2024-10-1 21:16:26 Author: cyble.com(查看原文) 阅读量:2 收藏
Key takeaways
- Cyble Research and Intelligence Labs (CRIL) uncovered a sophisticated attack that leverages legitimate tools such as Visual Studio (VS) Code and GitHub.
- The Threat Actor (TA) used a.LNK file as the initial attack vector, potentially delivered through spam or phishing emails. The .LNK file is disguised as a legitimate setup file, using an MSI setup icon to deceive users into executing it.
- Upon execution, the .LNK file silently downloads a Python distribution package and uses it to run a malicious Python script.
- The TA leverages a VScode tool to initiate a Remote Tunnel and retrieve an activation code, which the TA can use to gain unauthorized remote access to the victim’s machine. This enables the TA to interact with the system, access files, and perform additional malicious activities.
- To maintain persistence, the TA creates a scheduled task designed to automatically trigger the execution of a malicious Python script with SYSTEM privileges and high priority.
- Similar tactics, techniques, and procedures (TTP) were employed by the Chinese APT group, Stately Taurus, in cyber espionage campaigns aimed at organizations throughout Europe and Asia.
Overview
Cyble Research and Intelligence Lab (CRIL) uncovered a campaign that leverages a suspicious .LNK file as the initial attack vector. This file, potentially delivered via spam emails, downloads a Python distribution package that is then used to execute an obfuscated Python script retrieved from a paste site. At the time of publishing this research, this script had no detections on VirusTotal (VT), making it difficult to identify through standard security measures.
Once executed, the Python script establishes persistence by creating a scheduled task with system privileges and high priority. It checks if Visual Studio Code (VSCode) is installed on the victim’s machine. If not, the script downloads the standalone VSCode CLI from a trusted source. Using VSCode, the script creates a remote tunnel, sharing an activation code with the TA, which facilitates unauthorized remote access to the victim’s machine.
The VSCode Remote – Tunnels extension is typically used to connect to a remote machine, such as a desktop PC or virtual machine (VM), via a secure tunnel. This enables users to access the machine from any VSCode client without the need for SSH. However, in this campaign, the TA exploits this feature, using it to establish a remote connection to the victim’s system for malicious purposes.
This attack method mirrors tactics previously observed in campaigns by the Stately Taurus Chinese APT group, as documented by Unit42 researchers. In this blog, we will examine how the TA cleverly uses legitimate tools like VSCode and GitHub to conceal their activity and establish unauthorized remote connections. The figure below illustrates the infection chain.

Technical Analysis
CRIL has identified a campaign involving a suspicious .LNK file masquerading as an installer. When executed, it displays a fake “Successful installation” message in Chinese (“安裝成功“). However, in the background, it silently downloads additional components using the curl utility, including a Python distribution package named “python-3.12.5-embed-amd64.zip”.
The .LNK file then creates a directory at “%LOCALAPPDATA%\Microsoft\Python” and extracts the contents of the zip archive using tar.exe into this location. Afterward, it downloads a malicious script from a paste.ee site via the URL “hxxps[:]//paste[.]ee/r/DQjrd/0” and saves it as “update.py” in the same location. Once the download is complete, the “update.py” is executed using “pythonw.exe” without showing a console window. The contents of the LNK file are shown below:

Update.py
The script begins by checking whether Visual Studio Code (VSCode) is already installed on the system. It does this by verifying the existence of the directory located at “%LOCALAPPDATA%\microsoft\VScode.” If this directory is not found, indicating that VSCode is not installed, the script then proceeds to download the VSCode Command Line Interface (CLI) from a Microsoft source: “hxxps://az764295.vo.msecnd.net/stable/97dec172d3256f8ca4bfb2143f3f76b503ca0534/vscode_cli_win32_x64_cli[.]zip.” Once downloaded, the zip file is extracted, and the executable file “code.exe” is placed into the “%LOCALAPPDATA%\microsoft\VScode” directory

Persistence
The script then proceeds to create a scheduled task named “MicrosoftHealthcareMonitorNode” to ensure the persistence of its malicious activities. It is designed to execute the “update.py” script using “pythonw.exe,” which runs without showing a console window, allowing the malicious activity to stay hidden. Before creating the task scheduler entry, the script checks if it already exists by running the command “schtasks /query /tn MicrosoftHealthcareMonitorNode” to avoid creating duplicates.
The configuration of this task varies depending on the user’s privilege level. For non-admin users, the task is set to run every four hours, beginning at 8:00 AM, ensuring that the malicious script is executed at regular intervals. On systems where the user has administrative privileges, the task is configured to trigger at logon, running with elevated SYSTEM privileges and high priority, which grants it more control and less likelihood of being interrupted. The figure below shows the Schedule task entry created by the malware.

