Zero Trust security changes how organizations handle security by doing away with implicit trust while continuously analyzing and validating access requests. Contrary to perimeter-based security, users within an environment are not automatically trusted upon gaining access. Zero Trust security encourages continuous monitoring of every device and user, which ensures sustained protection after successful user authentication.
Why companies adopt Zero Trust security
Companies adopt Zero Trust security to protect against complex and increasingly sophisticated cyber threats. This addresses the limitations of traditional, perimeter-based security models, which include no east-west traffic security, the implicit trust of insiders, and lack of adequate visibility.
 |
| Traditional vs. Zero Trust security |
Zero Trust security upgrades an organization's security posture by offering:
- Improved security posture: Organizations can improve their security posture by continuously gathering data on network traffic, access requests, and user/system activities within their environment.
- Protection from insider threats: Zero Trust security ensures that every user within the network perimeter is authenticated before being granted access by adopting the principle of "never trust, always verify."
- Adaptation to remote work: Zero Trust security improves the security of remote work organizations by prioritizing identity verification, security, and continuous monitoring of each device/user.
- Compliance: It helps organizations meet compliance requirements by enforcing strict control, continuous monitoring, and data protection that aligns with regulatory standards.
- Mitigation of breaches: By implementing automated response mechanisms, organizations can quickly limit access privileges for compromised accounts and devices, thereby containing potential damage and reducing the overall impact of a breach.
How to apply Zero Trust security
Here are the factors to consider when implementing Zero Trust security for your organization:
- Continuous monitoring: This ensures that all network and system activities are monitored and analyzed. You can adopt a Security Information and Event Management (SIEM) platform. A SIEM is a security solution that offers real-time visibility, allowing organizations to identify and resolve security threats and vulnerabilities.
- Incident response: This enables organizations to respond swiftly to security incidents. Organizations use Extended Detection and Response (XDR) platforms to react quickly to security breaches, minimizing damage and reducing downtime.
- Initial access prevention: By continuously monitoring for vulnerability exploitation, unusual user behavior, and brute-force login attempts, organizations can detect threats in real-time before attackers establish an entry point.
- Least privilege: This encourages minimal privilege attribution within the system, as users should only be granted the necessary access. It can be achieved by using Identity and Access Management (IAM) solutions. IAM solutions use Role-Based Access Control (RBAC) to assign specific permissions to users. You can utilize a SIEM and XDR platform to monitor IAM configurations for unauthorized changes.
- Device access control: All devices accessing the network must go through a prior authentication and verification process. This process involves checking the device's identity, security posture, and compliance with organizational policies. Even after initial access is granted, the device may continue to be monitored for any signs of compromise, ensuring ongoing security.
- Microsegmentation: This Zero Trust security principle encourages organizations to break their network infrastructure into smaller, isolated parts. Each part operates independently with its security controls, reducing the attack surface by minimizing the risks of lateral movements.
- Multi-factor authentication: This adds an extra layer of security by requiring users to present multiple verification forms before gaining access to systems, applications, or data. It reduces the risk of unauthorized access, even if one factor, like a password, is compromised.
The following section shows examples of leveraging Wazuh capabilities for Zero Trust security.
How to leverage Wazuh for your Zero Trust security
Wazuh is a free, open source security platform that offers unified XDR and SIEM capabilities across workloads in cloud and on-premises environments. You can utilize the Wazuh documentation to set up this solution for your organization.
Wazuh capabilities help organizations safeguard their IT environments against various security threats, making it a suitable solution when applying Zero Trust security. With real-time monitoring, automated incident response, and extensive visibility into user behavior and system configurations, Wazuh enables you to detect and respond to potential breaches before they escalate. Below are some cases of Wazuh being used for Zero Trust security.
