Two security vulnerabilities have been disclosed in the Mailcow open-source mail server suite that could be exploited by malicious actors to achieve arbitrary code execution on susceptible instances.
Both shortcomings impact all versions of the software prior to version 2024-04, which was released on April 4, 2024. The issues were responsibly disclosed by SonarSource on March 22, 2024.
The flaws, rated Moderate in severity, are listed below -
- CVE-2024-30270 (CVSS score: 6.7) - A path traversal vulnerability impacting a function named "rspamd_maps()" that could result in the execution of arbitrary commands on the server by allowing a threat actor to overwrite any file that's can be modified with the "www-data" user
- CVE-2024-31204 (CVSS score: 6.8) - A cross-site scripting (XSS) vulnerability via the exception handling mechanism when not operating in the DEV_MODE
The second of the two flaws is rooted in the fact that it saves details of the exception sans any sanitization or encoding, which are then rendered into HTML and executed as JavaScript within the users' browser.
As a result, an attacker could take advantage of the scenario to inject malicious scripts into the admin panel by triggering exceptions with specially crafted input, effectively allowing them to hijack the session and perform privileged actions in the context of an administrator.
Put differently, by combining the two flaws, it's possible for a malicious party to take control of accounts on a Mailcow server and gain access to sensitive data as well as execute commands.
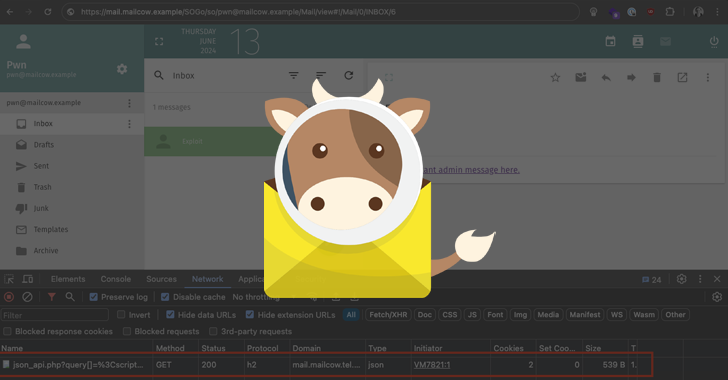
In a theoretical attack scenario, a threat actor can craft an HTML email containing a CSS background image which is loaded from a remote URL, using it to trigger the execution of an XSS payload.
"An attacker can combine both vulnerabilities to execute arbitrary code on the admin panel server of a vulnerable mailcow instance," SonarSource vulnerability researcher Paul Gerste said.
"The requirement for this is that an admin user views a malicious email while being logged into the admin panel. The victim does not have to click a link inside the email or perform any other interaction with the email itself, they only have to continue using the admin panel after viewing the email."
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.