Cybersecurity researchers have discovered an intricate multi-stage attack that leverages invoice-themed phishing decoys to deliver a wide range of malware such as Venom RAT, Remcos RAT, XWorm, NanoCore RAT, and a stealer that targets crypto wallets.
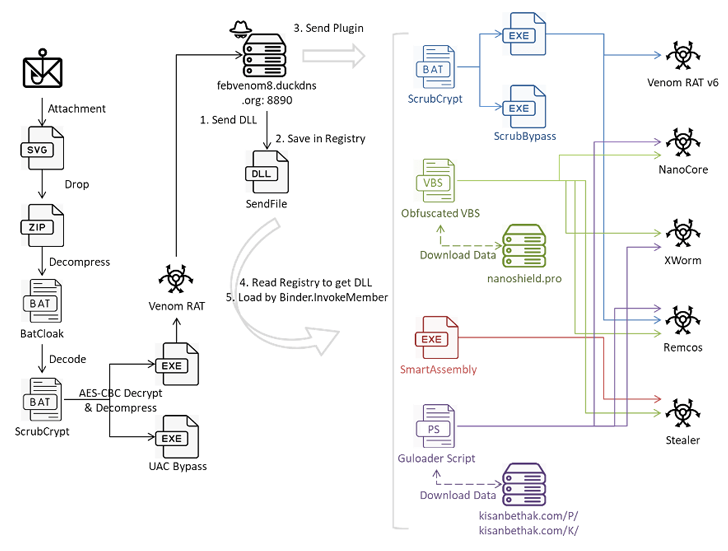
The email messages come with Scalable Vector Graphics (SVG) file attachments that, when clicked, activate the infection sequence, Fortinet FortiGuard Labs said in a technical report.
The modus operandi is notable for the use of the BatCloak malware obfuscation engine and ScrubCrypt to deliver the malware in the form of obfuscated batch scripts.
BatCloak, offered for sale to other threat actors since late 2022, has its foundations in another tool called Jlaive. Its primary feature is to load a next-stage payload in a manner that circumvents traditional detection mechanisms.
ScrubCrypt, a crypter that was first documented by Fortinet in March 2023 in connection with a cryptojacking campaign orchestrated by the 8220 Gang, is assessed to be one of the iterations of BatCloak, according to research from Trend Micro last year.
In the latest campaign analyzed by the cybersecurity firm, the SVG file serves as a conduit to drop a ZIP archive that contains a batch script likely created using BatCloak, which then unpacks the ScrubCrypt batch file to ultimately execute Venom RAT, but not before setting up persistence on the host and taking steps to bypass AMSI and ETW protections.
A fork of Quasar RAT, Venom RAT allows attackers to seize control of the compromised systems, gather sensitive information, and execute commands received from a command-and-control (C2) server.
"While Venom RAT's primary program may appear straightforward, it maintains communication channels with the C2 server to acquire additional plugins for various activities," security researcher Cara Lin said. This includes Venom RAT v6.0.3 with keylogger capabilities, NanoCore RAT, XWorm, and Remcos RAT.
"This [Remcos RAT] plugin was distributed from VenomRAT's C2 using three methods: an obfuscated VBS script named 'remcos.vbs,' ScrubCrypt, and Guloader PowerShell," Lin added.
Also delivered using the plugin system is a stealer that gathers information about the system and exfiltrates data from folders associated with wallets and applications like Atomic Wallet, Electrum, Ethereum, Exodus, Jaxx Liberty (retired as of March 2023), Zcash, Foxmail, and Telegram to a remote server.
"This analysis reveals a sophisticated attack leveraging multiple layers of obfuscation and evasion techniques to distribute and execute VenomRAT via ScrubCrypt," Lin said.
"The attackers employ a variety of methods, including phishing emails with malicious attachments, obfuscated script files, and Guloader PowerShell, to infiltrate and compromise victim systems. Furthermore, deploying plugins through different payloads highlights the versatility and adaptability of the attack campaign."
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.