Detection of abused legitimate tools
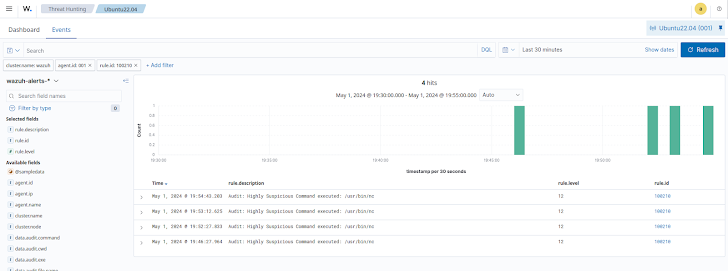
Wazuh capabilities, such as monitoring system calls, Security Configuration Assessment (SCA), and log data analysis, can be used to detect abused legitimate tools.
The monitoring system calls capability analyzes file access, command execution, and system calls on Linux endpoints. This helps threat hunters identify when trusted tools are used for malicious purposes, such as privilege escalation or unauthorized script execution.
The Wazuh SCA capability assesses system configurations to detect misconfigurations that attackers might exploit. By scanning for vulnerabilities like unnecessary services, weak password policies, or insecure network configurations, SCA reduces the attack surface and prevents the misuse of legitimate tools.
Netcat is a tool widely used by threat actors to establish backdoors, perform port scanning, transfer files, and create a reverse shell for remote access. Wazuh can monitor and alert on suspicious command usage as described in the guide monitoring the execution of malicious commands. This guide shows a scenario where the monitoring system calls capability can log Netcat activities and generate alerts.
 |
| Wazuh audits the Netcat command to detect suspicious activities |
As shown above, each time the nc command is executed, Wazuh generates an alert that allows threat hunters to gain visibility into the executed command and its output.
Detection of initial access
Wazuh uses its log data collection capability to aggregate logs from different sources within an IT environment. It collects, analyses, and stores logs from endpoints, network devices, and applications and performs real-time analyses.
The blog post on Detecting exploitation of XZ Utils vulnerability (CVE-2024-3094) shows how Wazuh leverages its log data collection capability. The CVE-2024-3094 is a critical vulnerability in versions 5.6.0 and 5.6.1 of XZ Utils, a widely-used data compression tool. It stems from a supply chain attack that introduced a backdoor into the software, allowing unauthorized remote access to systems. Specifically, it exploits the liblzma library, a dependency of OpenSSH, enabling attackers to execute arbitrary commands via SSH before authentication. This could lead to remote code execution (RCE), compromising system security.
Wazuh identifies and forwards logs about potentially malicious sshd descendant processes through customizable decoders and rules. This approach helps in the early detection of exploitation attempts for this vulnerability.
 |
| Wazuh audits the sshd service to detect CVE-2024-3094 |
As shown above, after analyzing the sshd service, Wazuh detects and flags abnormal activity patterns.
Incident response
The Wazuh platform enhances incident response for security teams by providing real-time visibility into security events, automating response actions, and reducing alert fatigue.
By leveraging its Active Response capability, Wazuh enables teams to manage incidents effectively through automated scripts that can be triggered for any configured event. This automation is particularly beneficial in resource-constrained environments, allowing security teams to focus on vital tasks while the system handles routine responses.
The blog post on detecting and responding to malicious files using CDB lists and active response highlights how security professionals can automate response actions based on specific events using Wazuh active response capabilities.
 |
| Wazuh Active Response capability auto-deletes files with hash values in the CDB list. |
This blog highlights how malicious files can be detected using the Wazuh File Integrity Monitoring (FIM) capability. It works with a constant database (CDB) list of known malicious MD5 hashes. The Wazuh Active Response capability automatically deletes files matching the hash values in the CDB list.
Conclusion
With sensitive data and applications now distributed across multiple servers and environments, the attack surface has expanded, making organizations more vulnerable to data breaches, ransomware, and emerging threats. Organizations adopting the Zero Trust security approach can establish an increased cyber defense mechanism against changing threats.
The Wazuh unified XDR and SIEM platform can implement aspects of this approach, using its log data collection, vulnerability detection, and automated incident response capabilities, amongst others. You can learn more about how the Wazuh platform can help your organization by visiting their website.
Found this article interesting? This article is a contributed piece from one of our valued partners. Follow us on Twitter and LinkedIn to read more exclusive content we post.