2024-11-27 16:37:35 Author: securityaffairs.com(查看原文) 阅读量:0 收藏
Russian group RomCom exploited Firefox and Tor Browser zero-days to target attacks Europe and North America
Pierluigi Paganini
November 27, 2024

The Russian RomCom group exploited Firefox and Tor Browser zero-day vulnerabilities in attacks on users in Europe and North America.
Russian-based cybercrime group RomCom (aka UAT-5647, Storm-0978, Tropical Scorpius, UAC-0180, UNC2596) exploited two Firefox and Tor Browser zero-day vulnerabilities in recent attacks on users across Europe and North America.
The first zero-day exploited by the Russian group, is a use-after-free issue, tracked as CVE-2024-9680, in Firefox.
The vulnerability CVE-2024-9680 resides in Animation timelines. Firefox Animation Timelines is a feature in the Firefox Developer Tools suite that allows developers to inspect, edit, and debug animations directly within the browser. It provides a visual interface for managing animations, including CSS animations and transitions, as well as those created with the Web Animations API.
An attacker could exploit this vulnerability to achieve code execution in the content process.
The second zero-day exploited by the threat actor is CVE-2024-49039. The issue is a Windows Task Scheduler privilege escalation flaw that allows AppContainer escape, enabling low-privileged users to run code at Medium integrity. Discovered by multiple researchers, it is actively exploited, especially across different regions, highlighting its potential impact.
RomCom chained the two vulnerabilities to compromise victims’ systems without user interaction. Victims were infected with the group’s backdoor by simply tricking them into visiting a maliciously crafted website.
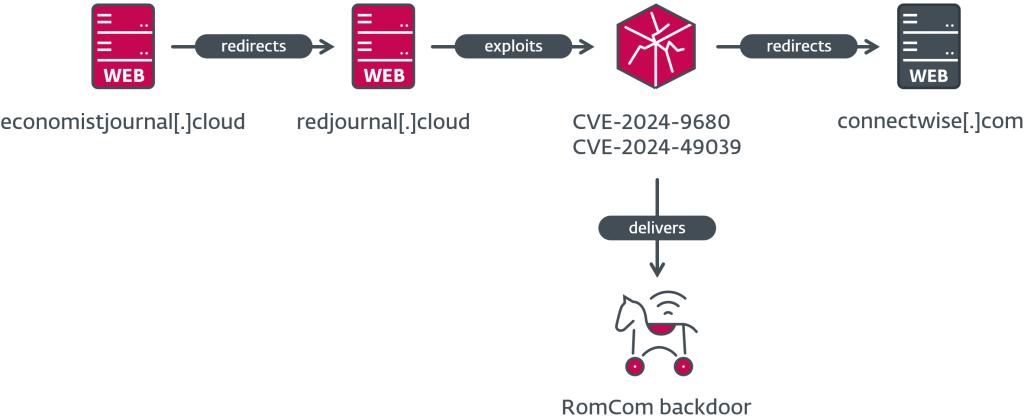
“The compromise chain is composed of a fake website that redirects the potential victim to the server hosting the exploit, and should the exploit succeed, shellcode is executed that downloads and executes the RomCom backdoor.” reads the report published by ESET.
From October 10–16, 2024, attackers exploited unpatched browsers via fake websites that dropped payloads with no user interaction. Victims were redirected to legitimate sites afterward to avoid suspicion. According to ESET, the attackers used fake servers with recurring prefixes or suffixes like “redir” or “red” in domain names.

When a user visits the specially crafted websites using a vulnerable browser, an exploit triggers shellcode execution, using Reflective DLL Injection (RDI) to escape Firefox’s sandbox. This leads to downloading and executing the RomCom backdoor from C2 servers like journalctd[.]live, correctiv[.]sbs, or cwise[.]store.
ESET reported that between October 10 and November 4, 2024, websites hosting the exploit primarily targeted victims in Europe and North America, with up to 250 victims per country.
“Chaining together two zero-day vulnerabilities armed RomCom with an exploit that requires no user interaction. This level of sophistication shows the threat actor’s will and means to obtain or develop stealthy capabilities.” concludes the report. “ESET shared detailed findings with Mozilla, following our coordinated vulnerability disclosure process shortly after discovery. Mozilla released a blogpost about how they reacted to the disclosure and were able to release a fix within 25 hours, which is very impressive in comparison to industry standards.”
In October 2024, Cisco Talos researchers observed Russia-linked threat actor RomCom targeting Ukrainian government agencies and Polish entities in a new wave of attacks since at least late 2023.
In the recent attacks, RomCom deployed an updated variant of the RomCom RAT dubbed ‘SingleCamper.’ SingleCamper is loaded directly from registry into memory and relies on a loopback address to communicate with its loader. The threat actors also employed two new downloaders, called RustClaw and MeltingClaw, plus two backdoors, DustyHammock (Rust-based) and C++-based ShadyHammock
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Russia)
如有侵权请联系:admin#unsafe.sh