In an ironic twist of fate, the hunter becomes the hunted in the cyber world as Veriti Research uncovers a surge in attacks orchestrated by a specific threat actor. Dubbed Androxgh0st, this adversary has deployed a web shell on vulnerable servers, pivoting towards ransomware deployment, showcasing a stark reminder that no one is immune in the realm of digital skirmishes.
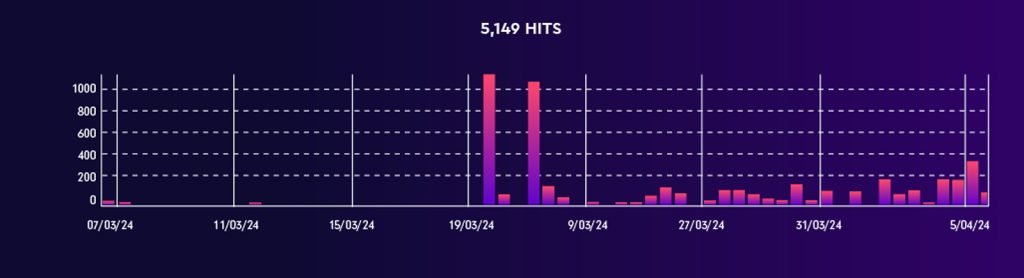
In the past few weeks we have seen a rise of attacks from the Androxgh0st attacker:

The attacker has been linked to deploying the adhublika ransomware. Evidence of this link includes observed communications with an IP address (192.229.211.108) known to be associated with the adhublika group.
Below we can see the extreme rise of attacks that were initiated by the attacker:

For those interested, you can find reference to the attack in the following CISA report (please note this does not include the new IoC’s that were discovered as part of Veriti’s research)
Analyzing the Attack
The group’s primary attack vector involves the exploitation of several CVEs, notably CVE-2021-3129 and CVE-2024-1709, among others, to deploy a web shell on vulnerable servers. This grants the attackers remote control capabilities. Evidence points to active web shells associated with CVE-2019-2725. The group’s automation efforts have focused on a set of vulnerabilities to carry out attacks, with the highest counts in the last week seen in attempts exploiting Craft CMS Remote Code Execution and others as detailed in the table.
| Top Vulnerabilities | Amount of attacks in the last 7 days |
| Craft CMS Remote Code Execution (CVE-2023-41892) | 24752 |
| Apache Struts Remote Code Execution (CVE-2013-2251) | 9813 |
| HTTP Headers Remote Code Execution | 49680 |
| Laravel Ignition Remote Code Execution (CVE-2021-3129) | 22075 |
| Web Servers Malicious Upload Directory Traversal | 5876 |
| Ivanti Endpoint Manager Mobile Authentication Bypass | 5360 |
| ConnectWise ScreenConnect Authentication Bypass (CVE-2024-1709) | 42569 |
| Netis Netcore Router Remote Code Execution | 13599 |
Below you can find the number of organizations that have been attacked by the attacker per vulnerability:
| Vulnerability used by the Attacker | Number of organizations that have been attacked |
| Craft CMS Remote Code Execution (CVE-2023-41892) | 620 |
| PHP Command Injection | 69 |
| Ivanti Endpoint Manager Mobile Authentication Bypass | 60 |
| Command Injection Over HTTP Payload | 57 |
| Apache Struts2 ParametersInterceptor Remote Command Execution | 55 |
| Zeroshell Remote Code Execution (CVE-2009-0545) | 47 |
| Oracle Fusion Middleware Showenv Servlet Information Disclosure | 44 |
| Zimbra Collaboration Directory Traversal | 40 |
| Zyxel USG Command Injection (CVE-2022-30525) | 40 |
| Alcatel Lucent OmniPCX Command Injection (CVE-2007-3010) | 35 |
| Apache Log4j Remote Code Execution (CVE-2021-44228) | 34 |
| Chamilo Command Injection (CVE-2023-34960) | 34 |
| Command Injection Over HTTP | 34 |
| Ivanti Endpoint Manager Cloud Services Appliance Remote Code Execution (CVE-2021-44529) | 34 |
| Ivanti MobileIron Sentry Authentication Bypass (CVE-2023-38035) | 34 |
| Sitecore XP Insecure Deserialization (CVE-2021-42237) | 34 |
| TOTOLINK X18 Command Injection | 34 |
| Web Servers Malicious Upload Directory Traversal | 34 |
| SQL Injection | 33 |
| Multiple Products Arbitrary File Location Upload | 32 |
| PhpMyAdmin Remote Code Execution (CVE-2009-1151) | 32 |
