We have some thrilling news to share with you today. Our team at ANY.RUN is happy to announce the launch of our new integration with Splunk!
How this integration benefits you
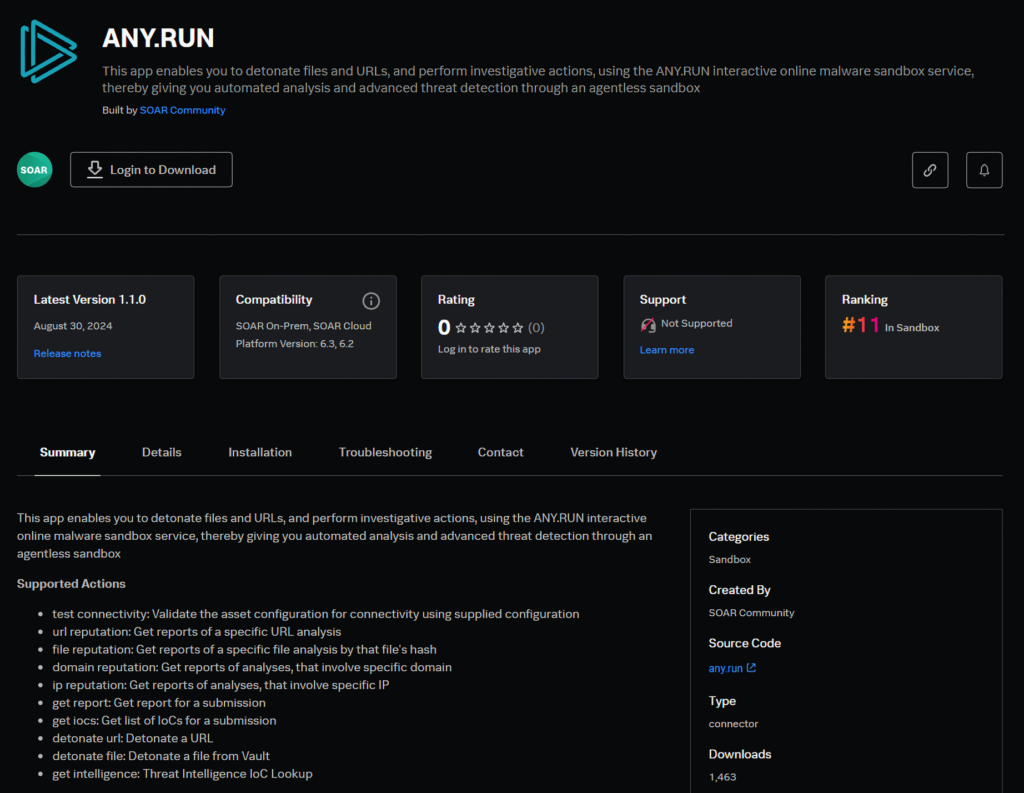
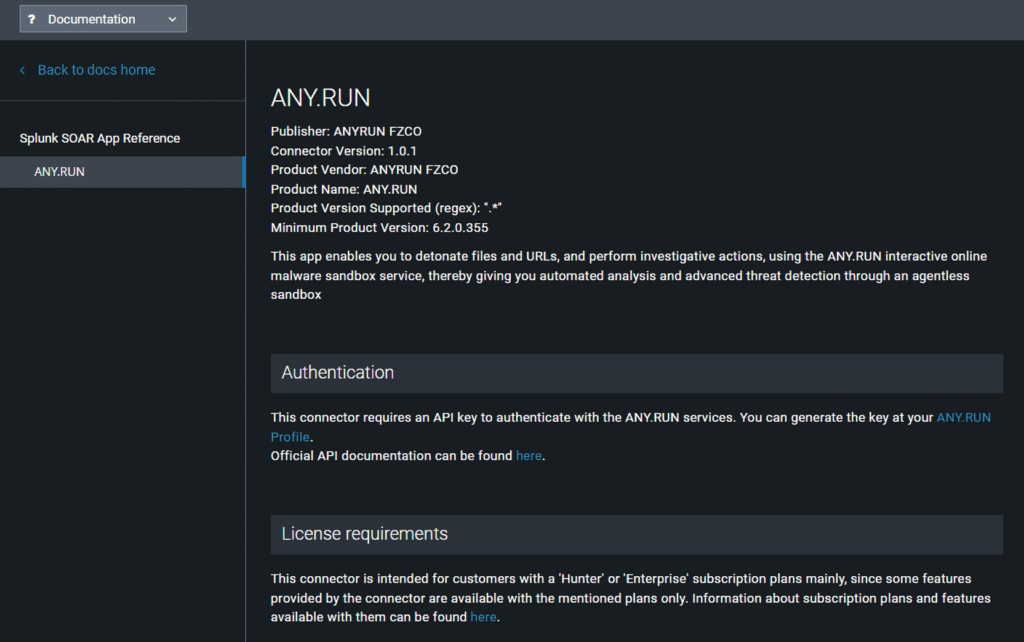
If you’re a Splunk user, you can now leverage ANY.RUN’s Interactive Sandbox and Threat Intelligence Lookup directly from your Splunk SOAR environment.
