
In November 2023, we introduced the Secure Future Initiative (SFI) to advance cybersecuri 2024-9-23 23:0:0 Author: www.microsoft.com(查看原文) 阅读量:16 收藏
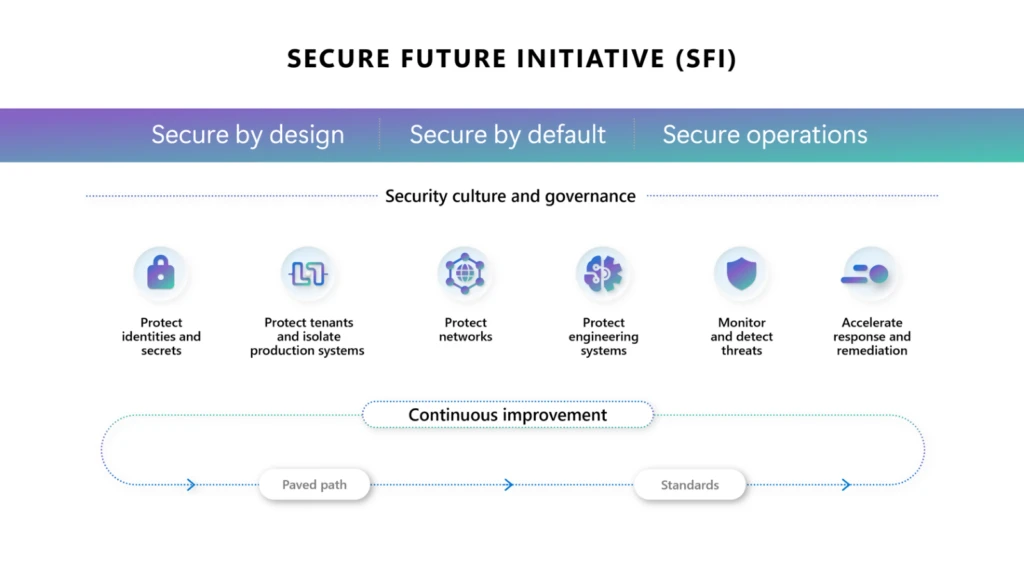
In November 2023, we introduced the Secure Future Initiative (SFI) to advance cybersecurity protection for Microsoft, our customers, and the industry. In May 2024, we expanded the initiative to focus on six key security pillars, incorporating industry feedback and our own insights. Since the initiative began, we’ve dedicated the equivalent of 34,000 full-time engineers to SFI—making it the largest cybersecurity engineering effort in history. And now, we’re sharing key updates and milestones from the first SFI Progress Report.
A focus on security above all else
At Microsoft, we recognize our unique responsibility in safeguarding the future for our customers and community. As a result, every individual at Microsoft plays a pivotal role to “prioritize security above all else.” We’ve made significant progress in fostering a security-first culture. Some of the main updates include:
- To improve governance, we announced the creation of a new Cybersecurity Governance Council and the appointment of Deputy Chief Information Security Officers (Deputy CISOs) for key security functions and all engineering divisions. Led by our CISO Igor Tsyganskiy, the Deputy CISOs form the Cybersecurity Governance Council, and are responsible for the company’s overall cyber risk, defense, and compliance.
- Security is now a core priority for all employees at Microsoft and will be included in their performance reviews. This will empower every employee and manager to commit to—and be accountable for—prioritizing security, and a way for us to codify an employee’s contributions to SFI and celebrate impact.
- We launched the Security Skilling Academy, a personalized learning experience of security-specific, curated trainings for all employees worldwide. The academy ensures that no matter the role, employees are equipped to prioritize security in their daily work and identify the direct part they have in securing Microsoft.
- To ensure accountability and transparency at the highest levels, Microsoft’s senior leadership team reviews SFI progress weekly and updates are provided to Microsoft’s Board of Directors quarterly. Additionally, Microsoft’s senior leadership team now has security performance directly linked to compensation.
