
2024-6-8 00:56:50 Author: www.tenable.com(查看原文) 阅读量:1533 收藏


Researchers disclose a critical severity vulnerability affecting PHP installations and provide proof-of-concept exploit code, which could lead to remote code execution.
Background
On June 6, maintainers of PHP released updates to address a critical vulnerability affecting installations where PHP is used in CGI mode. As part of a coordinated release, researchers at DEVCORE published a blog post with their analysis of the vulnerability and its impact.
| CVE | Description | CVSSv3 |
|---|---|---|
| CVE-2024-4577 | PHP-CGI Argument Injection Vulnerability | 9.8 |
Analysis
CVE-2024-4577 is a critical argument injection vulnerability in PHP that can be exploited to achieve remote code execution (RCE). According to researchers at DEVCORE, this flaw is the result of errors in character encoding conversions, affecting the “Best Fit” feature on Windows.
The DEVCORE team outlines two scenarios that administrators can use to determine if their servers may be impacted. The first is when PHP is running with CGI mode enabled. From documentation provided by PHP, CGI mode is dangerous and can open up your server to a variety of vulnerabilities.
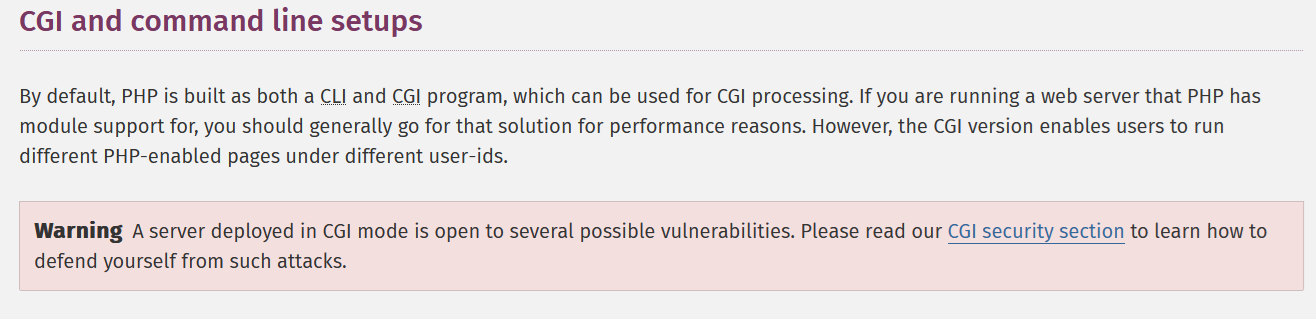
Credit: PHP.net documentation
The second scenario involves a PHP installation in which the PHP binary is exposed in a web-accessible directory. It’s important to note that according to DEVCORE, XAMPP, a popular PHP development environment, exposes the PHP binary by default, potentially having a wide impact on systems across the internet.
CVE-2024-4577 is a patch bypass of CVE-2012-1823
Both PHP and DEVCORE note that CVE-2024-4577 is a patch bypass of CVE-2012-1823. CVE-2012-1823 was patched in PHP versions 5.13.12 and 5.4.2 on May 3, 2012 and at the time was noted to be a vulnerability that “has gone unnoticed for at least 8 years.” The vulnerability was originally discovered during a capture the flag (CTF) event in 2012. While the original blog is no longer accessible, an archived copy details the discovery and reporting of the flaw. A variety of exploit scripts exist for CVE-2012-1823 and it has been in the U.S. Cybersecurity and Infrastructure Security Agency (CISA) Known Exploited Vulnerabilities (KEV) list since March 25, 2022.
Active scanning is underway
On June 7, The Shadowserver Foundation posted on X (formerly Twitter) that they have observed multiple IPs attempting to test this vulnerability against their honeypots.
Attention! We see multiple IPs testing PHP/PHP-CGI CVE-2024-4577 (Argument Injection Vulnerability) against our honeypot sensors starting today, June 7th. Vulnerability affects PHP running on Windows.
Patches released June 6th: https://t.co/jM5HgGUZJF
Exploit PoC is public.
— The Shadowserver Foundation (@Shadowserver) June 7, 2024
Proof of concept
On June 7, researchers at watchTowr released a proof-of-concept (PoC) script for CVE-2024-4577 on their GitHub page.
Solution
PHP versions of 8.1.29, 8.2.20 and 8.3.8 were released on June 6 to address this vulnerability. If you are unable to patch immediately, the DEVCORE blog does offer some mitigation guidance. As both PHP and DEVCORE note, CGI mode is insecure and dated, so it is recommended to migrate “to a more secure architecture.”
Identifying affected systems
A list of Tenable plugins for this vulnerability can be found on the individual CVE page for CVE-2024-4577 as they’re released. This link will display all available plugins for this vulnerability, including upcoming plugins in our Plugins Pipeline.
Get more information
- DEVCORE blog: Security Alert: CVE-2024-4577 - PHP CGI Argument Injection Vulnerability
- PHP 8.1.29 ChangeLog
- PHP 8.2.20 ChangeLog
- PHP 8.3.8 ChangeLog
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.

