This entry is a bit convoluted, but it’s still quite interesting. I have discovered it today onl 2024-10-20 06:17:28 Author: www.hexacorn.com(查看原文) 阅读量:29 收藏
This entry is a bit convoluted, but it’s still quite interesting. I have discovered it today only to google around and find out someone posted the info about it back in 2013. So, I will describe what they did in 2013 + will add one extra bit.
The trick relies on the way the UserInstStubWrapper API exported by advpack.dll / IEAdvpack.dll works.
When you execute a command like this:
rundll32.exe advpack.dll, UserInstStubWrapper test
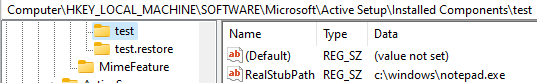
the UserInstStubWrapper function will read the value from RealStubPath:
HKLM\SOFTWARE\Microsoft\Active Setup\Installed Components\test RealStubPath=<PATH> (f.ex. c:\windows\notepad.exe)
and execute the program referenced by it (in this case Notepad).
As for the extra, there is a twin function called UserUnInstStubWrapper. This one requires admin privileges to run, but it behaves in a similar manner – f.ex. for the command:
rundll32.exe advpack.dll, UserUnInstStubWrapper test
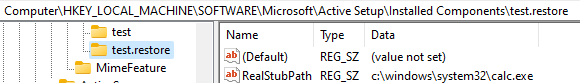
it will reach out to Registry and fetch the value of RealStubPath as well, but this time the key it accesses will be the name passed via the command line, but slightly modified by adding a suffix .Restore to it:
HKLM\SOFTWARE\Microsoft\Active Setup\Installed Components\test.Restore RealStubPath=<PATH> (f.ex. c:\windows\system32\calc.exe)
So, a persistence opportunity relies on populating these Registry entries and then using the following commands executed leveraging any of the existing persistence locations (f.ex. Run key):
rundll32.exe advpack.dll, UserInstStubWrapper test rundll32.exe advpack.dll, UserInstStubWrapper test rundll32.exe ieadvpack.dll, UserUnInstStubWrapper test rundll32.exe ieadvpack.dll, UserUnInstStubWrapper test
If we enable the advpack logging we can see these test log entries:
-------------------- advpack.dll is loaded or Attached ------------------------------ Date: 10/19/2024 (mm/dd/yyyy) Time: 15:11:52 (hh:mm:ss) UserInstStubWrapper: LaunchAndWait: Cmd=c:\windows\notepad.exe -------------------- advpack.dll is loaded or Attached ------------------------------ Date: 10/19/2024 (mm/dd/yyyy) Time: 15:11:58 (hh:mm:ss) UserUnInstStubWrapper: LaunchAndWait: Cmd=c:\windows\system32\calc.exe LaunchAndWait: End hr=0x0, c:\windows\system32\calc.exe UserUnInstStubWrapper: End hr=0x0 -------------------- advpack.dll is unloaded or Detached ----------------------------
如有侵权请联系:admin#unsafe.sh