Linux telemetry involves gathering and sending data from a Linux-based system to an 2024-9-25 01:57:57 Author: www.hackingarticles.in(查看原文) 阅读量:26 收藏
Linux telemetry involves gathering and sending data from a Linux-based system to an external server or service. The purpose of this process is often to monitor system performance, provide diagnostics, enable analytics, or improve system functionality. The collected data may encompass system performance indicators, usage patterns, hardware specifications, error logs, and other relevant information. In this article, we are going to discuss why telemetry can be seen as a potential threat to privacy, even when used for legitimate purposes. Also, we will discuss the methods to make the system more secure than before.
Table of Contents
- Secure OS Installation
- Removing the packages
- Settings in ubuntu
- Disable diagnostics reporting
- Disable lock screen notifications
- Disable tracking of recent files
- Turning off the problem reporting
- Turning off the screen blank
- Disable automatic screen locking
- Permanently delete option
- Show hidden files
- BleachBit
- KeePassXC
- Virus Scanner
- Metadata removal
- Firefox profilemaker
- Flatpak
- LibreWolf VeraCrypt
- Tor Browser
- Proton VPN
- NextDNS
- Conclusion
Secure OS Installation
Ideally we should consider the POP!_OS by System76 for installation, it is based on Ubuntu but redesigned for privacy and security. However, here we are considering the Ubuntu 22.04.4 version. We are considering this version of Ubuntu because the versions which begin with an odd number or end with the 0.10 are interim releases with a short support cycle and we will be needing a version which has the Long Term Support (LTS). Hence only versions which begin with an even number and end with 0.04 should be considered. We will discuss the steps to make it secure from the installation itself.
Step 1: Download the ubuntu-22.04.4-desktop-amd64.iso image from the following URL: https://old-releases.ubuntu.com/releases/22.04/

Step 2: Create a new virtual machine in VMware workstation PRO.

Step 3: Select the path of the installer disc.

Step 4: Enter the Full name, User name, Password and Confirm.

Step 5: Select the Normal installation and select both options in the Other options.

Step 6: Select Erase disk and install Ubuntu, click on Advanced features.

Step 7: Inside Advanced features, use the following options: Use LVM with the new Ubuntu installation and Encrypt the new Ubuntu installation for Security.

Step 8: Enter the Security key and click on Install now.

Step 9: Select Continue for the Write the changes to disks? Option.

Step 10: Enter the details in the Who are you? Installation option.

Once the installation is complete, you will see an ubuntu login screen like the one shown below.

Removing the packages
After login into the ubuntu machine, we can remove all those packages, which some how transfer the user/system information to an outside source either for improvement, feedback, or diagnostic purpose.
Starting with the whoopsie package, it is a crash reporting daemon designed to capture application crashes and send anonymized reports to the Ubuntu servers.
The command to remove its entire content is:
sudo apt purge apport apport-symptoms popularity-contest ubuntu-report whoopsie

We will also remove the motd-news package, it is responsible for delivering dynamic news messages as part of the Message of the Day (MOTD) system.
The command to remove its entire content is:
sudo rm /etc/update-motd.d/50-motd-news

Settings in ubuntu
After removing the packages, we can now proceed with the essential settings in ubuntu, which can help us to be more secure. Here we are going to show it using the terminal and how the same can be done on the GUI.
Disable diagnostics reporting
Apport is a crash reporting tool found in Ubuntu and other Linux-based operating systems. Its primary function is to identify when programs crash, gather detailed information about the error, and create reports that assist in diagnosing and troubleshooting the problem.
Setting the app crash report to false does not gives the apport crash pop-up notifications.
gsettings set com.ubuntu.update-notifier show-apport-crashes false

Disable lock screen notifications
Lock screen notifications can disclose various things which might be private to the user. So, we need to disable the lock screen notifications.
gsettings set org.gnome.desktop.notifications show-in-lock-screen false

