2024-10-25 23:0:46 Author: cyble.com(查看原文) 阅读量:2 收藏
Key takeaways
- Cyble Research and Intelligence Labs (CRIL) came across an ongoing cyberattack campaign originating from malicious LNK files.
- The sophisticated multi-stage attack chain relies heavily on PowerShell and BAT scripts to streamline the download and execution of additional payloads, demonstrating the Threat Actor’s (TA) preference for script-based methods to evade detection by traditional security solutions.
- The attack involves the creation of an administrative account on the victim’s system and altering Remote Desktop settings to lower authentication requirements, simplifying unauthorized RDP access for the attacker.
- The campaign deploys an additional well-known password recovery tool, ChromePass, which collects saved passwords from Chromium-based browsers, increasing the risk of broader account compromises.
- Based on its TTPs, we have not been able to attribute this campaign, so for tracking purposes, we are naming it “HeptaX”.
Overview
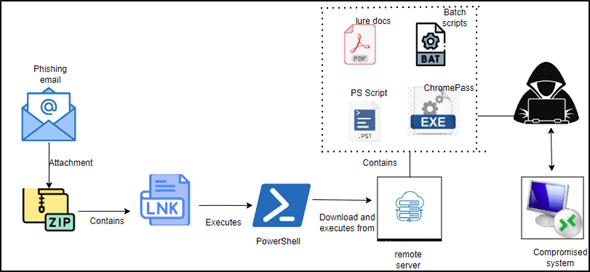
CRIL has come across a multi-stage cyberattack campaign that begins with a ZIP file containing a malicious shortcut file (.lnk). While the source of this ZIP file remains unknown, it is suspected to be disseminated through phishing emails. Based on the LNK file name, it is suspected that this campaign targets the healthcare industry.
Upon execution, the LNK file triggers a PowerShell command that downloads and executes a series of additional payloads, including PowerShell scripts and BAT files, from a remote server. These scripts work in tandem to create a new user account on the compromised system with administrative privileges and modify Terminal Services (RDP) settings, lowering authentication requirements. This setup enables the TAs to easily establish remote desktop access (RDP) to the victim’s system, facilitating further malicious activities such as data exfiltration, the installation of additional malware, or even system monitoring.
Furthermore, CRIL identified the presence of an unwanted application called “ChromePass” within the threat actors’ network infrastructure. This hacking tool is designed to steal saved passwords from Chromium-based browsers, adding another layer of risk for victims by exposing their credentials. The image below illustrates the infection chain.

Based on the information obtained through pivoting, this group has been operational since 2023 and has executed a range of attacks across different sectors, as reflected in the names of the lure files. While the overall attack flow has remained consistent, it is surprising that they are still active using the same techniques. Several researchers have previously identified this campaign [1],[2],[3],[4],[5], with the majority of findings shared by the Malware Hunter Team.
Campaign analysis
Over the past 12 months, this unidentified group has consistently reemerged with various lure themes while maintaining unchanged attack patterns. Tracked as HeptaX,’ the campaign relies heavily on PowerShell and Batch scripts to gain control over compromised systems. By pivoting the IP address, we uncovered several additional artifacts associated with the same TAs used across different campaigns.





One of the notable files from this campaign is:
- 202409_Resident_Care_Quality_Improvement_Strategies_for_Nursing_Homes_Enhancing_Patient_Satisfaction_and_Health_Outcomes.pdf.lnk
In addition, older campaigns attributed to this threat group over the past year include malicious files with names such as:
- SOW_for_Nevrlate.pdf
- WebContentWriting_Handout.pdf
- Blockchain_Trading_Website_Manager.docx
- Project Description – PoC smart assistant Vhyro Project from jvope signature.pdf
- Resume – professional sax, keys and guitar player with over 40 years experience working with own bands, accompanied world stars.pdf
- dropshipping Elien project prposal-soft online service ventilization from xihu.pdf.lnk
The diversity in file names and themes suggests that this group tailors its campaigns to appeal to a variety of victims, indicating a broad targeting strategy across multiple industries.
Technical Analysis
Upon execution, the LNK file runs a PowerShell command that downloads and executes subsequent payloads from a remote server. The image below shows a partially de-obfuscated PowerShell command.