Scott Caveza
Scott joined Tenable in 2012 as a Research Engineer on the Nessus Plugins team. Over the years, he has written hundreds of plugins for Nessus, and reviewed code for even more from his time being a team lead and manager of the Plugins team. Previously leading the Security Response team and the Zero Day Research team, Scott is currently a member of the Security Response team, helping the research organization respond to the latest threats. He has over a decade of experience in the industry with previous work in the Security Operations Center (SOC) for a major domain registrar and web hosting provider. Scott is a current CISSP and actively maintains his GIAC GWAPT Web Application Penetration Tester certification.
Interests outside of work: Scott enjoys spending time with his family, camping, fishing and being outdoors. He also enjoys finding ways to break web applications and home renovation projects.
Related Articles
- Exposure Management
Cybersecurity News You Can Use
Enter your email and never miss timely alerts and security guidance from the experts at Tenable.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy.
Your Tenable Vulnerability Management trial also includes Tenable Lumin and Tenable Web App Scanning.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy. Purchase your annual subscription today.
100 assets
Choose Your Subscription Option:
Thank You
Thank you for your interest in Tenable Vulnerability Management. A representative will be in touch soon.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy.
Your Tenable Vulnerability Management trial also includes Tenable Lumin and Tenable Web App Scanning.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy. Purchase your annual subscription today.
100 assets
Choose Your Subscription Option:
Thank You
Thank you for your interest in Tenable.io. A representative will be in touch soon.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy.
Your Tenable Vulnerability Management trial also includes Tenable Lumin and Tenable Web App Scanning.
Tenable Vulnerability Management
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy. Purchase your annual subscription today.
100 assets
Choose Your Subscription Option:
Thank You
Thank you for your interest in Tenable Vulnerability Management. A representative will be in touch soon.
Try Tenable Web App Scanning
Enjoy full access to our latest web application scanning offering designed for modern applications as part of the Tenable One Exposure Management platform. Safely scan your entire online portfolio for vulnerabilities with a high degree of accuracy without heavy manual effort or disruption to critical web applications. Sign up now.
Your Tenable Web App Scanning trial also includes Tenable Vulnerability Management and Tenable Lumin.
Buy Tenable Web App Scanning
Enjoy full access to a modern, cloud-based vulnerability management platform that enables you to see and track all of your assets with unmatched accuracy. Purchase your annual subscription today.
Try Tenable Lumin
Visualize and explore your exposure management, track risk reduction over time and benchmark against your peers with Tenable Lumin.
Your Tenable Lumin trial also includes Tenable Vulnerability Management and Tenable Web App Scanning.
Buy Tenable Lumin
Contact a Sales Representative to see how Tenable Lumin can help you gain insight across your entire organization and manage cyber risk.
Thank You
Thank you for your interest in Tenable Lumin. A representative will be in touch soon.
Request a demo of Tenable Security Center
Please fill out this form with your contact information.
A sales representative will contact you shortly to schedule a demo.
* Field is required
Request a demo of Tenable OT Security
Get the Operational Technology Security You Need.
Reduce the Risk You Don’t.
Request a demo of Tenable Identity Exposure
Continuously detect and respond to Active Directory attacks. No agents. No privileges.
On-prem and in the cloud.
Request a Demo of Tenable Cloud Security
Exceptional unified cloud security awaits you!
We’ll show you exactly how Tenable Cloud Security helps you deliver multi-cloud asset discovery, prioritized risk assessments and automated compliance/audit reports.
See
Tenable One
In Action
Exposure management for the modern attack surface.
See Tenable Attack Surface Management In Action
Know the exposure of every asset on any platform.
Thank You
Thank you for your interest in Tenable Attack Surface Management. A representative will be in touch soon.
Try Tenable Nessus Professional Free
FREE FOR 7 DAYS
Tenable Nessus is the most comprehensive vulnerability scanner on the market today.
NEW - Tenable Nessus Expert
Now Available
Nessus Expert adds even more features, including external attack surface scanning, and the ability to add domains and scan cloud infrastructure. Click here to Try Nessus Expert.
Fill out the form below to continue with a Nessus Pro Trial.
Buy Tenable Nessus Professional
Tenable Nessus is the most comprehensive vulnerability scanner on the market today. Tenable Nessus Professional will help automate the vulnerability scanning process, save time in your compliance cycles and allow you to engage your IT team.
Buy a multi-year license and save. Add Advanced Support for access to phone, community and chat support 24 hours a day, 365 days a year.
Try Tenable Nessus Expert Free
FREE FOR 7 DAYS
Built for the modern attack surface, Nessus Expert enables you to see more and protect your organization from vulnerabilities from IT to the cloud.
Already have Tenable Nessus Professional?
Upgrade to Nessus Expert free for 7 days.
Buy Tenable Nessus Expert
Built for the modern attack surface, Nessus Expert enables you to see more and protect your organization from vulnerabilities from IT to the cloud.
Learn How Tenable Helps Achieve SLCGP Cybersecurity Plan Requirements
Tenable solutions help fulfill all SLCGP requirements. Connect with a Tenable representative to learn more.
如有侵权请联系:admin#unsafe.sh