在内网渗透的过程中,经常会遇到需要查看域用户登陆了哪些机器,目前我们收集整理了三种方法,给大家分享出来。
1.使用vbs脚本来查询
' Script for getting current logged user name on Domain
"Select Name, Location from 'LDAP://"&strADsPath&"' " _
& "Where objectClass='computer'"
On Error Resume Next
sPC = objRecordSet.Fields("Name").Value
of.writeline " "
of.writeline "Machine Name: "&sPC
& "{impersonationLevel=impersonate}!\\" & sPC & "\root\cimv2")
If Err = 0 Then
Set col = Nothing
Else
of.writeline "!!! Cant connect to "&sPC&" !!!"
' Author : mwpq
' www.sharecenter.net
strDomainName = InputBox ("Please enter the internal Domain Name:","Script for getting current logged username","yourdomain.local")
arrDomLevels = Split(strDomainName, ".")
strADsPath = "dc=" & Join(arrDomLevels, ",dc=")Const ADS_SCOPE_SUBTREE = 2
Set objConnection = CreateObject("ADODB.Connection")
Set objCommand = CreateObject("ADODB.Command")
objConnection.Provider = "ADsDSOObject"
objConnection.Open "Active Directory Provider"'
Set objCOmmand.ActiveConnection = objConnection
objCommand.CommandText = _
objCommand.Properties("Page Size") = 1000
objCommand.Properties("Searchscope") = ADS_SCOPE_SUBTREE
Set objRecordSet = objCommand.Execute
objRecordSet.MoveFirst
Set oFSO = CreateObject("Scripting.FileSystemObject")
Set of = oFSO.CreateTextFile("LoggedUser.txt", True, True)
Do Until objRecordSet.EOF
End If
objRecordSet.MoveNext
Loop
of.close
MsgBox "Done! Cheers!"
2.使用Logondomaincomputersuser.exe来查询
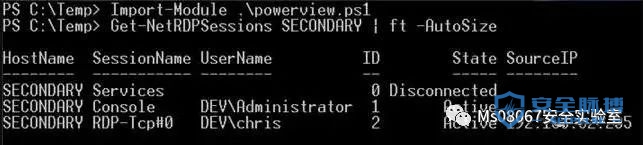
3.使用powershell枚举远程主机登陆会话PowerQuinsta 是powerview里的一个模块,可以枚举远程主机的登录会话。
像这样:

但是这不是重点,重点是作者详细的介绍了从qwinsta命令到windows API分析,然后再到powershell的开发,之前想表明powershell和.Net的关系,然后还可以借助.Net和其他的联系开发出更多适合场景的小工具之类的。
这里可以用下面的代码查找符合关键词的对象和方法。
## class
$searchtext = "*Domain*"
[AppDomain]::CurrentDomain.GetAssemblies() |
ForEach-Object { $_.GetExportedTypes() } |
Where-Object { $_ -like $searchtext } |
ForEach-Object { $_.FullName }

## method
$searchtext = "*connect*"
[AppDomain]::CurrentDomain.GetAssemblies() |
ForEach-Object { $_.GetExportedTypes() } |
ForEach-Object { $_.getmembers() } |
Where-Object { $_.isStatic} |
Where-Object { $_ -like $searchtext } |
ForEach-Object { "[{0}]::{1} --> {2}" -f `
$_.declaringtype, $_.toString().SubString( `
$_.toString().IndexOf(" ")+1), $_.ReturnType }

补充一个@xti9er提到的WMI对象:
get-wmiobject|get-member
但这个不完整,详细的搜索可以这样:
Get-WmiObject -List | Where-Object { $_.name -match 'domain'}

##附
【1】http://www.harmj0y.net/blog/powershell/powerquinsta/ 原文
【2】http://www.harmj0y.net/blog/powershell/powershell-and-win32-api-access/ Powershell and win32 API
本文作者:Ms08067安全实验室
本文为安全脉搏专栏作者发布,转载请注明:https://www.secpulse.com/archives/124699.html
如有侵权请联系:admin#unsafe.sh