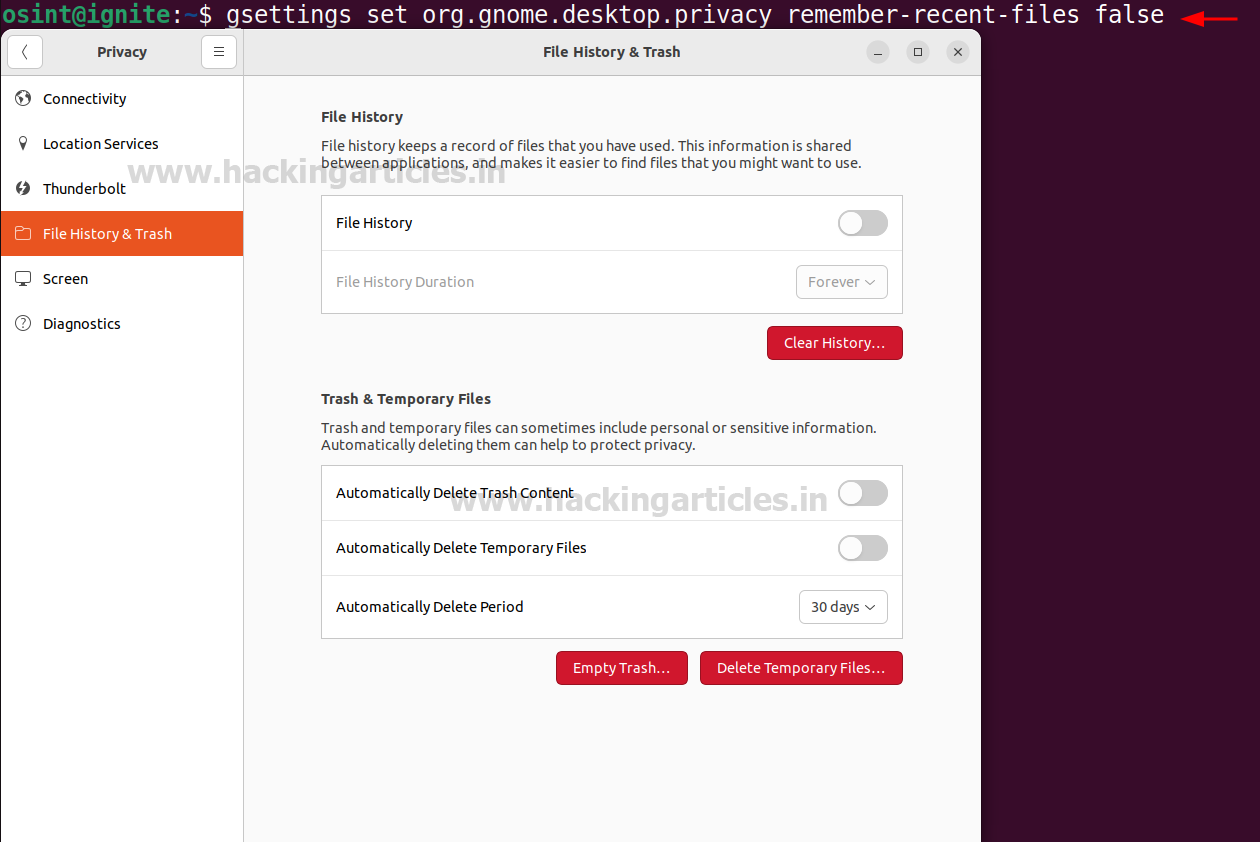
Disable tracking of recent files
To disable the tracking of recently opened files in the ubuntu machine, we can set the remember-recent-files to false.
gsettings set org.gnome.desktop.privacy remember-recent-files false

Turning off the problem reporting
Open the Privacy setting in the GUI and inside Diagnostics set the Send error reports to Canonical to Never. By doing this no error reports will be shared to the Canonical and a privacy can be maintained.

Turning off the screen blank
To disable the automatic screen blanking or locking due to inactivity, we can set the Screen Blank option to Never and Automatic Suspend to Off inside the Power options. Due to this option, the display will remain indefinitely on as the inactivity action would never be triggered.
gsettings set org.gnome.desktop.session idle-delay 0

Disable automatic screen locking
To disable the automatic lock when the system remains idle, click the Privacy option, then click Screen and disable all options.
gsettings set org.gnome.desktop.screensaver lock-enabled false gsettings set org.gnome.desktop.screensaver ubuntu-lock-on-suspend false

Permanently delete option
If we want to permanently delete an object without moving it to the trash, we can run the following command to get a permanently delete option for every file.
gsettings set org.gnome.nautilus.preferences show-delete-permanently true

After running the above command, we can now see that we have Delete permanently option available for all the files.