Creating Remote Tunnel
The script next checks if “code.exe” is already running in the background by inspecting the output of the “tasklist” command. If it detects that “code.exe” is not active, then proceeds to execute “code.exe” to log out any active remote sessions. This is done by issuing the command “code.exe tunnel user logout,” which ensures the termination of any existing remote tunnels connected to the victim’s system. This step is crucial for the TA, as it allows them to establish a fresh remote tunnel for future interactions with the victim’s system.

After ensuring the existing tunnel is closed, the script initiates a new process using the command:
- code.exe –locale en-US tunnel –accept-server-license-terms –name <COMPUTERNAME>
This command initiates a remote tunnel, and the script automatically associates it with a GitHub account for authentication. Now, the output of the “code.exe” command is saved in a file named “output.txt” within the “%localappdata%\microsoft\VSCode” directory. Additionally, the content of “output.txt” is copied to another file named “output2.txt” in the same directory to extract the 8-character alphanumeric activation code for the GitHub account.
Following this, the script reads the “output2.txt” file and identifies the GitHub account activation code using a regular expression pattern “and use code (\w{4}-\w{4})” as shown in the figure below. This extracted code is saved to a variable for later stages of the attack, enabling further malicious activities.

Exfiltration
The TA then gathers the victim’s system information by collecting the names of folders from several directories, including “C:\\Program Files,” “C:\\Program Files (x86),” “C:\\ProgramData,” and “C:\\Users.” In addition, Additionally, the TA obtains a list of processes currently running on the victim’s machine and sends this information directly to the TA’s command-and-control (C&C) server, “hxxp://requestrepo.com/r/2yxp98b3“ as shown below. RequestRepo.com is primarily a tool for analyzing incoming HTTP and DNS requests. However, the TA has exploited it to capture stolen data transmitted from victim machines.

Furthermore, the TA gathers more sensitive data, such as the system’s language settings, geographical location, computername, username, userdomain, the activation code for the remote tunnel, and details about user privileges. All of this data is base64 encoded to obfuscate it before being sent to the command-and-control (C&C) server via a POST request. The figure below shows the code snippet used by the TA for data exfiltration.

Impact
After the TA receives the exfiltrated data, they can log in using their GitHub account at the URL “hxxps://github.com/login/device”. Here, the TA can enter the exfiltrated alphanumeric activation code to gain unauthorized access to the victim’s machine.

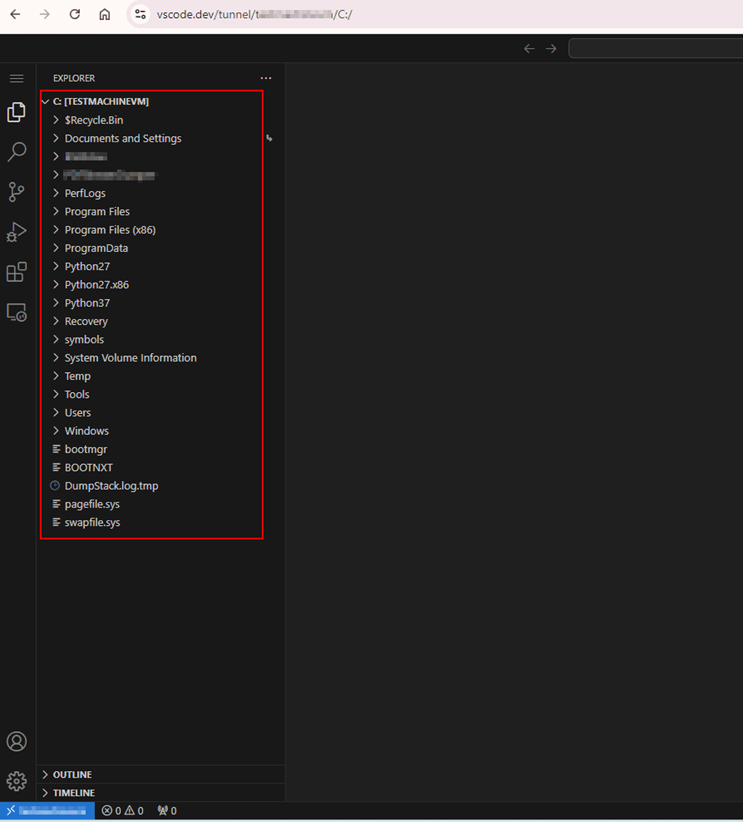
Unauthorized access to the victim’s machine allows the TA to view and manipulate files and directories stored on the victim’s system. The figure below shows how the TA can access the victim’s files through the VSCode tunnel using the stolen activation code.

