2024-5-16 21:0:0 Author: www.tenable.com(查看原文) 阅读量:13 收藏

Background
Cloud cryptomining has become an emerging trend in recent years, powered by the scalability and flexibility of cloud platforms. Unlike traditional on-premises infrastructure, cloud infrastructure allows attackers to quickly deploy resources for cryptomining, making it easier to exploit. One of the most common cryptomining threats for cloud environments is the Kinsing malware.
Kinsing is a notorious malware family active for several years, primarily targeting Linux-based cloud infrastructure. Known for leveraging various vulnerabilities to gain unauthorized access, the threat actors behind the Kinsing malware typically deploy backdoors and cryptocurrency miners (cryptominers) on compromised systems. After infection, Kinsing uses system resources for cryptomining, which leads to higher costs and slower server performance.
Recently, we discovered that Kinsing also attacks Apache Tomcat servers, and uses new techniques to hide itself on the filesystem, including utilizing innocent and non-suspicious file locations for persistence. In this article, we present our technical findings and share relevant indicators of compromise (IOCs) to help the community defend against this emerging threat.
Technical details
Kinsing campaigns are known for taking advantage of vulnerabilities in containers and servers in order to deploy malware, specifically backdoors and cryptominers. In this case, we've detected multiple infected servers within a singular environment, including an Apache Tomcat server with critical vulnerabilities. Apache Tomcat is an open source server that provides static data (like images and other static content), which makes it fully accessible from the internet, making it an attractive attack surface.
The Kinsing malware uses different locations to stay undetected and hides itself as a system file. We've found it in four locations, presumably for persistence purposes. Interestingly, three of these locations are manual files, or 'man' pages, where malware is rarely found. This unusual technique leverages the assumption that defenders typically don't search for malicious files in those locations. Here are the locations:
- /var/cache/man/cs/cat1/: typically used for user-level commands and applications.
- /var/cache/man/cs/cat3/: usually associated with library functions and programming interfaces.
- /var/lib/gssproxy/rcache/: The gssproxy (Generic Security Services Proxy) is a service that provides a proxy interface to the Kerberos library, making it easier for applications to use Kerberos authentication.
- /var/cache/man/zh_TW/cat8/: used for system administration and maintenance commands. Note the tz_TW folder - this is a Taiwan / Chinese folder. We can assume that the attackers have managed to create this directory structure as part of their malware installation and assume they won’t get discovered on this path.
These locations are typically used for legitimate system files, allowing the malware to blend in and avoid detection. By leveraging these seemingly innocuous paths, the attackers increase the chances of their malware staying unnoticed on compromised systems.
The malicious file itself detected is not new. It was first spotted at the end of 2022 in China. This specific attack on the Tomcat server started in mid-2023 based on the creation dates:
- var/cache/man/cs/cat3/ 06/22/2023
- var/cache/man/zh_TW/cat8/ 07/04/2023
- var/cache/man/cs/cat1/ 07/30/2023
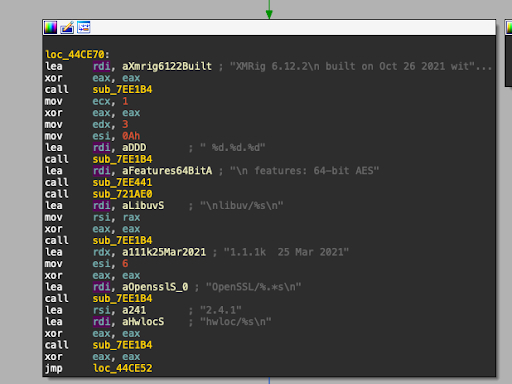
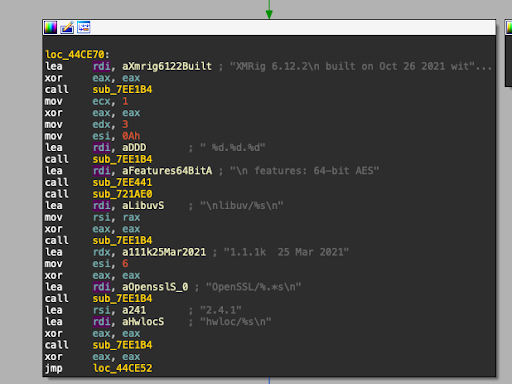
We see that the malicious operation has been active for almost a year without anyone noticing it. The malware has a cryptominer embedded in it called XMRig. XMRig is an open-source CPU mining software used for the mining of Monero, a cryptocurrency with high privacy. In the figure below, we can see that the version of XMRig is 6.12.2, while the current version on GitHub is 6.21.2:
Identifying affected systems
An effective detection mechanism that leverages research (such as the one presented here) is essential to locate this type of compromise.
