2024-9-27 07:22:30 Author: securityaffairs.com(查看原文) 阅读量:8 收藏
Hacking Kia cars made after 2013 using just their license plate
Pierluigi Paganini
September 26, 2024

Researchers discovered critical flaws in Kia’s dealer portal that could allow to hack Kia cars made after 2013 using just their license plate.
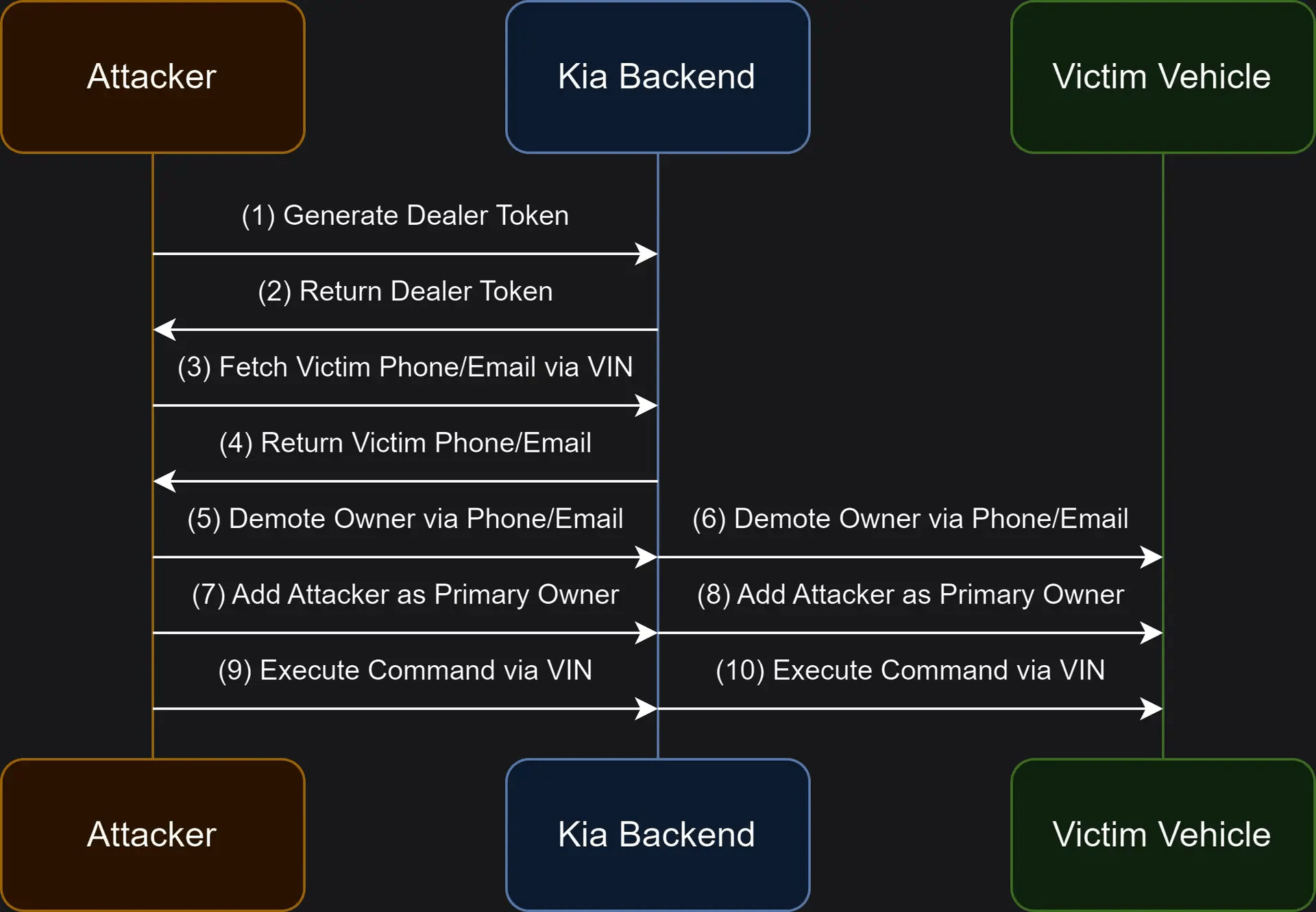
In June 2024, a team of experts (Neiko Rivera, Sam Curry, Justin Rhinehart, Ian Carroll) discovered multiple vulnerabilities in Kia vehicles that allowed remote control of key functions using their license plates. The researchers demonstrated how to execute the attack in about 30 seconds on any hardware-equipped vehicle, regardless of its Kia Connect subscription status. Additionally, attackers could secretly obtain personal information such as the victim’s name, phone number, email, and physical address. This would allow the attacker to add themselves as a second, hidden user on the victim’s vehicle without their knowledge.
