2024-8-6 15:19:37 Author: securityaffairs.com(查看原文) 阅读量:8 收藏
Should Organizations Pay Ransom Demands?

Ransomware attacks are the most significant risk for modern organizations, why organizations should avoid paying ransoms.
Ransomware attacks are the most significant risk for modern organizations, with the Verizon Data Breach Report 2024 reporting that ransomware is a top threat across 92% of industries. In recent years, the number of ransomware attacks has grown significantly. Actors have become more sophisticated, advancing their tactics, techniques, and procedures, such as with double extortion, a trend in which attackers exfiltrate and leverage sensitive data to force victims to pay the ransom demand.
However, despite ransomware being such a persistent and pervasive problem, experts still need to agree on how best to respond to it, particularly on whether or not to pay ransom demands. Let’s explore both sides of the debate.
What is a Ransomware Attack?
First, let’s briefly clarify what a ransomware attack is. Ransomware is a type of malicious software or malware that cybercriminals use to encrypt a victim’s data or lock them out of their system. The attacker then demands a ransom payment, typically in cryptocurrency, in exchange for providing a decryption key or unlocking the system.
Why Organizations Should Avoid Paying Ransoms
Perhaps the most compelling argument for refusing to pay ransom demands is that handing over money to cybercriminal groups almost always increases ransomware activity.
By paying a ransomware demand, businesses essentially fund cybercriminal groups, helping them expand their operations. Moreover, ransom pay can signal to cyber criminals that a sector is ripe for exploitation.
When reports came in that medical company Change Healthcare may have paid ransomware gang BlackCat/ALPHV a $22 million ransom in March 2024, the broader healthcare sector experienced a surge in ransomware attacks. Similarly, paying a ransom demand to one ransomware group may indicate to others that an organization is a worthwhile target.
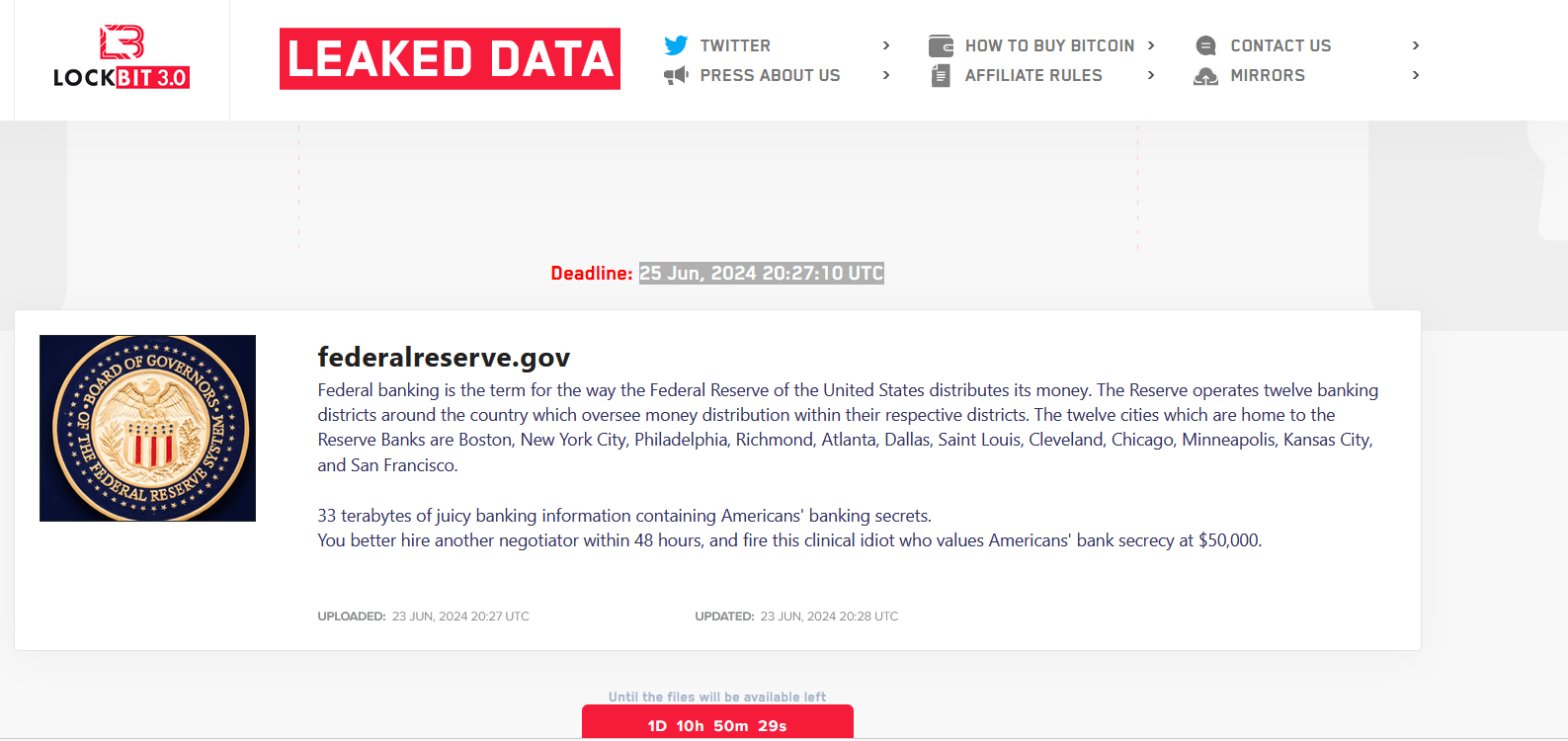
It’s also crucial to recognize that paying ransom demands doesn’t necessarily mean cybercriminals will restore an organization’s data. Remember, we’re dealing with criminals; we shouldn’t expect them to act morally or ethically. Many businesses have paid ransom demands, only for attackers to withhold decryption keys or provide faulty ones. Some groups even seem to find enjoyment in taunting their victims.
When Should Organizations Comply with Ransom Demands?
However, there are some situations where paying a ransom is the only option or the best course of action. For example, if a lack of system access could result in a loss of life – as may be the case with some healthcare, critical infrastructure, or industrial organizations – complying with ransom demands would likely be the most prudent option.
Some experts argue that organizations should pay ransoms when they are lower than the cost of restoring data or potential financial losses resulting from delayed recovery. This is a compelling argument at face value, but as noted, cybercriminals may not restore data after receiving a ransom and may even be motivated to attack the organization again. In some cases, data is even corrupted during decryption.
