
Tale of Stored XSS Leads to admin account takeover
Nov 17 · 2 min read
CVE:https://cve.mitre.org/cgi-bin/cvename.cgi?name=2020-24723
# Exploit Title: User Registration & Login and User Management System 2.1— Stored Cross-Site Scripting
# Date: 2020–11–18
# Exploit Author: Mayur Parmar(th3cyb3rc0p)
# Vendor Homepage: https://phpgurukul.com
# Software Link: https://phpgurukul.com/user-registration-login-and-user-management-system-with-admin-panel/
# Version: 2.1
# Tested on Pop OS(Linux)
# CVE: CVE-2020–24723
Stored Cross-site scripting(XSS):
Stored attacks are those where the injected script is permanently stored on the target servers,
such as in a database, in a message forum, visitor log, comment field, etc.
The victim then retrieves the malicious script from the server when it requests the stored information.
Stored XSS is also sometimes referred to as Persistent XSS.
Attack vector:
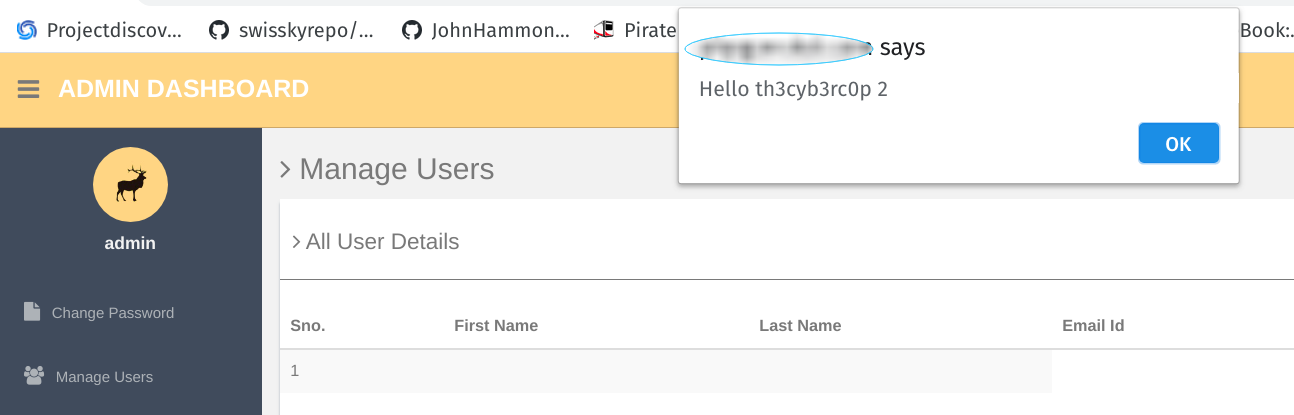
This vulnerability can result in an attacker to inject the XSS payload in the User Registration section and each time admin visits the manage user section from the admin panel,
the XSS triggers and the attacker can able to steal the cookie according to the crafted payload.
Vulnerable Parameters: Last Name
Steps to reproduce:
1. Goto registration page
2. fill in the details. & put <script>alert(“XSS”)</script> payload in First name,Last name
3. Now go to Admin Panel. we can see that our payload gets executed.
Author: Mayur Parmar(th3cyb3rc0p)
https://twitter.com/th3cyb3rc0p?lang=en
https://in.linkedin.com/in/th3cyb3rc0p
如有侵权请联系:admin#unsafe.sh