| Zoho ManageEngine ADSelfService Plus Authentication Bypass (CVE-2021-40539) | 27 |
| Juniper Junos Remote Code Execution | 24 |
| ownCloud Graph API Information Disclosure (CVE-2023-49103) | 21 |
| Apache Struts REST plugin Remote Code Execution | 14 |
| HTTP Headers Remote Code Execution | 10 |
| Apache Struts Remote Code Execution (CVE-2013-2251) | 9 |
| JPCERT LogonTracer Command Injection (CVE-2018-16167) | 5 |
| Laravel Ignition Remote Code Execution (CVE-2021-3129) | 4 |
| Microsoft Windows HTTP.sys Remote Code Execution (MS15-034: CVE-2015-1635) | 4 |
| NETGEAR Multiple Products Command Injection (CVE-2016-1555) | 4 |
| Primetek Primefaces Weak Encryption Remote Code Execution | 4 |
| Apache Struts Remote Code Execution (CVE-2021-31805) | 2 |
| Apache Struts2 Freemarker Remote Code Execution (CVE-2017-12611) | 2 |
| Common Arbitrary Files Upload Techniques | 2 |
| Comodo Unified Threat Management Firewall Command Injection (CVE-2018-17431) | 2 |
| D-Link DIR-818LW Command Injection | 2 |
| D-Link Multiple Products Command Injection | 2 |
| Dasan GPON Router Authentication Bypass | 2 |
| Dell EMC Remote Code Execution (CVE-2018-1207) | 2 |
| FUEL CMS Remote Code Execution (CVE-2018-16763) | 2 |
| HTTP Directory Traversal Request Attempt | 2 |
| Jenkins Pipeline Groovy Remote Code Execution (CVE-2019-1003001) | 2 |
| LG N1A1 Command Injection (CVE-2018-14839) | 2 |
| Linux System Files Information Disclosure | 2 |
| Malicious PHP File Upload | 2 |
| Netgear WNAP320 Command Injection | 2 |
| Pivotal Spring Commons Remote Code Execution | 2 |
| Red Hat Jboss Application Server Remote Code Execution (CVE-2017-12149) | 2 |
| Web Servers Malicious HTTP Header Directory Traversal | 2 |
| Western Digital Arkeia Remote Code Execution | 2 |
| XStream Insecure Deserialization | 2 |
| PHP CGI Query String Parameter Handling Information Disclosure Vulnerability | 1 |
Upon reviewing the attack analysis, it is evident that maintaining updated security measures is paramount. We strongly advise organizations to prioritize patch management for known vulnerabilities, implement robust monitoring to detect web shell deployments, and consider behavioral analysis tools to spot unusual server communications. Regular exposure assessments should also be in line with the latest threat intelligence to preempt potential breaches. This proactive stance can help safeguard against the exploitation of vulnerabilities similar to those identified in the attack.
A Classic case of “caught in his own trap”
In the digital game of cat and mouse, even hackers aren’t safe from the pitfalls of cyber vulnerabilities. Veriti’s research uncovered over 600 servers compromised by one such attacker, a majority in the U.S., with a significant number in India. The twist in the tale comes from the discovery of the attacker’s Command & Control (C&C) server, which, ironically, was found to be vulnerable. This vulnerability in the attacker’s defenses could allow for a counterstrike—penetrating their system to reveal victim lists and alert them.
This reversal of roles underscores the importance of proactive exposure management and threat intelligence in cyber security. By turning the tables on attackers, we can provide critical insights that not only inform but also shield against future attacks, encapsulating the essence of why hackers getting hacked is a stern reminder for robust security strategies.