This means that you can analyze potentially malicious files and URLs in the sandbox and enrich your investigations with threat data from TI Lookup without leaving the familiar Splunk interface.
Our main goal with this integration is to give you more options and help you make the most out of ANY.RUN while working with familiar systems.
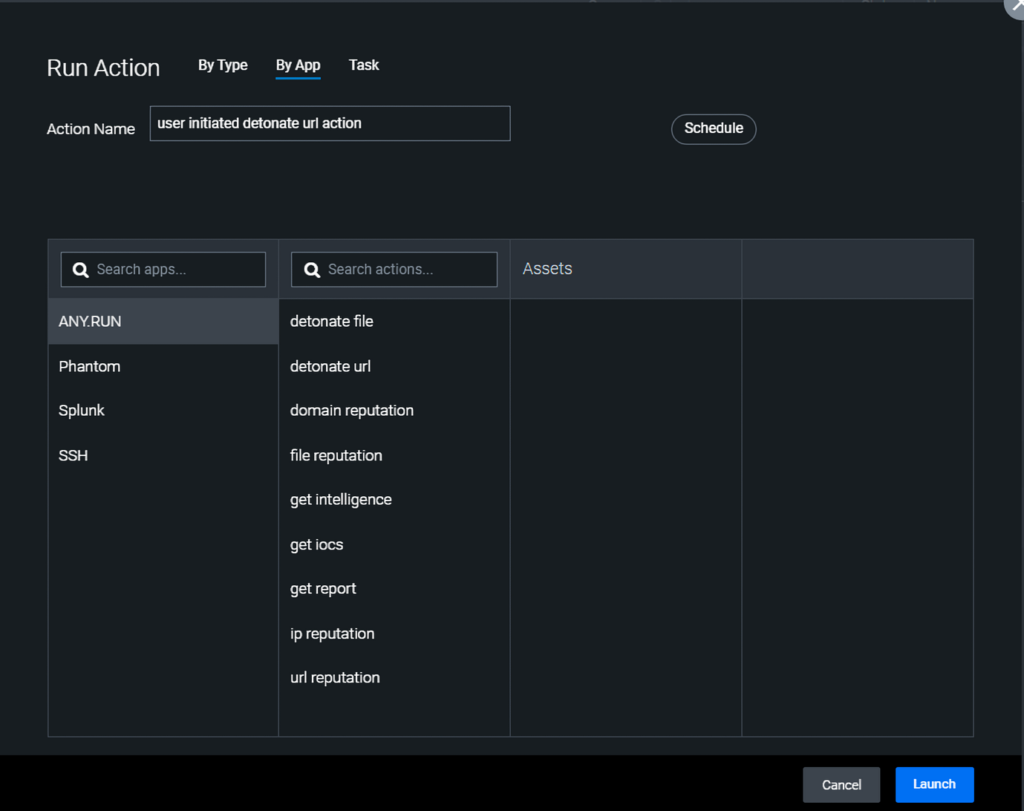
The integration supports a wide range of actions, from simple reputation checks to full detonation and analysis of suspicious objects.
Key Features
Comprehensive Threat Intelligence
The integration allows analysts to query ANY.RUN’s threat intelligence database directly from Splunk SOAR.
Automated Malware Analysis
One of the most powerful features of this integration is the ability to automatically detonate files and URLs in ANY.RUN’s sandbox.
This process can be triggered as part of a Splunk SOAR playbook, allowing for analysis of attachments in phishing emails or suspicious downloads detected by network monitors. You can also access any analysis session you launch in the sandbox to perform manual actions or gain a deeper understanding of the threat.