Protecting against These Attacks
It’s clear that, aside from a few specific situations, such as when human lives are at risk, organizations should avoid paying ransom demands. Essentially, paying ransom demands should only ever be a last resort. If an organization does suffer a ransomware attack, it’s almost always better to deploy cybersecurity professionals to restore company data. Organizations should develop and rehearse an incident response plan or even keep an incident response team on retainer to launch into action when an attack occurs.
It’s also crucial, of course, to take proactive measures against ransomware attacks. Often, the cost of preparation is significantly lower than that of a ransom. Businesses must implement effective cybersecurity measures. Here are some basic tools and techniques to help your organization ward off ransomware attackers:
- Endpoint Protection defends against ransomware by detecting and blocking malware, securing devices, enforcing policies, and providing real-time threat monitoring and response.
- Patch Management prevents ransomware attacks by promptly updating software to fix vulnerabilities, reducing the risk of exploitation by attackers.
- Data Backups protect against ransomware attacks by allowing restoration of encrypted files, eliminating the need to pay the ransom for decryption.
- Access Controls protect against ransomware by restricting user permissions, limiting malware’s ability to spread and encrypt critical files across the network.
- Employee Awareness Training helps prevent ransomware attacks by educating staff on identifying phishing attempts, avoiding malicious links, and reporting suspicious activities.
- A Dedicated Anti-Ransomware Solution is important because we know from all the headlines about major corporations getting disrupted by ransomware attacks that traditional solutions like EPP and EDR are missing these attacks.
- Resilience Testing protects against ransomware by identifying vulnerabilities, validating backup and recovery processes, and ensuring systems can withstand and recover from attacks.
Conclusion
If you take one thing away from this article, let it be this: prevention is better than a cure. By implementing an effective cybersecurity program, organizations significantly reduce the risk of suffering a ransomware attack and deciding whether to pay ransom demands. However, if you fall afoul of ransomware actors, try to avoid handing them money. Instead, invest in an incident response team – if you don’t, you risk being attacked again.
About the author: Josh Breaker-Rolfe
Josh is a Content writer at Bora. He graduated with a degree in Journalism in 2021 and has a background in cybersecurity PR. He’s written on a wide range of topics, from AI to Zero Trust, and is particularly interested in the impacts of cybersecurity on the wider economy.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, ransom)
如有侵权请联系:admin#unsafe.sh