This degree of access not only enables them to browse through the victims’ files but also enables them to execute commands through the terminal. With this control, the TA can perform a variety of actions, such as installing malware, extracting sensitive information, or altering system settings, potentially leading to further exploitation of the victim’s system and data.

Unit42 researchers explained that the TA can execute several tools, including mimikatz, LaZagne, In-Swor, and Tscan, to perform various malicious activities on the victim’s system.
Conclusion
This campaign demonstrates the growing sophistication of TAs in leveraging legitimate tools like VSCode to establish unauthorized access to victim systems. By utilizing a seemingly harmless .LNK file and an obfuscated Python script, the Threat Actot can effectively bypass detection measures. This access allows them to manipulate files, execute commands, and potentially install additional malware, amplifying the scope for exploitation.
Organizations maintain a proactive security posture, focusing on vigilance, enhancing existing security practices, and implementing new ones to defend against a constantly evolving threat spectrum. Understanding these tactics is crucial for building a more resilient cybersecurity posture.
Recommendations
- Utilize advanced endpoint protection solutions that include behavioral analysis and machine learning capabilities to detect and block suspicious activities, even those involving legitimate applications like VSCode.
- Review scheduled tasks on all systems regularly to identify unauthorized or unusual entries. This can help detect persistence mechanisms established by threat actors.
- Conduct training sessions to educate users about the risks of opening suspicious files or links, particularly those related to .LNK files and unknown sources.
- Limit user permissions to install software, particularly for tools that can be exploited, like VSCode. Implement application whitelisting to control which applications can be installed and run on systems.
- Deploy advanced monitoring tools that can detect unusual network traffic, unauthorized access attempts, and abnormal behavior within the system. Regularly audit and review system and application logs to catch early signs of intrusion.
MITRE ATT&CK® Techniques
| Tactic | Technique | Procedure |
| Execution (TA0002) | Command and Scripting Interpreter: Python (T1059.006) | Update.py is downloaded and executed by the shortcut file |
| Persistence (TA0003) | Scheduled Task/Job: Scheduled Task (T1053.005) | “MicrosoftHealthcareMonitorNode” scheduled task is created for non-admin users |
| Privilege Escalation (TA0004) | Scheduled Task/Job: Scheduled Task (T1053.005) | “MicrosoftHealthcareMonitorNode” scheduled task is created for admin users with SYSTEM privilege |
| Defense Evasion (TA0005) | Masquerading: Match Legitimate Name or Location (T1036.005) | Creates a folder “%localappdata%/Microsoft/Python” directory |
| Discovery (TA0007) | System Information Discovery (T1082) | Collects system’s language settings, geographical location, computername, username, and userdomain |
| Discovery (TA0007) | File and Directory Discovery (T1420) | Collects folder names present in program files and program data directory |
| Discovery (TA0007) | Process Discovery (T1057) | “tasklist” command is used to gather a list of currently running processes. |
| Command and Control (TA0011) | Application Layer Protocol: Web Protocols (T1071.001) | The VSCode tunnel feature is used to access the victim’s system. |
Indicators Of Compromise
| Indicators | Indicator Type | Description |
| 281766109f2375a01bad80478fd18841eccaefc1ee9277179cc7ff075d1beae2 | SHA-256 | Shortcut file |
| c7f07bdfb91653f53782885a3685436e2e965e1c5f4863c03f5a9825c0364489 | SHA-256 | update.py |
| hxxp://requestrepo.com/r/2yxp98b3 | C&C | POST request sent to this URL |
| hxxps://paste[.]ee/r/DQjrd/0 | URL | Downloads update.py |
Related
如有侵权请联系:admin#unsafe.sh