In 2022, some of the members of the above team of experts including the popular cybersecurity expert Sam Curry, discovered another set of vulnerabilities impacting over a dozen car makers.
The vulnerabilities could have been exploited by threat actors to perform a broad range of malicious activities, from unlocking cars to tracking them.
The flaws discovered by the experts affected vehicles of popular brands, including Kia, Honda, Infiniti, Nissan, Acura, Mercedes-Benz, Genesis, BMW, Rolls Royce, Ferrari, Ford, Porsche, Toyota, Jaguar, Land Rover. The research team also discovered flaws in the services provided by Reviver, SiriusXM, and Spireon.
The exploitation of some flaws gave the experts access to hundreds of Mercedes mission-critical internal applications via improperly configured SSO. An attacker could have also exploited them to achieve remote code execution on multiple systems. The flaws also allowed attackers to access the content of the memory of some systems, leading to the exposure of Mercedes’ employee/customer PII.
In the case of BMW and Rolls Royce, experts found SSO vulnerabilities that allowed them to access any employee application as any employee. The experts were able to access to internal dealer portals and retrieve sales documents for BMW by providing VIN numbers.
The experts were also able to access any application locked behind SSO on behalf of any employee, including applications used by remote workers and dealerships.
Curry explained that its team demonstrated the vulnerabilities using a custom-designed tool.
“We built a tool to demonstrate the impact of these vulnerabilities where an attacker could simply (1) enter the license plate of a Kia vehicle, then (2) execute commands on the vehicle after around 30 seconds.” wrote Curry. “These vulnerabilities have since been fixed, this tool was never released, and the Kia team has validated this was never exploited maliciously.“
Curry explained that he and his colleagues focused on Kia’s owners.kia.com website and the Kia Connect iOS app (com.myuvo.link) because both could execute internet-to-vehicle commands. While both served the same function, they handled vehicle commands differently. The website used a reverse proxy to forward user commands to the backend service (api.owners.kia.com), which actually executed the commands. In contrast, the mobile app accessed the API directly. An example HTTP request demonstrated how the website proxies an API request to unlock a car door.
The researchers also investigated how Kia performed vehicle activations for new purchases. They discovered that Kia would send a registration link to the customers’ email addresses, allowing them to register their vehicle or add it to their Kia account. Inspecting the link the experts noticed the use of a previously unknown domain, kiaconnect.kdealer.com, used to hand new vehicle registrations using a token and VIN number.
Further investigation revealed that dealer systems forwarded requests similarly to how the owners.kia.com site did. The researchers dug into the website’s JavaScript and discovered various dealer-only functionalities, such as vehicle and account lookups. The experts attempted to access the Kia dealer endpoints using their own token and vehicle VIN for testing purposes, but they failed.
Then they attempted to register as a dealer to generate a valid access token for the dealer’s system. By mimicking the registration process for the dealer site, they successfully created an account, logged in, and obtained a session token.
The token allowed them to access backend dealer APIs, then they successfully extracted sensitive information like the vehicle owner’s name, email, phone number, and other details. This hack potentially allows access to other dealer-endpoints using a valid dealer account and token.
Upon analyzing Kia’s JavaScript code, they discovered how to exploit enrollment, unenrollment, and vehicle modification endpoints to gain unauthorized access to a victim’s vehicle.

POST /apps/services/kdealer/apigwServlet.html HTTP/1.1
Host: kiaconnect.kdealer.com
Httpmethod: POST
Apiurl: /ownr/dicve
Appid: 123e4567-e89b-12d3-a456-426614174000
{
"vin": "5XYRK4LFXMG016215",
"loginId": "[email protected]"
}“Finally, we’ll assign our attacker-controlled email as the primary owner of the vehicle. This will allow us to send arbitrary commands to the vehicle.” concludes Curry.
“The above four HTTP requests could be used to send commands to pretty much any Kia vehicle made after 2013 (see “Vehicles Affected” table for specifics) using only the license plate.
From the victim’s side, there was no notification that their vehicle had been accessed nor their access permissions modified. An attacker could resolve someone’s license plate, enter their VIN through the API, then track them passively and send active commands like unlock, start, or honk.”
The good news is that the researchers reported the flaws to the car maker that has fixed them. Kia is not aware of attacks in the wild that have exploited these flaws.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, car hacking)
如有侵权请联系:admin#unsafe.sh