First stage – bb.ps1
As an initial step, the downloaded PowerShell script constructs a base URL to which it sends information and from which it downloads other stage payloads. The PowerShell script contains multiple functions, the first of which retrieves a unique identifier (UID) for the compromised system. This UID is obtained either from a specific registry path (HKEY_LOCAL_MACHINE\SOFTWARE\Wireless) or from a log file (id.log) in the “C:\Users\Public\Documents” directory. If neither exists, a new GUID is generated and saved to a newly created id.log file.

Next, the PowerShell script creates a shortcut file in the Windows Startup folder for persistence. The contents of the newly generated LNK file match those of the original malicious LNK file. The image below shows the function responsible for creating the new LNK file in the startup folder.

Then, the PowerShell script constructs a URL by appending the previously generated UID to the remote server, forming the request hxxp://157.173.104.153/up/get-command.php?uid=<UID>, and uses WebClient to send a request to fetch commands from the server. Upon receiving a successful response, it checks whether the response contains the string “autoreconnect”. If this string is present, the Powershell script runs the code in the current session using `iex`; otherwise, it executes the code as a background task in a separate PowerShell process.

Afterward, the PowerShell script downloads a password-protected lure document from the above-mentioned remote server, saves it in the system’s temporary directory “C:\Users\<Username>\AppData\Local\Temp”, and then launches the document. The image below displays the function code and the open directory containing the lure PDF.


Finally, the PowerShell script retrieves two registry values related to User Account Control (UAC):
- HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System\ConsentPromptBehaviorAdmin, which controls the consent prompt behavior for administrators.
- HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System\EnableLUA, which indicates whether UAC is enabled.
If either of these values is 0, suggesting that UAC is either disabled or configured to a less secure setting, the script proceeds to download and execute another PowerShell script (b.ps1) from the remote server.

Second Stage – b.ps1
The newly downloaded second-stage PowerShell script includes several functions, some mirroring those from the first stage. The primary function of this script is focused on evaluating the system’s User Account Control (UAC) settings, utilizing the same registry checks employed earlier to determine whether UAC is enabled and if the consent prompt for administrators remains active.
If UAC is disabled or the consent prompt behavior is configured to a less secure state, the function sends a message to the remote server indicating that UAC is off by default: (“hxxp://157.173.104[.]153/up/index.php?uid=$uid&msg=UAC off in default!”).
If both settings are enabled, the function enters a loop, repeatedly attempting to disable UAC by setting the “ConsentPromptBehaviorAdmin” value to 0. Once successful, it sends a message to the remote server stating that UAC has been forcefully disabled: (“hxxp://157.173.104[.]153/up/index.php?uid=$uid&msg=UAC force disabled!”). The below image shows the function code responsible for sending a POST request to the remote server, transmitting information about the victim’s User Account Control (UAC) status.

After a brief 300-millisecond sleep, the PowerShell script calls the schReg() function, which downloads three batch files from the remote server into the system’s temporary directory ($env:TEMP). The files are named “k1.bat,” “scheduler-once.bat,” and “k2.bat.” After downloading, the script runs the “scheduler-once.bat” file using the “Start-Process” cmdlet with elevated privileges. The image below shows the code responsible for downloading and executing the batch files.

Third Stage – scheduler-once.bat
The executed batch file copies “k1.bat” and “k2.bat” from the %temp% directory to “C:\Windows\System32”, renaming them to “sysmon.bat” and “sysmon2.bat”. It then deletes the original “k1.bat” and “k2.bat” files from the temp location. Next, the batch file checks for and removes any scheduled tasks named:
- Intel(R) Ethernet Connection 1219-LM
- Intel(R) Ethernet2 Connection 1219-LM
Afterward, it creates a new scheduled task called “Intel(R) Ethernet2 Connection 1219-LM” to run “sysmon2.bat”. Finally, the script “scheduler-once.bat” deletes itself to cover its traces from the system. The image below displays the contents of the batch file “scheduler-once.bat”.

Fourth Stage – sysmon2.bat
Once the scheduled task is triggered to execute the “sysmon2.bat” file, it first checks for and removes any existing scheduled tasks named:
- Intel(R) Ethernet Connection 1219-LM2
- Intel(R) Ethernet2 Connection 1219-LM2
Afterward, it creates a new scheduled task called “Intel(R) Ethernet2 Connection1219-LM2” to run the “sysmon.bat” file located in the “C:Windows\System32” folder. Notably, the previous third-stage batch file performs similar checks, but the task names differ slightly. The image below shows the content of the “sysmon2.bat” file.