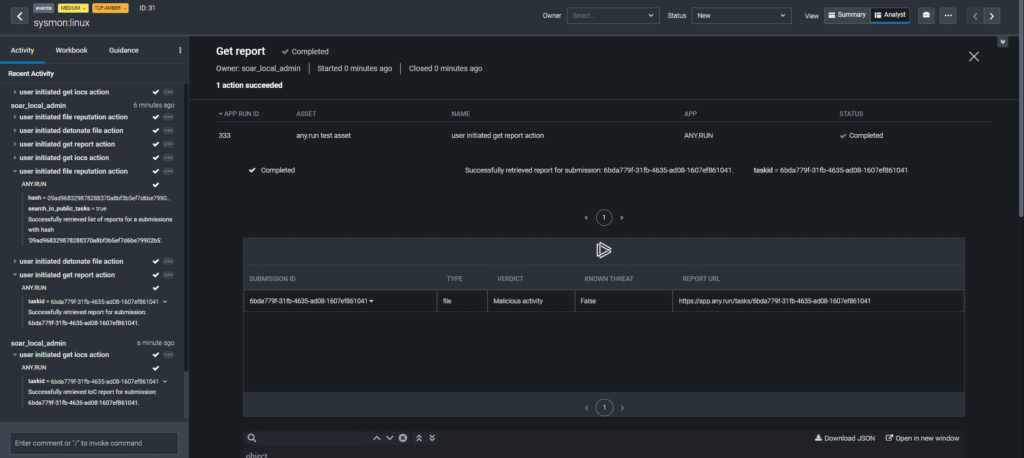
Detailed Reporting and IOC Extraction
The ‘get report’ action retrieves key analysis details, including the verdict on the sample’s threat level. You can also see the rest of the analysis results by navigating to the corresponding part of the interface.
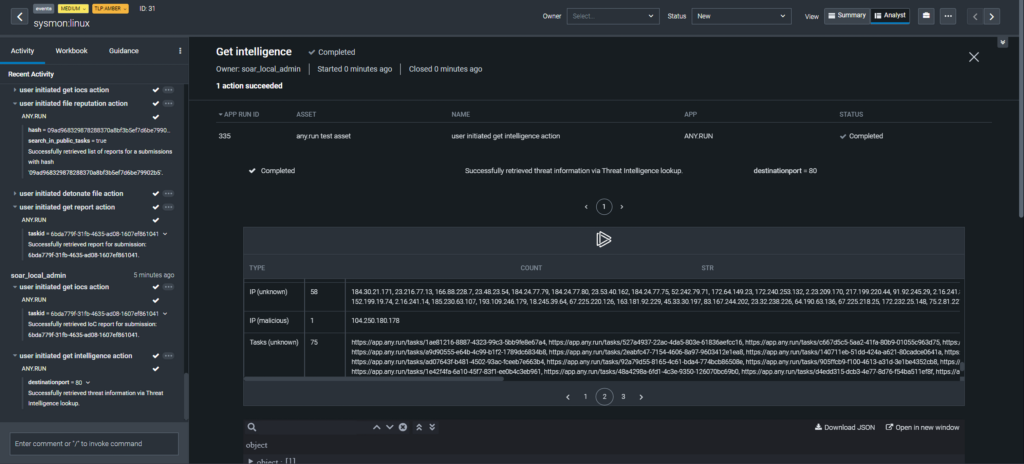
Advanced Threat Hunting
If you have ANY.RUN’s TI License, you can use the ‘get intelligence’ action to perform complex queries against ANY.RUN’s threat intelligence database.
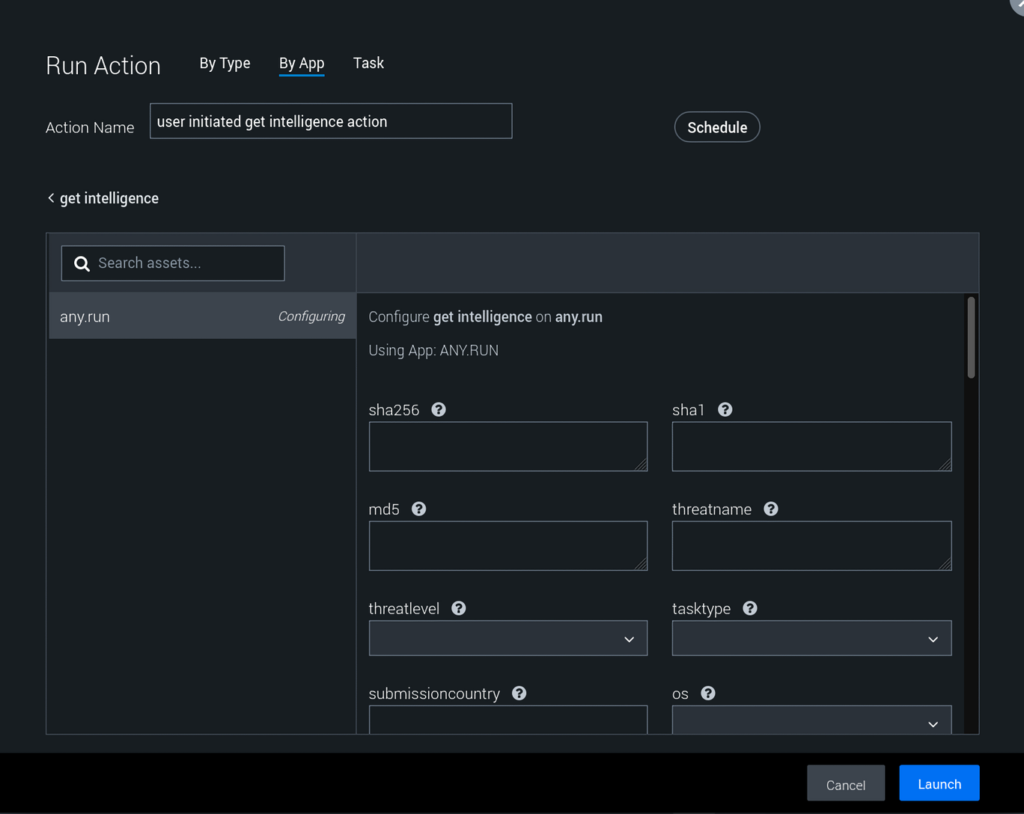
Search for specific file hashes, IP addresses, domains, or even MITRE ATT&CK techniques you uncover in previous analyses.
