2024-8-9 20:0:2 Author: securityboulevard.com(查看原文) 阅读量:3 收藏
Hello, My name is Chen, and I work as a threat intelligence analyst at Salt Security.
Every day, I dive into the complex world of cybersecurity, uncovering the hidden threats that hide in our digital lives. Today, I’d like to take you on a journey through the evolving landscape of API threats.
APIs are the quiet helpers of the digital world, allowing software applications to communicate easily with each other. They bring convenience and functionality to our digital interactions but also open doors to various vulnerabilities and risks.
Imagine APIs as bridges connecting islands of data and services. These bridges are essential for the smooth flow of information, but if not properly secured, they can allow unwanted people in or expose private information.
So now that we all agree that APIs, while super helpful, can also involve many risks, the question to be asked is, what are those risks, and how can we effectively map them?
Since API security is a relatively new domain, there is no standard methodology for achieving it. In this blog post, I want to share some standard techniques I use in my day-to-day job.
CVEs – Vulnerabilities By Type
Our first destination is the world of Common Vulnerabilities and Exposures (CVEs). Consider CVEs a lighthouse, highlighting hidden security flaws that we must recognize and understand to navigate the cybersecurity field safely.
One great resource for better understanding CVEs is CVEdetails. This site is a collection of detailed visualizations and valuable insights. It includes many interesting details, including this table:

The table summarizes all the CVEs found over the past decade, revealing the rise of various types of vulnerabilities. Web vulnerabilities like SQL injection and XSS truly stand out with their remarkable growth over the years.
In 2020, SQL injection-related CVEs were at 466. Fast forward to 2023, and this number has soared to 2,159—a staggering increase of 363.30% in just three years. Similarly, XSS has seen an impressive climb, with CVEs jumping from 2,203 in 2020 to 5,179 in 2023, marking a substantial 135.08% rise.
But our story doesn’t end there. As we delve deeper, we encounter CSRF, which saw its CVEs grow from 416 in 2020 to an astounding 1,398 in 2023, marking an increase of 236.05%. SSRF, too, has its tale of growth, with CVEs rising from 132 in 2020 to 248 in 2023, reflecting an 87.87% increase.
While this table provides great insights, as always in our domain, one source of information is rarely enough.
Take, for example, OAuth vulnerabilities. Salt-Labs’ previous publications indicate that OAuth is a popular and rising attack vector. However, this table does not seem to reflect this.
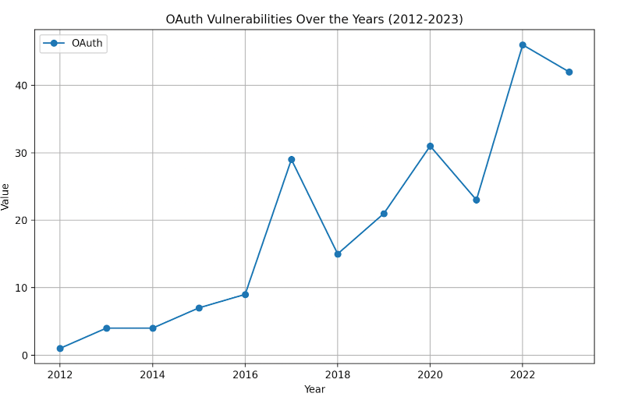
When looking at the raw CVE data from this website, it seems this information is available. I gathered all the CVEs related to OAuth over the past few years and calculated their numbers for each year. Here are the results of my investigation:

I’ve observed a significant increase in OAuth vulnerabilities. In 2012, there was just one CVE, whereas in 2023, there were 42 CVEs. This significant rise had a notable impact on our product, influencing its detection. For further details about our OAuth Protection Package, you can find more information right here.
Bug Bounty Reports
The second destination for better understanding the threat landscape is Bug Bounty reports. The bug bounty community has grown substantially over the past few years, and looking into the public reports and available information from them can yield fascinating insights.
If you inspect all of the categories related to web vulnerabilities and count the number of reports from 2014 to 2022. It’s important to note that I excluded 2023 from my analysis due to incomplete data.

You can quickly notice a clear rise in SSRF reports when delving into the data. In 2022, there was a significant increase, fitting well with the broader trends in the OWASP API 2023.
On the other hand, there’s been a sharp decline in reports of CSRF vulnerabilities. Once a significant concern, CSRF saw a substantial drop of 79.27% in reports from 2017 to 2022. This downward trend contrasts with the results from our CVE research. However, given that bug bounty data is typically more accurate, I suggest that CSRF might no longer be a focal point in the threat landscape in 2024.
Internal DB of Salt Security
So now that we have a better understanding of the API threat landscape from several different sources, we must ask ourselves how this correlates with the internal telemetry data we collect at Salt-Labs.
Focusing on categories such as ‘SQL injection’, ‘Code Injection’, ‘XSS’, and ‘Path Traversal’, based on 2023, we saw an increase in web vulnerabilities every month. At the beginning of 2024, the numbers within these key categories were 1.5 times higher than those recorded in 2023.
Our journey ends here, and what we’ve learned is alarming: web vulnerabilities are escalating and remain a significant threat in the security landscape. As we move into 2024, these issues will persist and potentially affect more companies.
How Salt Can Help
From day one, Salt Security could detect OAuth vulnerabilities and code injections. Recently, we extended these capabilities, launching a new, multi-layered OAuth protection package that can detect attempts to exploit OAuth and proactively fix vulnerabilities. We have enhanced our API protection platform with a comprehensive suite of new OAuth threat detections and posture rules to address the growing challenge of OAuth exploitation. The first API security vendor to launch deep OAuth threat detection capabilities. These innovations will empower organizations to identify and mitigate malicious attempts to exploit OAuth flows, ultimately safeguarding sensitive data and user accounts.
If you would like to learn more about Salt and how we can help you on your API Security journey through discovery, posture management, and run-time threat protection, please contact us, schedule a demo, or check out our website.
Action Items
- Keep Software Updated: Regularly update your operating system, browsers, and applications to protect against security vulnerabilities.
- Educate Yourself and Others: Stay informed about common cyber threats and educate friends and family about safe internet practices.
- Beware of Suspicious Links: Avoid clicking links or opening attachments from unknown sources, as these may lead to malicious sites that exploit these vulnerabilities.
- Boost Your Cybersecurity with Expert Partners: To enhance your protection against cyber threats, consider partnering with third-party companies specializing in cybersecurity. These experts can offer tailored solutions, continuous monitoring, and advanced threat detection, ensuring your systems stay secure and resilient.
*** This is a Security Bloggers Network syndicated blog from Salt Security blog authored by Chen Gafson. Read the original post at: https://salt.security/blog/exploring-the-dynamic-landscape-of-cybersecurity-threats
如有侵权请联系:admin#unsafe.sh