Fifth Stage – Sysmon.bat
The sysmon.bat script executes a series of actions:
- Creates a new user account named “_BootUEFI_”.
- Sets the password for this newly added account to “123456!!!” and activates it.
- Adds the “_BootUEFI_” account to the Administrators group, granting it administrative privileges.
- Adds the “_BootUEFI_” account to the Remote Desktop Users group, allowing it to utilize Remote Desktop.
- Removes the “_BootUEFI_” account from the Users group, ensuring it retains only administrative and remote desktop privileges.
- Additionally, the batch file makes several registry modifications to enable Remote Desktop and lower its security features. This includes hiding the “_BootUEFI_” user from the login screen and adjusting Terminal Services (Remote Desktop) settings to facilitate easier remote connections without stringent authentication requirements.
- The batch file runs a PowerShell command that circumvents execution policy restrictions and adds the System32 directory, which contains the three malicious batch files, to the Windows Defender exclusion list.
- Finally, it initiates a background PowerShell process that downloads and executes another PowerShell script from the remote server (hxxp://157.173.104[.]153/up/a.ps1).

Sixth Stage – a.ps1
The newly downloaded PowerShell script “a.ps1” functions similar to the first stage script (bb.ps1). It constructs a URL by appending the previously generated UID to the remote server address, forming a request to “hxxp://157.173.104.153/up/get-command.php?uid=<UID>”.
The script then utilizes a WebClient to send a request and retrieve commands from the server. Upon receiving a response, it checks for the presence of the string “autoreconnect id.” If this string is found, the PowerShell script executes the code in the current session using iex; otherwise, it runs the code as a background task in a separate PowerShell process. Notably, in both stages, we did not receive any specific commands such as “autoreconnect” or “autoreconnect id”. The main difference in this sixth-stage script is that it looks for the string “autoreconnect id” instead of just “autoreconnect”. The below image shows the code for reconnecting to the server.

Seventh Stage – Server response PowerShell Script
Upon establishing a connection with the server, a new PowerShell script is executed. This script contains several functions aimed at system reconnaissance, data exfiltration, and interaction with the remote server.
The script collects detailed system information, including:
- Computer name and username.
- Retrieves recent files from the directory: C:\Users\<user profile>\AppData\Roaming\Microsoft\Windows\Recent.
- Acquires network configuration details using “ipconfig /all”.
- List of users on the machine (net user).
- Obtains current logged-in user details.
- Identifies local user groups associated with the current user.
- Retrieves excluded directories in Windows Defender.
- Lists installed antivirus products.
- Captures running processes using “tasklist”.
- Gathers overall system information using “systeminfo”.
- All this data is saved in a log file located at “C:\Windows\Temp\OneDriveLog\OneDrive.log”.
The script then reads the contents of the log file, converts the data into a byte array, and encodes it in Base64 format. This encoded data, along with the unique user ID (uid), is appended to the base URL” hxxp://157.173.104[.]153/up/index.php” and sent via a POST request. After successfully transmitting the data, the log file and its directory are deleted to eliminate any traces of the data collection.