| CVE-2023-51767 | OpenSSH through 9.6, when common types of DRAM are used, might allow row hammer attacks (for authentication bypass) because the integer value of authenticated in mm_answer_authpassword does not resist flips of a single bit. NOTE: this is applicable to a certain threat model of attacker-victim co-location in which the attacker has user privileges. |
| CVE-2023-51385 | In ssh in OpenSSH before 9.6, OS command injection might occur if a user name or host name has shell metacharacters, and this name is referenced by an expansion token in certain situations. For example, an untrusted Git repository can have a submodule with shell metacharacters in a user name or host name. |
| CVE-2023-51384 | In ssh-agent in OpenSSH before 9.6, certain destination constraints can be incompletely applied. When destination constraints are specified during addition of PKCS#11-hosted private keys, these constraints are only applied to the first key, even if a PKCS#11 token returns multiple keys. |
| CVE-2023-48795 | The SSH transport protocol with certain OpenSSH extensions, found in OpenSSH before 9.6 and other products, allows remote attackers to bypass integrity checks such that some packets are omitted (from the extension negotiation message), and a client and server may consequently end up with a connection for which some security features have been downgraded or disabled, aka a Terrapin attack. This occurs because the SSH Binary Packet Protocol (BPP), implemented by these extensions, mishandles the handshake phase and mishandles use of sequence numbers. For example, there is an effective attack against SSH’s use of ChaCha20-Poly1305 (and CBC with Encrypt-then-MAC). The bypass occurs in [email protected] and (if CBC is used) the [email protected] MAC algorithms. This also affects Maverick Synergy Java SSH API before 3.1.0-SNAPSHOT, Dropbear through 2022.83, Ssh before 5.1.1 in Erlang/OTP, PuTTY before 0.80, AsyncSSH before 2.14.2, golang.org/x/crypto before 0.17.0, libssh before 0.10.6, libssh2 through 1.11.0, Thorn Tech SFTP Gateway before 3.4.6, Tera Term before 5.1, Paramiko before 3.4.0, jsch before 0.2.15, SFTPGo before 2.5.6, Netgate pfSense Plus through 23.09.1, Netgate pfSense CE through 2.7.2, HPN-SSH through 18.2.0, ProFTPD before 1.3.8b (and before 1.3.9rc2), ORYX CycloneSSH before 2.3.4, NetSarang XShell 7 before Build 0144, CrushFTP before 10.6.0, ConnectBot SSH library before 2.2.22, Apache MINA sshd through 2.11.0, sshj through 0.37.0, TinySSH through 20230101, trilead-ssh2 6401, LANCOM LCOS and LANconfig, FileZilla before 3.66.4, Nova before 11.8, PKIX-SSH before 14.4, SecureCRT before 9.4.3, Transmit5 before 5.10.4, Win32-OpenSSH before 9.5.0.0p1-Beta, WinSCP before 6.2.2, Bitvise SSH Server before 9.32, Bitvise SSH Client before 9.33, KiTTY through 0.76.1.13, the net-ssh gem 7.2.0 for Ruby, the mscdex ssh2 module before 1.15.0 for Node.js, the thrussh library before 0.35.1 for Rust, and the Russh crate before 0.40.2 for Rust. |
| CVE-2023-38408 | The PKCS#11 feature in ssh-agent in OpenSSH before 9.3p2 has an insufficiently trustworthy search path, leading to remote code execution if an agent is forwarded to an attacker-controlled system. (Code in /usr/lib is not necessarily safe for loading into ssh-agent.) NOTE: this issue exists because of an incomplete fix for CVE-2016-10009. |
| CVE-2021-41617 | 4.4 sshd in OpenSSH 6.2 through 8.x before 8.8, when certain non-default configurations are used, allows privilege escalation because supplemental groups are not initialized as expected. Helper programs for AuthorizedKeysCommand and AuthorizedPrincipalsCommand may run with privileges associated with group memberships of the sshd process, if the configuration specifies running the command as a different user. |
| CVE-2021-36368 | 2.6 An issue was discovered in OpenSSH before 8.9. If a client is using public-key authentication with agent forwarding but without -oLogLevel=verbose, and an attacker has silently modified the server to support the None authentication option, then the user cannot determine whether FIDO authentication is going to confirm that the user wishes to connect to that server, or that the user wishes to allow that server to connect to a different server on the user’s behalf. NOTE: the vendor’s position is “this is not an authentication bypass, since nothing is being bypassed. |
| CVE-2020-15778 | 6.8 scp in OpenSSH through 8.3p1 allows command injection in the scp.c toremote function, as demonstrated by backtick characters in the destination argument. NOTE: the vendor reportedly has stated that they intentionally omit validation of “anomalous argument transfers” because that could “stand a great chance of breaking existing workflows.” |