Pillar highlights: A comprehensive approach to cybersecurity
We’ve also made progress across our six key pillars, each representing a critical area of cybersecurity focus. These pillars guide our ongoing work to raise the bar for security across Microsoft and help us meet the evolving demands of the security landscape. These are the most recent updates across these areas:
- Protect identities and secrets: We completed updates to Microsoft Entra ID and Microsoft Account (MSA) for our public and United States government clouds to generate, store, and automatically rotate access token signing keys using the Azure Managed Hardware Security Module (HSM) service. We have continued to drive broad adoption of our standard identity SDKs, which provide consistent validation of security tokens. This standardized validation now covers more than 73% of tokens issued by Microsoft Entra ID for Microsoft owned applications. We have extended standardized security token logging in our standard identity SDKs to support threat hunting and detections and enabled those in several critical services ahead of broad adoption. We completed enforcement of the use of phishing-resistant credentials in our production environments and implemented video-based user verification for 95% of Microsoft internal users in our productivity environments to eliminate password sharing during setup and recovery.
- Protect tenants and isolate production systems: We completed a full iteration of app lifecycle management for all of our production and productivity tenants, eliminating 730,000 unused apps. We eliminated 5.75 million inactive tenants, drastically reducing the potential cyberattack surface. We implemented a new system to streamline the creation of testing and experimentation tenants with secure defaults and strict lifetime management enforced. We have deployed more than 15,000 new production-ready locked-down devices in the last three months.
- Protect networks: More than 99% of physical assets on the production network are recorded in a central inventory system, which enriches asset inventory with ownership and firmware compliance tracking. Virtual networks with backend connectivity are isolated from the Microsoft corporate network and subject to complete security reviews to reduce lateral movement. To help customers secure their own deployments, we have expanded platform capabilities such as Admin Rules to ease the network isolation of Platform as a Service (PaaS) resources such as Azure Storage, SQL, Cosmos DB, and Key Vault.
- Protect engineering systems: 85% of our production build pipelines for the commercial cloud are now using centrally governed pipeline templates, making deployments more consistent, efficient, and trustworthy. We have slimmed down the lifespan of Personal Access Tokens to seven days, disabled Secure Shell (SSH) protocol access for all Microsoft internal engineering repos, and significantly reduced the number for elevated roles with access to engineering systems. We also implemented proof of presence checks for critical chokepoints in our software development code flow.
- Monitor and detect threats: We have made significant progress enforcing that all Microsoft production infrastructure and services adopt standard libraries for security audit logs, to ensure relevant telemetry is emitted, and retain logs for a minimum of two years. For instance, we have established central management and a two-year retention period for identity infrastructure security audit logs, encompassing all security audit events throughout the lifecycle of current signing keys. Similarly, more than 99% of network devices are now enabled with centralized security log collection and retention.
- Accelerate response and remediation: We updated processes across Microsoft to improve Time to Mitigate for critical cloud vulnerabilities. We began publishing critical cloud vulnerabilities as common vulnerability and exposures (CVEs), even if no customer action is required, to improve transparency. We established the Customer Security Management Office (CSMO) to improve public messaging and customer engagement for security incidents.
Reaffirming our security commitment
In security, consistent progress is more important than “perfection” and this is reflected in the scale of resources mobilized to achieve our SFI objectives. The collective work we are doing to continually increase protection, eliminate legacy or noncompliant assets, and identify remaining systems for monitoring conclusively measures our success. As we look ahead, we remain committed to ongoing improvement. SFI will continue to evolve, adapting to new cyberthreats and refining our security practices. Our commitment to transparency and industry collaboration remains unwavering. Earlier in 2024, Microsoft became a major supporter of the United States Cybersecurity and Infrastructure Security Agency’s (CISA) Secure by Design pledge, reinforcing our dedication to embedding security into every aspect of our products and services. Additionally, we continue to integrate recommendations from the Cyber Safety Review Board (CSRB) to strengthen our cybersecurity approach and enhance resilience.
The work we’ve done so far is only the beginning. We know that cyberthreats will continue to evolve, and we must evolve with them. By fostering this culture of continuous learning and improvement, we are building a future where security is not just a feature, but a foundation.
SFI Progress Report
Discover the key updates and milestones from the first SFI Progress Report.
Learn more
To learn more about Microsoft Security solutions and Microsoft’s Secure Future Initiative, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us on LinkedIn (Microsoft Security) and X (@MSFTSecurity) for the latest news and updates on cybersecurity.
如有侵权请联系:admin#unsafe.sh