
"Operation FlightNight and the GoStealer campaign highlight a simple yet effective approach by threat actors to use open-source tools for cyber espionage," Büyükkaya said.
"This underscores the evolving landscape of cyber threats, wherein actors abuse widely used open-source offensive tools and platforms to achieve their objectives with minimal risk of detection and investment."
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.