| CVE-2020-14145 | 4.3 The client side in OpenSSH 5.7 through 8.4 has an Observable Discrepancy leading to an information leak in the algorithm negotiation. This allows man-in-the-middle attackers to target initial connection attempts (where no host key for the server has been cached by the client). NOTE: some reports state that 8.5 and 8.6 are also affected. |
| CVE-2019-16905 | 4.4 OpenSSH 7.7 through 7.9 and 8.x before 8.1, when compiled with an experimental key type, has a pre-authentication integer overflow if a client or server is configured to use a crafted XMSS key. This leads to memory corruption and local code execution because of an error in the XMSS key parsing algorithm. NOTE: the XMSS implementation is considered experimental in all released OpenSSH versions, and there is no supported way to enable it when building portable OpenSSH. |
| CVE-2016-20012 | 4.3 OpenSSH through 8.7 allows remote attackers, who have a suspicion that a certain combination of username and public key is known to an SSH server, to test whether this suspicion is correct. This occurs because a challenge is sent only when that combination could be valid for a login session. NOTE: the vendor does not recognize user enumeration as a vulnerability for this product |
| CVE-2008-3844 | 9.3 Certain Red Hat Enterprise Linux (RHEL) 4 and 5 packages for OpenSSH, as signed in August 2008 using a legitimate Red Hat GPG key, contain an externally introduced modification (Trojan Horse) that allows the package authors to have an unknown impact. NOTE: since the malicious packages were not distributed from any official Red Hat sources, the scope of this issue is restricted to users who may have obtained these packages through unofficial distribution points. As of 20080827, no unofficial distributions of this software are known. |
| CVE-2007-2768 | 4.3 OpenSSH, when using OPIE (One-Time Passwords in Everything) for PAM, allows remote attackers to determine the existence of certain user accounts, which displays a different response if the user account exists and is configured to use one-time passwords (OTP), a similar issue to CVE-2007-2243. |
The table included in the blog isn’t just a set of data; it’s a snapshot of vulnerability in action, showing that even hackers can get entangled in their own snares. These CVEs underscore a critical point: attackers and defenders alike can overlook key weaknesses. The irony here isn’t lost on us – the very individuals exploiting these gaps can also fall victim to similar oversights. It’s a reminder that ongoing, proactive exposure management is key to cyber security – a place where attackers getting hacked is a reality, not just a turn of phrase. Our in-depth research into these exposures supports a security approach that’s as nimble as it is steadfast, preventing disruption while closing the gaps.
In the wake of our comprehensive analysis, the statistics tell a story that underscores the crux of cybersecurity today. Notably, a significant percentage of organizations possess compensating controls, yet a staggering number remain misconfigured—leaving gaping vulnerabilities. This is where Veriti’s strategic approach to exposure assessment and remediation becomes pivotal. By harmoniously integrating with your existing security infrastructure, Veriti not only illuminates these hidden exposures but also swiftly removes them. With agentless integration and smart remediation strategies, you can ensure that the security infrastructure of your organization is both resilient and seamless, with no disruption to business continuity.
| Exposure Type | Enforcement status – % of organizations that have compensating controls but are misconfigured |
| Craft CMS Remote Code Execution (CVE-2023-41892) – 24752 | 15% |
| Apache Struts Remote Code Execution (CVE-2013-2251) – 9813 | 5% |
| HTTP Headers Remote Code Execution – 49680 | 12% |
| Laravel Ignition Remote Code Execution (CVE-2021-3129) – 22075 | 12% |
| Web Servers Malicious Upload Directory Traversal – 5876 | 5% |
| Ivanti Endpoint Manager Mobile Authentication Bypass – 5360 | 5% |
| ConnectWise ScreenConnect Authentication Bypass (CVE-2024-1709) – 42569 | 55% |
| Netis Netcore Router Remote Code Execution – 13599 | 22% |
Discover how even hackers face cyber threats, as Veriti Research reveals a rise in attacks by the Androxgh0st group, emphasizing the necessity of proactive exposure management and safe remediation
*** This is a Security Bloggers Network syndicated blog from VERITI authored by Veriti Research. Read the original post at: https://veriti.ai/blog/vulnerable-villain-when-hackers-get-hacked/