Show hidden files
To permanently enable the view hidden files option, we can run the following command:
gsettings set org.gnome.nautilus.preferences show-hidden-files true

BleachBit
BleachBit is an open-source application that functions as a system cleaner and privacy tool. It aims to optimize disk space and safeguard user privacy by eliminating unwanted files and data from your computer.
Installation of BleachBit can be performed using the following command:
sudo apt install bleachbit

KeePassXC
KeePassXC is an open-source tool, which is used for password management. It helps users to securely store and manage their passwords and sensitive information.
Installation of KeePassXC can be performed using the following command:
sudo apt install keepassxc

Virus Scanner
Here we will be installing the ClamAV, it is an open-source antivirus which is used for scanning the malware and malicious files. The GUI of the ClamAV is call as the ClamTK and to fetch the latest malware detection updates, we need to enable the freshclam.
apt install clamav clamav-daemon apt install clamtk sudo systemctl stop clamav-freshclam sudo systemctl enable clamav-freshclam --now

Metadata removal
There are cases while transferring the files sometimes metadata containing private information is also transferred along with the file. To remove the metadata from the file we are going to use the MAT2 tool (Metadata Anonymisation Toolkit 2).
To install the MAT2 tool, we can use the following commands:
sudo apt install mat2

Firefox profilemaker
To download a customized browser setup as per the requirement, we can use the firefox profilemaker. It provides us a variety of configurations, which we can set and then download the profile file or preference file which can be imported into the browser. This helps in ensuring the full customization as per the user’s need.
The profile setup can be performed using the following URL:

Flatpak
Flatpak is a tool which is used to install and run the applications within a sandboxed environment. Applications installed via Flatpak are sandboxed, meaning they run in an isolated environment. This prevents apps from interfering with the system or accessing unauthorized resources, increasing security.
Following are the commands to install the flatpak:
sudo apt install flatpak sudo apt install gnome-software-plugin-flatpak flatpack remote-add --if-not-exists flathub https://dl.flathub.org/report/flathub.flatpakrepo

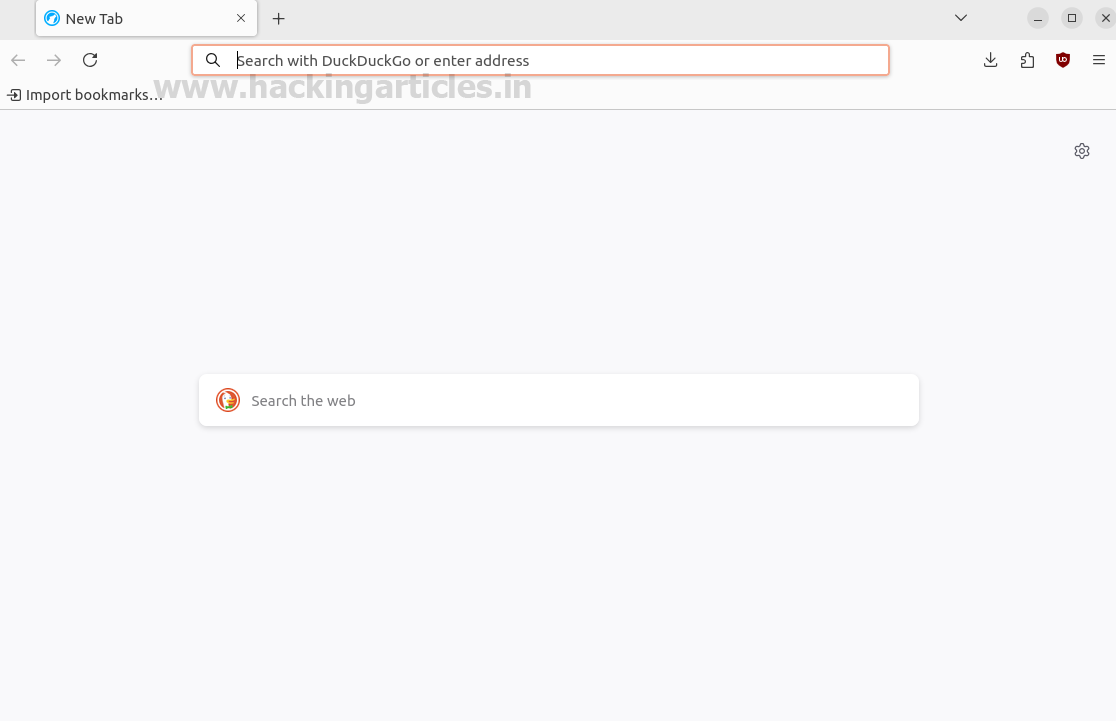
LibreWolf
LibreWolf is a web browser focused on privacy, it comes with improved security settings by default. It eliminates telemetry, data collection, and tracking features found in standard Firefox, offering a more private browsing experience.
To run the lLibreWolf using the flatpack we can use the following command:
flatpack run io.gitlab.librewolf-community
VeraCrypt
To create a virtual encrypted disk or encrypt the entire partition or storage devices, we can use VeraCrypt. To perform its installation, we need to add the unit193/encryption repository in the PPA (Personal Package Archive) and then update the system and install VeraCrypt.
sudo add-apt-repository ppa:unit193/encryption -y sudo apt update sudo apt install veracrypt