To address this need, Tenable Cloud Security has recently introduced a new malware detection feature designed to enhance our existing cloud security capabilities and work in full synergy with them. This capability effectively identifies malware across various cloud workloads, providing a critical layer of security by detecting threats to mitigate the harm they may cause. Our solution offers practical, straightforward integration with your cloud infrastructure, ensuring that security is both seamless and robust.
| Malware Name | SHA-256 |
|---|---|
| XMRig | 063f80c2c5accaecd8c9e6b6815ae80e372477f9df1113dafc72a2a0703aaa68 |
To understand how this feature can work for your organization, we invite you to request a demo of Tenable Cloud Security.
Related Articles
- Anti-malware
- Attack Surface Management
- Exposure Management
- Malware
- Threat Intelligence
- Threat Management
- Vulnerability Management
Cybersecurity News You Can Use
Enter your email and never miss timely alerts and security guidance from the experts at Tenable.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy.
Your Tenable Vulnerability Management trial also includes Tenable Lumin and Tenable Web App Scanning.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy. Purchase your annual subscription today.
100 assets
Choose Your Subscription Option:
Thank You
Thank you for your interest in Tenable Vulnerability Management. A representative will be in touch soon.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy.
Your Tenable Vulnerability Management trial also includes Tenable Lumin and Tenable Web App Scanning.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy. Purchase your annual subscription today.
100 assets
Choose Your Subscription Option:
Thank You
Thank you for your interest in Tenable.io. A representative will be in touch soon.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy.
Your Tenable Vulnerability Management trial also includes Tenable Lumin and Tenable Web App Scanning.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy. Purchase your annual subscription today.
100 assets
Choose Your Subscription Option:
Thank You
Thank you for your interest in Tenable Vulnerability Management. A representative will be in touch soon.
Try Tenable Web App Scanning
Enjoy full access to our latest web application scanning offering designed for modern applications as part of the Tenable One Exposure Management platform. Safely scan your entire online portfolio for vulnerabilities with a high degree of accuracy without heavy manual effort or disruption to critical web applications. Sign up now.
Your Tenable Web App Scanning trial also includes Tenable Vulnerability Management and Tenable Lumin.
Buy Tenable Web App Scanning
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy. Purchase your annual subscription today.
Try Tenable Lumin
Visualize and explore your exposure management, track risk reduction over time and benchmark against your peers with Tenable Lumin.
Your Tenable Lumin trial also includes Tenable Vulnerability Management and Tenable Web App Scanning.
Buy Tenable Lumin
Contact a Sales Representative to see how Tenable Lumin can help you gain insight across your entire organization and manage cyber risk.
Thank You
Thank you for your interest in Tenable Lumin. A representative will be in touch soon.
Request a demo of Tenable Security Center
Please fill out this form with your contact information.
A sales representative will contact you shortly to schedule a demo.
* Field is required
Request a demo of Tenable OT Security
Get the Operational Technology Security You Need.
Reduce the Risk You Don’t.
Request a demo of Tenable Identity Exposure
Continuously detect and respond to Active Directory attacks. No agents. No privileges.
On-prem and in the cloud.
Request a Demo of Tenable Cloud Security
Exceptional unified cloud security awaits you!
We’ll show you exactly how Tenable Cloud Security helps you deliver multi-cloud asset discovery, prioritized risk assessments and automated compliance/audit reports.
See
Tenable One
In Action
Exposure management for the modern attack surface.
See Tenable Attack Surface Management In Action
Know the exposure of every asset on any platform.
Thank You
Thank you for your interest in Tenable Attack Surface Management. A representative will be in touch soon.
Try Tenable Nessus Professional Free
FREE FOR 7 DAYS
Tenable Nessus is the most comprehensive vulnerability scanner on the market today.
NEW - Tenable Nessus Expert
Now Available
Nessus Expert adds even more features, including external attack surface scanning, and the ability to add domains and scan cloud infrastructure. Click here to Try Nessus Expert.
Fill out the form below to continue with a Nessus Pro Trial.
Buy Tenable Nessus Professional
Tenable Nessus is the most comprehensive vulnerability scanner on the market today. Tenable Nessus Professional will help automate the vulnerability scanning process, save time in your compliance cycles and allow you to engage your IT team.
Buy a multi-year license and save. Add Advanced Support for access to phone, community and chat support 24 hours a day, 365 days a year.
Try Tenable Nessus Expert Free
FREE FOR 7 DAYS
Built for the modern attack surface, Nessus Expert enables you to see more and protect your organization from vulnerabilities from IT to the cloud.
Already have Tenable Nessus Professional?
Upgrade to Nessus Expert free for 7 days.
Buy Tenable Nessus Expert
Built for the modern attack surface, Nessus Expert enables you to see more and protect your organization from vulnerabilities from IT to the cloud.
Learn How Tenable Helps Achieve SLCGP Cybersecurity Plan Requirements
Tenable solutions help fulfill all SLCGP requirements. Connect with a Tenable representative to learn more.
如有侵权请联系:admin#unsafe.sh