Real-World Application
Consider a scenario where a Splunk SOAR playbook is triggered by a potential phishing email.
The playbook could automatically extract any URLs and attachments from the email, then use the ‘url reputation’ action to check if the URLs have been previously analyzed by ANY.RUN.
- For new or suspicious URLs, the playbook could use the ‘detonate url’ action to analyze them in a sandbox environment.
- Similarly, for attachments, the ‘detonate file’ action could be used to safely execute and analyze them.
The playbook could then retrieve detailed reports and IOCs using the ‘get report’ and ‘get iocs’ actions.
Finally, it could use the extracted IOCs to automatically update firewall rules, trigger endpoint scans, or create new detection rules in the SIEM.
How to Set it Up
To leverage this new integration, users will need a Splunk SOAR environment and an ANY.RUN account with API access. Preferably, a ‘Hunter’ or ‘Enterprise’ subscription is recommended for full feature access.
The setup process is straightforward:
- Configure a new ANY.RUN asset in Splunk SOAR.
- Provide the ANY.RUN base URL (typically https://api.any.run).
- Enter the API key from your ANY.RUN profile page.
- Set a default timeout for API requests.
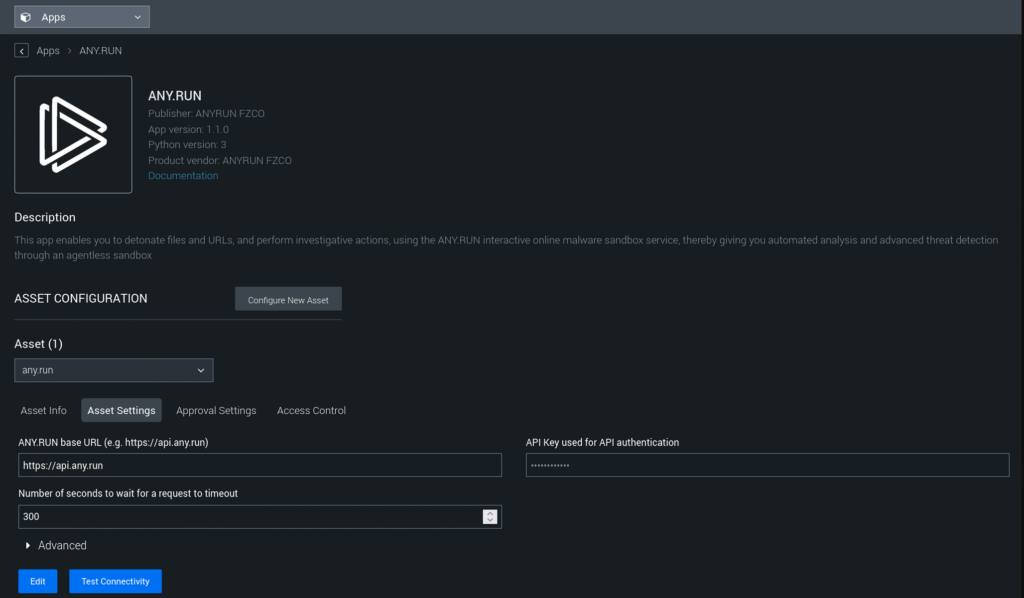
Once configured, the ANY.RUN actions will be available for use in Splunk SOAR playbooks and for manual invocation by analysts.
About ANY.RUN
ANY.RUN helps more than 400,000 cybersecurity professionals worldwide. Our interactive sandbox simplifies malware analysis of threats that target both Windows and Linux systems. Our threat intelligence products, TI Lookup, Yara Search and Feeds, help you find IOCs or files to learn more about the threats and respond to incidents faster.
With ANY.RUN you can:
- Detect malware in seconds
- Interact with samples in real time
- Save time and money on sandbox setup and maintenance
- Record and study all aspects of malware behavior
- Collaborate with your team
- Scale as you need