After installation we can launch the VeraCrypt.

Tor Browser
To maintain complete anonymity, Tor browser is an amazing browser to search for things. It directs the traffic through the Tor network making it difficult to track.
It can be downloaded from the following webite:
https://www.torproject.org/download/

After downloading, the file can be extracted, and the browser can be started. By using –register-app flag, the Tor browser can be launched from the applications menu.
./start-tor-browser.desktop --register-app

After successful installation, the browser can be launched from the applications menu.

Proton VPN
Proton VPN is a widely used VPN which gives 3 locations as a free service. It helps to remain anonymous and perform the tasks. It can be downloaded from the following link: https://protonvpn.com/support/official-linux-vpn-debian/
Following are the steps to install the Proton VPN:
sudo wget https://repo.protonvpn.com/debian/dists/stable/main/binary-all/protonvpn-stable-release_1.0.4_all.deb

sudo dpkg -i ./protonvpn-stable-release_1.0.4_all.deb && sudo apt update

echo "62a9d849835de8a5664cf95329458bf1966780b15cec420bf707b5f7278b9027 protonvpn-stable-release_1.0.4_all.deb" | sha256sum --check -

sudo apt update && sudo apt upgrade sudo apt install proton-vpn-gnome-desktop

After the installation is complete, we can launch the Proton VPN.

After connecting with the Netherlands location, we can check the public IP.

NextDNS
NextDNS is a cloud-based DNS solution which helps to perform content filtering and many more things. It serves as an alternative to the DNS provided by the ISP. There are times when we want to block access to certain websites in our system and want to check what were the websites visited by the user.
The profile can be setup using the DNS address given at the following link:
https://my.nextdns.io/2f7664/setup

After copying the systemd-resolved addresses, we can add this in the /etc/systemd/resolved.conf file.
sudo nano /etc/systemd/resolved.conf cat /etc/systemd/resolved.conf

After the addresses are added in the configuration file. Inside the browser, navigate to the Settings and select the option to choose the DNS over HTTPS and it should be set to Max Protection. Inside Max Protection select the custom DNS and enter the NextDNS URL shown in the DNS over HTTPS.

After the configuration is complete, the NextDNS setup will show a All good! status.

We can also restrict websites from visiting by adding them in the Parental Control list.

The user is no longer able to visit the website.

There is also a feature to check the logs, which can help in tracking the websites visited before in the Logs option.

Conclusion
As we become aware of the effects of telemetry, we can make choices that lead to a safer and more private computing environment. By using the above methods and tools, we can safeguard user ‘s privacy and can significantly reduce our exposure to unwanted data collection.
Author: Vinayak Chauhan is an InfoSec researcher and Security Consultant. Contact here
如有侵权请联系:admin#unsafe.sh