Taking Remote desktop
With all the collected information, User Account Control (UAC) disabled, and a new user account named “BootUEFI” created with administrative privileges, along with lowered authentication requirements for Terminal Services, the TAs can easily gain access to the compromised remote desktop. This access enables them to perform various actions on the victim’s machine, such as:
- Installing additional malware
- Exfiltrating sensitive data
- Monitoring user activity
- Modifying system settings
- Utilizing the machine for malicious activities
Additionally, we observed an unwanted application—a hacking tool named ChromePass—associated with the same network infrastructure at “hxxp://157.173.104[.]153/up/Tool/ChromePass.exe” This tool is designed to steal saved passwords from Chromium-based browsers.
Conclusion
Over the past year, this group has executed multiple attacks utilizing various lures and targeting different victims, all while remaining largely unnoticed. Their reliance on basic scripts has enabled TAs to gain remote access to compromised systems seamlessly, allowing for extensive exploitation without triggering alarms.
Additionally, the deployment of the ChromePass tool further underscores the group’s intent to harvest sensitive information, such as saved passwords from Chromium-based browsers, thereby posing a significant threat to the security of individuals and organizations alike. This combination of tactics highlights the need for enhanced detection and prevention measures to combat these stealthy cyber threats effectively.
Recommendations
- The initial breach may occur via spam emails. Therefore, it’s advisable to deploy strong email filtering systems to identify and prevent the dissemination of harmful attachments.
- Exercise caution when handling email attachments or links, particularly those from unknown senders. Verify the sender’s identity, particularly if an email seems suspicious.
- Consider disabling the execution of shortcut files (.lnk) from email attachments or implementing policies that require explicit user consent before executing such files.
- Consider disabling or limiting the execution of scripting languages, such as PowerShell and cmd.exe, on user workstations and servers if they are not essential for legitimate purposes.
- Implement policies that prevent the unauthorized creation of privileged accounts.
- Regularly track changes to User Account Control (UAC)- related registry keys, such as “EnableLUA” and “ConsentPromptBehaviorAdmin.” Monitoring these keys helps identify potential attempts to bypass UAC, enhancing system protection against unauthorized changes.
- Strengthen the security of Remote Desktop Protocol (RDP) by enforcing strong authentication mechanisms, such as multi-factor authentication (MFA), and by using network-level authentication (NLA). Limiting RDP access to trusted IP addresses and utilizing VPNs can also help mitigate risks.
- Set up network-level monitoring to detect unusual activities or data exfiltration by malware. Block suspicious activities to prevent potential breaches.
MITRE ATT&CK® Techniques
| Tactic | Technique | Procedure |
| Initial Access (TA0001) | Phishing (T1566) | The LNK file may be delivered through phishing or spam emails |
| Execution (TA0002) | User Execution: Malicious Link (T1204.001) Command and Scripting Interpreter: PowerShell (T1059.001) | Execution begins when a user executes the LNK file The LNK file executes PowerShell commands |
| Defense Evasion (TA0005) | Obfuscated Files or Information (T1027) | Scripts include packed or encrypted data. |
| Persistence (TA0003) | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder (T1547.001) | Adds LNK file in the startup folder |
| Privilege Escalation (TA0004) | Abuse Elevation Control Mechanism (T1548) Account Manipulation (T1098) | Bypass User Account Control Manipulate accounts to maintain and/or elevate access to victim systems. |
| Discovery (TA0007) | System Information Discovery (T1082) | Script gathers system information. |
| Credential Access (TA0006) | Credentials from Password Stores: Credentials from Web Browsers (T1555.003) | Retrieves credentials from web browsers |
| C&C (TA0011) | Ingress Tool Transfer (T1105) | Downloads files from webservers via HTTP |
| C&C (TA0011) | Application Layer Protocol (T1071) | Malware exe communicate to C&C server. |
Indicators Of Compromise
| Indicators | Indicator Type | Description |
| 6605178dbc4d84e789e435915e86a01c5735f34b7d18d626b2d8810456c4bc72 | SHA256 | Zip File |
| 18e75bababa1176ca1b25f727c0362e4bb31ffc19c17e2cabb6519e6ef9d2fe5 5ff89db10969cba73d1f539b12dad42c60314e580ce43d7b57b46a1f915a6a2b | SHA256 | Malicious LNK file |
| 1d82927ab19db7e9f418fe6b83cf61187d19830b9a7f58072eedfd9bdf628dab | SHA256 | bb.ps1 |
| a8d577bf773f753dfb6b95a3ef307f8b4d9ae17bf86b95dcbb6b2fb638a629b9 | SHA256 | b.ps1 |
| 999f521ac605427945035a6d0cd0a0847f4a79413a4a7b738309795fd21d3432 | SHA256 | K1.bat |
| 4b127e7b83148bfbe56bd83e4b95b2a4fdb69e1c9fa4e0c021a3bfb7b02d8a16 | SHA256 | GooglePass |
| hxxp://157.173.104[.]153/up/index.php hxxp://157[.]173.104.153/up/b.ps1 hxxp://157.173.104[.]153/up/bb.ps1 hxxp://157.173.104[.]153/up/scheduler-oncex hxxp://157.173.104[.]153/up/trigger hxxp://157.173.104[.]153/up/Tool/ChromePass.exe hxxp://157.173.104[.]153/up/get-command.php hxxp://157.173.104[.]153/up/bait/202409_Resident_Care_Quality_Improvement_Strategies_for_Nursing_Homes_Enhancing_Patient_Satisfaction_and_Health_Outcomes.pdf | URL | Remote server |
References
https://twitter.com/malwrhunterteam/status/1701669714244542758
https://twitter.com/AzakaSekai_/status/1846482785009348692
https://twitter.com/fmc_nan/status/1701427951714345296
https://twitter.com/malwrhunterteam/status/1708219656488571188
https://twitter.com/malwrhunterteam/status/1701672325580550176
Related
如有侵权请联系:admin#unsafe.sh